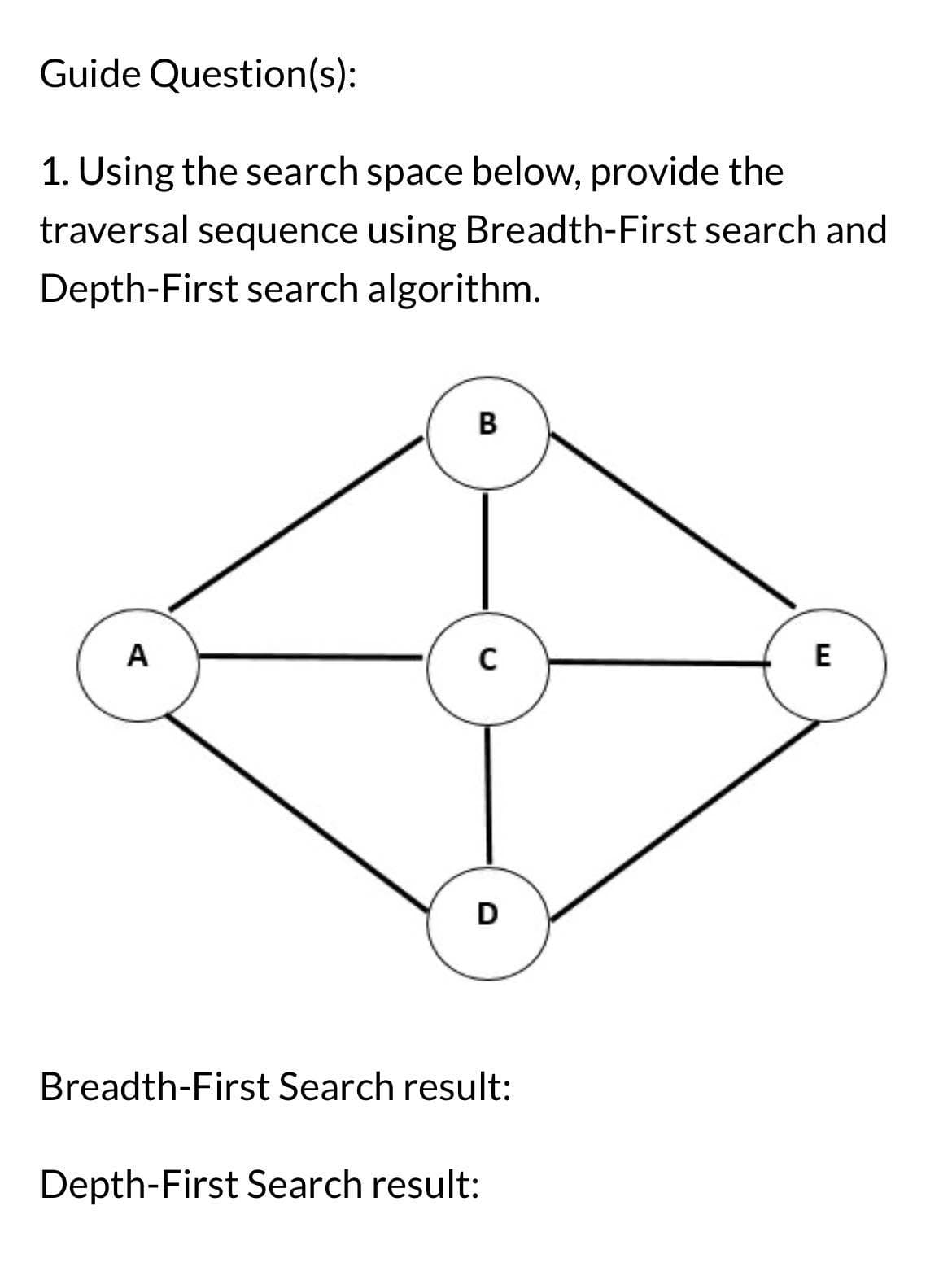
1. Using the search space below, provide the traversal sequence using Breadth-First search and Depth-First search algorithm. A B C D Breadth-First Search result: Depth-First Search result: E
Q: Explain the operating system's base, starting with the basic parts and working up to the most…
A: Explain the operating system's base, starting with the basic parts and working up to the most…
Q: Where is the screenshot of the terminal? How do I know whether this code works completely? I need to…
A: The code is changed a bit to show an output in the terminal.Also screenshot is attached
Q: Using Hamming(7.4) 1. Check if code 1101001 has errors and if so, indicate the position of the…
A: Hamming refers to a family of error-correcting codes developed by Richard Hamming in the 1940s.…
Q: III-Write an algo program that allows to To Create an array TAB containing 7 integers. b. Fill the…
A: In this exercise, we'll be exploring how to work with arrays in Python. Arrays are a fundamental…
Q: 2. Map this BANK ER diagram into relational database tables. Specify all tables, attributes, primary…
A: A relational schema is an outline that shows how companies store and organize information within a…
Q: Describe the many Software Configuration Management principles.
