Machine A Instruction Count (millions) CPI Arithmetic 8 2 Instruction Class Load/Store 6 4 Branch 7 1
Q: How can processor execution time be reduced? I found one way to reduce execution time: by reducing…
A: The formula for Execution Time in terms of clock rate is given below: Execution Time = No. of…
Q: For each of the three most often used file management methods, kindly provide an example.
A: Ordinary files, often known as simple files, can be found in programmes like notepad, paint, C++,…
Q: When converting from on-premises servers to an laaS design, are there any governance challenges?
A: Infrastructure as a service IaaS stands for Infrastructure as a service, it gives memory, storage,…
Q: Using Dev c++ Create an application containing 5 prices, such as $2.34, $7.89, and so on. The…
A: Here is the c++ code: See below steps for code.
Q: Which element provides the storage service in a client/server system?
A: Client/server system The element that communicates with the user is known as client.…
Q: Using For-Loop and If-statement, find all the numbers divisible by 3 in the 2D array "a2". Do not…
A: Program Plan Iterate through rows of 2d array. Iterate through columns of 2d array. If the number…
Q: Which of the following code snippets represents well-written code and the best desi problem (assume…
A: For the given all the code Ans (B) is correct ans
Q: Write a function solution that, given a string S consisting of N letters 'a' and/or 'b' returns true…
A: Step-1: Start Step-2: Declare a variable S and take input from user Step-3: Call function solution,…
Q: When moving from on-premises servers to an laaS architecture, what governance concerns should you be…
A: We need to explain cloud governance concerns we should be aware of during moving to IaaS from…
Q: An operating system handles the tasks of numerous open programmes at once via the multitasking…
A: Multitasking is the simultaneous performance of several tasks by hardware or software towards a…
Q: What does "parallel processing" really imply when it is used
A: The management process in clinical supervision involves parallel processing. This supports learning…
Q: What can you do to protect your organization from fake data?
A: Fake data: Fake data is information that has been altered intentionally, is incorrect, or has not…
Q: If you turn on the computer for the first time but don't hear the fan running or see any indicator…
A:
Q: A file manager is what? Describe the Windows Explorer software in detail. Include a few places for…
A: In light of the facts provided, we must discuss file managers and Windows explorer. Windows has a…
Q: What are the two most popular wireless technology types?
A: Wireless technology gives the capacity to convey between at least two elements over distances…
Q: ntial threats that HTTPS protects against and the mechanism by whic
A: Hypertext Transfer Protocol Secure (also known as https) combines HTTP (Hypertext Transfer Protocol)…
Q: Today, designing microprocessors and the systems that use them must take into account limiting…
A: introduction: The many parts of a computer require logic and control in order to operate. included…
Q: How does your business find possible security holes before they cause problems in its network?
A: Introduction: spotting network weaknesses before they become issues Firewalls may be used both…
Q: Using software that is hosted in the cloud as opposed to a client-based, more conventional storage…
A: This inquiry highlights the several advantages of a cloud-based programme over a conventional…
Q: What techniques may be used to determine if the operating system of a laptop has been tampered with?
A: An operating system is tempered means someone has done some changes in your Operating system. There…
Q: Q2: Complete the main programs and writing its functions, classes and find the Area for each shape:…
A: The following steps need to be taken for the given program: Create a Triangle class with a…
Q: On the other hand, the great majority of computer systems employ fewer levels than what the OSI…
A: While the TCP/IP protocols offer the principles on which the Internet was constructed, the Open…
Q: If true, how do time-sharing operating systems differ from distributed operating systems?
A: Operating system An OS goes about as a delegate between the client of a PC and PC hardware. The…
Q: Give an explanation of a cassette drive and how it varies from a typical tape recorder for storing…
A: A common cassette recorder is what is meant when people talk about a "cassette drive" in the context…
Q: Before one can recognise multiprocessor systems, one has to understand interprocessor communication.
