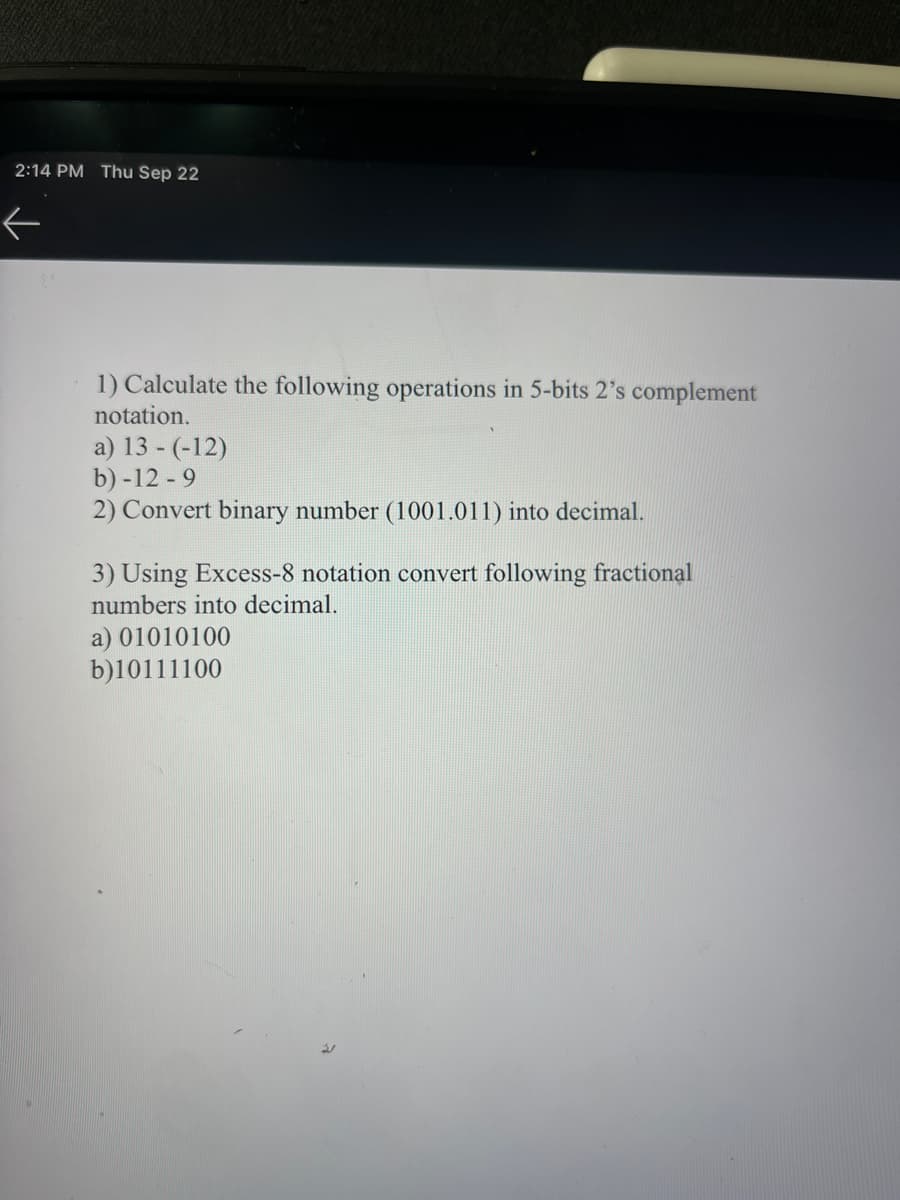
1) Calculate the following operations in 5-bits 2's complement notation. a) 13- (-12) b)-12-9
Q: What are database indexes, and why would you want to use them? How can we utilise indexes in a…
A: Load balancing : Load balancing is a networking technique used to divide work over numerous computer…
Q: In simple words, describe the instruction execution cycle.
A: The Instruction Cycle Each phase of Instruction Cycle can be decomposed into a sequence of…
Q: What time management method is not a preemptive algorithm? Why is this happening, exactly? Round…
A: Introduction The issue at hand is the scheduling technique used in processing, in which the…
Q: Please provide a brief explanation of Unicode.
A: We need to provide a brief explanation of Unicode.
Q: An overview of Visual Studio should be provided.
A: The solution for the above given question is given below:
Q: What are the two parameters that a TryParse function expects from you when you write code?
A: The method accepts two parameters. The first parameter is the string containing the data that is to…
Q: Write a computer program for calculating carburiz
A: The formula for calculating carburization heat treatments is C s − C x C s − C 0 .The solution…
Q: Why is it OK for a function to sometimes produce side effects?
A: Given: What exactly is meant by the term "function" when it comes to side effects In the field of…
Q: The words prefix, infix, and postfix notation should be defined. What does the term "Cambridge…
A: Initial notation: Here, we move the operator's operands to the left. Ex: In this case, (A+B) is…
Q: When is it important to do a type conversion run-time check?
