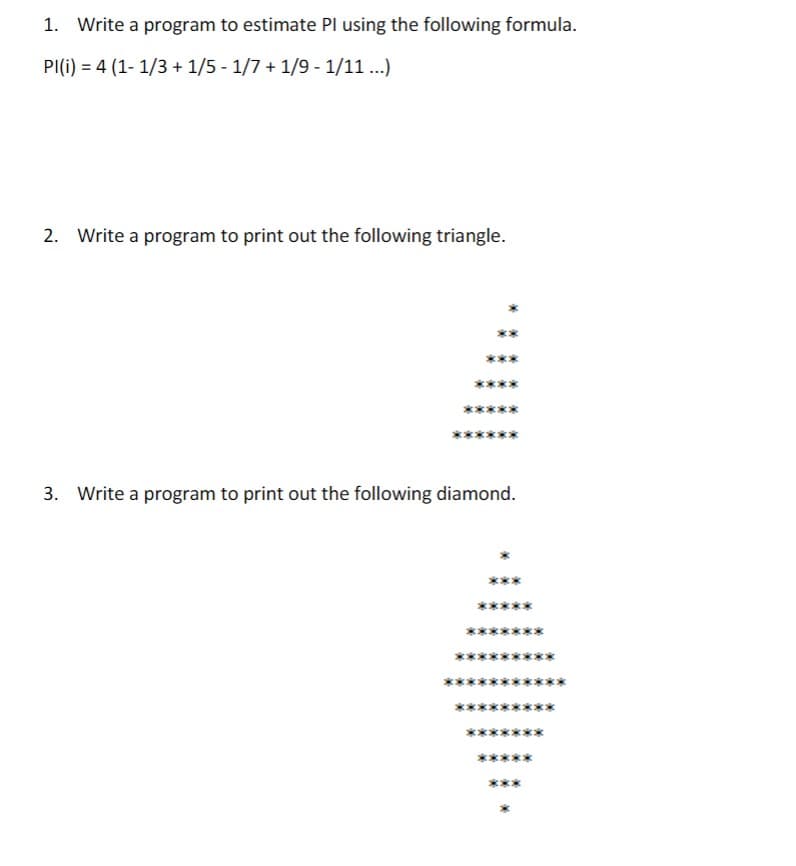
1. Write a program to estimate Pl using the following formula. PI(i) = 4 (1-1/3 + 1/5 - 1/7 + 1/9 - 1/11...) 2. Write a program to print out the following triangle. 3. Write a program to print out the following diamond.
Q: (Python) Plot the following functions and identify all cross-over points between all these functions
A: In this question we have to write a python program to plot this function in a graph and find the…
Q: What makes a fiber-coaxial network different from a standard one?
A: What makes a fiber-coaxial network different from a standard one answer in below step.
Q: I was hoping you could give me a quick rundown of the history of computing, touching on the major…
A: Introduction: Computing has a rich history that has shaped and revolutionized the way we live, work,…
Q: For instance, if you are starting a media firm and want to hire graphic designers and media…
A: Employee recruitment is an essential part of any business, and it is especially important when…
Q: What are the advantages of doing data analysis and storing data on the cloud?
A: Simply put, cloud computing is the provision of computing services such as servers, storage,…
Q: What does email look like in your mind? Which form of email sending is the most efficient? Note your…
A: Email is sent across computer networks, primarily the internet and local area networks. Lists and…
Q: The layered design of an OS may be stated as follows: If you have any thoughts on this method, I'd…
A: The operating system's layered architecture is a system structure. The operating system's services…
Q: When people talk about having a "memory vacuum," how do they mean it? Why does it happen, and how…
A: operating system verifies the memory access and aborts the program if it is invalid.
Q: What sets software engineering different from other technical specializations?
A: What sets software engineering different from other technical specializations answer in below step.