A: Answer: I agree that understanding interprocessor communication is necessary for recognizing…
Q: The sequencing of assembly language
A: No, all assemblers and compilers do not reorder assembly language instructions in the same way. Each…
Q: Write the status of the Carry (C), Zero (Z), Negative/Sign (N), and Overflow (V) flags after an…
A: below I have provided a handwritten solution to the given question
Q: Congrats! You work for Zillow now. Your first task is to write an algorithm that recommends…
A: Algorithm: 1. Input Apartment size 2. Input number of pets 3. Input rent 4. Display output
Q: Explain Propositions for Complexity Reduction.
A: Introduction: Complexity reduction: Reduced complexity aids in the simplification of your strategy,…
Q: Why is it so important to have a repair manual on hand while disassembling a notebook?
A: Repair manual is a guide book which is given my the manufacturer with the laptop/pc/notebook which…
Q: Which top four characteristics are most likely to be clustered together in software development? ...…
A: It is largely used whilst the security and many different factors of the software aren't an awful…
Q: What suggested firewall setup practices are there, and why are they so important?
A: When operating a firewall, it is advised that you adhere to the guidelines outlined in the following…
Q: What distinguishes a Key Derivation Function from other researched families of secure hash functions…
A: FUNCTION OF KEY DERIVATION KEY DERIVATION FUNCTION (kef), a cryptographic technique, is used to…
Q: Write code in js. String Challenge Have the function Stringchallenge (str) take the str parameter…
A: Below I have provided a js program for the given question. Also, I have attached a screenshot of the…
Q: Are you in agreement with Mukherjee's claim that the foundation of sustainable futures may be a…
A: Introduction: The field of physical sciences involves meticulous observation and analysis of natural…
Q: Why is it so crucial to fight cyber crimes?
A: Introduction: Because data and information are so valuable in the modern world, there has been an…
Q: The number of nodes that make up the strongest linkedlist is unknown. Is there a specific one that…
A: Introduction: A linked list is a special kind of data structure in which each individual component,…
Q: How is data compressed by the operating system's High Performance File System
A: Introduction HPFS: The high-performance file system (HPFS) was created specifically for the IBM OS/2…
Q: One of the most important advantages of multiprocessor systems is the increased flexibility they may…
A: statement: Two-dimensional materials offer the advantage of flexibility, which allows them to be…
Q: Question 1: Which of the following standard algorithms is not Dynamic Programming based. 01 02 03 04…
A: The solution for the above-given question is given below:
Q: A0o
A: Given according to question: since u[n] is a step signal we have to handle this before and then make…
Q: How can a network prosper and reach its potential if these three requirements are not met? In as few…
A: Introduction: Genuine interest in their connections is shown in successful networking relationships,…
Q: Use a real-world example to illustrate the importance of interrupts to the machine's functioning…
A: To interrupt is to put an end to something or to make something come to an end. Real world example…
Q: Using a try-except approach, write a Python program to check whether a string input by a user is…
A: Python One of the most well-liked programming languages in the world is Python, according to…
Q: The difference between a mouse push event and a mouse click event is that the former occurs before…
A: Mouse Click: noun [C] information technology, internet (also mouse-click) us. You just need a few…
Q: How can we stop a central processing unit from wasting cycles while it is executing many commands?…
A: Introduction: A CPU in a PC performs an action or a series of processes known as computer processing…
Q: When converting from on-premises servers to an laaS design, are there any governance challenges?
A: Architecture for IaaS: With the IaaS model, cloud a providers host infrastructure such servers,…
Q: The word used to describe the display that is often used in desktop computers is cathode ray tube,…
A: Due to this: Cathode-ray tubes, a prevalent kind of display in desktop computers, are the subject of…
Q: How exactly does Direct Mapping work? It is what?
