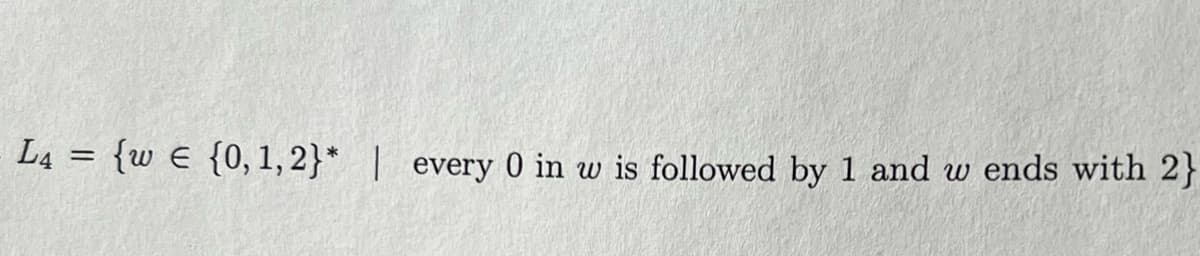
Prove L4 is regular Use DFA if you need to construct a machine
Q: Can the process be sped up with additional RAM? What impact does more RAM have on a computer's…
A: Introduction RAM: In general, a computer's processing speed increases with RAM speed. Upgrade to…
Q: Your data warehouse project team is now arguing whether or not they should first construct a data…
A: Information storage facility The data warehouse stores information for later use in analysis and…
Q: Does associative memory vary from regular memory? Which choice is more expensive, and why is it more…
A: Yes, associative memory is different from regular memory. Associative memory is a type of memory in…
Q: What precisely are these things called triggers? Which function are they meant to serve? How can the…
A: Triggers are SQL procedures that execute automatically when certain commands, including INSERT,…
Q: Which four advantages of continuous event simulation are considered to be the most significant?
A: Introduction: Continuous event simulation is a modeling technique that is used to simulate the…
Q: It is possible to describe the distinctions between the Harvard and von Neumann designs as follows:
A: Introduction: Computer architecture refers to the arrangement of the components that comprise a…
Q: Think about the impact that wireless networks may have in nations that are still developing. Why are…
A: In developing nations, the impact of wireless networks can be significant. The main reasons for…
Q: An assault known as a distributed denial of service occurs when several users collaborate in an…
A: Distributed denial of service (DDoS) is a sort of cyber assault in which attackers use a wide…
Q: What exactly does it mean to use a "green computer"?
A: Introduction: Green computing is described as the study and use of information technology with the…
Q: How is the router's startup procedure specified?
A: The answer is given below step.
Q: Accessible resources for cloud computing are listed. Which organizations conduct their activities…
A: The term "cloud computing" refers to the on-demand provision of computer services, which may include…
Q: When does each phase of a software project's life cycle occur, and why?
A: the phases of the software development life cycle The seven steps that make up the software…
Q: What's the dissimilarity between managing a computer system and designing one?
A: Computer architecture Computer design is the framework that determines how parts interact. A…
Q: What are the goals of Artificial Intelligence (AI) research and development? Include two examples…
A: Object of AI Artificial intelligence (AI) combines technologies like machine learning and deep…
Q: Could two network interfaces theoretically have the same MAC address? Can you explain this? Is…
A: Introduction: When a computer connects to a network, whether it be public or private, this is known…
Q: What distinguishes remote authentication from local authentication in terms of user identification?…
A: Given: What is the difference between local and remote user authentication? Which presented the…
Q: Before delving into specific examples, provide a general overview of real-time operating systems.…
A: Introduction: - A real-time operating system is a type of operating system designed to handle…
Q: Determine and explain the two primary functions of an OS.
A: An operating system is a software that connects the user to the computer system. Every desktop,…
Q: There are three different DNS zones in Windows: primary, secondary, and stub.
A: The DNS (Domain Name System) is divided into a number of separate zones known as DNS zones. A DNS…
Q: So, what exactly is meant when the term "operating system" is used? Generally speaking, an OS's two…
A: The answer is given below step.
Q: Does associative memory vary from regular memory? Which choice is more expensive, and why is it more…
A: Associative memory and regular memory are two different types of computer memory that serve…
Q: contrasting two transmission methods (twistted piars, coxial cable, microwave, satalitte, fibre…
A: Transmission Media: The repeater is the series circuit connecting the transmitter and the receiver…
Q: What makes a fiber-coaxial network different from a standard one?
