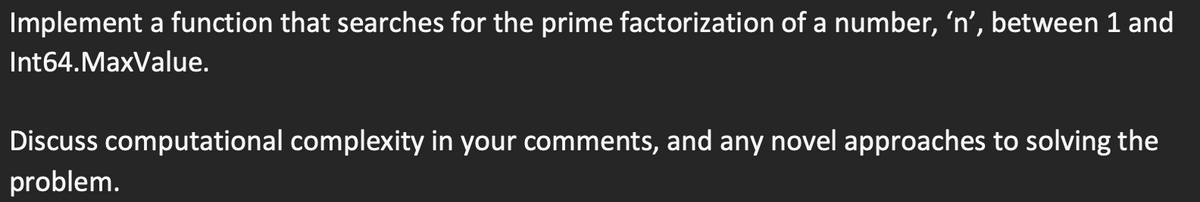
Implement a function that searches for the prime factorization of a number, 'n', between 1 and Int64.MaxValue. Discuss computational complexity in your comments, and any novel approaches to solving the problem.
Q: Is it expected of software developers to provide technology that can be maintained, even if their…
A: Software engineers must build code that is easy to maintain over time. This is true even if their…
Q: Prove L4 is regular Use DFA if you need to construct a machine
A: Please refer to the following step for the complete solution to the problem above.
Q: What would occur if there were no programs that could be relocated? This could make memory paging…
A: In this question we have to understand what would occur if there were no programs that could be…
Q: Just presume that there isn't any relocatable software code. How may the memory paging procedure be…
A: Assume that there is no relocatable software code in this question. That is the instruction that has…
Q: Review the five (5) primary OS functions and name the twenty (20) different OSes and their creators.
A: The Answer is given below step.
Q: When people talk about having a "memory vacuum," how do they mean it? Why does it happen, and how…
A: operating system verifies the memory access and aborts the program if it is invalid.
Q: How much should you rely on software service providers for all of your technology needs? What leads…
A: Outsourcing is the process of using external contractors for specific tasks and responsibilities.…
Q: Is it necessary to certify or license software engineers who design and develop systems with safety…
A: Yes, certifying or licensing software engineers who design and develop systems with safety…
Q: So, what exactly is meant when the term "operating system" is used? Generally speaking, an OS's two…
A: The answer is given below step.
Q: When does each phase of a software project's life cycle occur, and why?
A: the phases of the software development life cycle The seven steps that make up the software…
Q: Some experts in the field of information technology believe that businesses should employ ex-hackers…
A: A cyber-attack is an attack performed by hackers using numerous computers against many computers or…
Q: Can the process be sped up with additional RAM? What impact does more RAM have on a computer's…
A: Introduction RAM represents random access memory. it is available close to the processor, There are…
Q: he function accumulate_acronym has no parameters; it reads strings from standard input and…
A: Here is the code for the accumulate_acronym function in Python: def accumulate_acronym():…
Q: Consider the significance of wireless network technology in today's developing countries. Wireless…
A: 1. A computer network refers to interconnected computing devices that can exchange data and share…
Q: Question 9 nag .owing logarithm problem for the pos log_(x)2=(1)/(5) Full explain this…
A: The logarithmic problem you're asking about is to find the value of x in the equation:
Q: Individuals and computers located in the same area are able to connect with one another via the use…
A: Introduction: What we call a LAN is shorthand for a "local area network."A LAN is a computer network…
Q: Today, email provides two benefits that regular mail doesn't. You should include details to support…
A: In this question we have to understand benefits of email in comparison with regular mail. Let's…
Q: What's the dissimilarity between managing a computer system and designing one?
A: Computer architecture Computer design is the framework that determines how parts interact. A…
Q: Give a high-level explanation of real-time operating systems before delving into particular…
A: Here is your solution -
Q: The critical nature of continuous event simulation may be attributed to four factors.
A: SIMULATION OF CONTINUAL EVENTS - A continuous event simulation fundamentally refers to a simulation…
Q: What distinguishes circuit-switched networks from packet-switched networks?
A: Circuit-switched networks are designed to provide a dedicated communication path between two nodes…
Q: The three components that make up a computer's von Neumann architecture. A wide range of…
A: Neumann Architecture is characterised by the fact that the key components, as well as the visibility…
Q: In your opinion, which facet of the software engineering profession is the most important, and why?