A: Each memory block in the main memory is mapped directly to a specific line in the cache using this…
Q: const size_t n = 50; ALTE
A: The answer is
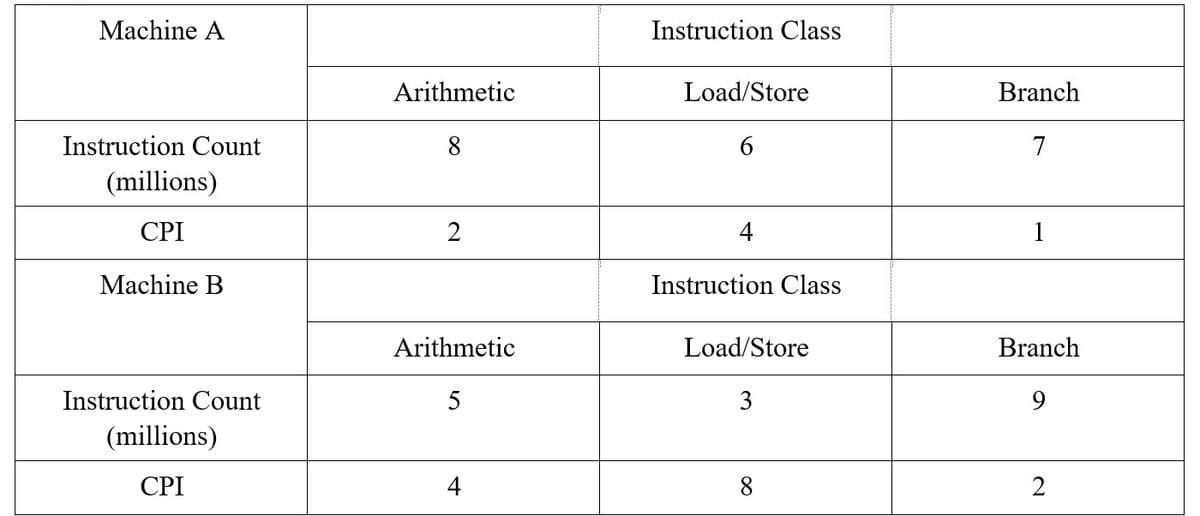
I am really having a hard time finding the average CPI for machine A. Could you help me step by step on how to do this?
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 3 images

- Linked List Question Which of the following statements are NOT correct about the ADTs? ADTs are only supported in Java programming language. All implementations of the same ADT will have the same time complexity for all the operations of the ADT. ADTs allow programmers to focus on important aspects of data without worrying about implementation details.Course: Data Structure and Algorithims Language: Java Kindly make the program in 2 hours. Task is well explained. You have to make the proogram properly in Java and attach output screen with program: Restriction: Prototype cannot be change you have to make program by using given prototype. TAsk: classBSTNode { Node left; Node right; int data; publicBSTNode(int _data);// assign data to_data and assign left and right node to null } class BST { BSTNoderoot; public BST();// assign root to null void insert(int data);// this function insert the data in tree which maintain property of BST boolean Search(int key); this function search the data in bst and return true if key is found else return false public void EvenPrint(Node n)// this function only print the data which are even, make this function resursive public void OddPrint(Node n)// this function only print the data which are odd, make this function resursive public void PrimePrint(Node n)// this function only…Computer Science create a guiuse java function for homestay rental system -add -display -delete -update
- Create a basic grading system app using Java Programming language The program should include the ff. topics: Operators Control Structures and Array OOP Encapsulation and Inheritance Polymorphism and Abstraction Exception Collections Input and Output StreamThe organization working on deforestation wants you to create software using your object-oriented concepts for trees. Trees has category of pine and eucalyptus. You must store information of all of these trees. Identify classes, their attributes and inheritance (if any) and implement following functionality: Input function Update info of pine tree Update info of eucalyptus Display functionProblem:Write a program to simulate the work of processes scheduler by using RR algorithm. Theprogram should have three classes which are:1. Process Class: This class represents the process where it has process id, executetime and completion time. Arrival is assumed to be zero all times. Process id shouldbe unique and the class create it for each process. Provide the required methodsaccordingly.2. RRSchedule Class: This class represents the work of the scheduler. It has mainlytwo lists of processes, quantum size, and clock. One of the list will be as a recordof the processes while the other is to work on to execute the process in CPU. Theclock should be a simple counter to represent timing to run the list of processes.The method list should be as following:a. Pop method: to remove the process from the top of the list.b. Push method: to insert the processes at the end of list after it is interruptedand still has to go to CPU again.c. RunRR method: to represent the job of RR scheduler.…
