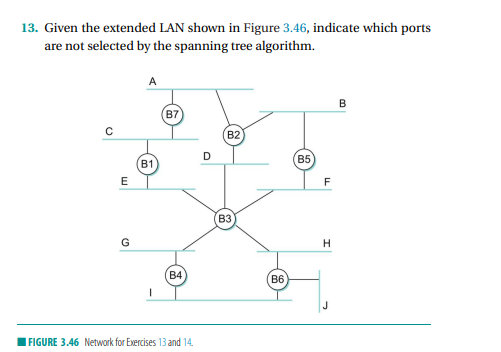
13. Given the extended LAN shown in Figure 3.46, indicate which ports are not selected by the spanning tree algorithm. E B1 B7 B4 D B2 B3 B6 B5 F H
Q: Why would your company pick high-availability DHCP? What's best? Any drawbacks? What makes it…
A: The setup of several DHCP servers to continually offer network configuration and IP address…
Q: Explain what a "hot zone" is and how it works, and talk about any problems it might have.
A: A "hot zone" in computer networking is a public area where Wi-Fi wireless open is provided, often by…
Q: The central processing unit's clock speed can't be changed after it has been made. This is like not…
A: Yes , The clock speed of a central processing unit (CPU) cannot be changed after it has been…
Q: What makes Compiler Phases different from other similar tools? At each level, you should give clear…
A: Compiler phases play a distinct role in the process of converting source code into executable…
Q: How do you determine the network's dependability, and what methods do you use to make this…
A: What is network's dependability: The network's dependability refers to its reliability,…
Q: Why is it good to go through the Compiler Phases? For each level, explain it and give an example…
A: Going through the phases of a compiler is beneficial for several reasons. The compilation process is…
Q: One phrase describes operating system components and their functions.
A: Operating systems are made up of numerous parts, each of which has a distinct purpose in ensuring…
Q: Give an example of a buffer overflow in C • The code below contains a simple example of an overrun…
A:
Q: Code_Method to check if x is power of 2*/ static boolean isPowerOfTwo (int x) { /* First x in…
A: Given code:static boolean isPowerOfTwo (int x){ /* First x in the below expression is for…
Q: How do context switch time and interrupt delay relate to each other?
A: Although they reflect separate facets of system performance, context switch time and interrupt delay…
Q: To explain what a real-time operating system is, you can use examples. How is this operating system…
A: An operating system is a product that goes about as an intermediary between PC hardware and client…
Q: I'm interested in learning Python, so it would be great if you could give me some detailed advice.
A: Python is a very adaptable charming talk that's used in a open array of works. It's known for its…
Q: How does dynamic memory placement mean "memory leaks?"
A: What is memory leaks: Memory leaks refer to the situation where dynamically allocated memory is not…
Q: Find the angular velocity from velocity and radius in python
A: Required:-Find the angular velocity from velocity and radius in pythonApproach:-Take the velocity…
Q: cent StuffDOT initiatives increased usability?
A: StuffDOT is an online platform that allows users to curate and share their favorite products.…
Q: Explain the different steps of software configuration management and the difference between basic…
A: Software configuration management (SCM) is an important process in software development that…
Q: Method to check if x is power of 2*/ static boolean isPowerOfTwo (int x) { /* First x in the…
A: The provided code is a method written in Java to check if a given integer x is a power of 2. Here's…
Q: In kernel-space threads, can two threads (in the same process) synchronize using a kernel semaphore?…
A: kernel semaphore is a synchronization object provided by the operating system kernel. It allows…
Q: Mobile app development: what should be considered?
A: Choosing the accurate platform for your app is crucial and often depends on your goal audience's…
Q: When a business uses BI tools and data, what kinds of ethics and security problems could it face?
A: BI tools, short for Business Intelligence tools, are software applications and technologies that…
Q: Define bounded summation and explain its significance in algorithm analysis.
A: Bounded summation is a concept used in algorithm analysis to describe the behavior and complexity of…
Q: How important is data security? Which security mechanism should be utilised when data integrity and…
A: In today's digital environment, data security is of the utmost significance. Data protection is…
Q: The blue part of this diagram is filled with code, and the right side is the result of the run.just…
A: I have provided COMPLETE HTML CODE along with OUTPUT SCREENSHOT----------Note: I have explaine…
Q: What are three technology controls that can be used to improve the security of the transport layer?
A: In order to increase the security of the transport layer, it is essential to implement reliable…
Q: mplement a stack data structure in Java and demonstrate its usage by performing the following…
A: Linear data structures that adhere to the Last-In-First-Out (LIFO) concept include stacks. The term…
Q: 3 1 2 3 4 5 6 7 8 9 10 2 4 6 8 10 12 14 16 18 20 6 9 12 15 18 21 24 27 30 4 8 12 16 20 24 28 32 36…
A: The complete code is given below with output screenshot
Q: How can technology be used to stop people from looking over your shoulder on a laptop?
