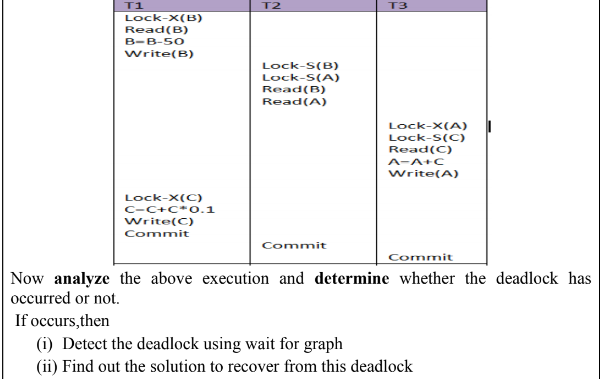
Now analyze the above execution and determine whether the deadlock has occurred or not. If occurs,then (i) Detect the deadlock using wait for graph (ii) Find out the solution to recover from this deadlock
Q: Compare with example/graph between the following: 1. Overfitting and Underfitting
A: Given: Write the difference between overfitting and underfitting.
Q: Please show the complete depth first traversal of a disconnected graph, recursively. Use the…
A: Below i have answered:
Q: Explain briefly [In a few paragraphs] 1) The relationship between undecidable problems like the…
A: The answer is given below:-
Q: The Conway game is played between two players in turn on a given finite vertices on a plane.…
A: The convey game is played between two players in turn on a given finite vertices on a…
Q: Analyze the graphs about the deadlock conditions with justifications. Write the cycle sequence if…
A:
Q: Mr. Williams is given a graph with p nodes rooted at node 1. Each node(X) of the graph has a pair of…
A: Solution as per the given information
Q: In this problem, let REF(x.i) → DEF(x.k) denote that the linkerwill associate an arbitrary reference…
A: /* Module 1 */ /* Module 2 */int main() int…
Q: explain with proper working that how we can come up with these answers.
A: Consider the given :
Q: Question: Trace the following graph from S to G using Branch & Bound with Dynamic Programming and…
A: Best path for A to G is S-B-C-G and S-A-D-G both have path value less than 14
Q: Problem 3. Give a linear time, depth-first-search algorithm to find the size of the largest…
A:
Q: Explain the principle of BFS or DFS algorithms in detecting the shortest possible path in the map…
A: The algorithm used in detecting the shortest path in google maps is the A* Algorithm. The algorithm…
Q: Question: Trace the following graph from S to G using Branch & Bound with Dynamic Programming and…
A:
Q: Not all augmenting paths are equal, and starting with different paths leads to different residual…
A: Your answer is given below. Introduction :- Given that, Not all augmenting paths are created equal,…
Q: Model the following problem as a network flow problem and write down the corresponding linear…
A: first we have to formulate given graph in matrix form [0, 1, 1, 0, 0] [0, 0, 1, 0, 1] [0,…
Q: Do implementation of DFS and BFS for the following graph: B E K M
A: DFS is applying depth first search strategy while solving graph. Suppose our root node is A then DFS…
Q: [a] Identify three ways to solve the problem of finding the shortest distance between all pairs of…
A: a) Identify three ways to solve the problem of finding the shortest distance between all pairs of…
Q: ack problem
A: NOTE: ACCORDING TO COMPANY POLICY WE CAN SOLVE ONLY 1 PART. YOU CAN RESUBMIT THE QUESTION AGAIN WITH…
Q: Given an implementation of an algorithm, you want to check formally its run-time performance before…
A: Answer: It depends on the recursion in the algorithm This is because, if a function recursively…
Q: Apply the augmenting algorithm to the following flow 4/6 B D 8/8 6/8 3/3 A |1/6 1/7 Z 1/3 3/10 5/9 C…
A:
Q: Given the following adjacency matrix: Nodes A B C E F A 1 C 1 1 1 E 1 1 F i) Draw a graph based on…
A: Answer:
Q: Short Answer: Write simple paths and prime paths for the following graph. 2 4
A: Simple Paths In the figure, followings are the simple paths. Length 0: Following nodes represents…
Q: Given the following graph: the state-space tree is generated by a backtracking algorithm for the…
A: An array path[V] that should contain the Hamiltonian Path. path[i] should represent the ith vertex…
Q: i. Plot a graph of SA vrs r for r=6 to 40 with a change in r as 0.2 ii. Plot a graph of SA vrs r for…
A: I have given solution in step2
Q: Question 24. Given an implementation of an algorithm, you want to check formally its run-time…
A: Given:
Q: In order to plot a graph of f(x)=z and g(y)=z in the same graph, with t as a parameter. The function…
A: We must select the proper choice from the four presented.