A: The circumstances around the type change The following are the conditions for a type conversion:…
Q: Within a few words, describe the Level-1 cache.
A: Answer is in next step.
Q: Please provide a brief explanation of Unicode.
A: Unicode: Unicode is a character encoding standard that uses 16 bits of data.It is a set of…
Q: An overview of Visual Studio should be provided.
A: Windows Studio It's very common to utilise Visual Studio, an integrated development environment, to…
Q: What do you mean by Data Terminal Equipment(DTE)?
A: Lets see the solution in the next steps
Q: When is it important to do a type conversion run-time check?
A: Conversion between types is referred to as type conversion. Making variables of one type compatible…
Q: Find (49.3) - (00110110.0010), 10 BCD = (?) BCD, with BCD weight (8421)
A: Binary coded decimal is a notation that assigns each digit from 0 to 9 of a decimal number (base 10)…
Q: Give Seven characteristics of a candidate key
A: QUESTION Answer: Candidate key is a single key or a group of multiple keys that uniquely…
Q: How can a new type named doublePointeutir be produced that can be used in place of double*?
A: According to what is stated in the definition: Of the typedef keyword, the declaration of typedef…
Q: Please provide a brief explanation of Unicode.
A: A Unicode is a character encoding standard that has well-known recognition. It is a structure to…
Q: If all of the RadioButton controls are in the same GroupBox, how many of them may be chosen…
A: Introduction: Controls for "RadioButton" may be found in "GroupBox.""RadioButton" controls are…
Q: Describe the application programming interface in a few words (API)
A: Interface for Application Programming (API) An API is a collection of procedures, protocols, and…
Q: Why is it OK for a function to sometimes produce side effects?
A: When something has side effects, what does it mean? An operation, function, or expression is said to…
Q: Business Model Breakdown At the heart of Etsy's success is its business model. A business model is a…
A: Hello student Answer will be in next step and as per my best of knowledge
Q: all of the RadioButton controls are in the same GroupBox, how mi imultaneously?
A: RadioButton A graphical control element known as a radio button or option button allows the user to…
Q: Briefly describe how to press a button.
A: Traditionally, the mouse button is used to press a push button. However, the keyboard can also be…
Q: Can a statement be distinguished from an expression? What does it imply for a language to be…
A: In programming language an Expression which refers to the combination of values and functions that…
Q: Directions: Construct a program flowchart using a sequence control structure to answer the given…
A: In this program we will write the C program to input the temperature convert in Fahrenheit(F) and…
Q: The phrase "de-normalization" refers to the process of altering something from its initial…
A: De-normalization Denormalization is a technique used in a traditional database that was previously…
Q: What exactly does the term "location aware application" mean?
A: Location aware application Location-aware applications refers to the capability of the device to…
Q: Give a thorough analysis of the network adapter's operating features.
A: Answer is in next step.
Q: Why should you utilise an Open and/or Save As dialogue box in an application that deals files? What…
A: Introduction: Dialog box: You use dialog boxes to display information and prompt for input from the…
Q: What distinguishes a text file from a binary file? Can a text editor be used to see a binary or text…
A: Text files are typically used to store a stream of characters and are those in which data is stored…
Q: What distinguishes a variable reference model from a variable value model? Why is it important to…
A: Introduction In this question, we are asked to distinguish a variable reference model from a…
Q: What's the difference between type compatibility and type equivalence?
A: Type Equivalence: Which kinds are viewed as being equivalent is described by type equivalence. When…
Q: The phrase "de-normalization" refers to the process of altering something from its initial…
A: De-normalization Denormalization is a technique used in a traditional database that was previously…
Q: The question was: What are the methods and difficulties for using blockchain in the banking…
A: Answer: Blockchain implementation methods include: Having cryptographic keys: Without cryptography,…
Q: There are three subtleties in the design of enumeration-controlled loops that are presented.
A: Enumerated controlled loops Enumeration-controlled loops repeat a collection of statements a…
Q: In just a few phrases, describe ALIGN.
A: The word ALIGN, commonly referred to as alignment, describes how a text is positioned on the screen.…
Q: Give examples of how all types of software systems may benefit from the key software engineering…
A: Basic computer fundamentals Software is a collection of programming instructions that, when…
Q: The difference between a threat and an assault
A: Threat and an Assault Threats can be intended, such as when someone is negligent, or unintended,…
Q: Open-source software is produced by the Network Funtime Company. The business features a small sales…
A: My primary responsibility as the system administrator for the Network Funtime firm is to protect it…
Q: Are the sensors on microcomputers used for anything in particular?
A: Microcomputer: A microcomputer is a compact, low-cost computer that has a microprocessor, memory,…
Q: Assuming a business has already implemented a KMS system, how can a manager ensure that internal…
A: A manager ensure that Internal knowledge-sharing and learning takes place in person.