A: In today's digital age, the use of laptops and other personal electronic devices has become…
Q: Which kind of is optimal for SIMD? What kind of parallelism does MIMD excel at? parallelism (data or…
A: Data parallelism refers to the execution of the same operation or instruction on multiple data…
Q: During your computer science class, you were told to make a link between the parts of…
A: In a computer science class, you were assigned the task of establishing a connection between the…
Q: Tell me about the business method you plan to use.
A: What is business method plan: Apologies for any confusion, but there is no specific term "business…
Q: Write down the pros and cons of using the star shape instead of the snowflake shape. Which is odder?
A: The terms "star schema" and "snowflake schema" are used in the context of data warehousing. These…
Q: What kind of security strategy would be the most effective at stopping attacks on purpose if…
A: In today's digital age, organizations face numerous challenges in protecting their sensitive data…
Q: Can cloud computing benefit your business? Cloud use safe? Risks and drawbacks? Do cloud computing's…
A: Cloud computing has come out as a critical reply for businesses aim to make more efficient their…
Q: There must be a record of the FTP port numbers. Is it true that FTP sends "out of band" (away from…
A: FTP (File Transmission Protocol) is a frequently employed protocol for file transmission over a…
Q: ell me about the business method you plan to use.
A: A business method or strategy is a plan of action that a company implements in order to attain its…
Q: Write a php program to take the current room temperature from the user in degree celsius and try to…
A: Required:-Write a PHP program to take the current room temperature from the user in degree celsius…
Q: How would you explain DFDs?
A: Data Flow Diagrams (DFDs) be graphical tools within system analysis plus design, chiefly in software…
Q: How exactly does a database management system get normalised?
A: Database normalization is a fundamental aspect of database design that aims to minimize data…
Q: Why would your company pick high-availability DHCP? What's best? Any drawbacks? What makes it…
A: High availability DHCP dynamic host configuration protocol is a solution that ensures uninterrupted…
Q: Multiple ways to keep track of how info flows?
A: Structures similar to trees, graph, queue, stacks, and plants are all instance of data Structure.It…
Q: In Java, objects are explicitly deallocated from the stack. True False
A: In the Java programming language, memory management is handled by the Java Virtual Machine (JVM)…
Q: To put it simply, how much room does a computer need?
A: When it comes to computers, the amount of physical space they require is an essential consideration.…
Q: discuss how to creat a non-executable stac and disuss the stack's exploitable weaknesses
A: Creating a non-executable stack involves implementing a security measure that prevents the execution…
Q: Which hardware permits direct network connection
A: Many hardware and devices support direct connection. Here are some examples:Network Interface Card…
Q: I'd want some real-world examples to assist me comprehend the distinctions between digital piracy…
A: Understanding the distinctions between digital piracy and intellectual property infringement is…
Q: Identify what can directly access and change the value of the variable res. Package…
A: The following options determine which entities can directly access and change the value of the…
Q: I'm interested in learning Python, so it would be great if you could give me some detailed advice.
A: Python is a popular and versatile programming language that is widely used for a variety of…
Q: Discuss business intelligence implementation challenges?
A: Implementation challenges that organizations face when adopting business intelligence (BI) systems.…
Q: Please do not give solution in image formate thanku Readthe following scenario which contains…
A: The questionnaire aims to gather feedback from customers who have used the Mobile Application…
Q: How do context switch time and interrupt delay work together?