Q: In recurrence relation, how many sub-problems we get in every subsequent call to recursion? a.3 b.…
A: In recurrence relation, how many sub-problems we get in every subsequent call to recursion? It is…
Q: You have to show (no explanations necessary) how the following reductions work. Please remember that…
A: Answer: I have given answer in the handwritten format.
Q: Is it still feasible to starve if deadlock is prevented via deadlock-avoidance schemes? Your…
A: Deadlock: When a deadlock occurs, a collection of halted processes occurs, each of which is holding…
Q: Consider the following allocation graphs G1 and G2. What can be said about the deadlock conditions?…
A: the answer is given below :
Q: Given two sequences X and Y, we want to find Z i.e., the longest common subsequence (LCS) of both X…
A: LCS or Longest Common Subsequence is the maximum sequence between two strings that is common.
Q: Part(a): Explain Race Condition with example. Part(b): What are the conditions that need to hold to…
A: a) Race condition occurs when the correct working of a system or program depends on timing of one…
Q: We discussed how Prim’s algorithm runs on a graph G = (V,E)in O(|V|2). However, we also noted that…
A: Dear Student, Let a graph consists of very large number of vertices say n and even a larger number…
Q: how could someone solce this one? The Chinese postman problem: Consider an undirected connected…
A: For undirected connected graph if we want to find out the shortest route from a given starting node…
Q: Yes, even if deadlock is prevented by deadlock-avoidance schemes, starvation is still possible. Your…
A:
Q: i) Detect the deadlock using wait for graph ii) Find out the solution to recover from this deadlock
A: T1 T2 T3 Lock-X(B)Read(B) B=B-50…
Q: Explain the procedure that allows all the processes to get their resource allocation for the…
A: Given question has ask the procedure that allows all the processes to get their resource allocation…
Q: ; Solving Recurrence Relations Draw the recursion tree for T(n) = 3T(Ln/2J) + cn, where c is a…
A: Answer is given below .
Q: You are given a weighted, undirected graph G = (V, E) which is guaranteed to be connected. Design…
A: Graph of edges, E = V(V-1)/2 nearly to V2 'V' invocation in Dijkstra algorithm => O (VE log V)…
Q: Write pseudocode for a dynamic solution to find the shortest paths in a DAG, only pseudocode. Don’t…
A: Let the vertices V be {v1……vn}. The pseudocode for the dynamic solution for finding the shortest…
Q: Consider the problem of finding the length of a "longest" path in a weighted, not necessarily…
A: Simple Technique: Calculating the length of the longest path from each node using DFS is a…
Q: Read the lecture slides about NN pruning heuristics, and write the pseudo code of computing the…
A: According to the information given:- We have to write pseudo code for maximum distance between…
Q: Assume an interaction matrix with a minimum of 12 nodes. Demonstrate how the Kruskal algorithm can…
A: Kruskal’s Algorithm is used to find the minimum spanning trees. It treats every node as an…
Q: Given the graph below implement an array based storage backend for a map application to leverage for…
A:
Q: What information does the banker's algorithm need to know a priori in order to avoid a deadloc
A: The answer is...
Q: Problem 3. Recollect that the standard implementation of the Dijkstra's algorithm uses a priority…
A: // C++ is using to write the dijkstra's algorithm uses a priority queue that supports extract-min()…
Q: Draw a wait for graph to detect deadlock in given situation.
A: Given table contains, 4 processes P1, P2, P3 and P4. For each process, some resources are allocated…
Q: You are given a weighted, undirected graph G = (V, E) which is guaranteed to be connected. Design…
A: Using Johnson;s algorithm, used to find all shortest pair paths in G using of Dijkstra and…
Q: 1 8 2 7 3 2 11 4 8 14 4 10 6 5 4,
A: We are given a graph and we are going to find out its MST using Kruskal's algorithm. Note: In…
Now analyze the above execution and determine whether the deadlock has
occurred or not.