A: This question dives into the principles of Software Configuration Management (SCM). SCM is a…
Q: Which of the following is not part of the database infrastructure A) High Availability B)…
A: The term "database infrastructure" refers to the underlying components and resources that support…
Q: Discuss the evolution of computing, the current instruments we use, and the potential future of the…
A: The journey of computing is a remarkable one. Early computational devices like the abacus existed…
Q: Examples define real-time operating systems. What differentiates this OS? Real-time operating…
A: What is RTOS: RTOS stands for Real-Time Operating System. It is an operating system specifically…
Q: Replace any alphabetic character within 2-character string passCode. Ex: If passCode is "9a", output…
A: #include <stdio.h>#include <string.h>#include <ctype.h>int main(void) {char…
Q: Introduce real-time operating systems before examining particular cases. Compare it to a standard OS…
A: The word "real-time in service organization" (or "RTOS") refers inside the direction of a special…
Q: Exists anything that could impede a satisfactory performance compromise among the central processing…
A: The CPU, the heart of a computer system, shows a substantial role in determining the system's…
Q: (a) Consider the decimal number 701. Explain and show how to write this number in binary. (b)…
A: In further steps , I have provided all 3 answers with explanation
Q: Mathematical logic Is (((P→Q→P)→P) a tautology?
A: According to the information given:-We haev to define the statement
Q: Create a fully-developed use case description for the use case Find caterer. Follow the template…
A: The case study mentions that caterers pay to use the WPE system through purchasing credits using…
Q: Please tell us what you found out about software development process data. Everything needs to be…
A: Software development is a complex and iterative process that involves the creation, deployment, and…
Q: How does dynamic memory placement mean "memory leaks?"
A: What is memory leaks: Memory leaks refer to the situation where dynamically allocated memory is not…
Q: Give examples of different computer systems.
A: Here are examples of different computer systems based on their form factor, purpose, and usage:1.…
Q: Memory is not like virtual machines. How do business goals compare? What are the pros and cons of…
A: Virtual memory:It is an Operating system feature which allows a computer to compensate for physical…
Q: Describe the origins of computer systems, how they have evolved technologically, and their…
A: The origins of computer systems can be traced back to the early 19th century with the development of…
Q: Why is it good to go through the Compiler Phases? For each level, explain it and give an example…
A: Understanding the process of compiling code is essential for programmers and software developers
Q: If you use cloud computing instead of running your own computers and networks, there are a number of…
A: Cloud computing offers numerous advantages over traditional methods of running individual computers…
Q: Explain the various phases of software configuration management and differentiate baseline version…
A: What is software configuration management: Software Configuration Management (SCM) is the process of…
Q: Describe the TM that accepts the language, L = {w = {a,b,c}* | w contains equal number of a's, b's…
A: The language is generating six types of string and a, b, c can be in any order but contains equal…
Q: What does it mean exactly to be "networking"? What are some good and bad things about using this…
A: In this answer, we’ll discuss about networking and some good and bad things about using networking.
Q: Could you give more information about the CSRF attack?
A: Cross-Site Request Forgery (CSRF) is a malicious website use someplace criminal information is…
Q: Where does a computer need to be in order to work?
A: a computer needs the following to work:Access to electricity or a power source.Properly installed…
Q: Virtualization is the best technique to run several OSes. Regardless of your feelings, explain the…
A: According to the information given:-We have to define Virtualization is the best technique to run…
Q: 2-Displaye the name Nd department number of all employees working in departments 10 and 30 in…
A: According to the Bartleby guideline, we are supposed to answer only first 3 similar question at a…
Q: How much do people matter when it comes to computer networks?
A: One of the essential elements of computer networking is people. They significantly contribute to…
Q: Give examples of different computer systems.
