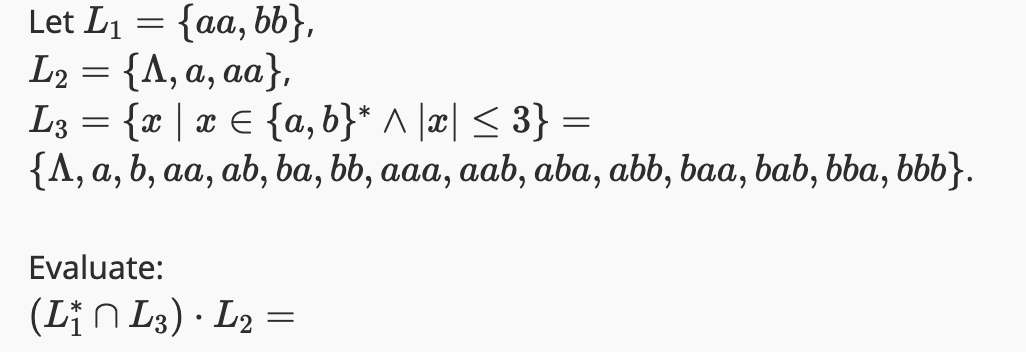
Let L₁ = {aa, bb}, L₂ = {A, a, aa}, L3 = {x | x = {a,b}* ^ |x| ≤ 3} = {A, a, b, aa, ab, ba, bb, aaa, aab, aba, abb, baa, bab, bba, bbb}. Evaluate: (L₁n L3) · L2 = •
Q: a) Manually (you do not need do any of this in code) create a graphical user interface such as the…
A: The objective of the question is to create a graphical user interface that allows the user to input…
Q: Question - Make a Python Program That Solves the Following Probability Problem (Answer to Problem in…
A: StartImport the binom function from the scipy.stats module. binom function is used to work with…
Q: There is a hierarchical relationship between A and B, B and C, C and D, C and E. Select one: True ○…
A: The question is asking whether the given relationships form a hierarchical structure. A hierarchical…
Q: Hello, I'm currently encountering significant challenges in problem-solving and would greatly…
A: The objective of the question is to create a pushdown automata (PDA) for the language defined in…
Q: Consider the game tree below. Run the minmax with alpha-beta pruning algorithm on this tree starting…
A: A total of 10 nodes can be pruned by applying alpha-beta pruning (including leaf nodes). The pruned…
Q: A priority encoder is a combinational circuit that implements a priority function. The operation of…
A: A combinational logic circuit that produces outputs in response to only one input among all…
Q: The following is an example of what? John Doe Anna Smith Peter Jones OREST OHTML OXML JSON…
A: In the provided text we need to find the the given text is example of what among EST HTML XML JSON…
Q: Draw a high level state machine for this process.
A: 1) A state machine is a powerful concept used to model the behavior of a system that can be in…
Q: are six strings of length 4 which cannot be produced by the following regular expre e alphabet Σ =…
A: A regular expression is a string of letters that defines a search pattern. It is frequently…
Q: Perform the following binary multiplication. Assume that all values are 2’s complement numbers.…
A: In step 2, I have provided complete solution to the question...Binary multiplication rules:1 x 0 =…
Q: Title: System Information: router1.gatech.edu Name or IP Address: 172.16.252.1 System Name…
A: The system information provided pertains to a router named "router1.gatech.edu" along with its…
Q: do the following: - A or a to add a container. - D or d to delete a container. - R or r to retrieve…
A: Below C program that stores the information of up to 25 containers loaded on ship.Ask the user for…
Q: Model the following business process. Use pools/lanes where needed.
