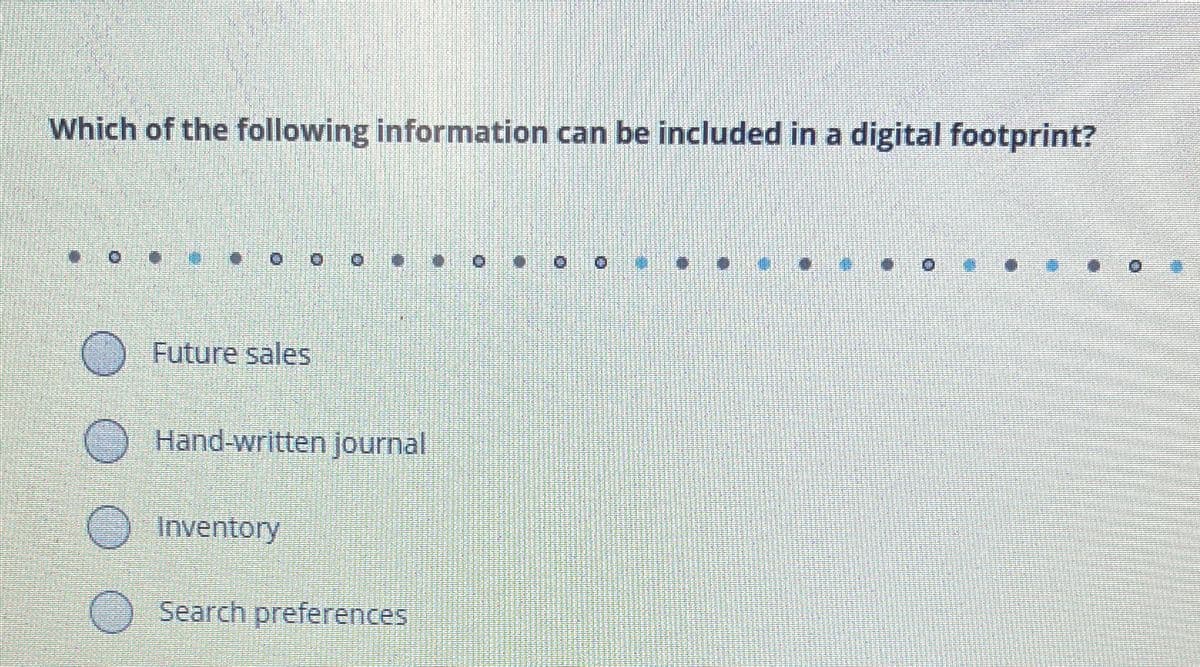
Which of the following information can be included in a digital footprint?
Q: Search engines of the late 2000s provided results based on the number of times a search term…
A: The statement is partially true. In the late 2000s, search engines did consider the frequency of a…
Q: Give two strings of different lengths that are accepted by the above NFA.
A: In this question we have been given with the NFA diagram, using which we have to list the accepted…
Q: What do VPNs do? What are they good for?
A: A Virtual Private Network (VPN) is a technology that creates a safe and encrypted connection over a…
Q: Explain the different asymptotic notations used in expressing the complexity of algorithms?
A: Asymptotic notations are used to express the time and space complexity of algorithms in computer…
Q: Please provide a solution for the Knapsack Problem using Genetic Algorithm:
A: 1. Encoding the problem and creating an initial populationIn a 0/1 Knapsack problem with a genetic…
Q: 1. Read a list of fictional characters from a file named "Characters.txt" and store them in a Python…
A: In this question we have to write a python code for the fictional character from a given characters…
Q: can you please help me with this problem: you will develop an AI for a game in which two players…
A: Initialization Method (__init__):Define a constructor technique __init__ inside the DominoesGame…
Q: Translate the following C program to Pep/9 assembly language. #include int myAge;void putNext(int…
A: The supplied C code snippet demonstrates an easy application that calculates and prints a person's…
Q: The Profile class constructor has a self parameter and two additional parameters: status and…
A: The objective of the question is to complete the constructor of a class named 'Profile' in Python.…
Q: Part (a): Show the result of inserting 2, 0, 5, 7, 9, 1, 6, 8, 3, 4 into an initially empty binary…
A: A binary search tree (BST) is a type of hierarchical data structure in which the left and right…
Q: k to test the software and equipment that you have recommended by your manager (NOS, Applications,…
A: You can use Cisco Packet Tracer to simulate the network setup in order to construct a small wireless…
Q: Your solution for lab #4 will be to create a C program which will accept a number of fixed verb…
A: This project presents a custom shell programmed in C, offering a basic command-line interface…
Q: Explain what a BBIT is and how to use it
A: "BBIT" typically stands for "Bachelor of Business Information Technology." It's an undergraduate…
Q: Dynamic programming: Find the Longest Common Subsequence (LCS) for 10010101 and 010110110. Justify…
A: With the supplied sequences "10010101" and "010110110," we can utilize dynamic programming to…
Q: 533256.4063714.qx3zqy7 Jump to level 1 When the input integer variable suitcaseSize is: • less than…
A: The objective of the question is to write a Java program that takes an integer input for…
Q: Please use the mean normalization formula below to normalize the Age feature (1st column) and Income…
A: In this question we have to normalize the age feature after applying mean normalization.Let's apply…
Q: Need java help 1) If myList is a declared ADT list and the front of the list is on the left, show…
A: 1) In Java, an ADT (Abstract Data Type) list refers to a data structure that represents a collection…
Q: Unstructured decisions is where the rules and constraints governing are known. O True O False
A: The statement is asking whether unstructured decisions are those where the rules and constraints…
Q: Ex 15) Devise an algorithm to input a positive integer, n, and by using "** characters - output the…
