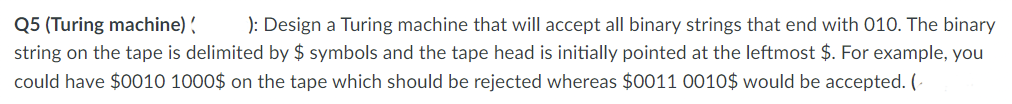
Q5 (Turing machine) ): Design a Turing machine that will accept all binary strings that end with 010. The binary string on the tape is delimited by $ symbols and the tape head is initially pointed at the leftmost $. For example, you could have $0010 1000$ on the tape which should be rejected whereas $0011 0010$ would be accepted. (
Q: A gateway, file server, utility server, or printing server establishes a connection between computer…
A: That's correct. A gateway, file server, utility server, or printing server are all types of servers…
Q: Two of the most essential qualities of a functional network are its effectiveness and efficacy. We…
A: In the context of networks, both effectiveness and efficacy are crucial qualities that contribute to…
Q: Please provide at least three distinct examples of the responsibilities of the WinMain (beginning)…
A: The Win Main function is liable for setting the application. This is one of the first duties…
Q: Solve the following linear programming problem with a simplex table: 3x1+x2+5x3→max x1+x3≤12…
A: To solve the given linear programming problem using the simplex method, we need to set up the…
Q: To generate a trace, the traceroute programme can transmit IP datagrams of various sizes to X.…
A: Understanding Traceroute and Packet CaptureTraceroute is a network diagnostic tool used to track the…
Q: What interactions exist between machine-to-machine (M2M) and the Internet of Things (IoT)?
A: Machine-to-Machine (M2M): M2M refers to direct communication between two or more devices without…
Q: Uniprocessor systems require essential sections to safeguard shared memory from multiple processes.…
A: Because SMP systems share memory, programmed that process large amounts of data or move data between…
Q: What ethical and safety concerns may a business encounter when utilising BI technologies and data?
A: The utilization of Business Intelligence (BI) technologies and data has become increasingly…
Q: Given a system with 2 memory channels and 4 DRAM DIMMs (2 DIMMs per channel), each DIMM has: • 1…
A: Addressing in physical and virtual memory spaces refers to the mechanism by which a computer's…
Q: Some content creators have gone so far as to establish their own communities. How would you…
A: Google's network is a vast and varied ecosystem of users, examines, and platforms. It has shown…
Q: What information should be included in your abstract in order to construct your own system?
A: In order to construct your own system, there are several key pieces of information that should be…
Q: What separates computers and IT from non-computer media? Technology changes everyday. Consider…
A: Information Technology (IT) and computers contain reshaped our world radically. The ability to…
Q: Neither of us knows enough about operating systems to have a meaningful conversation about how they…
A: Running Structures (OS) is an essential bridge linking a computer's hardware and package. They…
Q: IP, Subnet Mask, Subnet Information? field value Host IP subnet mask Subnet bitcount Subnet count…
A: The provided information includes an IP address, subnet mask, and subnet details.
Q: (b) Determine which of the following two graphs are planar. Justify your answer and show your work.…
A: In graph theory, the terms "K5" and "K33" refer to specific types of complete bipartite graphs.A…
Q: IP, Subnet Mask, Subnet Information? field value Host IP subnet mask Subnet bitcount Subnet count…
A: Given:IP address= 172.33.2.34Subnet mask= 255.255.255.252
Q: When the College opens, your email arrives on the BMCC web server. The BMCC web server will refuse…
A: The ARP protocol is used to identify the local computer receiving Internet data by mapping the IP…
Q: 31. Consider the network shown below, and assume that each node initially knows the costs to each of…
A: Distance-Vector algorithm is iterative, asynchronous and distributed algorithm. The algorithm is…
Q: 5.question What advantages does fiber optics have over other media
A: A fiber-optic cable, it is also known as an optical-fiber cable, and is similar to an electrical…
Q: given input word, return the list of abbreviations. ex) word => ['word', 'wor1', 'wo1d', 'wo2',…
A: 1. Define a function `generate_abbreviations` that takes a word as input.2. Create an empty list…
Q: What are the primary distinctions between restarting and reloading a service?
