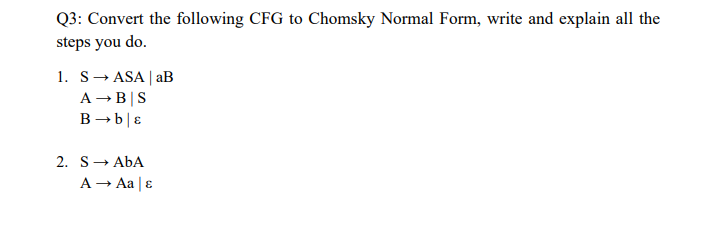
Q3: Convert the following CFG to Chomsky Normal Form, write and explain all the steps you do. 1. SASA | aB A → B|S B→b & 2. S→ ABA A → Aa | &
Q: A system administrator must monitor live programme issues caused by the development team's updates.…
A: In today's fast-paced software development environment, system administrators play a crucial role in…
Q: This is the error I am getting could I get an explanation on why this is please and how to fix it
A: From the given expected output in green, we are expected to display message only if it is the first…
Q: Neither of us knows enough about operating systems to have a meaningful conversation about how they…
A: Running Structures (OS) is an essential bridge linking a computer's hardware and package. They…
Q: Why not make new recruits learn the new computer system instead of theorising?
A: As technology rapidly evolves, organizations frequently adopt new computer systems to streamline…
Q: clude computer vision, face recognition, and sentiment analysis. Also, text mining. These methods…
A: Computer vision mostly focuses on extracting data from digital photos and utilising it for other…
Q: A friend has requested for your help in establishing a private computer network at his house. The…
A: Star Topology:In this configuration, all devices connect directly to the central router or…
Q: Write a code using C# for the following images.
A: Below code uses multiple threads to simulate the producer and consumer operations. The producer…
Q: What are the primary distinctions between restarting and reloading a service?
A: Understanding the Concepts of Restarting and Reloading a ServiceIn computer systems, a service is a…
Q: What information should be included in your abstract in order to construct your own system?
A: In order to construct your own system, there are several key pieces of information that should be…
Q: How do you use the =HLOOKUP function when looking for a formual to calculate an answer, using Named…
A: Accoridng to the inforamtion given:-We have to define =HLOOKUP function
Q: Complete the following tasks on CorpServer: Power off the system. Then power the system back on and…
A: As I do not have a Linux system that is maintained by the administrator so not possible to provide…
Q: Explain why rapid software development and delivery is so essential. Why continue providing updated…
A: The rationale behind providing updated versions of a flawed product that has already been delivered,…
Q: How would infrastructure and endpoint devices be interconnected in a local area network? What type…
A: In a local area network (LAN), endpoint devices like computers, printers, and IP phones are linked…
Q: What advantages does the Hypertext Transfer Protocol (HTTP) offer network applications? What else is…
A: What is HTTP: HTTP stands for Hypertext Transfer Protocol. It is a protocol that governs the…
Q: Instead of using a theory-based approach to train the new employees on the new computer system, why…
A: What is computer system:Computer system is a combination of hardware, software, and user interfaces…
Q: Create a SinglyLinkedList class method called reverse that reverses the order of the list's items.…
A: A singly linked list which refers to the one it is a type of linked list in which each node which it…
Q: Technically, RAM stands for random-access memory. Each list should have its own separate list. Why…
A: Random Access Memory (RAM) is vital in embedded approaches due to its fast interpretation and symbol…
Q: Which of the following does is NOT a term used with respect to storage devices? A) Queue…
A: In relation to storage devices, the word "Volume" is not frequently used. A "Volume" is a logical…
Q: How does the data dictionary work into each of the six phases of the DBLC?
A: The Data Dictionary is a crucial component in the design and development of a database system. It…
Q: Two networks are connected by a gateway, file server, utility server, or printing server.
A: What is gateway:A gateway is a network device or software that serves as an entrance or exit point…
Q: Two networks are connected by a gateway, file server, utility server, or printing server.
A: A gateway, file server, utility server, or printing server can be used to connect two networks,…
Q: Choose the best answer. An algorithm to determine if a graph with n=>3 vertices is a star is:…
A: Graph theory, a fundamental branch of mathematics, studies graphs as mathematical structures that…
Q: Which IP datagram sections vary in your systems' ICMP messages? Stable fields? Which constant? Edit…
A: ICMP stands for Internet Control Message Protocol. It is a protocol used by network devices to send…
Q: What benefits does the deep web offer businesses that rely on IT systems?
A: An information system (IS) which refers to the one it is a formal, sociotechnical, organizational…
Q: What KPIs define effective software maintenance?
A: Effective software maintenance is crucial for ensuring the smooth functioning and longevity of…
Q: What purpose do protocols serve within network communication? Clarify the protocols that enable a…
A: Hello studentGreetingsThe communication between a web server and a web client is a fundamental…
Q: What are some situations where SSH might be useful? Can you provide an exhaustive inventory of SSH…
A: A strong network protocol called SSH (Secure Shell) provides computers with secure and encrypted…
Q: can you please fix the code to resolve the error:Oh no! You've got an error in your assembly code…
A: Assembler programming which refers to the one it is a type of computer programming that involves…
Q: If you want your network to be productive and effective, there are three conditions that must be…
A: In order to achieve productivity and effectiveness, a network must fulfill three crucial conditions.…
Q: The inner workings of operating systems are beyond our ability to explain. When people hear the term…
A: When people hear the term "operating system," it typically refers to a software component that acts…
Q: Enter File Name to read: ASCII | Percent | Code 97 | 0.14000 | 98 0.08000 0.13000 99 | —— 101 001…
A: Huffman Tree:The Huffman tree is a binary tree used in data compression algorithms. It assigns…
Q: rces, inve
A: As we are asked to investigate health information system issues utilising technology and…
Q: Show that: ¬q 1) p→¬q 2) (p∧r)∨s 3) s→(t∨u) 4) ¬t∧¬u where ¬ is denied.