A: 1. Start2. Read input integer n3. If n is less than or equal to 0, print an error message and exit4.…
Q: Define a class attribute named min_in_full in the Time class, and assign min_in_full with 'minutes'.…
A: The objective of the question is to define a class attribute named 'min_in_full' in the 'Time' class…
Q: Order the runtimes from fastest growth to slowest growth. fastest growth × 1.1N × Nlog(N) ×…
A: Please refer below page.If you have any doubts please feel free to ask.Explanation:Step 1:Step 2:…
Q: The electronic age is what we currently live in. It can be defined as the time between O A. 1930 B.…
A: 1940Option C is correct.Explanation:Step 1:The electronic age is what we currently live in. It can…
Q: d to the caller: 32k + 1k = 33k (since x will be placed after the header of 1k) Address returned to…
A: The heap, a section of the computer's memory used for dynamic memory allocation, can have a certain…
Q: Write C++ code to copy elements from an old queue to new queue utilizing the enqueue() and dequeue()…
A: The objective of the question is to write a C++ program that copies elements from an old queue to a…
Q: 8 Provide MATLAB code to solve, please.
A: Both Section_A and Section_B are written in Matlab code as below in explanation.Explanation:a)%…
Q: Please make an animation using html, css, and javascript in visual studios to the best of your…
A: In this question we have to write a HTML CSS JS, interactive narrative experience where the user…
Q: Insertion sort, merge sort and quicksort on doubly-linked list Outline: you will implement insertion…
A: In this question we have to write a C++ code for the Insertion sort, merge sort and quicksort on…
Q: Using a switch-tail structure design the following: a) an 8-bit counter with only one bit set to…
A: The specifications for these counters are distinct, and both could be implemented using different…
Q: Model the following business process. Use pools/lanes where needed.
A: A process flow diagram is a visual representation that illustrates the sequence of steps,…
Q: I need help with MATLAB programming. The following code graphs a ellipsoid and a line. I need to…
A: 1. Initialize Parameters: - Set w, beta, and I. - Calculate H_NU and related parameters.2.…
Q: Draw a Class Diagram using the attatched scenario. In the diagram includeclasses, attributes,…
A: Analyze the actors and major use cases for the campus housing system based on the provided…
Q: The following image shows a graph with 7 vertices (nodes) labelled from 1 to 7 and edges connecting…
A: Graph Initialization:Establish a graph comprising seven vertices, each uniquely labeled from 1 to…
Q: Multiple key-value pairs, each representing a person's name and food, are read from input and added…
A: SOLUTION-I have solved this problem in Python code with comments and screenshots for easy…
Q: what is the range of of the unsigned integer data type? a. -128 to +127 b. 0 to 255 c 0 to 65, 535…
A: Data types are used to define what kind of data the variables or functions can hold. Some of the…
Q: Warm up: Variables, input, and type conversion (1) Prompt the user to input an integer between 32…
A: 1. Prompt the user to input an integer between 32 and 126, a float, a character, and a string,…
Q: What cryptography techniques are used to secure data in transit?
A: The objective of the question is to identify and explain the cryptography techniques that are used…
Q: (IV) Given the automaton below for a language L a b a, b 2 Construct an automaton for (i) Reverse of…
A: We need to find the reverse and complement of the given automaton:
Q: e. R is a relation on ZxZZ such that ((a, b), (c, d)) ER if and only if a+b>c+d.