A: In a multitasking system, context switching is a critical process that efficiently shares CPU…
Computer science
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 1 images

- 1 . Given a Class B network, what is the length of the SubnetID and the HostID should be in order to get 100 subnets with each having 200 hosts? Hint: such question may have multiple answers, give all the possible answers57- A network for a local office requires 4 LAN subnets as follows: · Subnet A - North Office with 31 hosts; · Subnet B - East Office with 15 hosts; and · Subnet C - South Office with 7 hosts. · Subnet D – West Office with 4 hosts. Given the IP Address 192.168.15.0 /24 and above described network requirements: 1. Design an optimal address scheme using Variable Length Subnet Mask (VLSM) method; What will be the range of usable (assignable) host addresses in Subnet C? Select one: A. 192.168.15.64 to 192.168.15.128 B. 192.168.15.97 to 192.168.15.110 C. 192.168.15.140 to 192.168.15.191 D. 192.168.15.128 to 192.168.15.139 E. 192.168.15.193 to 192.168.15.254Switches make forwarding decisions: a. Using a routing table which maps IP addresses to specific ports b. Using the shortest path first algorithm and a topology database c. Using a look up database mapping IP addresses to MAC addresses d. Using a switching table which maps MAC addresses to specific ports
- 13.9 What is the purpose of an IP address mask? Suppose an IP address is identified as 222.44.66.88/24. What is the network address in this case? What is the host address? How many hosts can this network address support? Repeat this exercise for the IP address 200.40.60.80/26. 13.10 Explain the concept of a DHCP lease. How is it obtained? How is it used? What does it provide? 14.5 In recent years, much of the storage and communication of data has been in digital form, even if the source data is actually analog. Even most television is now transmitted digitally. What benefits and advantages are gained by using digital storage and signaling?52- A network for a local office requires 4 LAN subnets as follows: · Subnet A - North Office with 31 hosts; · Subnet B - East Office with 15 hosts; and · Subnet C - South Office with 7 hosts. · Subnet D – West Office with 4 hosts. Given the IP Address 192.168.15.0 /24 and above described network requirements: 1. Design an optimal address scheme using Variable Length Subnet Mask (VLSM) method; What will be the subnet mask of Subnet A? Select one: A. 255.255.255.192 B. 255.255.128.255 C. 255.255.255.128 D. 255.255.192.192 E. 255.255.192.058- A network for a local office requires 4 LAN subnets as follows: · Subnet A - North Office with 31 hosts; · Subnet B - East Office with 15 hosts; and · Subnet C - South Office with 7 hosts. · Subnet D – West Office with 4 hosts. Given the IP Address 192.168.15.0 /24 and above described network requirements: 1. Design an optimal address scheme using Variable Length Subnet Mask (VLSM) method What will be the network address of Subnet D? Select one: A. 192.168.15.232 B. 192.168.15.191 C. 192.168.15.112 D. 192.168.15.240
- 56- A network for a local office requires 4 LAN subnets as follows: · Subnet A - North Office with 31 hosts; · Subnet B - East Office with 15 hosts; and · Subnet C - South Office with 7 hosts. · Subnet D – West Office with 4 hosts. Given the IP Address 192.168.15.0 /24 and above described network requirements: 1. Design an optimal address scheme using Variable Length Subnet Mask (VLSM) method; What will be the subnet mask of Subnet C? Select one: A. 255.255.128.255 B. 255.255.192.0 C. 255.255.255.240 D. 255.255.255.192 E. 255.255.255.12853- A network for a local office requires 4 LAN subnets as follows: · Subnet A - North Office with 31 hosts; · Subnet B - East Office with 15 hosts; and · Subnet C - South Office with 7 hosts. · Subnet D – West Office with 4 hosts. Given the IP Address 192.168.15.0 /24 and above described network requirements: 1. Design an optimal address scheme using Variable Length Subnet Mask (VLSM) method; and What will be the network address of Subnet B? Select one: A. 192.168.15.64 B. 192.168.15.0 C. 192.168.15.32 D. 192.168.15.1QUESTION 27 The network portion of an IP address is the same for all the hosts on the same IP network. True False QUESTION 28 Ethernet and 802.11 use different frame structures. True False
- Short answer27. A company is assigned to an address block 136.23.12.64/26, now it needs to be further divided into four subnets of the same size. Question: (1) How long is the network prefix of each subnet? (2) How many addresses are there in each subnet? (3) What is the address block of each subnet? (4) What is the minimum address that each subnet can be assigned to a host? (5) What is the maximum address that each subnet can be assigned to a host?55- A network for a local office requires 4 LAN subnets as follows: · Subnet A - North Office with 31 hosts; · Subnet B - East Office with 15 hosts; and · Subnet C - South Office with 7 hosts. · Subnet D – West Office with 4 hosts. Given the IP Address 192.168.15.0 /24 and above described network requirements: 1. Design an optimal address scheme using Variable Length Subnet Mask (VLSM) method; What will be the network address of Subnet C? Select one: A. 192.16.15.128 B. 192.168.15.191 C. 192.168.15.96 D. 192.168.15.323.1 An end device was given the IP address of 198.168.4.35/28. Consider this address and indicate: 3.1.1 The network ID/address to which the host belongs. 3.1.2 The network broadcast address to which the host belongs. 3.1.3 The total number of hosts available in the network. 3.1.4 The total number of networks. 3.2 Consider two neighbours, Alice and Bob. Each have wireless IPv4 routers with integrated NAT. Each neighbour connects their laptop to their own wireless router, and each uses appropriate utilities to examine the IP address of each laptop. They realise the laptops have the same IP address. 3.2.1 How is that possible? 3.2.2 Justify one reason that wide-spread deployment of IPv6 would remove the need for the NAT devices.