A: Restart and reloading are indispensable in the circumstance of service administration in central…
Q: The new wireless network infrastructure causes patient monitor connection concerns in many…
A: In the context of a healthcare ability, the wireless network communications is a dangerous part of…
Q: What role does WiFi play in the evolution of computer technology if this is the case?
A: The advent of WiFi (Wireless Fidelity) has drastically altered the way we use computers and other…
Q: can you please fic the error I am getting in the LC3 simulator: Oh no! You've got an error in your…
A: The issue here is that you're trying to use the label 'PROMPT' as an offset, but the LEA instruction…
Q: This section should provide a concise summary of an operating system's two main functions.
A: An operating system (OS) serves as a crucial component of any computer system, providing an…
Q: Simply stated, "Kernel components" are the essential building blocks of every modern operating…
A: The essential building blocks that make up the kernel of a contemporary operating system are the…
Q: The smallest logical units of the desired functionality of a system are called processes.
A: What is processes: Processes are units of execution within an operating system, representing running…
Q: There is a complete lack of knowledge about the inner workings of an operating system.
A: An operating system (OS) is essentially a piece of software that controls the resources of a…
Q: What causes DFDs to be unbalanced?
A: Data Flow Diagrams (DFDs) are graphical representations that illustrate the flow of data within a…
Q: We want to have a responsive UI where the rectangles will line up as follows for different screen…
A: <!DOCTYPE html><html lang="en"><head> <meta charset="UTF-8"> <meta…
Q: Instead of using a theory-based approach to train the new employees on the new computer system, why…
A: It is an effective approach for onboarding employees to get a mandatory training and immediate…
Q: How operating systems carry out operations is beyond the scope of our investigation.
A: What is an OS: An operating system (OS) is software that manages computer hardware and provides…
Q: Technically, RAM stands for random-access memory. Each list should have its own separate list. Why…
A: Random Access Memory (RAM) is vital in embedded approaches due to its fast interpretation and symbol…
Q: Examine the differences between the file-oriented and database-centric strategies. List some of the…
A: The serious difference sandwiched between the file-oriented system and the database-centric strategy…
Q: With continued use, a computer's performance may degrade. Using a disc defragmenter and disc…
A: Over time, a computer's performance can degrade due to various factors such as file fragmentation…
Q: Why is network segmentation bad? To restrict access to broadcast domains, decrease bandwidth usage,…
A: Network segmentation is not inherently wrong. Instead, it is a crucial strategy for network security…
Q: We lack the knowledge to make an informed evaluation of an operating system's inner workings.
A: What is an OS: An operating system (OS) is a software program that manages computer hardware and…
Q: dition of a sele
A: A flowchart is a type of diagram that uses shapes and symbols to visually represent the sequence of…
Q: Risk management study. Identify assets, threats, vulnerabilities, risks, and mitigation. Category…
A: To conduct a risk management study, we need to identify assets, threats, vulnerabilities, risks, and…
Q: The smallest logical units of the desired functionality of a system are called processes
A: Process in computer knowledge are instance of computer program that are being Executed by one or…
Q: In terms of price and functionality, what are the distinctions between primary and secondary…
A: Primary and secondary storage are two essential components of a computer system that play different…
Q: What three characteristics must a successful network possess? Spend a few moments describing it in…
A: A successful network is an essential component in today's interconnected world. It enables the…
Q: Was intent behind the LOCAL
A: Dear Student,No, the LOCAL directive was not created with intent. It was created as a way to declare…
Q: What information should be included in your abstract in order to construct your own system?