Q: What precisely are aggregates?
A: Given: What precisely are aggregates?
Q: Are the sensors on microcomputers used for anything in particular?
A: Microcomputer: The microcomputer is a compact and affordable kind of computer that consists of a…
Q: 1. Should specialized courts for computer related crimes be created? 2. which categories of…
A: Yes, the creation of a cyber court would be advantageous for the courts in many ways. Primarily,…
Q: Why is it that most languages do not specify the order in which the parameters to an operator or…
A: Parameters of the Function: The names of the arguments that are passed into a function are referred…
Q: Is it true that C has loops controlled by enumerations? Explain.
A: There are two different kinds of loops in C programming: both the entrance and the exit are…
Q: Define orthogonality in the context of the design of computer languages.
A: Orthogonality in the context of the design of programming language:
Q: Suppose within your web browser you click on a link to obtain a Web page. The IP address for the…
A: The solution is given below for the above given question:
Step by step
Solved in 3 steps

- 6. Perform the following binary multiplication. Assume that all values are 2’s complementnumbers. Indicate the result and whether there is overflow or not.1011 * 1101EX.3:Convert four last digits (suppose that each digit is the hexadecimal number) in your roll number to binary.Example: if your roll number is HE162491, then four last digits in your roll number are 2491. So, in binary form you will have: 0010 0100 1001 0001a. Encoding each block of 8 bits with Hamming Code (12, 8). b. Using any one encoded block in [a] and modify to one bit error. Explain how to correct error bit?11. Perform the following hexadecimal additions and subtractions. Assume the numbers are stored in 32-bit 2’s complement binary numbers. Indicate the sign of the answer and whether overflow occurs. a. 74F – D63E
- Please write all the process. 1.. Perform the following multiplications. Assume that all values are unsigned numbers. (No problem with unsigned (always positive) numbers, just use the same standard techniques as in base 10.) a.1010 * 0110 2.Perform the following multiplications. Assume that all values are signed 2’s complement numbers. c.11101 * 1110111. Perform the following hexadecimal additions and subtractions. Assume the numbers are stored in 32-bit 2’s complement binary numbers. Indicate the sign of the answer and whether overflow occurs. c. E9B20F5D – FE605C8D7. Perform the following binary division. Assume that all values are unsigned positive numbers.10100 / 11
- Perform the following binary multiplication. Assume that all values are 2’s complement numbers. Indicate the result and whether there is overflow or not. 1011 * 1101 Perform the following binary division. Assume that all values are unsigned positive numbers. 10100 / 116. Convert the following numbers from unsigned binary notation to decimal notation, and from 6-bit 2's complement notation to decimal notation: i) 110011, ii) 001101, iii) 101101 7. Show how each of the following floating point values would be stored using IEEE-754 single precision (be sure to indicate the sign bit, the exponent, and the significand fields): a. 12.5 b. −1.5 c. 0.75 d. 26.625 8. The following is a representation of a decimal floating value using IEEE-754 single precision. Find out the value in decimal. 0 10000011 10101000000...01. List the octal and hexadecimal numbers from (16)10 to (32)10.2. Convert the following numbers with indicated bases to decimal.(a) (4310)5(b) (123)8(c) (2F A)16(d) (212)33. What is the largest binary number that can be expressed with:(a) 8 bits,(b) 10 bits,(c) 16 bits.In each case, write their decimal and hexadecimal equivalents.4. Determine the base of the numbers for the following operation to be correct: 54/4 = 135. Convert the hexadecimal number 68BE to binary, and then convert it from binary to Octal.6. Convert the decimal number 431 to binary in two ways:(a) Convert directly to binary.∗Engr. Sheraz Ali Khan, PhD 1 (b) First convert it into hexadecimal and then from hexadecimal to binary. Which is faster in youropinion?7. Express the following numbers in decimal:(a) (10110.0101)2(b) (26.24)8(c) (F AF A.B)168. Solve the following conversion problems:(a) Convert the decimal number 27.315 to binary.(b) Calculate the binary equivalent of 2/3 to eight places after the binary point.…
- 8. Add the following two 8-bit binary numbers, producing an 8-bit result. Indicate the status of the carry and overflow bits at the end of the addition by circling the appropriate choices. The space in between is only for readability. 1111 0010 + 1101 0110 ----------- Overflow? Yes or No Carry? Yes or No2. Write the normalized floating-point representation of (+ 33.025)10. Assume 16 bits to represent mantissa and 8 bits to represent exponents. Compare 84-2-1and 8421 code. Draw a figure for five bits odd parity generator and parity checker.Perform the following additions and subtractions. Assume the numbers arestored in hexadecimal representation. 74F – D63E Perform the following hexadecimal additions and subtractions. Assume thenumbers are stored in 32-bit 2’s complement binary numbers. Indicate the sign ofthe answer and whether overflow occurs. E9B20F5D – FE605C8D

