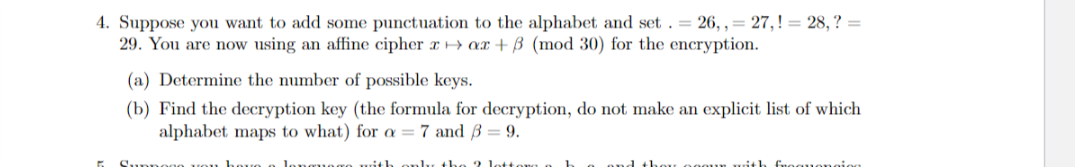
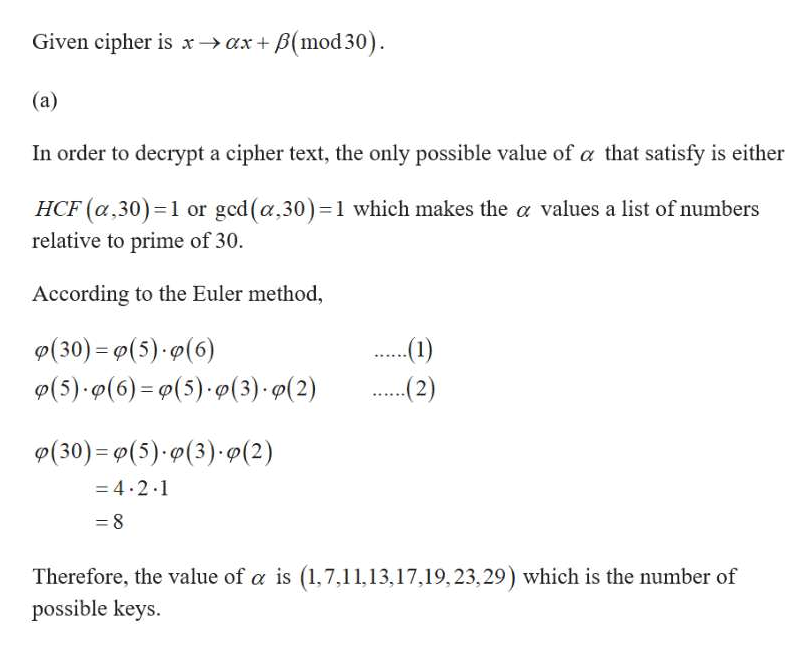
4. Suppose you want to add some punctuation to the alphabet and set . = 26, , = 27,! = 28, ? = 29. You are now using an affine cipher x > ax + B (mod 30) for the encryption. (a) Determine the number of possible keys. (b) Find the decryption key (the formula for decryption, do not make an explicit list of which alphabet maps to what) for a = 7 and ß = 9.
Q: Verify the following facts about Fibonacci number: If we make a list of any four consecutive…
A: Here the two different four number list of Fibonacci number with the property.
Q: if b is modulo m and a is another unit with a=b mod m, we say that d is the---------of a modulo m to…
A: As with such a large amount of concepts we are going to see, congruence is straightforward, perhaps…
Q: Without using Calculator or other mechanical tools, find the Decryption function of the following…
A: Given encryption function is : fp=7p+3 mod26
Q: If positive integers are chosen at random, what is the minimum number you must have in order to…
A:
Q: 1. If Alice uses the RSA modulus N = 77 and e=17, what is d? 2. Decrypt the message 5559 vising an…
A:
Q: Solve the following problems: (a) How many ways can a store manager arrange a group of 1 team leader…
A:
Q: Use 672 = -1 mod 449 and Hermites' algorithm to find a pair of positive integers s and t such that…
A: Given : s2 +t2 = 449672 = -1 mod449
Q: Alice wants to send to all her friends, including Bob, the message “SELL EVERYTHING” so that he…
A:
Q: . (a) How many quadratic residues are in the residue set Z19? (b) Determine if 4 and 9 are quadratic…
A: Introduction: Quadratic residue is a part of congruent modulo theory. It is a non-linear congruence.…
Q: In the use of RSA Cryptography, for the public key (11, 65), what is the decrypted original message…
A: Solution :-
Q: Consider the pseudorandom number generator given in our lessons: with Uf +1 = (auf + b) mod m…
A:
Q: Using Euclid's Algorithm, what is a multiplicative inverse of 23 mod 75 and then solve 23x is…
A:
Q: Suppose that message is to be encrypted using the formula c=9p mod 26. What is the formula that you…
A: The message p is encrypted as c using the formula, c≡9p (mod 26)
Q: The integers mod 5 (i.e., Z5) form a Boolean algebra, where - addition and multiplication are the…
A: The given question is solved below.
Q: Assume they are used for an encryption in Hill ciphers. In each case, find two plaintexts that…
A: The matrices given are as follows: 1322 and 131242351 For 1322 Let x1y1 and x2y2 be two plain…
Q: What is the secret message produced from the message “MEET YOU IN THE PARK” using the Caesar cipher?