A: An abstract is a powerful and short summary which describes the focus of a research paper. This…
Q: Question 1 [ 5 . 2 1 5 2 Figure 1: Traffic Engineering with Open Flow Figure 1 reveals a network…
A: The question asks to describe the local flow table of each of the switches (U, V, W, X, Y, Z) in a…
Q: Assist a buddy with home networking. All home gadgets must be networked. List networking hardware.…
A: What is Topology: Topology refers to the arrangement or layout of devices and connections in a…
Q: What function do coding standards serve? Examine the Java programming language's coding standards.
A: What is coding standards: Coding standards are guidelines and best practices that developers should…
Q: Let's say you used in-order traversal to print the nodes of this tree. What nodes would be printed…
A: Dear Student,Inorder traversal is a type of depth-first traversal that visits the left-subtree, then…
Q: How does voting technology work? What effect does this have on computer networking?
A: Voting technology which refers to the devices and also with the processes that are used for casting…
Q: What are the three objectives of a functional network? How would you characterise one in a few…
A: A purposeful network, within the circumstance of computer knowledge, is a collection of…
Question M
.
Full explain this question and text typing work only
We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this line
Step by step
Solved in 4 steps

- PYTHON CODE: In order to beat AlphaZero, Grandmaster Hikaru is improving her chess calculation skills.Today, Hikaru took a big chessboard with N rows (numbered 1 through N) and N columns (numbered 1 through N). Let's denote the square in row r and column c of the chessboard by (r,c). Hikaru wants to place some rooks on the chessboard in such a way that the following conditions are satisfied:• Each square of the board contains at most one rook.• There are no four rooks forming a rectangle. Formally, there should not be any four valid integers r1, c1, r2, c2 (≠r2,c1≠c2) such that there are rooks on squares (r1,c1), (r1,c2 (r2,c1)and (r2,c2).• The number of rooks is at least 8N.Help Hikaru find a possible distribution of rooks. If there are multiple solutions, you may find any one. It is guaranteed that under the given constraints, a solution always exists.InputThe first line of the input contains a single integer T denoting the number of test cases. The first and only line of each test…Q4. Recursion Find how many possible combinations that a number can be decomposed into the multiple of integers (smaller than the number itself) by a recursion function.Suppose we have a positive number Y as input, and it need to be decomposed into the multiple of several integers, Yi, where each Yi, is smaller than Y(e.g., Y=Y1∗Y2∗ Y3∗...∗Yn). In addition, these decomposed integers can only be arranged in an ascending order (Y11. Write a recursive function that takes as a parameter a nonnegative integer and generates the following pattern of stars. If the nonnegative integer is 4, then the pattern generated is:********************Also, write a program that prompts the user to enter the number of lines in the pattern and uses the recursive function to generate the pattern. For example, specifying 4 as the number of lines generates the above pattern. 2. A palindrome is a string that reads the same both forward and backward. For example, the string "madam" is a palindrome. Write a program that uses a recursive function to check whether a string is a palindrome. Your program must contain a value-returning recursive function that returns true if the string is a palindrome and false otherwise. Do not use any global variables; use the appropriate parameter.
