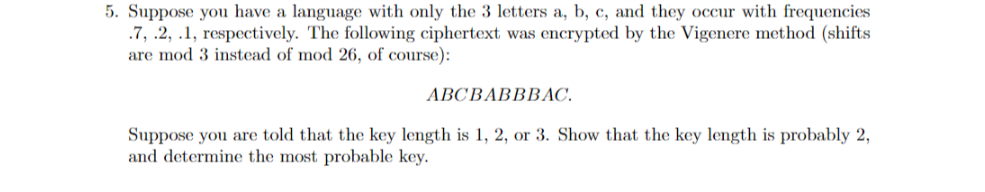
5. Suppose you have a language with only the 3 letters a, b, c, and they occur with frequencies .7, .2, .1, respectively. The following ciphertext was encrypted by the Vigenere method (shifts are mod 3 instead of mod 26, of course): ABCBABBBAC. Suppose you are told that the key length is 1, 2, or 3. Show that the key length is probably 2, and determine the most probable key.
Q: Decrypt the message XUPPWFIDD which was encrypted using the athine cipher f(p) = (15p + 6) mod 26…
A:
Q: Suppose p = 5 and q RSA cryptosystem with public key (n, e) = (55, 7)? 11. Which of the following is…
A:
Q: b.Given Bob's public key of (85, 7) and private key of (85, 55), show how Alice can encrypt m=5 to…
A: Given: b) Given Bob's public key of (85, 7) and private key of (85, 55), To show how Alice can…
Q: Let's say that Alice and Bob are exchanging keys using Diffie-Hellman key exchange using…
A: Here, we have p=499 (which is a prime number) g=7 a=23 (which is a secret exponent of Alice) and b…
Q: 1. If Alice uses the RSA modulus N = 77 and e=17, what is d? 2. Decrypt the message 5559 vising an…
A:
Q: Assume you are constructing an RSA algorithm where primes are p=11, q=7 a) Choose a proper public…
A: Use the following formulae, to obtain the required result. n=pqϕn=p-1q-1ed≡1mod ϕny=xe mod nx=yd mod…
Q: 1. A long-winded, encrypted transmission has been intercepted. Frequency analysis of the entire…
A: As per our guidelines we are supposed answer only one question and rest can be reposted
Q: Construct an affine cipher that uses only uppercase letters of English alphabet encoded as elements…
A:
Q: Decrypt the word OSCEG if it was encrypted using an alphabetic Caesar shift cipher that starts with…
A: The objective is to decrypt the word OSCEG if it was encrypted using an alphabetic Caesar shift…
Q: Consider a binary communication system. The pulse p(t) and the pulse q(t) are defined by ´A6 + 1, а,…
A: a. Sketch the signals p(t) and q(t) p(t)=∑t=03t p(t) =0(a6+1)+1(a6+1)+2(a7+a8)+3(a9) where…
Q: Encipher these messages using a Rosicrucian cipher: 1. SWIM 2. BASEBALL 3. НОСКEY 4. FOOTBALL 5.…
A: Rosicrucian Chipher : For ciphering the alphabets consider the boxes and the dots corresponding to…
Q: What is the Plaintext of the following Ciphertext, based on Caesar cipher algorithm, if the KEY=5?…
A:
Q: Encrypt the message ATTACK using c = (p+12) mod 26 O a. MGGMOX O b. LFFLOW O C. LFFLOX O d. MFFMOW
A: Each letter in the alphabet corresponds to a number between 0 to 26. Letter A B C D E F G H I J K…
Q: Queston 2 only please
A: The given Caesar encryptions is OKBDRZBYFSNOCOXYEQRDYCKDSCPIOFOBIWKXCXOONCLEDXYDOFOBIWKXCQBOON.In…
Q: Encrypt the message ATTACK using the RSA system with n = 43 · 59 and e = 13, translating each letter…
A:
Q: 2. Decrypt the letters MRYYXHJULYSL if it was encrypted using the alphabetic random substitution…
A: We are asking to decrypt the latter MRYYXHJULYSL by using the given table.