A: To show that ¬q holds based on the given statements, we need to derive it using logical deductions.…
Q: An operating system and a client application have very distinct perspectives on virtual machines.…
A: A virtual machine (VM) in computing is a software-based simulation of a physical computer that runs…
Q: How can the performance of an ArrayList be assessed?
A: Assessing the Performance of an ArrayListArrayList, a resizable array implementation in the Java…
Q: Disc prefetching is exactly what it sounds like: preloading data onto a disc. What are the benefits…
A: Disc prefetching is a technique used to enhance the performance of data retrieval from a disk by…
Q: What is the functional difference between writing the value 5 into cell number 6 and copying the…
A: Computer memory can be conceptualized as a sequence of cells, each with a unique address. These…
Q: You are given a list of integers. Write a function in Python to find the maximum sum that can be…
A: We use dynamic programming to solve this problem.We initialize an array dp of…
Q: Why use private network addresses? Can a private network datagram become accessible via the…
A: Private network addresses are used to designate IP addresses that are not routable on the public…
Q: Show that the following issue belongs to the NP category: We are given a set S of integers and an…
A: The problem is deciding whether a subset of a given set S of integers with component product equals…
Q: The challenge is to find ways to simplify complex programming languages. What method would you use…
A: To simplify complex programming languages, one approach to categorize the words is through lexical…
Q: What distinguishes the numerous unsigned binary formats, other than the underscore character?
A: It is possible to represent positive numbers or zero using unsigned binary formats, which represent…
Q: Schedulers require attention. Therefore, why do we require a scheduler that sees so far ahead?
A: Schedulers play a critical role in managing and optimizing the allocation of resources, tasks, or…
Q: What do you hope to accomplish by overseeing a group? What aspects of management do you find…
A: Overseeing a group entails assuming a management role and exercising leadership to achieve certain…
Q: A network with these three characteristics might be effective and efficient. Provide an exact…
A: Steadfastness is a vital aspect of effective and efficient networks. The term refers to the…
Q: ascertain the objective of visual information and media.
A: in the following section we will learn about the reasons that state possibility to ascertain the…
Q: 1. Add two numbers in PHP with form. 2. Create a php web form to submit the name and age of an…
A: 1. The below code shows how to add two numbers in PHP. The code first defines two variables, $var1…
Q: age processi
A: In image processing, the image quality assessment (IQA) is an essential task, aiming to evaluate the…
Q: Would you visit a comparable web page? Why?
A: 1) A comparable web page refers to a web page that shares similarities or comparable features with…
Q: Perhaps it would be useful to have a summary of the advantages of utilising tables in databases. How…
A: 1. Organized Data: Tables provide a structured way to organize and store data. They consist of rows…
Step by step
Solved in 3 steps

- Even if CNF may be converted to DNF, why is it easier to satisfy Disjunctive Normal Form (DNF) than Conjunctive Normal Form (CNF) in run time?What is the output of the following ML (or SMLNJ) code (use ~ to represent negation ) fun square(x:int) = x * x; map (~, map(square(, map(~, [1 -2 3]))); write your solution as it would appear in ML3. Write the difference between structure and union. Also discuss a scenario where using aunion will be more appropriate with explanation
- Construct DFA to accept (0 + 1)* (00 + 01 + 11) (0 + 1)* over the language∑ = {0, 1} Note:please solve it by more than one way with explanation all steps4. Repeat Programming Exercise 3 by declaring numl, num2, and num3, and average of type double. Store 75.35 into numl, -35.56 into num2, and 15.76 into num3.Write a BNF description of the precedence and associativity rules defined below. Assume the only operands are the names a,b,c,d, and e. Precedence Highest *, / +, - - (unary) Lowest =, /= Associativity Left to right
- show a parse tree and a leftmost derivation for each of the following statements:For the following pairs of expressions, find a unifier for each pair if a unifier exists. If a unifierdoes not exist, explain why.(a) p(X,Y) and p(a,Z)(b) p(X,X) and p(a,b)(c) f(X,Y) and f(a,g(a))(d) q(X) and ¬q(a)C++ question Question 2: syllable count Problem statement In English, a syllableLinks to an external site. is a unit of pronunciation having one vowel sound (a, e, i, o, u). For example the word innocent has 3 syllables as we can break it into 3 sounds like in·no·cent. As a general rule of thumb, the Oxford English Dictionary says, “with most adjectives and adverbs of more than one syllable, and with all those of more than two syllables,” “the normal mode” of forming the comparative and superlative is by using “more” and “most”. For example we say more or most innocent rather than using innocenter or innocentest. Imagine you are an engineer of a team developing English grammar checker. Your task is to write a function named count_syllables to count number of syllables in a given English word of all lower case letters.
- (c) Write a BNF description of the following precedence and associativity rules. Assume theonly operands are the names a,b,c,d, and e.Using the symbolization key given, translate each English-Language sentence into SL.M: Those beings are men in pajamasL: Those beings are lymers O: Those beings are orangutans 1) Those beings are neither orangutans nor lymers.2) If those beings are lymers, then they are neither orangutans nor men in pajamas.3) Unless those beings are men in pajamas, they are either lymers or they are orangutans.Using the following variable bindings: (setq x ‘(a b c d)) (setq y ‘(1 2 3 4)) Using only variables x and y, car, cdr, and cons, provide Lisp S-expression to generate: (a 1) (b 2) (c 3) (d 4))