A:
Q: (a) Suppose Alice and Bob use the simple encryption scheme in which c = (m + k) mod N and m = (c –…
A: Suppose Alice and Bob use the simple encryption scheme in whichc=m+kmodN and m=(c-k)modN. Suppose…
Q: Find integers X, E > 2 such that XE = X (mod 74329). How does this illustrate a potential problem in…
A: Given : E ≥ 2 such that XE ≡ X (mod 74329). To find integer X.
Q: npojd Assume that a person has ElGamal public key (2633, 3, 1138) and private key k = 965. If the…
A:
Q: Let (P, C, K, E, D) be a cryptosystem such that #K = #P = #C. Show that if this cryptosystem has…
A:
Q: Suppose that the most common letter and the second most common letter in a long ciphertext produced…
A:
Q: Once the length of the key string of a Vig`enere cipher is known, explain how to determine each of…
A: The length of the key's known. Let its k. therefore the text is going to be divided into groups of k…
Q: Alice wants to send to all her friends, including Bob, a message using the RSA cryptosystem. She…
A: a Number of ways Alice can choose an encryption key n,e is the number of ways Alice can choose e as…
Q: A department store wants to send codes for $15 off a $75 purchase to the subscribers of its…
A: The coupon code have three letters followed by one digit and followed by one letter. i.e. we have…
Q: Take the last four digits ABCD of your student identification number, and let AB and CD be the…
A:
Q: Books are identified by an International Standard Book Number (ISBN), a 10-digit code x1x2... x10,…
A:
Q: 5. Suppose you have a language with only the 3 letters a, b, c, and they occur with frequencies .7,…
A:
Q: Suppose a community of RSA users share the same encryption exponent e but each user i has their own…
A: Show that if k>e, then a cryptanalyst can recover the plaintext x without factoring any of the…
Q: Select the following statements that are true. The number of bit strings of length n that start with…
A: Option b,c and e are True
Q: Solve the following problems: (a) How many ways can a store manager arrange a group of 1 team…
A: a) No of ways to choose 4 from 25= 25C4 = 12650 No of ways to choose 1 from 3= 4C1 = 4 Therefore No…
Q: Suppose that (n, e) is an RSA encryption key, with n = pq, where p and q are large primes and gcd(e,…
A:
Q: What is the decryption function for an affine cipher if the encryption function is c = (15p + 13)…
A:
Q: (b) If the public key for an RSA cryptosystem is (N, e) = (69,5), find the private key d.
A: We follow the standard techniques use in the RSA algorithm. The detailed typeset solution is…
Q: (d) Devise a recursive algorithm for computing bn mod m, where b, n, and m are integers with m > 2,…
A:
Q: Ξ. Σ Suppose = {0, 1, 2, 3, ..., 34} is the alphabet for the affine cipher. Find the size of the…
A: Given, ∑=0, 1, 2, 3, . . . ,34 is the alphabet for the affine cipher.
Q: A sequence of pseudorandom numbers is generated as follows Xo = 4 x₁ = ( 6x₁-1 + 5 ) mod 13 if i > 0…
A:
Q: 1- A simple encryption method is being used to encrypt a small number (called the secret…
A: First of all, look for the condition that under this method when will secret number and the…
Q: 13, Let (n, e) = (16504217646971, 78893) be Alice's public key, where e represents the encryption…
A:
Q: If a (mod 0) = a, How would you interpret the congruence a ≡ b (mod 0)?
A: According to the given information, it is given that:
Q: Suppose the RSA system that is used for sending secret messages has private key (15, 3) and the…
A: Given that, private key=15,3 Cipher text=3
Q: ocibicur mic (a) A person with public key (31, 2, 22) and private key k = 17 wishes to sign a…
A:
Q: 14. Show that if x mod 8 = 6, then x mod 4 = 2, when x is an integer. Give an example. 15. Decrypt…
A: Given that x mod 8 =6 x mod 8=x-8n=6, Where n=1, 2, .... x=6+8n
Q: Find all pairs of integers keys (a, b) for affine ciphers for which the encryption function c = (ap…
A:
Q: Use the RSA cipher with public key (n, e) = (713, 43) to encrypt the word "TEE." Start by encoding…
A:
Q: (b) Solve the set of congruences 2x =1 (mod 5) x=3 (mod 4)
A: Note:- We’ll answer the first question according our protocol. Please submit a new question…
Q: 1. In the Diffie-Hellman key exchange protocol, Alice and Bob choose a large prime p and a primitive…
A: An algorithm is a finite sequence of rigorous well-defined instructions, typically used to solve a…
Q: Solve the system of congruence x ≡ 3 (mod 6) and x ≡ 4 (mod 7) using the method of back…
A:
Q: Solve for d using Euclid's Extended Algorithm 3d ≡ 1 mod 5200
A: Given 3d≡1 mod 5200 . The objective is to solve for d using Euclid's Extended Algorithm.