A: Introduction: The question concerns severe challenges in the subject of software engineering, and…
Q: Computer Science Problem: Convert the following 32-bit two's complement binary numbers into…
A: (a) First bit is nagtive hence we came to know that number is negative Now , invert all the bits of…
Q: Discrete event simulation is crucial for four main reasons.
A: Discrete event simulation: Discrete event simulation is a technique for representing the many…
Q: As you can see the Ipv4 Cidr block range of Vpc and subnet -1, Which was Created in Aws Console. My…
A: Given that, IPv4 CIDR address for VPC= 10.0.0.0/24 IPv4 CIDR address for subnet 1= 10.0.0.0/25 Total…
Q: The majority of software, including operating systems, does not function flawlessly at first…
A: Solution: A company may protect its clients from risk and carelessness by taking the following…
Q: Part 2: Development of a Java Project The ultimate goal of this section is to generate a Java based…
A: Way to play game created in java with the use of mentioned content Each player marks one of their…
Q: Suppose we are performing a binary search on a sorted vector initialized as follows: // index 0 1 2…
A: The binary search algorithm would work as follows: Initialize start = 0, end = numbers.size()-1,…
Q: Create a program that calculates the total cost of a restaurant bill, including tax and tip.…
A: The C# code is given below with output screenshot
Q: What does email look like in your mind? Which form of email sending is the most efficient? Note your…
A: Email is sent across computer networks, primarily the internet and local area networks. Lists and…
Q: How is the hash value used for message authentication stored securely? Is it possible to break a MAC…
A: Introduction The authentication of messages is one more sort of security. In that it gives data…
Q: The structure of an OS may be broken down into the following layers: I'm curious as to the pluses…
A: The operating system's layered approach is a system structure. The operating system services are…
Q: What differentiates software engineering from other subfields and areas of engineering are the…
A: What differentiates software engineering from other subfields and areas of engineering are the…
Q: Question kha Order the numbers from least Put the lowest number on the lef…
A: Whichever number gives the lowest answer on division will be on left as we have to arrange in…
Q: An assault known as a distributed denial of service occurs when several users collaborate in an…
A: Distributed denial of service (DDoS) is a sort of cyber assault in which attackers use a wide…
Q: The fundamental concepts of software engineering do not take into account the things that are not…
A: The above question is solved in step 2 :-
Q: Java program that determines, given a number n, the nth Fibonacci number. Provide two solutions, one…
A: The following code is a Java program that calculates the nth Fibonacci number in the Fibonacci…
Q: We can wonder why we need cache memory since we already have RAM, which is a volatile memory similar…
A: cache is important because it improves the efficiency of data retrieval. cache is an extremely fast…
Q: Suppose we are performing a binary search on a sorted vector initialized as follows: // index Ø 1…
A: Given: vector <int> numbers (-5, -1,0, 3, 9, 14, 19, 24, 33, 41, 56, 62, 70, 88, 99);int index…
Q: Create Java program Part one. Create a class called a BankSystem. Then, create the following…
A: Given: A task to create a Java program called BankSystem that manages bank accounts Task: Part…
Q: Which of the following does Ubuntu utilize to get an IP address? In order to understand what you are…
A: Introduction Ubuntu is an open-source Linux-based operating system that is free to use and ad-free.…
Q: Is it possible to identify the overarching purpose of software engineering? What, in particular, are…
A: The aim of software engineering may be summed up, and this is accurate.
Q: Analyze the pros and cons of using microcontrollers with pins that may serve many functions.
A: The microcontroller is straightforward to connect additional RAM, ROM and I/O port. Once a…
Q: Examine the ways in which wireless networks are used in underdeveloped countries. Wireless…
A: Introduction:- Due to its benefits, several businesses are ditching traditional LANs and physical…
Q: Just presume that there isn't any relocatable software code. How may the memory paging procedure be…
A: Introduction: Software that can have its execution address changed is referred to as relocatable…
Q: what exactly are the OS's primary building blocks?
A: The primary building blocks of an Operating System (OS) include: Kernel: The core component of an…
Q: A time diagram for Direct Memory Access (DMA) that synchronizes with the clock?