Q: C++ please 3.9.3: Populating a vector with a for loop. Write a for loop to populate vector…
A: Here's an example of populating a 'vector' in C++ with a 'for' loop and reading integers from 'cin'…
Q: Analyze how the Little Man computer differs from the Von Neumann design. Tell me how the various…
A: The solution is given in the below step
Q: As part of this task, you will need to investigate common anti-patterns and develop a list of them,…
A: Definition of Anti-pattern: Anti-patterns involve both failing to do the correct thing and making…
Q: Metrics are being used to assess the software quality process and product, which has to be made…
A: Software metric A software metric is a program's quantifiable or countable property. In addition to…
Q: In the course of your daily activities, do you make use of databases or applications that make use…
A: In order to make data accessible and valuable for users, databases play a critical role in storing…
Q: You are given an array with all the numbers from 1 to N appearing exactly once, except for one…
A: 1. Programming is the process of creating a set of instructions that tells a computer how to perform…
Q: C++ Need help with the functions While testing I am not getting the count for the vowles and…
A: Please refer to the following steps for the complete solution to the problem above.
Q: Do you believe that there are risks involved with the use of cloud computing in financial systems,…
A: Explanation: Existing cloud goods are basically public, exposing the system to a bigger number of…
Q: Explain why one method of communication is more successful than another by comparing and contrasting…
A: The given question asks for a comparison and contrast between two methods of communication and an…
Q: Write a C++ function weird_sum that takes two integer parameters, n1 and n2. The function…
A: Algorithm: 1. Start 2. Prompt the user for two integers, n1, and n2. 3. Calculate the sum of n1 and…
Q: which encoding technique uses the least amount of time and space? Is there a particular high-speed…
A: Encoding technique and data transfer protocol that uses the least amount of time and space that is…
Q: It is essential to do research on wireless network infrastructure in developing nations. Due to the…
A: Wireless network infrastructure can be a desirable choice for supplying connection in poor countries…
Q: Which three of the following are instances of discrete event simulations?
A: The act of codifying the behaviour of a complex system into an ordered set of well-defined events is…
Q: To demonstrate that you are aware of the importance of this topic, could you write up or come up…
A: Given: It not only helps to prevent mistakes and flaws from being introduced into the software that…
Q: Which components make up an ADT, and what kinds of materials are used? Please provide your comment…
A: HI THEREI AM ADDING ASNWER BELOWPLEASE GO THROUGH ITTHANK YOU
Q: We can wonder why we need cache memory since we already have RAM, which is a volatile memory similar…
A: cache is important because it improves the efficiency of data retrieval. cache is an extremely fast…
Q: Create a program that calculates the total cost of a restaurant bill, including tax and tip.…
A: Introduction In a simple# program, we use System. System is the namespace and Console is the class…
Q: What makes a fiber-coaxial network different from a standard one?
A: HI THEREI AM ADDING ASNWER BELOWPLEASE GO THROUGH ITTHANK YOU
Q: This is syllabus for question in the given picture Course: Data Base Administration Module No. 1…
A: Module No. 1: Introduction to database architectures and database management systems: This module…
Q: Identify the three instances of discrete event simulation from the list below.
A: The answer is given below step.
Q: In your opinion, which facet of the software engineering profession is the most important, and why?
A: Introduction: The question concerns severe challenges in the subject of software engineering, and…
Q: List and discuss the pros and cons of the various online communication methods, keeping in mind how…
A: Globalization and the rise of business collaboration worldwide mean that online communication is no…
Q: Paul needs to read and write some documents. In the following, assume the system security policy is…
A: System security: System security refers to the measures taken to protect computer systems and the…
Q: what exactly are the OS's primary building blocks?
A: The primary building blocks of an Operating System (OS) include: Kernel: The core component of an…
Q: "Save and forward" is no longer used in everyday communications. Look through the mechanics.
A: "Save and forward" is no longer used in everyday communications. Look through the mechanics answer…
Q: When creating web applications, how important is the Model-View-Controller pattern? What are the…
A: The Model-View-Controller (MVC) pattern is a widely used design pattern in web application…
Q: What is the difference between dynamic binding of C++ and Java?
A: Dynamic binding refers to the process of linking a function call to the actual code to be executed…
Q: People may experience significant inconvenience as a result of a malfunctioning piece of software.…
A: I've included things to look out for in the programme before it's released, as well as things that…
Q: round on the evolution of co
A: Introduction: The foremost people employed the first counting system. They counted with sticks,…
Q: Metrics are being used to assess the software quality process and product, which has to be made…
A: Start: A subset of programming metrics called software quality metrics focuses on the qualities of…
Q: any two means of transmission (twistted piars, coxial cable, microwave, satalitte, fiber optical).