A: In mathematics, relations play a crucial role in understanding the interactions between elements of…
Q: his ri
A: Virtual addresses are addresses that a programme uses to access memory while it is running.The…
Q: using? because It seems like you were trying t
A: As an AI language model, I don't work directly with a compiler. I don't write or execute code;…
Q: Assume a computer is sending the following 3 bytes of data: 89 241 72 over UDP. The data is being…
A: The acronym UDP denotes User Datagram Protocol. Along with TCP (Transmission Control Protocol), it…
Q: evidence, which requires finding To establish authorship of digital evidence in these cases,…
A: In this question we have to determine who created or is responsible for data or activities on…
Q: n in detail so i can fully understand . Attaching a visual will be of great help as well. (as in a…
A: A relational database management system is called MySQL. Instead of storing all the data in one…
Q: design a programmable module UP/DOWN counter. Suggested circuits are the SN74193 counter, SN7485…
A: To design a programmable UP/DOWN counter using the SN74193 counter and SN7485 magnitude comparator,…
Q: Suppose your company takes orders for its products, which are supplied to your company by vendors.…
A: In the area of database control, designing an efficient relational database to deal with orders,…
Q: Dictionary doctor_on_duty contains two key-value pairs read from input. In the try block, integer…
A: The objective of the question is to handle exceptions in Python, specifically the KeyError…
Q: The program opens up the data.txt file using the fopen function and will read the data into two…
A: In this question we have to write a C Program where we need to read data from a text file (data.txt)…
Q: Can you please do it step by step, I only need help with question 2.10 but you need question 2.9 to…
A: A formal grammar that describes the syntax of programming languages or other formal languages is…
Q: Using the table, either buying a network of PCs for a department at your workplace or outfitting a…
A: Multicriteria analysis is a decision-making methodology that involves assessing and comparing…
Q: How to add code (python) to mine to have the try-except validation loop so it only adds valid…
A: First, the code defines the function calculate_paint_needed.In that function, it calculates and…
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- dont dont post existing content else report aswer ur sure else skip dont answerBuild a business model for your startup idea. Download and use the attached business modeling template. Fill in the following tabs: Zen Statement Value Proposition Canvas Lean Canvas Business Model Use this template https://www.google.com/url?q=https://www.google.com/url?q%3Dhttps://docs.google.com/spreadsheets/d/1tB4uULrga0xWA7j0qbHLc7OeQnENnqHpcpShfre6Tok/edit?usp%253Dsharing%26amp;sa%3DD%26amp;source%3Deditors%26amp;ust%3D1638267793223000%26amp;usg%3DAOvVaw1q48l7-WW8VF_PFiOvdRyj&sa=D&source=docs&ust=1638267793248000&usg=AOvVaw3BHU4MqcUH5zgXUvliv2PtChoose one answer: - You have been tasked to develop a website to advertise your school's upcoming dance. Users should be able to register for a ticket and submit song requests through the website. What type of website on AWS is most appropriate for this task? a. Responsive b. Dynamic c. Static d. Nonresponsive
- Go to the Collectibles section of eBay (http://collectibles.shop.ebay.com/) and pick any subcategory that looks interesting to you. Find an auction that is just about to end and bookmark it. When the auction has ended, return to the auction page and click on “Bid History.” (If you have an eBay account, you have the option for searching “Completed Listings.”) Your assignment is to use the bid history to construct a demand curve. (You will have to “reorder” the bids a bit to figure this out. Try to figure out the maximum price that each of the bidders is willing to pay, and then use that information to construct the demand curve. See this example for how to get from a bid history to a demand curve.)HELPFUL NOTES: Only count the highest bid for each bidder. If one bidder bids $25 but then later bids $50 and then never bids again, it must be that his maximum willingness-to-pay is $50; the $25 bid is irrelevant. If the bidder had been willing to bid more than $50, he probably would have…What is a unique feature for Power BI Services (PowerBI.com)? Build interactive visuals Build PivotTables Build Dashboards Build PivotChartsS? P? For Plagarism content we will report
- Design the layout of users, domains, trusted domains, anonymoususers, etc for a start-up open source software company ABC. Theyshould have an internal CVS server, which only internal developerscan access, an anonymous CVS server for outsiders to downloadsource code, WWW servers (one for internal and one for external),and a mail server. Outsiders should not be able to access eitherinternal CVS or internal WWW servers..You should finish the following parts:a) The topology diagram for the different servers and locations andtrust domains. For example, where are the firewalls, and whereare the users located in the topology.b) The assumptions that you make for your design and the securitypolicy to achieve this assumption Your final document should include the following parts:1. Network topology diagram and the domains of trust.2. Security related assumptions in your design, and security policy tomake this assumption valid.3. Trust assumptions about users (e.g., who could be root, what…Which is better for collaboration: Office 365 or Google Docs?https://cleveronly.com/brainbucket/index.php?route=common/home Navigation bar Desktops Create scripts for test cases: Opening PC will show all PCs. If there are no PCs available, then the message "There are no products to list in this category." is displayed Opening Mac will show all Macs. The number of items should match the number in the dropdown option: Clicking on all desktops will show available desktops.
- Choose one answer for this question: - You have been tasked to develop a website to advertise your school's upcoming dance. Users should be able to register for a ticket and submit song requests through the website. What type of website is most appropriate for this task? a. Nonresponsive b. Responsive c. Dynamic d. StaticYou are building a bot that retrieves order updates for customers of an e-commerce application. Your bot must retrieve order details from an Azure Function when the user provides their order reference number. What action do you need to include in your bot? Select only one answer. A. Send HTTP request B. Connect to a skill C. Update Activity D. Send a responsea. State the six (6) major phases involve in effective and efficient web site development & Briefly explain the following terminologies as used in web site development. 1.Server side scripting 2.wireframe



