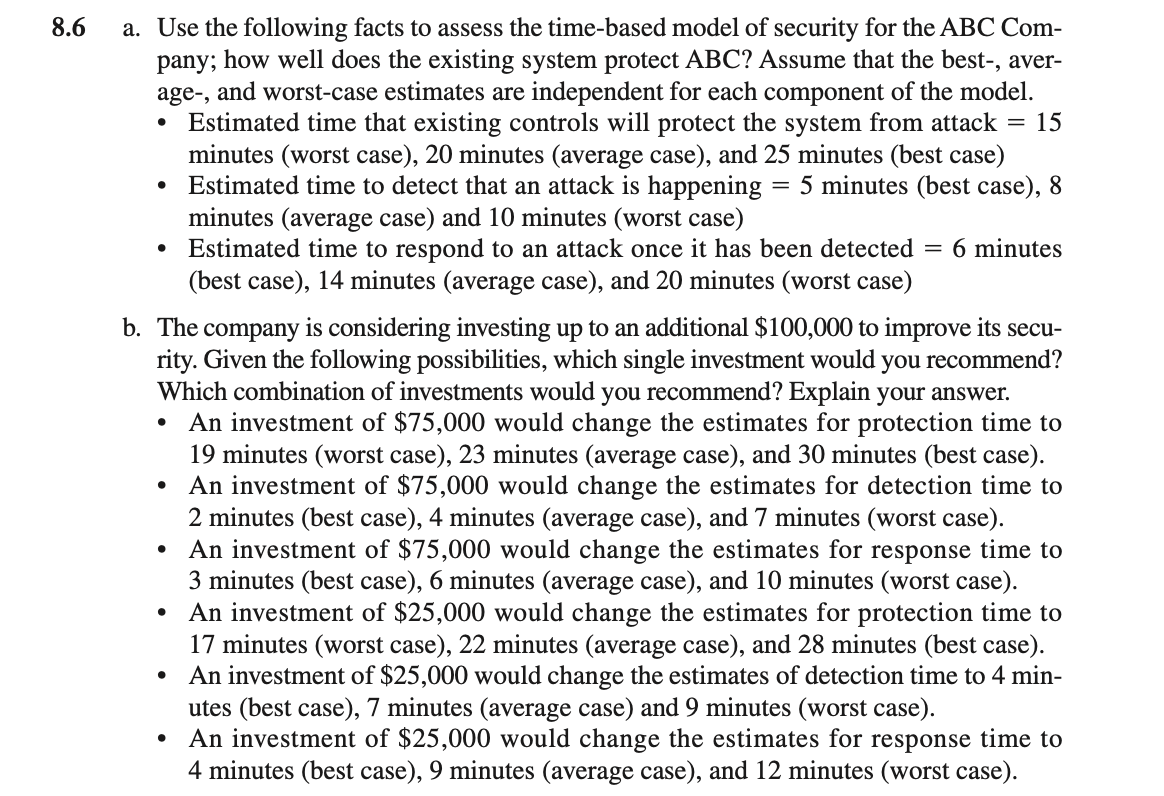
8.6 a. Use the following facts to assess the time-based model of security for the ABC Com- pany; how well does the existing system protect ABC? Assume that the best-, aver- age-, and worst-case estimates are independent for each component of the model. Estimated time that existing controls will protect the system from attack = 15 minutes (worst case), 20 minutes (average case), and 25 minutes (best case) Estimated time to detect that an attack is happening minutes (average case) and 10 minutes (worst case) Estimated time to respond to an attack once it has been detected (best case), 14 minutes (average case), and 20 minutes (worst case) = 5 minutes (best case), 8 = 6 minutes
8.6 a. Use the following facts to assess the time-based model of security for the ABC Com- pany; how well does the existing system protect ABC? Assume that the best-, aver- age-, and worst-case estimates are independent for each component of the model. Estimated time that existing controls will protect the system from attack = 15 minutes (worst case), 20 minutes (average case), and 25 minutes (best case) Estimated time to detect that an attack is happening minutes (average case) and 10 minutes (worst case) Estimated time to respond to an attack once it has been detected (best case), 14 minutes (average case), and 20 minutes (worst case) = 5 minutes (best case), 8 = 6 minutes
Auditing: A Risk Based-Approach to Conducting a Quality Audit
10th Edition
ISBN:9781305080577
Author:Karla M Johnstone, Audrey A. Gramling, Larry E. Rittenberg
Publisher:Karla M Johnstone, Audrey A. Gramling, Larry E. Rittenberg
Chapter7: Planning The Audit: Identifying, And Responding To The Risk Of Material Misstatement
Section: Chapter Questions
Problem 26MCQ
Related questions
Question
Transcribed Image Text:8.6
a. Use the following facts to assess the time-based model of security for the ABC Com-
pany; how well does the existing system protect ABC? Assume that the best-, aver-
age-, and worst-case estimates are independent for each component of the model.
Estimated time that existing controls will protect the system from attack = 15
minutes (worst case), 20 minutes (average case), and 25 minutes (best case)
Estimated time to detect that an attack is happening
minutes (average case) and 10 minutes (worst case)
Estimated time to respond to an attack once it has been detected = 6 minutes
(best case), 14 minutes (average case), and 20 minutes (worst case)
= 5 minutes (best case), 8
b. The company is considering investing up to an additional $100,000 to improve its secu-
rity. Given the following possibilities, which single investment would you recommend?
Which combination of investments would you recommend? Explain your answer.
An investment of $75,000 would change the estimates for protection time to
19 minutes (worst case), 23 minutes (average case), and 30 minutes (best case).
An investment of $75,000 would change the estimates for detection time to
2 minutes (best case), 4 minutes (average case), and 7 minutes (worst case).
An investment of $75,000 would change the estimates for response time to
3 minutes (best case), 6 minutes (average case), and 10 minutes (worst case).
• An investment of $25,000 would change the estimates for protection time to
17 minutes (worst case), 22 minutes (average case), and 28 minutes (best case).
An investment of $25,000 would change the estimates of detection time to 4 min-
utes (best case), 7 minutes (average case) and 9 minutes (worst case).
An investment of $25,000 would change the estimates for response time to
4 minutes (best case), 9 minutes (average case), and 12 minutes (worst case).
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, accounting and related others by exploring similar questions and additional content below.Recommended textbooks for you