- Artificial Intelligence (Part - 2) ==================== The Towers of Hanoi is a famous problem for studying recursion incomputer science and searching in artificial intelligence. We start with N discs of varying sizes on a peg (stacked in order according to size), and two empty pegs. We are allowed to move a disc from one peg to another, but we are never allowed to move a larger disc on top of a smaller disc. The goal is to move all the discs to the rightmost peg (see figure). To solve the problem by using search methods, we need first formulate the problem. Supposing there are K pegs and N disk. (2) What is the size of the state space?Artificial Intelligence (Part - 1) ==================== The Towers of Hanoi is a famous problem for studying recursion in computer science and searching in artificial intelligence. We start with N discs of varying sizes on a peg (stacked in order according to size), and two empty pegs. We are allowed to move a disc from one peg to another, but we are never allowed to move a larger disc on top of a smaller disc. The goal is to move all the discs to the rightmost peg (see figure). To solve the problem by using search methods, we need first formulate the problem. Supposing there are K pegs and N disk. (1) Propose a state representation for the problem?Code in python: A certain company has encoded the accounts of its customers and requires that you provide an algorithm that, given an account code, informs if it is valid according to the following description: The account codes are made up of 4 digits counted from right to left, plus the verification digit. The verifying digit is obtained by adding the digits of the account number of the even positions and multiplying the digits of the odd positions, from the new result the residue of the division is extracted for 10, which represents the verifying digit. Develop the code in python as a check digit class that returns 1 if it is correct or 0 if not Heading: Extract digits, verifier calculation, Account verification, Integral algorithm
- Python code Here are n posts at particular directions on a plane. It is ensured that no three fence posts lie on a similar line. There are a limitless number of cows on the plane, one at each point with whole number directions. Gregor is an individual from the Illuminati, and needs to construct a three-sided fence, interfacing 3 unmistakable existing wall posts. A cow stringently inside the fence is supposed to be encased. In case there are an odd number of encased cows and the space of the fence is a whole number, the fence is supposed to be intriguing. Track down the quantity of intriguing wall. Information : The primary line contains the whole number n (3≤n≤6000), the quantity of fence posts which Gregor can decide to shape the vertices of a fence. Every one of the following n line contains two whole numbers x and y (0≤x,y≤107, x and y are even), where (x,y) is the arrange of a fence post. All fence posts lie at unmistakable directions. No three fence posts are on a similar…1. A set of integers are relatively prime to each other if there is no integer greater than 1 that divides all the elements. Furthermore, in Number Theory, it is known that the Euler function,ϕ (n), expresses the number of positive integers less than n that are relatively prime with n. Choose the alternative that has the correct value of ϕ(n) for every n below. A) ϕ(5) = 4 B) ϕ(6) = 2 C) ϕ(10) = 3 D) ϕ(14) = 6 E) ϕ(17) = 16python In order to beat AlphaZero, Grandmaster Hikaru is improving her chess calculation skills.Today, Hikaru took a big chessboard with N rows (numbered 1 through N) and N columns (numbered 1 through N). Let's denote the square in row r and column c of the chessboard by (r,c). Hikaru wants to place some rooks on the chessboard in such a way that the following conditions are satisfied:• Each square of the board contains at most one rook.• There are no four rooks forming a rectangle. Formally, there should not be any four valid integers r1, c1, r2, c2 (≠r2,c1≠c2) such that there are rooks on squares (r1,c1), (r1,c2 (r2,c1)and (r2,c2).• The number of rooks is at least 8N.Help Hikaru find a possible distribution of rooks. If there are multiple solutions, you may find any one. It is guaranteed that under the given constraints, a solution always exists.InputThe first line of the input contains a single integer T denoting the number of test cases. The first and only line of each test case…
- In c++ please with clear indentation thank you so much Write the simplest program that will demonstrate iteration vs recursion using the following guidelines - Write two primary helper functions - one iterative (IsArrayPrimeIter) and one recursive (IsArrayPrimeRecur) - each of which Takes an array of integers and its size as input params and returns a bool such that 'true' ==> all elements of the array are prime, so the array is prime, 'false' ==> at least one element in array is not prime, so array is not prime. Print out a message "Entering <function_name>" as the first executed statement of each function. Perform the code to test whether every element of the array is a Prime number. Print out a message "Leaving <function_name>" as the last executed statement before returning from the function. Remember - there will be nested loops for the iterative function and there can be no loops at all in the recursive function. For the recursive function - define one…12.10 LAB: All permutations of names- Java Write a program that lists all ways people can line up for a photo (all permutations of a list of Strings). The program will read a list of one word names (until -1), and use a recursive method to create and output all possible orderings of those names, one ordering per line. When the input is: Julia Lucas Mia -1 then the output is (must match the below ordering): Julia Lucas Mia Julia Mia Lucas Lucas Julia Mia Lucas Mia Julia Mia Julia Lucas Mia Lucas JuliaCompilation Techniques a. Translate the three-address statement, the following expression: n = f((x+2), y) – 5; b. If A is an array of integers with width = 4; Translate with a three-address statement, the following expression: x = a[i] + 2