Q: What is the secret message produced from the message “MEET YOU IN THE PARK” using the Caesar cipher?
A:
Q: Decrypt the message ''EOXH MHDQV Using the shift cipher f(p)=(p+3)mod26
A: Solution by using shift cipher as follows :
Q: (a) Suppose Alice and Bob use the simple encryption scheme in which c = (m + k) mod N and m = (c –…
A: Suppose Alice and Bob use the simple encryption scheme in whichc=m+kmodN and m=(c-k)modN. Suppose…
Q: 11. Here is our second code. Once more you agree with your friend on a modulus (say, 25) and a…
A:
Q: Suppose (n, d) = (55, 3) is the private key of an RSA cryptosystem. If the received ciphertext is C…
A:
Q: The message NOT NOW (numerically 131419131422) is to be sent to a user of the EIGamal system who has…
A:
Q: Jse the RSA cipher with public key (pq, e) = (23 · 31, 43) = (713, 43) and private key (pq, d),…
A: Given pq=713d=307e=43 cipher text 675 001 423
Q: 3. The message NOT NOW (numerically 131419131422) is to be sent to a user e a EIGamal system who has…
A:
Q: Encrypt the message GRIZZLY BEARS using blocks of five letters and the transposition cipher based on…
A:
Q: IS SIX ba ch has an upcoming game against State on I State employs five different defenses. Th rards…
A: Q
Q: Decrypt these messages encrypted using the shift cipher f (p) = (p + 10) mod 26.a) CEBBOXNOB XYGb)…
A:
Q: (7) Which of the following formulas represent the process of encryption in Caesar Cipher? (Choose…
A: Option B M=(C-3)mod26
Q: Alice received the following ciphertext from Bob, "08 01 08 05". Bob had encrypted it using the RSA…
A:
Q: (b) If the public key for an RSA cryptosystem is (N, e) = (69,5), find the private key d.
A: We follow the standard techniques use in the RSA algorithm. The detailed typeset solution is…
Q: Bob wants to send Alice the message, "JAW," which he plans to encrypt using Alice's RSA cypher with…
A:
Q: Which of the following is the decryption function of an RSA cryptosystem having public and private…
A: We Know that, The RSA algorithm can be used for both public key encryption and digital signatures.
Q: Use the method of Example 9.5.10 to answer the following questions. (a) How many 15-bit strings…
A:
Q: Suppose an RSA cryptosystem is used to send the plaintext "4" with public key (n, e) = (33, 3). What…
A: RSA algorithm is an encryption method that uses two types of keys namely private and public and,…
Q: 1. Encrypt and decrypt the sentence “Pay more cash" using Hill Cipher with the key: 17 17 5 21 18 21…
A: First we convert given plaintext to 3x1 vectors then we use the key matrix to find the corresponding…
Q: 6| Alice wants to send message HELLO using the RSA system with p = 7 and q = 11 and n= 53 by…
A:
Q: (a) Use the Atbash cipher to encrypt the following messages: in Alphabet: ABCDEFGHIJKLMNOPQRSTUVWXYZ…
A: Since the second question is independent of the first question so I am the answering the first…
Q: Let p = 3, q = 11. This means N = 33 and phi = 20. Let e = 7. This means d = 3. Public key: 33, 7…
A:
Q: Having chosen primes p and q, and suitable integers d and e, what is the public-key of our RSA…
A: There are primes p and q and integers d and e, the public-key of RSA cipher is: n,e=pq, e
Q: In a lengthy ciphertext message, sent using a linear cipher C = a P +b (mod 26), the most frequently…
A:
Q: Apply the affine cipher formula C=(5P + 2) mod 26 to encript "LASER PRINTER". JGNSA DUNTXNA JSNAS…
A:
Q: 1. The following sentence was encoded using the Cesar Cipher, your job is to decode it: KRZ DUH BRX.
