1. A polynomial can be represented as a linked list, where each node called a polyNode contains the coefficient and the exponent of a term of the polynomial. For example, the polynomial 4x³ + 3x²-5 would be represented as the linked list: 43 I 3 L -50 - 5xo 2 7. 4x3 3x² Write a Polynomial class that has methods for creating a polynomial, reading and writing a polynomial, and adding a pair of polymomials. In order to add 2 polynomials, traverse both lists. If a particular exponent value is present in either one, it should also be present in the resulting polynomial unless its coefficient is zero.
1. A polynomial can be represented as a linked list, where each node called a polyNode contains the coefficient and the exponent of a term of the polynomial. For example, the polynomial 4x³ + 3x²-5 would be represented as the linked list: 43 I 3 L -50 - 5xo 2 7. 4x3 3x² Write a Polynomial class that has methods for creating a polynomial, reading and writing a polynomial, and adding a pair of polymomials. In order to add 2 polynomials, traverse both lists. If a particular exponent value is present in either one, it should also be present in the resulting polynomial unless its coefficient is zero.
Chapter11: Advanced Inheritance Concepts
Section: Chapter Questions
Problem 3PE
Related questions
Question
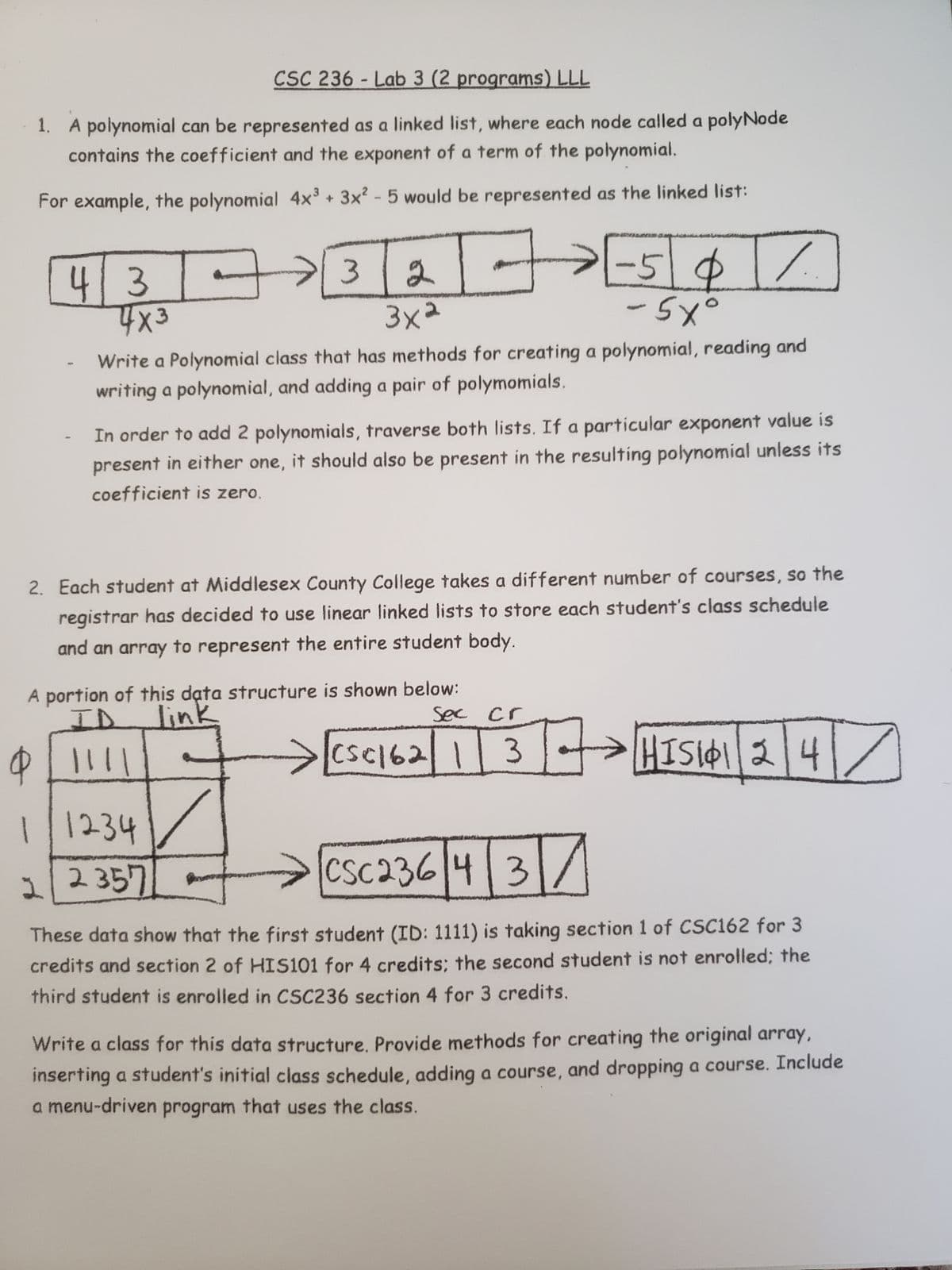
Transcribed Image Text:CSC 236-Lab 3 (2 programs) LLL
1. A polynomial can be represented as a linked list, where each node called a polyNode
contains the coefficient and the exponent of a term of the polynomial.
For example, the polynomial 4x³ + 3x² - 5 would be represented as the linked list:
43-
4x3
●
-
3
2
3x²
3
1/1234
22357
A portion of this data structure is shown below:
I
link
9 LI!!!
Write a Polynomial class that has methods for creating a polynomial, reading and
writing a polynomial, and adding a pair of polymomials.