A: What makes a fiber-coaxial network different from a standard one answer in below step.
Q: Examine the ways in which wireless networks are used in underdeveloped countries. Wireless…
A: Introduction:- Due to its benefits, several businesses are ditching traditional LANs and physical…
Q: ronic mail over conventional mail for modern communication. Provide evidence in the form of examples…
A: Introduction: Dispatch is an provident and effective way to communicate with others online. Dispatch…
Q: Is a topology that uses mesh capable of handling the challenges of traffic, security, and…
A: Step 2 is where we get to the bottom of why Mesh topology is so good at addressing security, being…
Q: Examples of real-time operating systems abound. What sets this OS apart from the competition? When…
A: Given: In this article, we'll talk about real-time operating systems and how their performance and…
Q: without defined order but which permit duplication, i.e., more than one element. We define the…
A: Given : sum : List × List -> ListThis function should take as arguments two lists representing…
Q: What differentiates software engineering from other subfields and areas of engineering are the…
A: What differentiates software engineering from other subfields and areas of engineering are the…
Q: (Python) Plot the following functions and identify all cross-over points between all these functions
A: In this question we have to write a python program to plot this function in a graph and find the…
Q: 1. How to make a comparison with ilustration between Class Diagram and Entity-Relationship Diagram…
A: Given: Information on Class Diagrams and Entity-Relationship Diagrams Knowledge of Object-Oriented…
Q: Why do embedded systems depend on microcontrollers for so much of their functionality?
A: Why are microcontrollers used in embedded systems so frequently?CPUs that have been combined with a…
Q: Two typical topologies for local area networks (LANs) are the mesh and the ring. Could you kindly…
A: INTRODUCTION: Network topology describes the physical or logical configurations of nodes and links…
Q: Could you please name 10 operating systems and describe their 5 main features?
A: An operating system is a programme that runs application programmes and acts as a communication…
Q: round on the evolution of co
A: Introduction: The foremost people employed the first counting system. They counted with sticks,…
Q: If we can assume that the keys in the list have been arranged in order (for example, numerical or…
A: The practical testing of the generated functions provides a suitable counterpoint to the theoretical…
Q: Perhaps some of the basics in software development are missing. Explain?
A: Basic concepts in software development include algorithms, data structures, programming languages,…
Q: Cout FA b3 N FA b2 C2 Z Figure 036) FA bl C₂ XO yo FA ao bo Cin (c) Figure Q3(c) shows a functional…
A:
Q: Discrete event simulation is crucial for four main reasons.
A: Discrete event simulation: Discrete event simulation is a technique for representing the many…
Q: Is it necessary to certify or license software engineers who design and develop systems with safety…
A: Yes, certifying or licensing software engineers who design and develop systems with safety…
Q: What kinds of services and applications may be hosted in a network that is based on the cloud?
A: Numerous services and applications can be found on a cloud network, including:
Q: Give an example of how the CPU of a computer could affect the performance as a whole.
A: Introduction: The CPU is constantly obeying computer programme instructions that tell it which data…
Q: Identify two elements that database systems implemented in the 2000s to facilitate data-analytics…
A: The two aspects that assisted the database system in managing the growth of its data-analytics…
Q: Review the five (5) primary OS functions and name the twenty (20) different OSes and their creators.
A: The Answer is given below step.
Q: What distinguishes remote authentication from local authentication in terms of user identification?…
A: What distinguishes remote authentication from local authentication in terms of user identification?…
Q: When referring to subprograms, variables, and other objects in code, which is better to use: fully…
A: To seek specific information, he must first speak with another officer in the sales department.…
Q: Utilize a program for recognizing named entities to illustrate how to utilize it. Explain Hobb's…
A: INTRODUCTION: Named entity identification focuses mostly on identifying the unique significance and…
Q: What about software and services that are hosted in the cloud?
A: Cloud computing refers to the delivery of computing resources, such as servers, storage, databases,…
Q: In the Designer, the bounding box of an object may be used to infer information about the item's…
A: A bounding box is a rectangle that encloses an object in an image or a 3D space. It defines the…
Q: Give a high-level explanation of real-time operating systems before delving into particular…
A: Introduction Operating systems are software programs that deal with the equipment and software…
Please refer to the following step for the complete solution to the problem above.