A: 1. The following table is used to decrypt the message.
Q: Suppose the RSA system that is used for sending secret messages has private key (15, 3) and the…
A: Given that, private key=15,3 Cipher text=3
Q: Decrypt the message EABW EFRO ATMR ASIN, which is the ciphertext produced by encrypting a plaintext…
A:
Q: 14. Show that if x mod 8 = 6, then x mod 4 = 2, when x is an integer. Give an example. 15. Decrypt…
A: Given that x mod 8 =6 x mod 8=x-8n=6, Where n=1, 2, .... x=6+8n
Q: The following affine cipher with the key k = (a, b) uses only uppercase letters of English alphabet…
A:
Q: The ciphertext letter for T when the congruence is C =( P + 10 ) mod 26 is
A:
Q: a. Given p=23, q=7, and e=5, generate the public key (n,e) and the private key (n,d) using RSA Key…
A:
Q: Suppose that you know that a ciphertext was produced by encrypting a plaintext message with a…
A:
Q: 3. To login to a particular phone app, users must create a 6-character password using only the…
A: We have 10 digits available
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 7 images

- Suppose that in an RSA Public Key Cryptosystem, the public key is. Encrypt the message "pay me later” using two-digit blocks and the -letter alphabet from Example 2. What is the secret key? Example 2 Translation Cipher Associate the letters of the "alphabet" with the integers. Let and define the mapping by where is the key, the number of positions from the plaintext to the ciphertext. If our alphabet consists of through, in natural order, followed by a blank, then we have "letters" that we associate with the integers as follows:Suppose that in an RSA Public Key Cryptosystem, the public key is e=13,m=77. Encrypt the message "go for it" using two-digit blocks and the 27-letter alphabet A from Example 2. What is the secret key d? Example 2 Translation Cipher Associate the n letters of the "alphabet" with the integers 0,1,2,3.....n1. Let A={ 0,1,2,3.....n-1 } and define the mapping f:AA by f(x)=x+kmodn where k is the key, the number of positions from the plaintext to the ciphertext. If our alphabet consists of a through z, in natural order, followed by a blank, then we have 27 "letters" that we associate with the integers 0,1,2,...,26 as follows: Alphabet:abcdef...vwxyzblankA:012345212223242526Rework Example 5 by breaking the message into two-digit blocks instead of three-digit blocks. What is the enciphered message using the two-digit blocks? Example 5: RSA Public Key Cryptosystem We first choose two primes (which are to be kept secret): p=17, and q=43. Then we compute m (which is to be made public): m=pq=1743=731. Next we choose e (to be made public), where e must be relatively prime to (p1)(q1)=1642=672. Suppose we take e=205. The Euclidean Algorithm can be used to verify that (205,672)=1. Then d is determined by the equation 1=205dmod672 Using the Euclidean Algorithm, we find d=613 (which is kept secret). The mapping f:AA, where A=0,1,2,...,730, defined by f(x)=x205mod731 is used to encrypt a message. Then the inverse mapping g:AA, defined by g(x)=x613mod731 can be used to recover the original message. Using the 27-letter alphabet as in Examples 2 and 3, the plaintext message no problem is translated into the message as follows: plaintext:noproblemmessage:13142615171401110412 The message becomes 13142615171401110412. This message must be broken into blocks mi, each of which is contained in A. If we choose three-digit blocks, each block mim=731. mi:13142615171401110412f(mi)=mi205mod731=ci:082715376459551593320 The enciphered message becomes 082715376459551593320 where we choose to report each ci with three digits by appending any leading zeros as necessary. To decipher the message, one must know the secret key d=613 and apply the inverse mapping g to each enciphered message block ci=f(mi): ci:082715376459551593320g(ci)=ci613mod731:13142615171401110412 Finally, by re-breaking the message back into two-digit blocks, one can translate it back into plaintext. Three-digitblockmessage:13142615171401110412Two-digitblockmessage:13142615171401110412Plaintext:noproblem The RSA Public Key Cipher is an example of an exponentiation cipher.
