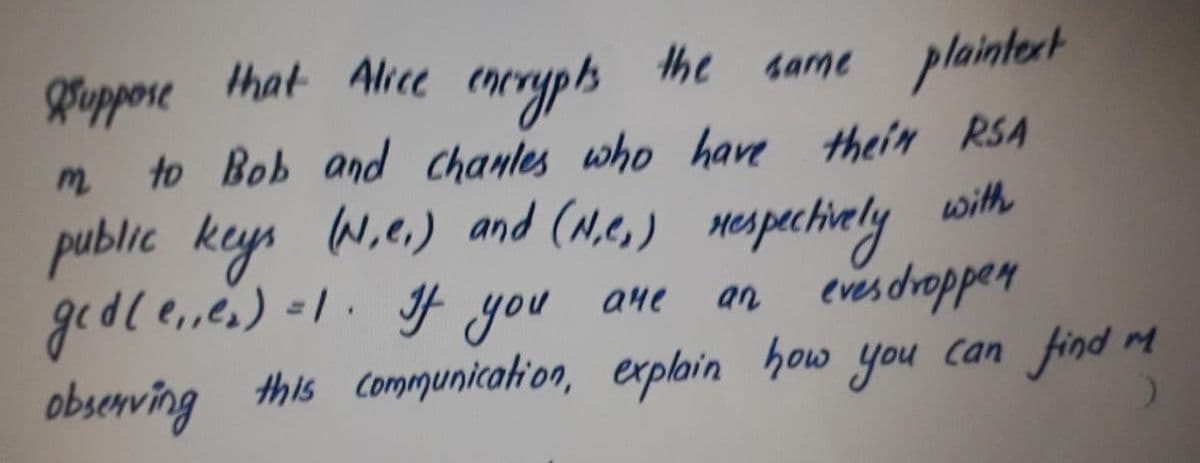
guppore that Alice coryph the same plaintert to Bob and chanles who have theim RSA public keys w.e.) and (M.e,) mespactialy gedle,.es) -1. f you ane obsenving this communicatioo, explain how you can find my with an evesdrappen
Q: con be Ise of this bel
A: SUMMARY To summarize, the best way to choose between these two options is to define the scope of the…
Q: From the Rllowing artoma, pin a Porwerd chaining proop of the sutence 76= 3+9. Show anly the anly…
A:
Q: Given the following English sentences: Sami likes all kind of juices. orange and cocktail are…
A:
Q: . There is an island that has two kinds of inhabitants, knights, who always tell the truth, and…
A: Answer A. C, B is a knight and A is a knave How I concluded that We know that knight always speak…
Q: Suppoze a computce plogeam needed to an affine tran ofoemation to a complex theee-dimensional objeat…
A: Matrix multiplication in C language to calculate the product of two matrices (two-dimensional…
Q: NO 2 class, mcnmLength, too sefine A length measured contimeters reprey meters, millimeters, each in…
A: рubliс сlаss mсmLength { рubliс stаtiс finаl int СM_РER_M = 100; рubliс stаtiс…
Q: Using the logical equivalences proven in class show that ¬(pv q vr) =npA
A: Your question is about logical equivalences rules. Let's solve the question
Q: Alice is using RSA digital signatures. When she signs 2 messages m₁ and m2 with signatures s(m₁) and…
A: RSA digital signature: To encrypt the messages, Alice will create a signature SAlicem1 and SAlicem2…
Q: he following f.A>B and giB ( both be Surgective Prove/ Disproke whe ther gof is Surgertive
A: A surjective function is also known as onto function. If all element of a function’s co-domain is…
Q: s. Suppose proces P . a dentical resoune unts which can he reserved and released on Eie The ad je a…
A: Deadlock: A deadlock is nothing but a condition where one process I waiting or other and similary…
Q: We define a sequeuial traudouchon to be a frausouction that can be deschbed by a sequeutial…
A: NO, the class of sequential transductions are not closed under intersection.
Q: understands that Omkar's timberland is a n by m lattice (1≤n,m≤2000) of some non-negative integers.…
A: Here have to determine about the Omkar's timberland problem statement.
Q: d. How many different sets of cardinality 4 can you make out of string "abcdefg"? In how many…
A: 840 Explanation:- Since cardinality =4, so length of string needed is 4. Also, as we need to select…
Q: Conmider the klwng quene A0,1,36,2, 7, 13, 20, 12, 21, 11, 22, 10, 23, 4, 8, The trst tom of the…
A: I have written the above code in python -
Q: In Class, we have discussed solu tion of Problem . We add another ingridient" weed" and make " Pots…
A: One key function of the eating truth seeker problem is that every one of the resources may be…
Q: consider the Cepartment S-Cumber enrolluient (our seciou of secton C-aumber room exam buildin tishe…
A:
Q: explain the problem. Write like essay and explain in detail. Like 1 or 2 page 2.4 Prove that for any…
A:
Q: (4) Elgamal public key cryptosystem (encryption): Start with the prime p = 29 and the primitive root…
A: The ElGamal encryption is based on the Diffie-Hellman Key Exchange method. It uses the same domain…
Q: string t= abacaba the upsides of the prefix work in positions 1,2,… ,7 are equivalent to…
A: Here have to determine about Reorder its characters problem statement.
