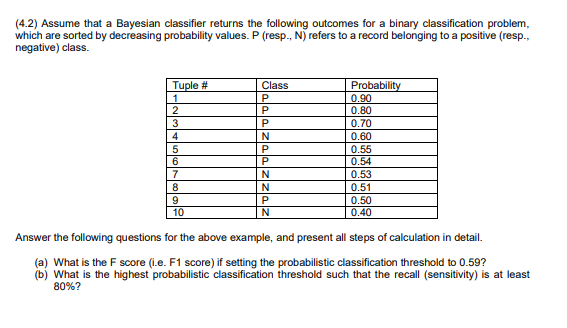
e that a Bayesian classifier returns the following outcomes for a binary classification pro rted by decreasing probability values. P (resp., N) refers to a record belonging to a positive ( ass. Tuple # 1 Class Probability 0.90 0.80 0.70 3 P
Q: random answer. Computer science. Ksenia has an exhibit a comprising of n positive integers a1,a2,……
A: Here have to determine about the Powerful Ksenia programming problem statement.
Q: In order for an algorithm to successfully achieve the goal of mutual exclusion, what type of…
A: Let's look at the answer step by step: - MUTUAL EXCLUSION:- is a property of concurrency control…
Q: Let X and Y be sets of attributes. Show that if X ⊂ Y , then X+ ⊂ Y + , where the closures are taken…
A: for the required prove - we uses contrapositive method: It means we are proving that if X+ is not…
Q: From previous slide, if M hasn states, how many states does M' have by this construction? (а) 2n (b)…
A: According to the information given:- We have to choose the correct option to satisfy the statement.
Q: Prove the soundness of the following inference rule (called Modus Tollens) (P → Q), ¬ Q = ¬P
A: We have to Prove that the soundness of the inference rule (called Modus Tollens) :
Q: Given below are some facts and predicates for some knowledge base (KB). State if the unification for…
A: Unification is a process by which two logical individual atomic expressions, identical by replacing…
Q: given P(D|M) P(M\D)P(D) solve the followin %3D p(M)
A:
Q: Consider a knowledge base (KB) shown in Figure4. Assume that the initial fact base from a user is {Q…
A: Consider a knowledge base (KB) shown in Figure4. Assume that the initial fact base from a user is {Q…
Q: Select the appropriate characteristic for each of the following environments Note: The…
A: Here we need to find the characteristics of the environment given and put the following…
Q: Consider the following information: a → b a → c a → d Draw the inference chain. Complete the…
A: Draw the inference chain.
Q: Ques: Perform KNN-classification Algorithm on following dataset and Predict the class for X (P₁=3…
A: The k-nearest neighbors algorithm, also called KNN or k-NN, is a non-parametric, supervised learning…
Q: 22.6. Show that for n attributes A1, A2, A3, .., An (A1 A2 Az ... A,)2(A ) +( A2 ) + ( A3 ) + ... +…
A: The Handwritten complete solution/answer is given below:
Q: Using titanic_data.csv, write a supervised binary classification using RandomForestClassifier to…
A: The code is given below for the above given question
Q: 2. Given the following data set, we apply a naïve Bayesian (NB) classifier to predict the Health…
A: Given Data : The dataset where Heath is the class variable. To find : Given the data row = {ID…
Q: 3. Consider an ensemble of 3 independent 2-class classifiers, each of which has an error rate of…
A: The ensemble classifier returns a classification in the form of a percentage. Given only two…
Q: This issue asks you to develop a Julia programme that does the following: When provided a policy,…
A: Given: The process of discovering various policy choices that might handle your issue, comparing…
Q: For classification algorithms, the best dataset is to have: A y=1 cases is much more than y=0 B y=0…
A: Answer : C : comparable number of both classes
Q: Data mining "SVM" & " Bayesian Classifier" Class + Question 1: Consider the data set shown in the…
A: Data mining "SVM" & "Bayesian Classifier" Question 1: Consider the data set shown in the…
Q: =1 (cold) i=2 (allergy) i=3 (stomach pain) p(Hi) 0.6 0.3 0.1 p(E1 |Hi) 0.3 0.8 0.3 p(E2 |Hi) 0.6 0.9…
A: Below the solution