A: A process flow diagram is a visual representation that illustrates the sequence of steps,…
Q: # CG Q6a # Customer 27 in our dataset did not end up subscribing to the term deposit. ##########…
A: The objective of the question is to use a previously fitted model to predict whether a specific…
Q: Just need the awk program. Tarball is not necessary
A: The required answer is given below:Explanation:For this task, you can use awk to process the output…
Q: Blockchain and the dangers of investing in Digital Currencies. Write an abstract for this topic
A: Blockchain:Blockchain is a distributed ledger system that operates decentralized and makes it…
Q: FIR Filter of 10 dB ripple by using Blackman window in ng an speech signal recorded by MATLAB…
A: To shape the frequency response of a data sequence, such as the FIR filter's impulse response, a…
Q: What potential data will an artificial intelligence (AI) system need to collect for an insurance…
A: The objective of the question is to identify the types of data that an AI system would need to…
Q: C = { € {0, 1}*|| o has twice as many 1's as 0's (Note: this is a little complicated. Use sample…
A: PDA stands for Push Down Automata. The three components of a PDA are an input tape, a control unit…
Q: Using Python or awk script and any given text file such as a book find: (A) the number of unique…
A: This is the Python Script to acheive the desired functionalities: from collections import Counter…
Q: function problem13() { var outputObj = document.getElementById("output"); var inputNumber =…
A: Input:The user inputs a number into the input field.When the button is clicked, the problem13()…
Q: can you show me a virtual representation of each of the followingg parts not words. Can you help me…
A: Context-Free Grammar (CFG): A context-free grammar is a set of recursive rewriting rules/productions…
Q: character: 'Narrator', text: "In the dead of night, beneath a moon veiled by misty clouds, a lone…
A: Rich client applications (RIAs) that function consistently across platforms can be designed,…
Q: Ex 3) Trace the following flowchart for when input values are -10, -1, 3, 2, 11, 13, 1, 0 and…
A: Flowcharts are graphical representations of algorithms or processes. They consist of various symbols…
Q: Computer Architecture Consider a computer that has a number of registers such that the three…
A: let's go through them one by one:1. ADD (R0)+, R2Effective Address: The memory location pointed to…
Q: Please help me with these questions. I am having trouble understanding what to do Programming…
A: 1. Start2. Enter a positive integer3. Set number = input4. While number > 0 a. digit = number…
Q: They question only asks for the number of caloires burnt in the output and not the stuff above it,…
A: SOLUTION -The code is almost correct just you need to directly read the input from the user.In this…
Q: Write a program in C that has three float variable (place random values in them) and that will call…
A: Step-1: StartStep-2: Define three float variables a, b & c, and assign random values to…
Q: User.java User is a class that represents a user in the music player application. Every User…
A: The `User` class in Java is defined with a constructor and instance variables. It is used to create,…
Q: In software engineering, requirements are categorized as functional and non-functional. Could you…
A: Software engineering is a multi-stage engineering practice that involves the precise development of…
Q: The cardinality ratio depends on the real-world meaning of the entity types involved and is defined…
A: 1.A student can only one Social Security number while a Social Security number can belong to only…
Q: Draw an ER diagram for the following scenarios:
A: The question asks to create an Entity-Relationship (ER) diagram for a library system at Stanford…
Q: Part (a): Show the result of inserting 2, 0, 5, 7, 9, 1, 6, 8, 3, 4 into an initially empty binary…
A: A binary search tree (BST) is a type of hierarchical data structure in which the left and right…
Q: Prove that Note: H(XY) ≤ H(X) using log sum inequality. -X and Y are random variables -X and Y are…
A: In information theory, entropy is a measure of uncertainty or randomness in a random variable.…
Q: List and briefly define four different kinds of assembly language statements.
A: In this question we have to list and define four different kinds of assembly language…
Q: Warm up: Variables, input, and type conversion (1) Prompt the user to input an integer between 32…
A: 1. Prompt the user to input an integer between 32 and 126, a float, a character, and a string,…
Q: Draw a class diagram for the above scenario. Bell’s hospital has a patient management system. A…
A: Within Bell's Hospital, the Patient Management System is essential to the coordination of the…
Q: Q4 You will undertake the role of an IT Support and Network Technician working in a help-desk…
A: The objective of the question is to set up a small wireless network using Cisco Packet Tracer. The…
Q: Discuss the concept of cache memory in computer architecture, detailing its role in improving system…
A: Computer architecture belongs to a realm of computer design where it denotes physical organization…
Q: How does Eclipse IDE address patch management? How do they alert users to new vulnerabilities? Is…
A: Eclipse IDE, a popular integrated development environment, addresses patch management through its…
Q: Write MIPS code that prompts the user to enter 3 integers and print the largest and smallest…
A: In programming, efficiently identifying the largest and smallest values within a set of data is a…
Q: Here is the question about mips.Q1). Suppose $s0 stores the base address of word array A and $t0 is…
A: For Q1), the MIPS assembly code to perform the operation A [240] = A[240+m] would look like this: #…
Q: What is the waterfall model in software development? What are its advantages and disadvantages?