Auditing: A Risk Based-Approach to Conducting a Q…
Accounting
ISBN:
9781305080577
Author:
Karla M Johnstone, Audrey A. Gramling, Larry E. Rittenberg
Publisher:
South-Western College Pub

Pkg Acc Infor Systems MS VISIO CD
Finance
ISBN:
9781133935940
Author:
Ulric J. Gelinas
Publisher:
CENGAGE L

Accounting Information Systems
Finance
ISBN:
9781337552127
Author:
Ulric J. Gelinas, Richard B. Dull, Patrick Wheeler, Mary Callahan Hill
Publisher:
Cengage Learning

Auditing: A Risk Based-Approach to Conducting a Q…
Accounting
ISBN:
9781305080577
Author:
Karla M Johnstone, Audrey A. Gramling, Larry E. Rittenberg
Publisher:
South-Western College Pub

Pkg Acc Infor Systems MS VISIO CD
Finance
ISBN:
9781133935940
Author:
Ulric J. Gelinas
Publisher:
CENGAGE L

Accounting Information Systems
Finance
ISBN:
9781337552127
Author:
Ulric J. Gelinas, Richard B. Dull, Patrick Wheeler, Mary Callahan Hill
Publisher:
Cengage Learning

Accounting Information Systems
Accounting
ISBN:
9781337619202
Author:
Hall, James A.
Publisher:
Cengage Learning,