A: This question investigates the different scope of computer systems accessible in the present…
Q: Exists anything that could impede a satisfactory performance compromise among the central processing…
A: A computer system's performance is a key component in determining whether it can handle the demands…
Q: Draw an activity diagram to represent the flow of activities for the use case Print credit payments…
A: Here is an activity diagram that represents the flow of activities for the use case "Print Credit…
Q: Read up on any innovative technology using NLP (by companies such as Google or IBM, for instance)…
A: One innovative technology that utilizes Natural Language Processing (NLP) is the Smart Reply feature…
Q: Based on the understanding you have obtained about numerical estimation methods, critically evaluate…
A: The critical analysis examines the strengths, limitations, and real-life applications of numerical…
Q: Explain how computer science project management software can be beneficial. As per the client's…
A: Happening computer science, achieving projects effectively exists critical pro successful software…
Q: Give a short explanation of what information system tasks are, and then use cases from your company…
A: What is information system: An information system is a collection of hardware, software, data,…
Q: How are computers distinctive?
A: Computers are distinctive in several ways which set them apart from other devices and make them…
Q: The method for automating growth needs to be figured out.
A: Depending on the situation and objectives of the company, the broad idea of automating growth may…
Q: ublic static int gcd(int a, int b) { BigInteger b1 = BigInteger.valueOf(a);…
A: The code you provided is a Java program that finds the greatest common divisor (GCD) of two numbers.…
Q: To explain what a real-time operating system is, you can use examples. How is this operating system…
A: An operating system is a product that goes about as an intermediary between PC hardware and client…
Q: ter, but its software regulates the physical components that perform its operations. It's a method…
A: The given statement describes a particular entity and provides some characteristics or features…
Q: Please convert following figure into a relational schema. In each table, the primary key and foreign…
A: Hello studentGreetingsIn the given diagram, the entity BankBranch is a weak entity and therefore we…
Q: Please draw a diagram of the visual representation
A: The visual representation of firm management that contains cloud based software and website contains…
Q: Find a server-based programme online or in old Computerworld issues. After reading, why do you…
A: A server-based computing environment is chosen by companies for a variety of reasons. The most…
Q: Computer networks A "data collision" occurs when several senders access the same material. How can…
A: Data collision in processor networks is at what time two or additional data packet vie for The same…
Q: Describe the operating system's kernel from the simplest to the most complex components.
A: 1) An operating system kernel is the core component of an operating system that acts as an…
Q: CHALLENGE 3.16.2: Conditional expression: Print negative or positive. ACTIVITY Create a conditional…
A: Start the program.Declare the variables userVal as an integer to store the user input and condStr as…
Q: Create a list of the numerous components that comprise a typical operating system and briefly…
A: An (OS) is fundamental to any computer organization It serves as an boundary sandwiched between the…
Q: Which firewall management strategies are suggested? Explain.
A: What is Firewall: A firewall is a network security device that monitors and controls network traffic…
1
Step by step
Solved in 4 steps

- To what kinds of tasks may one use the Depth First Search technique?Explain how AI is used in Google Search with emphasis on indexing and relevancy sortingExplain the concept of semantic search and how it differs from traditional keyword-based search. Discuss its impact on search engine algorithms and results.
- How does the use of synonyms and semantic similarity algorithms enhance keyword-based search results?Please solve with the computer Explain in detail about Search Engine Indexing.Sorting algorithms are one kind of algorithm whose performance may depend upon the data. Choose one of the sorting algorithms or any other algorithm and explain whether the there are any differences in the best, average and worst cases. If there are no differences, explain why not. If there are differences, describe the data in the different cases and explain how the performance differs in each case.-Use course material cmsc and additional sources. Please provide reference at the end must and donot copy from other sites please
- Explain informed search strategies with example.Calculate the number of comparisons that were made for the provided data list and search list when I a transpose sequential search and ii) an interpolation search were conducted on the search list's keys.Pin, ink, pen, clip, ribbon, eraser, duster, chalk, pencil, paper, stapler, pot, weight, and calculator are among the data listed.Pen, clip, paper, calculator, pen, on the search listExplain the role of keywords in information retrieval systems, including their use in search engines, document retrieval, and knowledge management. How have modern search engines evolved beyond basic keyword matching?
- How do library subscription databases differ from well-known search engines like Google when it comes to completing research?How do well-known search engines like Google compare to the subscription databases that are available via the library when it comes to doing research?Why do today's Internet Web applications and smartphone apps need databases?