A: The waterfall model is a sequential design process in software development, often used in software…
Q: You are expected to create a file that contains 2 classes named "car" and "human". Class car: •The…
A: Algorithm for Car Class:1. Define a class named "Car".2. Define a constructor (__init__) method that…
Q: How is the restaurant industry becoming more effienct and saving money by artificial intelligence…
A: The objective of the question is to understand how the restaurant industry is leveraging artificial…
Q: Show that the following sentence of FOL is a theorem. 1 T3x3уL(x,y) + 3y3xL(y,x) 1. (X,Y) AS 2.…
A: The given problem deals with proving the validity of a sentence in first-order logic (FOL), which is…
Q: x=[20,15,9,7] y=[85,83,80,78] y1=1./(y-x) plot (x,y1)
A: To find the area under the curve defined by the points (x, y) using the trapezoidal rule.Calculating…
Q: k to test the software and equipment that you have recommended by your manager (NOS, Applications,…
A: You can use Cisco Packet Tracer to simulate the network setup in order to construct a small wireless…
Q: Computer Architecture -Compute the decimal value of the binary number (1011 1101 0101 0110)2 if…
A: In computer architecture, binary numbers can be interpreted in different ways depending on the…
Q: Solve these questions
A: The objective of the question is to estimate the values of the given integrals using the Monte Carlo…
Step by step
Solved in 1 steps

- 1. Big-O Notation Let f and g be functions from the set of integers or the set of real numbers to the set of real numbers. We say that f ( x ) is O ( g ( x ) ), read as "f ( x ) is big-oh of g ( x )", if there are constants C and k such that | f ( x ) | ≤ C | g ( x ) | whenever x > k. (a) Show that f(x) = x2 + 2x + 1 is O(x2) Solution: When x>1; ? 2 (1 + 2 ? + 1 ? 2 ) < ? 2 (1 + 2 1 + 1 1 2 ) = 4? 2 So, ??? ? > 1, ? 2 + 2? + 1 < 4? 2 From the definition 0 ≤ f(x) ≤ cg(x) for x≥1 Hence, for N0 = 1; c=4; and g(x)=x2 for N0 = 2; c=3; and g(x)=x2 for N0 = 3; c=2; and g(x)=x2 … Therefore, ? ? + ?? + ? = ?(? ? ) O(g(x)) = {f(x)|there exist positive constant c and N0 such that 0 ≤ f(x) ≤ cg(x) for all x≥N0} 2. Show that 7x2 is O(x3). 3. Suppose there are x number of boxes to be delivered to x number of household that is 2km apart, what is the distance travelled by the transport delivery service? 4. In number 3, suppose that each boxes…Q. No. 2: Let Σ = {a, b, c}. a. Draw a DFSA that rejects all words for which the last two letters match. b. Draw a DFSA that rejects all words for which the first two letters match.Assume the following scoring matrix. A T C G - A 1 -1 -1 -2 -1 T 1 -1 -1 -1 C 2 -1 -1 G 1 -1 Fill out the dynamic programming table for the global alignment between sequences v = TAGCTCCG and w = GCATCCA using the scoring matrix above. Use the following recursive scoring formula. w= G C A T C C A 0 1 2 3 4 5 6 7 v= 0 T 1 A 2 G 3 C 4 T 5 C 6 C 7 G 8 What is the score and global alignment between v and w?
- QUESTION 4 State whether the following statement is true or false : there exists x element of R comma space there exists y space element of R space left parenthesis x plus y equals 2 right parenthesis space logical and left parenthesis x minus y equals 3 right parenthesis True False"Equatable and Comparable" in the Swift Programming: The Big Nerd Ranch Guide (2nd Ed.) e-book: Point’s current conformance to Comparable yields some confusing results. let c = Point(x: 3, y: 4) let d = Point(x: 2, y: 5) let cGreaterThanD = (c > d) // false let cLessThanD = (c < d) // false let cEqualToD = (c == d) // false As the above example demonstrates, the trouble arises in comparing two points when one point’s x and y properties are not both larger than the other point’s. In actuality, it is not reasonable to compare two points in this manner. Fix this problem by changing Point’s conformance to Comparable. Calculate each point’s Euclidean distance from the origin instead of comparing x and y values. This implementation should return true for a < b when a is closer to the origin than b. Use the formula shown in below Figure 25.1 to calculate a point’s Euclidean distance. Figure 25.1 Euclidean distance Euclidean distanceHi! I get this error message with this code. Can you help me? # Write your solution here def who_won(game_board): # Initialize counters for each player's encircled area player1_area = 0 player2_area = 0 # Iterate through each square in the game board for i in range(len(game_board)): for j in range(len(game_board[i])): # Check if the square is encircled by player 1's game pieces if game_board[i][j] == 1: # Check if all four surrounding squares are also player 1's game pieces if (i > 0 and game_board[i-1][j] == 1) and (i < len(game_board)-1 and game_board[i+1][j] == 1) and (j > 0 and game_board[i][j-1] == 1) and (j < len(game_board[i])-1 and game_board[i][j+1] == 1): player1_area += 1 # Check if the square is encircled by player 2's game pieces elif game_board[i][j] == 2: # Check if all four surrounding squares are also player…
- Not pseudocode Suppose the economies of the world use a set of currencies C1, . . . , Cn; think of these as dollars, pounds, Bitcoin, etc. Your bank allows you to trade each currency Ci for any other currency Cj, and finds some way to charge you for this service. Suppose that for each ordered pair of currencies (Ci, Cj ), the bank charges a flat fee of fij > 0 dollars to exchange Ci for Cj (regardless of the quantity of currency being exchanged). Describe an algorithm which, given a starting currency Cs, a target currency Ct, and a list of fees fij for all i, j ∈ {1, . . . , n}, computes the cheapest way (that is, incurring the least in fees) to exchange all of our currency in Cs into currency Ct. Also, justify the its runtime. [We are expecting a description of the algorithm, as well as a brief justification of its runtime.]Write a classifier algorithm for p(Y |X,α)4. Let N(x) be the statement “x has visited North Dakota,” where the domain consists of the students in your school. Express each of these quantifications in English. a) ∃x N(x) b) ∀x N(x) c) ˺∃x N(x) d) ∃x ˺N(x) e) ˺∀x N(x) f ) ∀x ˺N(x)
- PYTHON DATASET given x = np.array([i*np.pi/180 for i in range(60,300,4)]) np.random.seed(10) #Setting seed for reproducibility y = 4*x + 7 + np.random.normal(0,3,len(x)) Write a function inspired by sklearn’s polynomial preprocessing: (https://scikit-learn.org/stable/modules/generated/sklearn.preprocessing.PolynomialFeatures.html) your function should have: degree and include bias parameters only. For this assignment, assume that input is a 1-dimensional numpy array. For example, if an input sample is np.array([a, b]), the degree-2 polynomial features with "include_bias=True" are [1, a, b, a2, b2].Given g = {(1,c),(2,a),(3,d)}, a function from X = {1,2,3} to Y = {a,b,c,d}, and f = {(a,r),(b,p),(c,δ),(d,r)}, a function from Y to Z = {p, β, r, δ}, write f o g as a set of ordered pairs.Simplify the following assertions (so that ¬ does not appear). a) ¬((∃a ∈ A,((∀b ∈ B, a × b = 2) ⇒ (∃b ∈ B, a + b ≠ 3))) & (∀a ∈ A, ∃b ∈ B, ((a+b = 5)∨(a−b = 5)))) b) ¬((∃a ∈ A, ∀b ∈ B, ((a + b = 3) ∨ (a - b = 3))) & (∀a ∈ A, ((∃b ∈ B, a × b = 7) ⇒ (∀b ∈ B, a + b ≠ 4)))) c) ¬((∃a ∈ A, ∀b ∈ B, ((a + b = 2) & (a - b = 2))) ∨ (∀a ∈ A, ((∃b ∈ B, a + b = 7) ⇒ (∀b ∈ B, a + b = 5)))) d) ¬((∀a ∈ A,((∃b ∈ B, a - b = 4) ∨ (∀b ∈ B, a + b ≠ 2))) & (∃a ∈ A, ∀b ∈ B, ((a+b = 5)∨(a−b = 5))))