Step by step
Solved in 2 steps

- Assign pizzasInStore's first element's numCalories with the value in pizzasInStore's second element's numCalories. #include <stdio.h>#include <string.h> typedef struct Pizza_struct { char pizzaName[75]; int numCalories;} Pizza; int main(void) { Pizza pizzasInStore[2]; scanf("%s", pizzasInStore[0].pizzaName); scanf("%d", &pizzasInStore[0].numCalories); scanf("%s", pizzasInStore[1].pizzaName); scanf("%d", &pizzasInStore[1].numCalories); /* Your code goes here */ printf("A %s slice contains %d calories.\n", pizzasInStore[0].pizzaName, pizzasInStore[0].numCalories); printf("A %s slice contains %d calories.\n", pizzasInStore[1].pizzaName, pizzasInStore[1].numCalories); return 0;} I tried 10 time but I cant solve it so please help mePlease Explain this code Step by Step (How Code Works). #include <stdio.h>#include <string.h>#include <stdlib.h>char password[10] = "1234";struct library{int id;char title[40];char author[20];float price;};//dynamic booksstruct library *b[100];int num = 0;void Add(){int count = 0;printf("How many books' info do you want to enter? ");scanf(" %d", &count);for (int i = 0; i < count; i++){b[num] = (struct library *)malloc(sizeof(struct library));//local variablesint id;char title[40];char author[20];float price;printf("Enter the following information about the book:\n");printf("Enter ID: ");scanf("%d%*c", &id);fflush(stdin);fflush(stdin);printf("Enter title: ");scanf("%[^\n]%*c", title);printf("Enter author's name: ");scanf("%[^\n]%*c", author);printf("Enter price(in Tk): ");scanf("%f", &price);//check if information exists alreadyfor (int i = 0; i < num; i++){if (b[i]->id == id){printf("Book with id %d already present in the library",…Programming in C#: Write a console-based application that displays every perfect number from 1 through 10000. A number is perfect if it equals the sum of all the smaller positive integers that divide evenly into it. For example, 6 is perfect because 1, 2, and 3 divide evenly into it and their sum is 6. Use format strings(field size 8, right alignment) to show all perfect numbers. Display the results as seen below. 6 28 496 8128
- C++ Help. "qwerty" is a string commonly found in weak passwords. Remove all occurrences of "qwerty" from secretStr. Then, assign lengthStr with the length of secretStr. Ex: If the input is qwertyvk*M7$gKXhJ%P9qwerty, then the output is: Remaining string: vk*M7$gKXhJ%P9 Length: 14 Note: string.find(item) returns the index of the first occurrence of item in string. If no occurrence is found, then the function returns string::npos. string.replace(indx, num, subStr) replaces characters at indices indx to indx+num-1 with a copy of subStr. Code provided to complete: #include <iostream>#include <string>using namespace std; int main() { string secretStr; int index; int lengthStr; cin >> secretStr; index = 0; lengthStr = 0; /* Your code goes here */ cout << "Remaining string: " << secretStr << endl; cout << "Length: " << lengthStr << endl; return 0;}void removeStudent(){System.out.print("\n Enter StudentID to remove: ");long id =sc.nextLong();int pos = searchStudentID(id);if(pos == -1)System.out.println("\n ERROR: No student found having same ID: " + id);elsecourses.remove(pos);} int searchStudentID(long studentID){for(int c = 0; c < students.size(); c++)if(studentID == students.get(c).getId())return c;return -1;} The code is supposed to prompt the user to enter a studentID and if it is in the records then it will be removed, but instead it just prompts me to enter and when i enter the ID, it does not remove the ID (I display the data again after I supposedly removed it but it is still there) and just returns back to the menu. What can I do to correct it?void removeStudent(){System.out.print("\n Enter StudentID to remove: ");long id =sc.nextLong();int pos = searchStudentID(id);if(pos == -1)System.out.println("\n ERROR: No student found having same ID: " + id);elsecourses.remove(pos);} int searchStudentID(long studentID){for(int c = 0; c < students.size(); c++)if(studentID == students.get(c).getId())return c;return -1;} The code is supposed to prompt the user to enter a studentID and if it is in the records then it will be removed, but instead it just prompts me to enter and when i enter the ID, it just exits and goes back to the menu. is there something wrong with my code?
