Cryptography: Cryptography is a way to keep messages and other data secret. It is the art of writing or solving ciphers. What's a cipher? It's a "secret or disguised way of writing," says the Concise Oxford Dictionary. In the business world, cryptography refers to mathematically based encryption methods that keep data away from the prying eyes of criminals or enemy governments. Today's businesses and governments use what is called "strong" encryption. This type of encryption is created using applied mathematics. Strong encryption was once used solely for military purposes, but in today's information society, encryption is needed for all kinds of uses. Keys are a fundamental component of cryptography, being used in cryptographic operations such as encryption, hashing and signing to provide desirable properties like confidentiality (keeping information secret), integrity (preventing information being altered) or authenticity (verifying who the information came from). One key (public key) is used for encrypt the plain text to convert it into cipher text and another key (private key) is used by receiver to decrypt the cipher text to read the message Key generation is the process of generating keys in cryptography. The aim of this assignment is to generate a private key based on the given public key as a positive integer “n” from the range 1 to 10 (excluding 1 and 10). Continue the process of dividing “n” by 2 if the value of “n” is even or add 1 to “n” if the value of “n” is odd until the value of “n” becomes less than or equal to 1. During this process add the value of “n” in a variable “sum” if the value of “n” is between 1 and 10 (excluding 1 and 10). The value of the variable “sum” represents the private key Write: 1)Problem solving methodology and flow chart diagram (Word file) 2)C++ program
Cryptography:
Cryptography is a way to keep messages and other data secret. It is the art of writing or solving ciphers.
What's a cipher? It's a "secret or disguised way of writing," says the Concise Oxford Dictionary. In the
business world, cryptography refers to mathematically based encryption methods that keep data away from
the prying eyes of criminals or enemy governments. Today's businesses and governments use what is called
"strong" encryption. This type of encryption is created using applied mathematics. Strong encryption was
once used solely for military purposes, but in today's information society, encryption is needed for all kinds
of uses.
Keys are a fundamental component of cryptography, being used in cryptographic operations such as
encryption, hashing and signing to provide desirable properties like confidentiality (keeping information
secret), integrity (preventing information being altered) or authenticity (verifying who the information came
from). One key (public key) is used for encrypt the plain text to convert it into cipher text and
another key (private key) is used by receiver to decrypt the cipher text to read the message
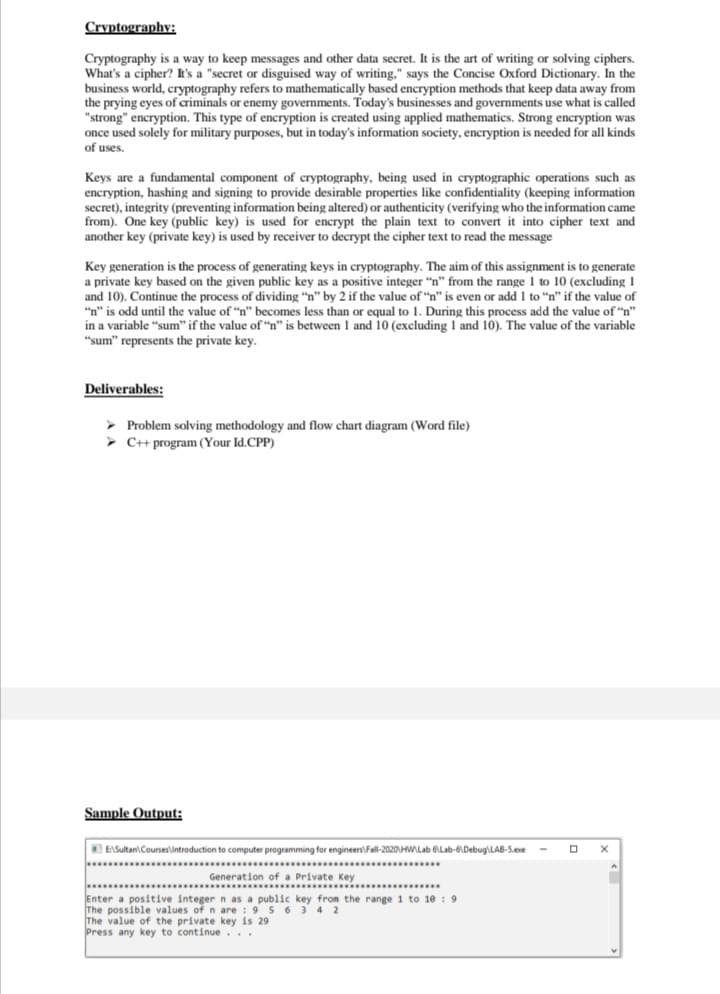
Key generation is the process of generating keys in cryptography. The aim of this assignment is to generate
a private key based on the given public key as a positive integer “n” from the range 1 to 10 (excluding 1
and 10). Continue the process of dividing “n” by 2 if the value of “n” is even or add 1 to “n” if the value of
“n” is odd until the value of “n” becomes less than or equal to 1. During this process add the value of “n”
in a variable “sum” if the value of “n” is between 1 and 10 (excluding 1 and 10). The value of the variable
“sum” represents the private key
Write:
1)Problem solving methodology and flow chart diagram (Word file)
2)C++ program
Trending now
This is a popular solution!
Step by step
Solved in 4 steps with 2 images