Q: the following training data. Use Naive Bayes classifier to classify Que 3.18. Consider a two-class…
A: Naive Bayes Naive Bayes is a statistical classification technique based on Bayes Theorem. It is one…
Q: Consider the following inference chaining rule diagram. Drive the inference rule by considering the…
A: ANSWER: Backward Chaining: Backward chaining is otherwise called a backward derivation or backward…
Q: What kind of fairness assumption should be used in an algorithm to accomplish mutual exclusion?…
A: MUTUAL EXCLUSION :prevents race circumstances. IT is the requirement that a process can't enter its…
Q: Let S be a source with probabilities p; = 0.4, 0.2, 0.2, 0.1, 0.1 then e) If C is ternary Huffman…
A: Summary:In this question, we need to find the average word Length without constructing the code and…
Q: Use a full truth table to explain why any implication p → q is logically equivalent to it:…
A: Here in this question we have asked to show that any implications is equivalent to its…
Q: Fill-in the boxes with the correct answer. The recurrence relation for bar(x, y) when x, y > 0 is:…
A: Answer : T(x,y) = 2 T(x,y/2) + O(1) O(2n) = O(n) Explanation given below
Q: Consider the following data sets comprising of 3 boolean input attributes and 1 boolean -output.…
A: Note : Answering the question in python as no programming language is mentioned. Task : Import the…
Q: The Following table contains (fictitious) examples of holiday trips and also shows how much fun the…
A:
Q: Consider the following recurrence relation, give the Big-Theta behaviour of T(n) using induction:
A: Given, T(n) = 1, for n = 1 and T(n) = 5 T(n/5) + 2
Q: The first step in most classification algorithms is to estimate the probability that a case belongs…
A: posterior probability
Q: Your MDP has four states: Read emails (E), Get money (M), Be fooled (F) or Have fun (H). The actions…
A: Answer: There are 2 policies: both map state M to Stay, F to Go back and H to Stay. The only…
Q: rеpair. (i) Give an informal description of why the arrows in the diagram are neces- sary, and why…
A: Qb(i)Here in the graph L, P and F shows the common effect in which we can say that L and P are…
Q: Below are given the three sets of sequence labels below of a 4-class problem (labels belong either…
A:
Q: 1. Can we cast the prediction as a binary classification task. Explain your answer. 2. We consider…
A: ->A Naive Bayes classifier is an algorithm that uses Bayes' theorem to classify objects. ->…
Q: Given the premises p ∨ ¬q and r, which of the following is a correct inference? p ∧ (q ∧ r)…
A: The premises are p v q and r. Here r has to be T.
Q: Given A (0.3), B (0.2), C (0.6), D (0.8), E(0.4), M(0.6) IF A and B THEN M (0.8) IF C and D THEN G…
A: According to the information given:- We have to apply MYCIN approach to given fact table and…
Q: We know that A1,A2,..,An EA if and only if A is true in all worlds where each of A1, A2, .., An are…
A: Let's see the solution in the next steps
Q: A bigram model computes the probability p(D;θ) as: p(D;θ)=p(w0)∏w1,w2∈Dp(w2|w1) where w0 is the…
A: Bigram model: Bigram model written word model represents the conditional distribution…
Q: The predict() function allows us to predict the Y values that correspond to X values based on the…
A: As you can see, Linear model could be a quantitative output variable of y and for multiple predictor…
Q: Select the appropriate characteristic for each of the following environments Note: The…
A: Given: Here they are given some of the characteristics of the games we need to choose the…
Q: What type of fairness assumption shall be appropriate to achieve mutual exclusion in an algorithm?…
A: To Do: To list down types of fairness assumptions.