- Write in C Language Frequent Letter Your Facebook account has just been hacked and you want to change its password. To create a strongpassword, Facebook just recommended you two strings S and T, each contains N lowercase English letters. You want to choose a password containing N lowercase English letters such that the i th character is either the i th character of S or the i th character of T. For example, if S = icyz and T = ixpc, then there are 8 different passwords that you can choose: icyz, icyc, icpz, icpc, ixyz, ixyc, ixpz, ixpc. The strength of your password is defined as the number of occurences of the most frequent letter. For example, the strength of icyz is 1 and the strength icpc is 2. You are wondering what is the strength of the strongest password that you can choose.PHP Write a matchIPAddress function Write a function matchIPAddress($str) that takes a string representing an IP address as a parameter. The function should return true if the IP address is valid, and false if it is not. An IP address consists of a series of 4 numbers on the range 0-255 separated by dots (e.g. 192.168.0.1). Use regular expressions with capture groups and some additional validation in your solution (e.g. preg_match).]Given following code and write comments for those code #include <stdio.h>#include <stdbool.h>#include <string.h>#include <ctype.h> #define MAX_PASSWORD_LENGTH 128#define MIN_PASSWORD_LENGTH 10#define ALLOW_PASSPHRASE true#define MIN_PHRASE_LENGTH 20#define OPTIONAL_TESTS_REQUIRED true#define MIN_OPTIONAL_TESTS_TO_PASS 4 bool isStrongPassword(char *password);void printTestResults(char *password, bool isPassphrase, int optionalTestsPassed); int main() { char passwords[][128] = { "password", "mypassword", "thisismypassword", "passssword", "This is my password phrase1", "Tinypw1", "Ireallydontlikehavingtomakeupnewpasswordsallthetime1", "Iloveyouxxxooo1", "Boom**********!", "IHATEPWORDS1!", "ihatepwords1!", "IHatePwords!", "IHatePwords", "my pass phrase does not need to pass tests", "short pass phrase", "x", "x1", "Zxcvbnmnas7",…
- # Write python codes here.print("Total E-Customer:", ECustomer.count)c1 = ECustomer("James")c1.setProductDetails("TV",35000,"Air Cooler", 9000)c2 = ECustomer("Mike")c2.setProductDetails("Mobile",20000,"Headphone",1200,"Fridge", 45000)c3 = ECustomer("Sarah")c3.setProductDetails("Headphone", 1200)print("=========================")c1.printDetail()print("=========================")c2.printDetail()print("=========================")c3.printDetail()print("=========================")print("Total E-Customer:", ECustomer.count)Output:Total E-Customer: 0=========================Name: JamesProducts: TV, Air CoolerTotal cost: 44000=========================Name: MikeProducts: Mobile, Headphone, FridgeTotal cost: 66200=========================Name: SarahProducts: HeadphoneTotal cost: 1200=========================Total E-Customer: 3Question 5 Write a program in C++ that ranks a data set of Poker hands.2 3 4 5 6 7 8 9 10 J Q K A Suit: S H D C**This program should be able to tell the difference between higher hands of flushes and rank them accordingly. Full explain this question and text typing work only thanksfunction myChoice(items) {if (!this.value && !this.items) {this.items = items[0];} else if (!this.value || (params.length > 0 && params[0] == "rechoose")) {let index = Math.floor(Math.random() * (this.items.length - 0)) + 0;this.value = this.items[index];return this.value;}return this.value;} var a = myChoice([1, "a", 3, false]);console.log(myChoice(3, 12));console.log(myChoice(51, -2));console.log(myChoice("happy", false));console.log(myChoice([1, 2, 3]));console.log(myChoice("rechoose"));console.log(myChoice(a, a)); these are directions and examples myChoice( items ) This function accepts a list of items as input and creates a function that returns a randomly-chosen item. After choosing a random item, that same item will be always be returned, regardless of the functions input, with one exception. If the first input is the string 'rechoose', then a new random item will be chosen and therafter returned. this is KEYYYY!! Examples var a = myChoice( [1, "a", 3, false]…