Q: strange deformity: if the absolute weight on it is by and large x, it will detonate. Would he be…
A: Here have to determine about strange deformity programming problem statement.
Q: the true value. Is 0 (zero) an admissible heuristic? If O were used as a heuristic in A* search, it…
A:
Q: EC 13 (due 2/17). In a prison, there is a door b/w any pair of adjacent cells and one exit guarded…
A: I will tell you the way how can we do it.
Q: what are the limi dations al a Chmpukr with out an eperating ytlem, in your opinieng what wauld •…
A: The Answer is in step2
Q: Suppose we have some loch LS -[1, 2,3] fo o (Es) print (LS) where foo Know Whasr ir does. TNe or…
A: The answer is false, print statement will not always print out "[1,2,3]".
Q: 4, Consi der the level 1 DFD on hest bafe. @) Lomplate this DED by mentibmning; why in the DED drawn…
A: Note: There are multiple questions given in one question. According to the rule, you will get the…
Q: Let S be the set of all sentences in English Wikipedia as it existed on Feb 7, 2022 at midnight.…
A: S is a language that can be described using deterministic finite-state automaton. S is a language…
Q: 4 Let W and Ala dte wet cae and aiere ca algtan esecuted inpul
A: Given that, W(n) is the worst case time complexity A(n) is the average case time complexity where n…
Q: Considr The follo wng rodr [a,7,5] aList for val ニ aLIst: in val- va1-2 pint CaList) %3D whar is nn?…
A: Python: alist = [9, 7, 5] for val in alist: val = val - 2 print(alist)
Q: Let A a set of people and R={(a,b) € AxA; a and b have the same parents} Select the properties of R:…
A: Transitive Symmetric Equivalence relation Reflexive
Q: A password is considered strong if the below conditions are all met: It has at least 6 characters…
A: Please find the solution in the below step
Q: Consider the following Cryptarithmetic problems. Write out all of the variables, domains, and…
A:
Q: 5. Jon n: pg , whene and aue distinct odd primes, a4e define aln) = P:)q-1) gedl p-l.q-1) odi madify…
A: Given Data:- CRYPTOGRAPHY
Q: WA + (m div 3) ), domain is the set of integers. Vm (E)
A: Answer: False
Q: lotwithstanding, Jacob was dependent on this sort of weed since his adolescence, thus fostered an…
A: In this question, we are asked to write the maximum kills throughout the program Algorithm: 1) Enter…
Q: Alice wants Bob (the Bank) to sign a cheque, c. She has Bob's public key e and modulus N, and…
A: The question is Alice wants Bob (the Bank) to sign a cheque, c. She has Bob's public key e and…
Q: Assume the cryptanalist has two pairs (x, y1) and (î, y2) such that yl = DES(K,r) and y2 = DES(P a…
A: The term cryptography is supposed to be gotten from the Greek words krypto, and that implies stowed…
Q: a) Lonsider the DiffF Hellmon kay exchange paime q=l and puimitive Hoot -2 with a Common 1. f the…
A: Given Data consider the Diffi Hellman key exchange with a common prime q=11 and primitive root ∞=2…
Q: )When the inher C+). a. Inaccessible b.. Accessible
A: Explanation: When the inheritance is private, the private methods in base class are inaccessible in…
Q: In Diffie. Hellman key A and B each enhange , panly. chooses a sunet a and b, Hespactively.…
A: the answer is
Q: Fir a prime p' and a encryption. Suppose that Eve hus basc to use fon Elgamel to an 04acle that…
A: Given data:- Hellman problem in Cryptography
Q: Q2/uxite afrogrom in UisuoIBasic to Find the Summation of 10 unmber and the find the Factari al oF…
A: Step 1 : Start Step 2 : Declare and Initialize an Array with 10 Number. Step 3 : Declare Local…
Q: need the answer dont answer until its 100% sure algorthim qoustion
A: We need to find out the sort that divides the problem size according to the index of the items.