If occurs,then
(i) Detect the deadlock using wait for graph
(ii) Find out the solution to recover from this deadlock
Step by step
Solved in 3 steps with 1 images

- Write a JavaFX program to read a username and password from the user and store it in a databse in a encrypted manner during the signup. Validate given user by reading his credentials by decrypting it from the database. (use shift methods for encryption and decryption ex: A-C, B-D, C-E).Rewrite the same code with a different logic make sure you have the same output. <?php$cookie_name = "user";$userID = $_COOKIE[$cookie_name];if(!isset($_COOKIE[$cookie_name])){ echo "Please login in first!<br>"; exit();} include "dbconfig.php";$conn = new mysqli($hostname, $username, $password, $dbname) or die($conn->connect_error);$name = $_POST['name'];$description = mysqli_real_escape_string($conn, $_POST['description']);$term = mysqli_real_escape_string($conn, $_POST['term']);$enrollment = $_POST['enrollment'];//Query course name$Rid = '';$userGivenFacultyID = $_POST['Fid'];$userGivenRoom = $_POST['Rid'];$queryRid = "SELECT Rid FROM TECH3740.Rooms WHERE CONCAT(Building,Number) like '%$userGivenRoom%' ";$resultRid = mysqli_query($conn, $queryRid);$rid_row_ct = $resultRid->num_rows;if($rid_row_ct = 1){while($ridRow = $resultRid->fetch_assoc()){$Rid = $ridRow['Rid'];}} $queryRoomSize = "SELECT Size FROM TECH3740.Rooms WHERE Rid = $Rid";$resultRoomSize =…Suppose Alice has r and w rights over the file book. Alice wants to copy r rights to book to Bob. a.Assuming there is a copy right c, write a command to do this. b.Now assume the system supports a copy flag; for example, the right r with the copy flag would be written as rc. In this case, write a command to do the copy. c.In the previous part, what happens if the copy flag is not copied? Note:Follow the concept of access control matrix and do not use commands like chmod.
- ProblemFor the purposes of collecting entropy or obtaining cryptographically robust pseudo-random data, you should use a library-level access to EGADS. On a system like Microsoft Windows, for instance, where there isn't a built-in API for obtaining it, you might need entropy.86. If only the primary is active, the transaction is allowed to commit as soon as its commit log record is written to stable storage at the primary site. This is a. One Safe b. Two Safe c. Two-very Safe d. Very SafeSuppose Alice has r and w rights over the file book. Alice wants to copy r rights to book to Bob. Assuming there is a copy right c, write a command to do this. Now assume the system supports a copy flag; for example, the right r with the copy flag would be written as rc. In this case, write a command to do the copy. In the previous part, what happens if the copy flag is not copied?
- Book reference: Windows PowerShell Step by Step 3rd Edition - Ed WilsonChapter 16 6. What parameter can be used to bypass the below confirmation prompt? Remove-ADGroupMember -Identity TestGroup1 -Members UserGroupTest Confirm Are you sure you want to perform this action? Performing operation "Set" on Target "CN=TestGroup1,OU=TestOU,DC=NWTraders,DC=Com". [Y] Yes [A] Yes to All [N] No [L] No to All [S] Suspend [?] Help (default is "Y"):Look the following code and describe the difference between commands "read -p" and "read -s -p" #!/bin/bash# Register 5 users for user_no in {1..5}; do echo "Registering user no: $user_no" read -p "Enter username: " username read -s -p "Enter password: " password # do something here to check password validity # do something here to register the userecho -e "\n" doneHey, so would i have to make three seperate java files labeled in order EncryptorOne EncryptorTwo EncryptorMain
- The following code could deadlock. True or Falsevoid thread1() { pthread_mutex_lock(lock1); pthread_mutex_lock(lock2); pthread_mutex_lock(lock3); // ... pthread_mutex_unlock(lock2); pthread_mutex_unlock(lock3); pthread_mutex_unlock(lock1);}void thread2() { pthread_mutex_lock(lock1); pthread_mutex_lock(lock2); pthread_mutex_lock(lock3); // ... pthread_mutex_unlock(lock1); pthread_mutex_unlock(lock2); pthread_mutex_unlock(lock3);}How to write this code to a Pseudo Code? from threading import Thread, Lockfrom datetime import datetimeimport time # 2shared_resource = ""lock = Lock() # 1modify_readers = Lock();n_readers = 0; # 3fifo_lock = Lock() def wait():time.sleep(2)### def acquire_reader():global n_readers, modify_readers, fifo_lockfifo_lock.acquire()modify_readers.acquire()fifo_lock.release() n_readers += 1;if(n_readers == 1): lock.acquire() modify_readers.release()### def release_reader():global n_readers, modify_readers, fifo_lockmodify_readers.acquire() n_readers -= 1;if(n_readers == 0): lock.release() modify_readers.release()### def write_normal():while True:global shared_resource, fifo_lock fifo_lock.acquire()lock.acquire()fifo_lock.release() print("Writing normal")shared_resource = datetime.now() lock.release()wait()### def write_reverse():while True:global shared_resource, fifo_lock fifo_lock.acquire()lock.acquire()fifo_lock.release() print("Writing reverse")shared_resource = str(datetime.now()…In the case of password storage in a file, why is hashing the passwords a much better idea than encrypting the password file a much worse idea?