Q: Pruning to a decision tree is done to. O improve predictions diminish data leakage shrink a dataset…
A: According to the question the pruning decision tree helps to prevent the overfitting of the training…
Q: Estimate John’s weight if you gave: A) The degree of membership for each fuzzy fact: • John is tall…
A: In the given question, throughout the height of John were aware that Following are the rule for…
Q: 1. Prove that IR2 of the Armstrong Inference Rules is correct (sound). We did that for IR3 in class.…
A: Solution: IR2 indicates Augmentation Rule and IR3 indicates Transitive Rule and we have find given…
Q: Analyze the dataset given in image of Infection forecast to classify the patient to Infected or not.…
A:
Q: C.avb, a => C,
A: The evaluation is given below
Q: 4) Complete the following level-3 probability tree: 75% A. 20% 35% 90% i) P(AOBOC)= i) P(ĀOBOC)=…
A: According to the Bartleby guideline we are suppose to answer only first 3 sub part of the question…
Q: The accuracy in the output depends on the correct inputs. The model designed is supposed to be…
A: Answer is given below-
Q: d) Repeat part (b) using the conditional probabilities given in part (c). e) Compare the two methods…
A: According to the information given:- we have to answer only d,and e on the basis of instruction…
Q: The values of the set membership is represented by ___________ Select one: a. Both Degree of truth…
A: Given question about set membership The values of the set membership is represented by
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

- Crack the crag def crag_score(dice): Crag (see the Wikipedia page for the scoring table needed in this problem) is a dice game similar to the more popular games of Yahtzee and Poker dice in style and spirit, but with much simpler combinatorics of roll value calculation due to this game using only three dice. Players repeatedly roll three dice and assign the resulting patterns to scoring categories so that once some roll has been assigned to a category, that category is considered to have been spent and cannot be used again for any future roll. These tactical choices between safety and risk-taking give this game a little bit more tactical flair on top of merely relying on the favours of Lady Luck for rolling the bones. Given the list of pips of the three dice of the first roll, this function should compute and return the highest possible score available when all categories of the scoring table are still available for you to choose from, so that all that matters is maximizing this…Chirality def is_left_handed(pips): Even though this has no effect on fairness, pips from one to six are not painted on dice just any which way, but so that pips on the opposite faces always add up to seven. (This convention makes it easier to tell when someone tries to use crooked dice with certain undesirable pip values replaced with values that are more desirable for the cheater.) In each of the 23 = 8 corners of the cube, exactly one value from each pair of forbidden opposites 1-6, 2-5 and 3-4 meets two values chosen from the other two pairs of opposites. You can twist and turn any corner of the die to face you, and yet two opposite sides never spread into simultaneous view. This discipline still allows for two distinct ways to paint the pips. If the numbers in the corner shared by the faces 1, 2, and 3 read out clockwise as 1-2-3, that die is left-handed, whereas if they read out as 1-3-2, that die is right-handed. Analogous to a pair of shoes made separately for the left and…Make an argument that supports the usage of deep access rather than shallow access from the perspective of a coder; try to avoid making an argument that revolves around performance.
- PLEASE ANSWER THEM. JUST GIVE THE OPTIONS! 1- Consider the following sets consisting of only two kinds of items. Choose the item with the highest entropy: Select one a) aaaaaaab , b) aaaabbbb , c) aab , d) abaaaaab, e) aaaaaaaa 2- Consider an association rule eypressed as follows: {Bagels, ...) -> (Potato Chips) Choose all which is true for this rule: select one or more. Bagels is the antecedent Bagels is the consequent The rule indicates that people who buy bagels would like to buy potato chips afterwards Potato chips is the consequent The rule indicates that people who buy potato chips would like to buy bagels afterwards 3- Choose all of the following which is true about "support of association rules Select one or more is defined as support(A -> B) = P(A U B) For practical reasons one must favor rules with support value less than a threshold Measures now commonly seen are the events in the rule Support is a measure of the strenght of the rule A treshold for support is…Correct answer will be upvoted else Multiple Downvoted. Computer science. You have 2n integers 1,2,… ,2n. You need to rearrange these 2n components into n sets. From that point forward, you pick x combines and take least components from them, and from the other n−x sets, you take most extreme components. You will likely acquire the arrangement of numbers {b1,b2,… ,bn} as the aftereffect of taking components from the sets. What is the number of various x-s (0≤x≤n) with the end goal that it's feasible to get the set b if for every x you can pick how to appropriate numbers into sets and from which x sets pick least components? Input The main line contains a solitary integer t (1≤t≤1000) — the number of experiments. The primary line of each experiment contains the integer n (1≤n≤2⋅105). The second line of each experiment contains n integers b1,b2,… ,bn (1≤b1<b2<⋯<bn≤2n) — the set you'd prefer to get. It's dependable that the amount of n over experiments…Make an argument that supports the use of deep access rather than shallow access; attempt to avoid making an argument that centres around performance. This may be done by making an argument that supports the use of deep access rather than shallow access.
- JAVA: Texas Hold em poker game 2 to 8 human or computer players Each player has a name and stack of chips Computer players have a difficulty setting: easy, medium, hard Summary of each hand:o Dealer collects ante from appropriate players, shuffles the deck, and deals eachplayer a hand of 2 cards from the deck.o A betting round occurs, followed by dealing 3 shared cards from the deck.o As shared cards are dealt, more betting rounds occur, where each player can fold,check, or raise.o At the end of a round, if more than one player is remaining, players' hands arecompared, and the best hand wins the pot of all chips bet so far. What classes are in this system? What are their responsibilities? Which classes collaborate? Create the Use Cases for this systemCreate a Use Case diagram for this system Draw a class diagram for this system. Include relationships between classes (generalization andassociational).[15 marks] Let M be the NDFSM below. Construct a DFSM that accepts ¬L(M). Show your work using the algorithm ndfintodfsm (Rich 2008, page 75). 8, 6 2 b b a.b aTexas Hold em poker game 2 to 8 human or computer players Each player has a name and stack of chips Computer players have a difficulty setting: easy, medium, hard Summary of each hand:o Dealer collects ante from appropriate players, shuffles the deck, and deals eachplayer a hand of 2 cards from the deck.o A betting round occurs, followed by dealing 3 shared cards from the deck.o As shared cards are dealt, more betting rounds occur, where each player can fold,check, or raise.o At the end of a round, if more than one player is remaining, players' hands arecompared, and the best hand wins the pot of all chips bet so far. What classes are in this system? What are their responsibilities? Which classes collaborate? Create the Use Cases for this systemCreate a Use Case diagram for this system Draw a class diagram for this system. Include relationships between classes (generalization andassociational).
- Not pseudocode Suppose the economies of the world use a set of currencies C1, . . . , Cn; think of these as dollars, pounds, Bitcoin, etc. Your bank allows you to trade each currency Ci for any other currency Cj, and finds some way to charge you for this service. Suppose that for each ordered pair of currencies (Ci, Cj ), the bank charges a flat fee of fij > 0 dollars to exchange Ci for Cj (regardless of the quantity of currency being exchanged). Describe an algorithm which, given a starting currency Cs, a target currency Ct, and a list of fees fij for all i, j ∈ {1, . . . , n}, computes the cheapest way (that is, incurring the least in fees) to exchange all of our currency in Cs into currency Ct. Also, justify the its runtime. [We are expecting a description of the algorithm, as well as a brief justification of its runtime.]Correct answer will be upvoted else downvoted. Computer science. Presently Nezzar has a beatmap of n particular focuses A1,A2,… ,An. Nezzar might want to reorder these n focuses so the subsequent beatmap is great. Officially, you are needed to find a change p1,p2,… ,pn of integers from 1 to n, to such an extent that beatmap Ap1,Ap2,… ,Apn is great. In case it is unthinkable, you ought to decide it. Input The primary line contains a solitary integer n (3≤n≤5000). Then, at that point, n lines follow, I-th of them contains two integers xi, yi (−109≤xi,yi≤109) — directions of point Ai. It is ensured that all focuses are unmistakable. Output In case there is no arrangement, print −1. In any case, print n integers, addressing a legitimate change p. In case there are numerous potential replies, you can print any.Artificial Intelligence - Local Search Starting from a randomly generated state of the 15-puzzle game (https://en.wikipedia.org/wiki/15_puzzle), steepest-ascent hill-climbing (the vanilla version of hill-climbing search) gets stuck 76% of the time, i.e., solving only 24% of problem instances. But it works very quickly, i.e., it takes just 6 steps on average when it succeeds and 5 steps when it gets stuck. In contrast, if sideways moves are allowed, this raises the percentage of problem instances solved by hill-climbing from 24% to 81%, with the success at a cost: the algorithm averages roughly 7 steps for each successful instance and 32 steps for each failure. Now suppose that we are implementing random-restart hill climbing (i.e., if a search fails, it keeps to try, and try, until it gets a success) by the following two versions: one uses vanilla steepest-ascent hill climbing, and the other one uses hill climbing with sideways moves. Can you please tell which version of…