- Suppose the alphabet consists of a through z, in natural order, followed by a blank and then the digits 0 through 9, in natural order. Associate these "letters" with the numbers 0,1,2,...,36, respectively, thus forming a 37-letter alphabet, D. Use the affine cipher to decipher the message X01916R916546M9CN1L6B1LL6X0RZ6UII if you know that the plaintext message begins with "t" followed by "h". Write out the affine mapping f and its inverse.Suppose that in an RSA Public Key Cryptosystem. Encrypt the message "algebra" using the -letter alphabet from Example 4. Use two-digit blocks. Use three-digit blocks. What is the secret key?a. Excluding the identity cipher, how many different translation ciphers are there using an alphabet of n "letters"? b. Excluding the identity cipher, how many different affine ciphers are there using an alphabet of n "letters," where n is a prime?
- Suppose that the check digit is computed as described in Example . Prove that transposition errors of adjacent digits will not be detected unless one of the digits is the check digit. Example Using Check Digits Many companies use check digits for security purposes or for error detection. For example, an the digit may be appended to a -bit identification number to obtain the -digit invoice number of the form where the th bit, , is the check digit, computed as . If congruence modulo is used, then the check digit for an identification number . Thus the complete correct invoice number would appear as . If the invoice number were used instead and checked, an error would be detected, since .Suppose a codding scheme is devised that maps -bit words onto -bit code words. The efficiency of the code is the ratio . Compute the efficiency of the coding scheme described in each of the following examples. Example 1 Example 2 Example 3 Example 4 Example 1: Parity check – Consider -bit words of the form . One coding scheme maps onto , where is called the parity check digit. Example 2: Repetition Codes – Multiple errors can be detected (but not corrected) in a scheme in which a -bit word is mapped onto a -bit code word according to the following scheme: Example 3: Maximum Likelihood Decoding- Multiple errors can be detected and corrected if each -bit word is mapped onto a - bit code word according to the following scheme (called a triple repetition code): Example 4: Error Detection and Correction – Suppose -bit words are mapped onto -bit code words using the scheme , Where is the parity check digit .Use the alphabet C from the preceding problem and the affine cipher with key a=11andb=7 to decipher the message RRROAWFPHPWSUHIFOAQXZC:Q.ZIFLW/O:NXM and state the inverse mapping that deciphers this ciphertext. Exercise 7: Suppose the alphabet consists of a through z, in natural order, followed by a colon, a period, and then a forward slash. Associate these "letters" with the numbers 0,1,2,...,28, respectively, thus forming a 29-letter alphabet, C. Use the affine cipher with key a=3andb=22 to decipher the message OVVJNTTBBBQ/FDLWLFQ/GATYST and state the inverse mapping that deciphers this ciphertext.
- Suppose that the most common letter and the second most common letter in a long ciphertext produced by encrypting a plaintext using an affine cipher f (p) = (ap + b) mod 26 are Z and J, respectively. What are the most likely values of a and b?Suppose that when a string of English text is encrypted using a shift cipher f (p) = (p + k) mod 26, the resulting ciphertext is DY CVOOZ ZOBMRKXMO DY NBOKW. What was the original plaintext string?Consider the affine cipher with key k = (k1, k2) whose encryption and decryption functions are given by (1.11) on page 43. Alice and Bob decide to use the prime p = 601 for their affine cipher. The value of p is public knowledge, and Eve intercepts the ciphertexts c1 = 324 and c2 = 381 and also manages to find out that the corresponding plaintexts are m1 = 387 and m2 = 491. Determine the private key and then use it to encrypt the message m3 = 173.