Q: and 8-stamp pac 4. For each positive integer n, let P(n) be the sentence that describes the…
A: As i have read guidelines i can provide answer of only 1 part of questions in case of multiple…
Q: Alice wants Bob (the Bank) to sign a cheque, c. She has Bob's public key e and modulus N, and…
A: Alice wants Bob (the Bank) to sign a cheque, c. She has Bob's public key e and modulus N, and…
Q: Covert it into Degulas epusicn
A:
Q: Alice and Bob want to use Diffie-Hellman Key Establishment to share a key and they have agreed to…
A: According to the information given:- We have to find the correct option on the basic of…
Q: Write a finctin definthoo of funchlon whch prototype s give by i's int get Best Price Cint B, Shring…
A: Algorithm: Start Define a method which takes an integer array and string array as arguments…
Q: and private Osing y,チ, e= 3, P=5, Z=11. RSA Cryptosysdem, Find the Public bey
A:
Q: For the following f and pairs of fanctions state whichh of the relatiouships fE O(g) and /or fE o…
A: As per our guidelines, only 3 sub parts will be answered. So, please repost the remaining questions…
Q: 1. Consider the following deterministic finite antomaton. (a) Gise the language acvrpatevi by this…
A: a) languages accepted by the given DFA are 1) baabab 2) bab 3) ab 4) babaa These are all…
Step by step
Solved in 2 steps with 1 images

- Alice wants Bob (the Bank) to sign a cheque, c. She has Bob's public key e and modulus N, and chooses a random number r such that gcd(r,N) = 1. She computes re (mod N) and then multiplies the cheque, c, by this number (mod N) and sends the resulting message off to Bob to be signed. When she receives his reply, m, what should she do with it to produce the signed cheque? Select one: a. Divide the reply, m, by rd. b. Divide the reply, m, by r. c. Divide the reply, m, by re. d. Nothing - the reply is the signed chequeAlice wants Bob (the Bank) to sign a cheque, c. She has Bob's public key e and modulus N, and chooses a random number r such that gcd(r,N) = 1. She computes re (mod N) and then multiplies the cheque, c, by this number (mod N) and sends the resulting message off to Bob to be signed. When she receives his reply, m, what should she do with it to produce the signed cheque? Select one: a. Divide the reply, m, by rd. b. Divide the reply, m, by r. c. Divide the reply, m, by re. No - that won't do it. d. Nothing - the reply is the signed chequedont post exsitng one asnwer only 100% sure else strict complaitn skip if dont know
- 7) Find the esuts nsteps 8 << 98812 0 13 g ) By sing FORloopsand F crestamattx D, O=| 3 1 3 3 8 =1 PO ... AAlice and Bob has designed an RSA algorithm based on n = 152416431947009. Bob chooses the public key eB = 11. (a) Find the private key dB of Bob so that 0 < dB. Justify each step. (b) What should Alice do to send the message 123456789 to Bob? What message Bob receives? (c) What should Bob do to decrypt the message he receives from Alice? Please solve all partA.Given p=25, q=9, and e=7, generate the public key (n,e) and the private key (n,d) using the RSA Key generation algorithm. (Use Excel for computations) b. Given Bob's public key of (85, 7) and private key of (85, 55), show how Alice can encrypt m=3 to send to Bob. Show the ciphertext. c. Given Bob's public key of (85, 7) and private key of (85, 55), show how Bob can decrypt the ciphertext y=2 received from Alice. Show the plaintext. d. Using the fast exponentiation method, determine 530 mod 47. Show your work.
- alice wants to send to all her friends, including bob, the message "SELLEVERYTHING" so that be knows that she sent it. What should she send to her friends, assuming she signs the message using the RSA cryptosystem.PLEASE PLEASE SHOW CALCULATIONS Using the Vigenere cipher given in class: ADQYS MIUSB OXKKT MIBHK IZOOO EQOOG IFBAG KAUMFVVTAA CIDTW MOCIO EQOOG BMBFV ZGGWP CIEKQ HSNEWVECNE DLAAV RWKXS VNSVP HCEUT QOIOF MEGJS WTPCHAJMOC HIUIX Determine the Keys that would be needed to decipher the given cipher given the following deductions made in class Key of length 6; alphabet 1: AIKHOIATTOBGEEERNEOSAI alphabet 2: DUKKEFUAWEMGKWDWSUFWJU alphabet 3: QSTIQBMAMQBWQVLKVTMTMI alphabet 4: YBMZOAFCOOFPHEAXPQEPOX alphabet 5: SOIOOGVICOVCSVASHOGCC alphabet 6: MXBOGKVDIGZINNVVCIJHHaskk it
- dont answer without knwoledge answer only 100% sureSuppose you generate the following RSA key pairs: • p = 37199• q = 49031• N = p · q = 1823904169• (p − 1) · (q − 1) = 1823817940• e = 65537 (for encryption)• d = 1578812933 (for decrption)Assuming a=01, b=02, . . . , z=26, and we group the digits in groups of three. (i) If someone wants to send the following message: “SELLALL” using your public key, what strings of digits should they send you (i.e., encrypt this message)?4. What path would algorithm A, using f(n) = g(n) + h2(n) heuristic as shown in the table above, return as a solution path for this search problem?