A: Memory on a computer: It is the location where information and methods for carrying out tasks are…
Q: Which one of the following issues do you believe is currently having the most significant impact on…
A: Introduction: The question concerns a major problem in the realm of software engineering, and the…
Q: Which fundamental principles of software engineering are often disregarded, and why is this the…
A: Introduction: It was challenging to keep up with the hardware, which generated various problems for…
Question 12 kana
. use python
Full explain this question and text typing work only
We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this line
Step by step
Solved in 5 steps with 2 images

- Refine the is_palindrome function to work with arbitrary strings, by ignoring non-letter characters and the distinction between upper- and lowercase letters. For example, if the input string is "Madam, I’m Adam!" then you’d first strip off the last character because it isn’t a letter, and recursively check whether the shorter string "Madam, I’m Adam" is a palindrome. c++Give a recursive definition of the function that takes ? (?ℎ??? ? ∈ ℕ) and gives the number of strings of length ? over the alphabet Σ = {0,1,2} that contain two consecutive symbols that are the same.Give Description of GetNumberOfConsoleInputEvents function.
- Below,enter code to complete implementation of a recursive function sum_all_integers(), which takes an input n and adds all intergers preceding it, up to n: add_all_integers(n):Write programs with these input and output Given positive integers m and n, find the number of ontofunctions from a set with m elements to a set with n elements.Write a recursive function named decrypt, which takes a string s and a dictionary d where each key in the dictionary is a string word associated with a secret code as its key. This function should return the list of all possible ways (order it returns it in doesn’t matter) in which the string s can be decoded by splitting it into secret codes and separating the corresponding words of the decoded word with spaces. For instance, calling decrypt('turing', {'turing': 'A', 'tur': 'B', 'ing': 'C', 'tu': 'D', 'ring': 'E', 'ri': 'F', 'ng': 'G'}) returns ['A', 'D E', 'D F G', 'B C']. def decrypt(s: str, d: {str: str}) -> [str]:
- By using java, Write a recursive function that finds the maximum element in an array ofintegers, based on comparing the first element in the array against themaximum in the rest of the array recursively.Implement the following function in C programming language that get a string, and compute an array of non-empty tokens of the string containing only lower-case letters. For example: ● For a string "abc EFaG hi", the list of tokens with only lower-case letters is ["abc", "hi"]. ● For a string "ab 12 ef hi ", the list of such tokens is ["ab","ef","hi"]. ● For a string "abc 12EFG hi ", the list of such tokens is ["ab","hi"]. ● For a string " abc ", the list of such tokens is ["abc"]. ● For a string "+*abc!! B" the list of such tokens is empty.That is, we break the string using the spaces as delimiters (ascii value 32), and look only at the tokens with lower-case letters only . The function get_tokens gets a string str, and returns the array with the tokens containing only lower-case letters in the correct order. The length of the array should be the number of tokens, computed in count_tokens. char** get_tokens(const char* str); For example:● get_tokens("abcEFaG…Implement a function (Java or pseudocode) that will accept a mathematical expression which containssquare brackets, curly brackets and normal brackets (i.e. “[ …]”, “{ …}” and “( … )”) as the input andwould return whether the expression has matching brackets or not. The input expression will be given asa String array where each element in the array is a bracket (one of “[”, “]”, “{”, “}”, “(”, “)”) number ora mathematical operator. It should return true if expression has matching brackets and false otherwise
- Implement the following function, without using any data structure. /* Given two vectors of chars, check if the two vectors are permutations of each other, i.e., they contains same values, in same or different order.e.g., V1=[‘a’,’b’,’a’] and V2=[‘b’,’a’,’a’] stores same multi-set of data points: i.e., both contains two ‘a’, and one ‘b’. e.g., V3=[‘a’,’c’,’t’,’a’] and V4=[‘a’,’c’,’t’] are not same multi-set. V3 contains two ‘a’s, while V4 has only one ‘a’. Note: when considering multiset, the number of occurrences matters. @param list1, list2: two vectors of chars @pre: list1, list2 have been initialized @post: return true if list1 and list2 stores same values (in same or different order); return false, if not. */ bool SameMultiSet (vector<char> list1, vector<char> list2)Write pseudocode for a function Det-Quicksort(A, p, r) that receives array A[1..n], and indices p and r. The function should sort the subarray A[p..r] recursively (meaning you should call itself). You can also use a function LinearSearch(A, p, r, v) that searches subarray A[p..r] for an element of value v and return its index (in case it exists) in O(r − p) time. (Just to give you something to compare to, the solution has 8 lines.)Write a function(in pyhton) that RECURSIVELY merges the characters in two given strings in alphabetical order. For example, mergeTwoString(("aghp","bdct") results "abcdghpt".