→
In order to add 2 polynomials, traverse both lists. If a particular exponent value is
present in either one, it should also be present in the resulting polynomial unless its
coefficient is zero.
-50
- 5xo
2. Each student at Middlesex County College takes a different number of courses, so the
registrar has decided to use linear linked lists to store each student's class schedule
and an array to represent the entire student body.
Sec cr
%
CSC1621 3
37 HIS141|2|4|7
CSC23643/
These data show that the first student (ID: 1111) is taking section 1 of CSC162 for 3
credits and section 2 of HIS101 for 4 credits; the second student is not enrolled; the
third student is enrolled in CSC236 section 4 for 3 credits.
Write a class for this data structure. Provide methods for creating the original array,
inserting a student's initial class schedule, adding a course, and dropping a course. Include
a menu-driven program that uses the class.
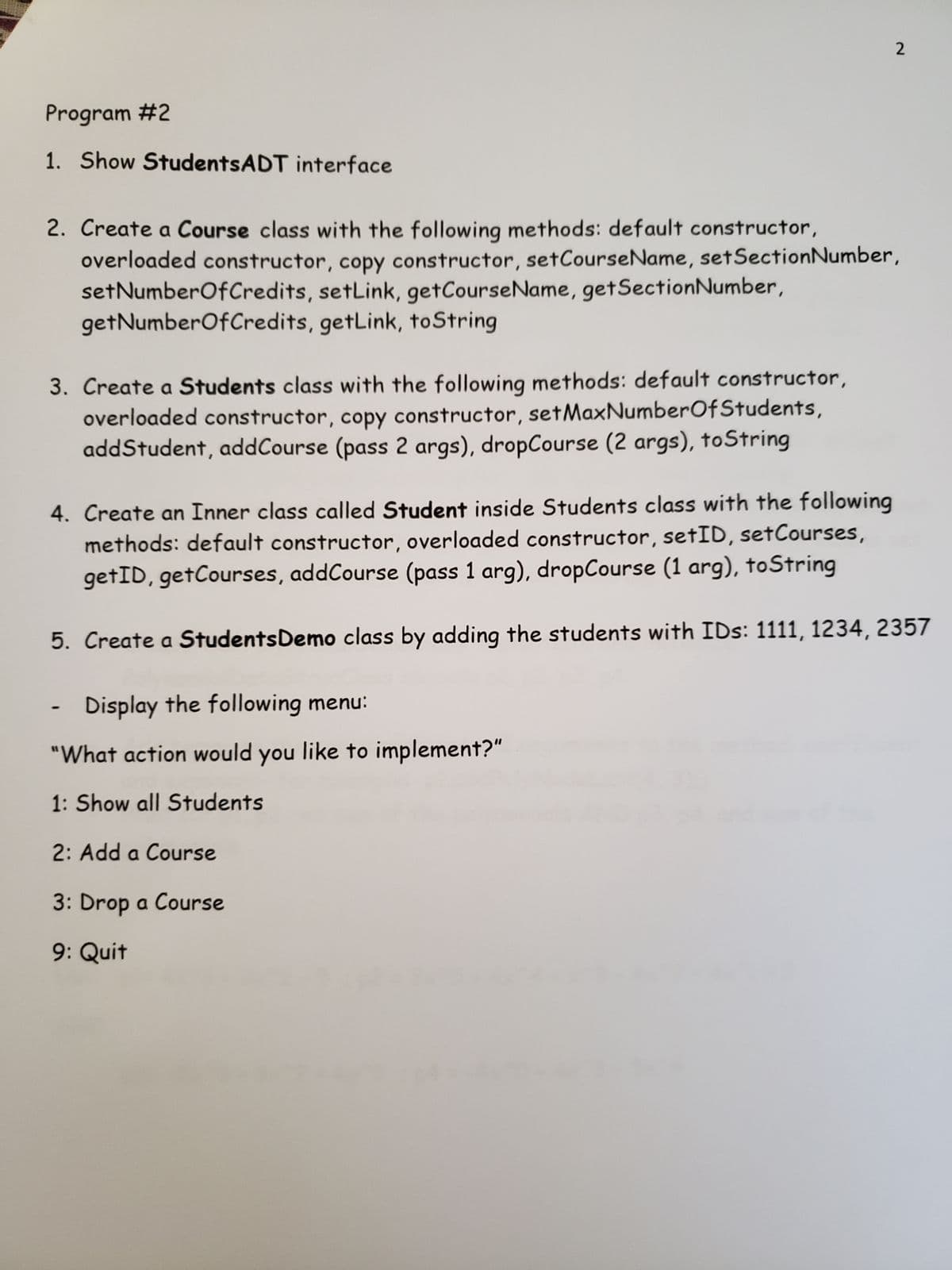
Transcribed Image Text:Program #2
1. Show StudentsADT interface
2
2. Create a Course class with the following methods: default constructor,
overloaded constructor, copy constructor, set Course Name, set Section Number,
set NumberOfCredits, setLink, get CourseName, getSection Number,
getNumberOfCredits, getLink, toString
3. Create a Students class with the following methods: default constructor,
overloaded constructor, copy constructor, setMaxNumber Of Students,
addStudent, addCourse (pass 2 args), dropCourse (2 args), toString
4. Create an Inner class called Student inside Students class with the following
methods: default constructor, overloaded constructor, setID, setCourses,
getID, getCourses, addCourse (pass 1 arg), dropCourse (1 arg), toString
5. Create a Students Demo class by adding the students with IDs: 1111, 1234, 2357
Display the following menu:
"What action would you like to implement?"
1: Show all Students
2: Add a Course
3: Drop a Course
9: Quit
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 4 steps with 5 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT