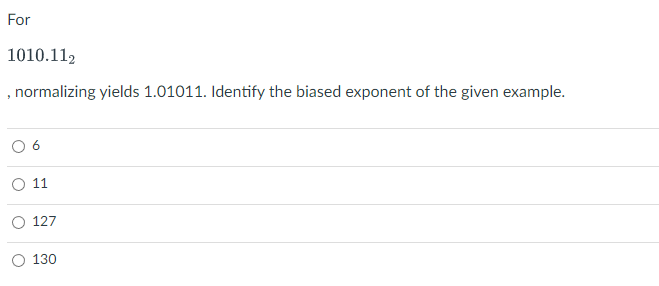
For 1010.112 , normalizing yields 1.01011. Identify the biased exponent of the given example. 11 127 130
Q: Federal Express (FedEx), founded in 1971, handles an average of 3 million package-tracking requests…
A: Introduction: Web Development: Website creation & upkeep are referred to as web ongoing…
Q: Why are wiretapping and network sniffing seen as a passive threat yet they share many similarities?
A: Wiretapping refers to the unauthorized interception or recording of private or confidential…
Q: When it comes to the management of software, what is the primary difference between distributed and…
A: The version control system is a device cluster responsible for managing changes to various…
Q: Here in this video, I'll outline the reasons I believe that human interaction and data…
A: The points were all addressed as a consequence, as stated in the introduction. - RESPONSE - - - -…
Q: Managers need to know what they're shooting for if they want to build stronger relationships with…
A: The followings are some comparable CRM objectives: Improving customer satisfaction: One of the…
Q: TODO 11 Using the axis_array defined below complete the following TODOs. Hint: Think about which…
A: Introduction In Python, the term "for each row" and "for each column" refers to the concept of…
Q: How can you help an employee who isn't putting up their best effort?
A: Improve their ability to see well. In order to provide assistance in the accomplishment of their…
Q: Describe ebool format.
A: An eBook is a reflowable and non editable book which is converted into the digital format and this…
Q: If you wanted to do some mathematical sets computations python, would a variable be the same as a…
A: In Python, a variable is a placeholder for storing values, while a set is a collection of unique…
Q: Multiple difficulties may arise from the widespread use of IT in the workplace. How should we…
A: Introduction : IT, or Information Technology, is a broad term that refers to any technology used to…
Q: i. For a second benchmark, libquantum, assume an execution time of 960 ns, CPI of 1.61, and clock…
A: CPU time: It is also called process time. It is the time taken by the CPU for processing the…
Q: For what reason are databases often called the "grandmother of all software programs"? To what end…
A: Database as the womb of computer programs We deal with a sizable volume of data for all computer…
Q: We don't fully comprehend how operating systems function. What does the term "operating system"…
A: An operating system (OS) is a software that manages computer hardware and software resources and…
Q: When developing a comprehensive cyber security plan, it is important to keep in mind the following…
A: The following are some factors that must be kept in mind while developing a comprehensive…
Q: When it comes to the analytical process, what part does data modeling play, and how significant is…
A: Data modeling makes it easier for developers, data architects, business analysts, and other…
Q: w well each security option deals with your specific sec
A: We must identify the security measures necessary to address diverse security concerns. Here are five…
Q: How common are different forms of cyberattack, and what do they want to achieve?
A: 1. Encryption is the study of secure communication techniques that allow only the sender and…
Q: What exactly does a Cyber Security teacher have to do?
A: The responsibilities of a cyber security teacher may include: Designing and delivering lessons on…
Q: When We Host Webserver On Ec2 Linux Instance ,We can access it from Putty Right? But We can do the…
A: Yes, it is possible to access an EC2 Linux instance from a Windows command prompt using the Secure…
Q: How does one make use of dynamic memory as opposed to non-dynamic memory, and what is the difference…
A: Dynamic memory is a memory which can change the size at run time. Non dynamic memory is also called…
Q: The volume of a sphere is 4/3πr3, where π has the value of "pi" given in Section 2.1 of your…
A: We can take the input custom way or we can give the custom input using input function
Q: What distinguishes symmetric and asymmetric encryption techniques (PKI, TLS, SSL) for network data…
A: Symmetric encryption and asymmetric encryption are two main techniques used for network data…
Q: What are three ways to sense check keywords? Ask whether the terms will add commercial value Ask…
A: Please refer to the following step for the complete solution to the problem above.
Q: Customer Number: Customer Name: Customer Address: 1001 Sales Order Number: Sales Order Date: ABC…
A: 3NF: 3NF stands for Third Normal Form, which is a database design principle used in relational…
Q: From what does a firewall protect a network? The process of filtering packets follows certain…
A: A firewall is a security system that monitors and controls the incoming and outgoing network traffic…
Q: To the best of your ability, list at least five separate domains of cyber security expertise…
A: One knowledge field: Data Protection The safety of data while it is in motion, being processed, and…
Q: how do i zip a folder with code in python?
A: To compress individual files into a ZIP file, create a new ZipFile object and add the files you want…
Q: Describe how the avalanche effect enhances DES security
A: Introduction The avalanche effect is a term associated with the specific behavior of mathematical…
Q: How do Boolean expressions work? What are they used for?
A: What does a Boolean expression actually mean? A logical assertion that can only be TRUE or FALSE is…
Q: It is recommended to submit a proposal for a security education program. Artifacts that have been…
A: 1. Encryption is the study of secure communication techniques that allow only the sender and…
Q: What exactly is meant by the term "release method" when it comes to the creation of software? Why is…
A: "Release method" refers to the process of making a new version of software available to the public…
Q: When will we see the ethical reasoning paradigm used in business settings?
A: Moral choices are made everyday. Ethics should guide individual conduct, the establishment of…
Q: Only IT security issues will have their proposed remedy developed.
A: 1. Encryption is the study of secure communication techniques that allow only the sender and…
Q: Don't forget to outline the necessary education and accreditation, and to illustrate abstract…
A: A person, product, or organisation may only be certified if it contains a set of qualities that have…
Q: Why does quicksort's efficiency change depending on the threshold value? Defend your position.
A: Introduction QuickSort is an efficient sorting algorithm with an average time complexity of O(n log…
Q: How can you measure how successfully people are using their social skills in the workplace when…
A: The effectiveness of social skill training in the workplace can be evaluated in a number of ways:
Q: TODO 1 Let's load the forestfires.csv by using Pandas read_csv() function. The read_csv() function…
A: Introduction Pandas: Pandas is just a Library for python to manipulating and analyzing the data. It…
Q: What is data modeling such an essential tool?
A: Data modelling is an essential tool for organizations to accelerate their application development…
Q: Assume that we have a 12-bit system (8-bits.2-bits), find a decimal representation of 2's complement…
A: Answer:-
Q: Which advantages does authentication have? Examine the pros and cons of various verification…
A: 1. Encryption is the study of secure communication techniques that allow only the sender and…
Q: Which of the following is NOT a benefit of collaboration networks? Group of answer choices protect…
A: 1. A computer network refers to interconnected computing devices that can exchange data and share…
Q: 1 [Start, Ti] 2 [Start, T2] 3 [T1, Bounce, 500, 1000] 4 [T2, Salary, 4000,4400] 5 [Checkpoint,…
A: Transactions: A transaction is a type of database transaction used to ensure data consistency and…
Q: Why do you think website hacking is a concern, specifically?
A: For several reasons, hackers attack websites. Hackers used to do it for Fun back in the day. To…
Q: What kind of repercussions does a data breach have for the security of the cloud? In order to combat…
A: Data loss in the Cloud A data breach is the purposeful or accidental disclosure of secure or…
Q: Implement the BFS algorithm to find the shortest path from S to G from te sketch below. N.b…
A: In this code first it creates two lists visited and queue. Here visited notes all nodes that are…
Q: How do you carry out an assessment to see whether an implementation impacts the effectiveness of…
A: The answer is given in the below step
Q: this C++ code is pre-existing and cannot be changed or modified. for it to work, the program has to…
A: Solution: Given, #include <iostream>#include <vector>using namespace std; int main() {…
Q: Find the equivalent decimal value of the following floating-point representation using IEEE 754…
A: The answer for the above question is given in the following step for your reference
Q: Why Should We Use the COCOMO Detailed Model? How should it be utilized?
A: Model COCOMO A model for software estimate is the COCOMO Model, often called the Constructive Cost…
Q: Which are the two primary categories of software products? Please provide an illustration of each…
A: Introduction Software is an assortment of information, guidelines, and programs, and decides that…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Given X = 10002 , Y = 111112 . Find X-Y and Y-X (justify your answer using the complement method).given 0011 0000 0000 0000 0000 0000 1111 0011 what is the answer when multipy by 25. Compute the Hamming distance of the following code: 0011010010111100 0000011110001111 0010010110101101 0001011010011110
- Compute the Hamming distance of the following code:00010000111101110010000011111011Compute the Hamming distances between the following pairs of n-tuples. a) (11110101), (01010100) b) (1001), (0111)Perform subtraction on the given unsigned binary numbers using the 2’s complement of the subtrahend. Where the result should be negative, find its 2’s complement and affix a minus sign. (a) 10011 − 10010 (b) 100010 − 100110 (c) 001001 − 110101 (d) 101000 − 010101 C++
- Perform subtraction on the given unsigned number using the 10’s complement of the subtrahend. Where the result should be negative, find its 10’s complement and affix a minus sign. Verify your answers. 125−1,800.Perform subtraction on the given unsigned binary numbers using the 2’s complement of the subtrahend. Where the result should be negative, find its 2’s complement and affix a minus sign. (a) 10011−10010 (b) 100010−100110Work out the following without using a calculator 111010102 + 21228 + ABC16 - 1238, Give your answer in decimal Given a binary number 11100101, find its equivalent in Decimal using Horner’s Rule Multiply the following binary numbers: 11011.101 by 101.111 Convert A74816 to octal equivalents Using Subtraction by 2’s Complement: 10100.01 – 11011.10
- Given 11110111 and 11111111, provide the following: AND OR XOR NOT (per individual number)Let these 2 variables be signed binary numbers, P=110100 (-12) and Q=000110 (6). a) Multiply P and Q b) Divide P by Q.Perform subtraction on the given unsigned binary number using the 2’s complement of the subtrahend. Where the result should be negative, find its 2’s complement and affix a minus sign. 101000−10101.