A: Media of Transmission: The repeater is the series circuit that associates the transmitter and…
Q: You are given an array with all the numbers from 1 to N appearing exactly once, except for one…
A: Given an array containing all the numbers from 1 to N, except for one missing number, the task is to…
Q: Why would a firm prefer closed-source encryption technologies over open-source cryptography?
A: Encryption is a critical component of modern technology that helps to secure sensitive information…
Q: Individuals and computers located in the same area are able to connect with one another via the use…
A: Introduction: What we call a LAN is shorthand for a "local area network."A LAN is a computer network…
Q: Accessible resources for cloud computing are listed. Which organizations conduct their activities…
A: The term "cloud computing" refers to the on-demand provision of computer services, which may include…
Q: In what four different ways is discrete event simulation capable of being depicted as critical?
A: Each associated event in the process occurs at a certain moment. The event's occurrence is what…
Q: Which four benefits of discrete event simulation are most notable?
A: Introduction: Discrete event simulation is a modeling technique used to simulate the behavior of…
Q: Many variables affect how well a network can exchange information with one another.
A: The following are major elements that have a significant impact on the ability of a network to…
Q: Do you, as an analyst, have any experience with computer system design strategies?
A: What is a Good System Design Strategy? A system design approach in software engineering often refers…
Q: Further details on the criteria used to rate the product's quality as well procedure would be of…
A: A software metric is a characteristic of a program that can be measured or counted.Program metrics…
Q: What is the multifactor identification procedure? What security precautions does it take to guard…
A: 1. Encryption is the study of secure communication techniques that allow only the sender and…
finish assignments C#
Trending now
This is a popular solution!
Step by step
Solved in 6 steps with 2 images

- Translate the statement into equation: When three is multiplied by one less than a number x, the result is 10 less than 5 times the number x.Write a program that plots the sine function, as shown in Figure 5.5a.(Mechanics) The deflection at any point along the centerline of a cantilevered beam, such as the one used for a balcony (see Figure 5.15), when a load is distributed evenly along the beam is given by this formula: d=wx224EI(x2+6l24lx) d is the deflection at location x (ft). xisthedistancefromthesecuredend( ft).wistheweightplacedattheendofthebeam( lbs/ft).listhebeamlength( ft). Eisthemodulesofelasticity( lbs/f t 2 ).Iisthesecondmomentofinertia( f t 4 ). For the beam shown in Figure 5.15, the second moment of inertia is determined as follows: l=bh312 b is the beam’s base. h is the beam’s height. Using these formulas, write, compile, and run a C++ program that determines and displays a table of the deflection for a cantilevered pine beam at half-foot increments along its length, using the following data: w=200lbs/ftl=3ftE=187.2106lb/ft2b=.2fth=.3ft
- Write a program that asks the user to enter two numbers and print the sum, difference, product and quotient. using c ++vi) In C# programming language, create a program to take input three integers x, y, and z and print their product in the output.iii) In C# language, write a program to take input three integers x, y, and z and print their product in the output.
- Develop pseudocode to read in a sphere's radius, compute the volume of the sphere (using the formula volume = 4 * * r3 / 3), then print out both the radius and the volume.Construct a truth table for the statements belowa. (p ∧ q) ∧ (~r ∨ q).b. ~[~p ∧ (q ∧ r)]c. [p ∧ (q ∨ ~p)] → ~p then find the truth value of the statement givena. p is a false statement, q is a true statement and r is a true statement.b. p is a false statement, q is a false statement and r is a false statement.c. p is a false statement, q is a false statement and r is a true statement.Write a c++ program to calculate the area of a triangle with side a,b and c
- 77. What is the value of the following expression:8/4/2, 8/(4/2) a. (1.0, 4.0) b. (1.0, 1.0) c. (4.0. 1.0) d. (4.0, 4.0)Write program segments that accomplish " Calculate the integer remainder when integer a is divided by integer b ."write a program is to calculate and display the volume of cone with given the value for the diameter and height of the cone.