Q: Suppose that Bob has used two distinct primes p and q to create the public modulus n = pq and public…
A: RSA algorithm: 1. Choose two distinct prime numbers p and q. Take n = pq. 2. Compute λ(n), where λ…
Q: 3. To login to a particular phone app, users must create a 6-character password using only the…
A: We have 10 digits available
Step by step
Solved in 2 steps with 2 images

- Suppose that in an RSA Public Key Cryptosystem, the public key is. Encrypt the message "pay me later” using two-digit blocks and the -letter alphabet from Example 2. What is the secret key? Example 2 Translation Cipher Associate the letters of the "alphabet" with the integers. Let and define the mapping by where is the key, the number of positions from the plaintext to the ciphertext. If our alphabet consists of through, in natural order, followed by a blank, then we have "letters" that we associate with the integers as follows:Suppose that in an RSA Public Key Cryptosystem, the public key is e=13,m=77. Encrypt the message "go for it" using two-digit blocks and the 27-letter alphabet A from Example 2. What is the secret key d? Example 2 Translation Cipher Associate the n letters of the "alphabet" with the integers 0,1,2,3.....n1. Let A={ 0,1,2,3.....n-1 } and define the mapping f:AA by f(x)=x+kmodn where k is the key, the number of positions from the plaintext to the ciphertext. If our alphabet consists of a through z, in natural order, followed by a blank, then we have 27 "letters" that we associate with the integers 0,1,2,...,26 as follows: Alphabet:abcdef...vwxyzblankA:012345212223242526a. Excluding the identity cipher, how many different translation ciphers are there using an alphabet of n "letters"? b. Excluding the identity cipher, how many different affine ciphers are there using an alphabet of n "letters," where n is a prime?
- Suppose the alphabet consists of a through z, in natural order, followed by a blank and then the digits 0 through 9, in natural order. Associate these "letters" with the numbers 0,1,2,...,36, respectively, thus forming a 37-letter alphabet, D. Use the affine cipher to decipher the message X01916R916546M9CN1L6B1LL6X0RZ6UII if you know that the plaintext message begins with "t" followed by "h". Write out the affine mapping f and its inverse.Suppose that in an RSA Public Key Cryptosystem. Encrypt the message "algebra" using the -letter alphabet from Example 4. Use two-digit blocks. Use three-digit blocks. What is the secret key?Suppose that the check digit is computed as described in Example . Prove that transposition errors of adjacent digits will not be detected unless one of the digits is the check digit. Example Using Check Digits Many companies use check digits for security purposes or for error detection. For example, an the digit may be appended to a -bit identification number to obtain the -digit invoice number of the form where the th bit, , is the check digit, computed as . If congruence modulo is used, then the check digit for an identification number . Thus the complete correct invoice number would appear as . If the invoice number were used instead and checked, an error would be detected, since .
- Use the alphabet C from the preceding problem and the affine cipher with key a=11andb=7 to decipher the message RRROAWFPHPWSUHIFOAQXZC:Q.ZIFLW/O:NXM and state the inverse mapping that deciphers this ciphertext. Exercise 7: Suppose the alphabet consists of a through z, in natural order, followed by a colon, a period, and then a forward slash. Associate these "letters" with the numbers 0,1,2,...,28, respectively, thus forming a 29-letter alphabet, C. Use the affine cipher with key a=3andb=22 to decipher the message OVVJNTTBBBQ/FDLWLFQ/GATYST and state the inverse mapping that deciphers this ciphertext.Rework Example 5 by breaking the message into two-digit blocks instead of three-digit blocks. What is the enciphered message using the two-digit blocks? Example 5: RSA Public Key Cryptosystem We first choose two primes (which are to be kept secret): p=17, and q=43. Then we compute m (which is to be made public): m=pq=1743=731. Next we choose e (to be made public), where e must be relatively prime to (p1)(q1)=1642=672. Suppose we take e=205. The Euclidean Algorithm can be used to verify that (205,672)=1. Then d is determined by the equation 1=205dmod672 Using the Euclidean Algorithm, we find d=613 (which is kept secret). The mapping f:AA, where A=0,1,2,...,730, defined by f(x)=x205mod731 is used to encrypt a message. Then the inverse mapping g:AA, defined by g(x)=x613mod731 can be used to recover the original message. Using the 27-letter alphabet as in Examples 2 and 3, the plaintext message no problem is translated into the message as follows: plaintext:noproblemmessage:13142615171401110412 The message becomes 13142615171401110412. This message must be broken into blocks mi, each of which is contained in A. If we choose three-digit blocks, each block mim=731. mi:13142615171401110412f(mi)=mi205mod731=ci:082715376459551593320 The enciphered message becomes 082715376459551593320 where we choose to report each ci with three digits by appending any leading zeros as necessary. To decipher the message, one must know the secret key d=613 and apply the inverse mapping g to each enciphered message block ci=f(mi): ci:082715376459551593320g(ci)=ci613mod731:13142615171401110412 Finally, by re-breaking the message back into two-digit blocks, one can translate it back into plaintext. Three-digitblockmessage:13142615171401110412Two-digitblockmessage:13142615171401110412Plaintext:noproblem The RSA Public Key Cipher is an example of an exponentiation cipher.Suppose the alphabet consists of a through, in natural order, followed by a blank, a comma, and a period, in that order. Associate these "letters" with the numbers, respectively, thus forming a -letter alphabet,. Use the affine cipher to decipher the message if you know that the plaintext message begins with "" and ends with ".". Write out the affine mapping and its inverse.