- Data structure & Alogrithums java program A system of caves is a group of connected undergrounds tunnels. Design an ADT for a cave and cave system. An archaelogist should be able to add a newly discovered cave to a cave system. He/she can enter this system through only one cave and exit the system only through a different cave. Duplicate caves - based on GPS coordinates - are not permitted. Archaelogoist should also be able to list the caves in a given cave system.Computer ScienceQuestion: Draw a sequence diagram to illustrate the interaction that takes place between the Client, the TumbleDryer and Bosch objects, and System.out when the describe() message is sent. You will need to read through the code of the TumbleDryer and Bosch classes to trace the sequence. The sequence diagram should be in this format like the diagram below. Client Class public class Client { public static void main(String[] args) { Implementation impl1 = new Bosch(); Appliance apl1 = new TumbleDryer(impl1); apl1.describe(); } } Appliance Class public abstract class Appliance { Implementation impl; public Appliance(Implementation impl) { this.impl = impl; } public abstract void describe(); } Washing Machine Class public class WashingMachine extends Appliance { public WashingMachine(Implementation impl) { super(impl); } public void describe() { System.out.println("Washing Machine");…Accomplish the following for the given class diagram. Elevator 1. Create the class implementation using C++ upDirection 2. Create one object from class Elevator and store it in the stack memory. 3. Create one object from class Elevator and store it in the heap memory. 4. Test all the functions of the two objects • currentFloor: int • move (numFloors : int): void stop (): void + status (): string
- Serialization and Deserialization using Json and XML The Atom class This is the front end of the application. There are 12 members. Atom Class Fields Properties + «c# property, set» Name : string + «c# property, set» Symbol : string + «c# property, set» Proton : int + «c# property, set» Neutron : int + «c# property, set» Weight : double Methods + «c# constructor» Atom() + «c# constructor» Atom( string name, int proton, int neutron, double weight, string symbol) $+ Parse(string objectData) : Atom $+ GetAtoms() : List<Atom> + ToString() : double Description of class members Fields: There are no fields in this class. Properties: All the properties have public get and set Name – this is a string representing the name of this atom. Both the getter and setter are public. Symbol – this is a two-letter string representing the…CPU Scheduling Algorithm Simulator in C++Instructions:Create a .zip file consisting of code, output files, readme file .The readme file should explain briefly your code. The simulator will consists of following classes:(i) Process: The data members of this class should store process id, arrival time in the ready queue,CPU burst time, completion time, turn around time, waiting time, and response time. The memberfunctions of this class should assign values to the data members and print them. A constructorshould also be used.(ii) Process_Creator: This class will create an array of processes and assign a random arrival timeand burst time to each process. Data members, constructor and member functions can be writtenaccordingly.(iii) Scheduler: This class will implement the scheduling algorithm. The class will maintain a readyqueue of infinite capacity (i.e., any number of processes can be accommodated in the queue). Theready queue should be implemented using the min-Heap data structure…MemoryManagerFirstFit The MemoryManagerFirstFit class is derived from the MemoryManagerBase class. Based on the TODO entries in memory_manager_first_fit.h and memory_manager_first_fit.cpp, implement the functions as instructed. memory_manager_first_fit.cpp #include "memory_manager_first_fit.h" #include using namespace std; MemoryManagerFirstFit::MemoryManagerFirstFit(int size) { // Set up the list of memory blocks with the info for this initial // unallocated block. memory_block b; // TODO: Fill in the appropriate values here based on the data elements // you added in the header file. // Add the block to the list of blocks m_blocks.push_back(b); } // Allocate a block of memory of the given size // We will walk through our current list of blocks and // find the block with the first fit. int MemoryManagerFirstFit::allocate(int size, string name) { // TODO: Implement the allocate logic here // // Iterate through the current list of blocks // and find the first one that is big enough…









