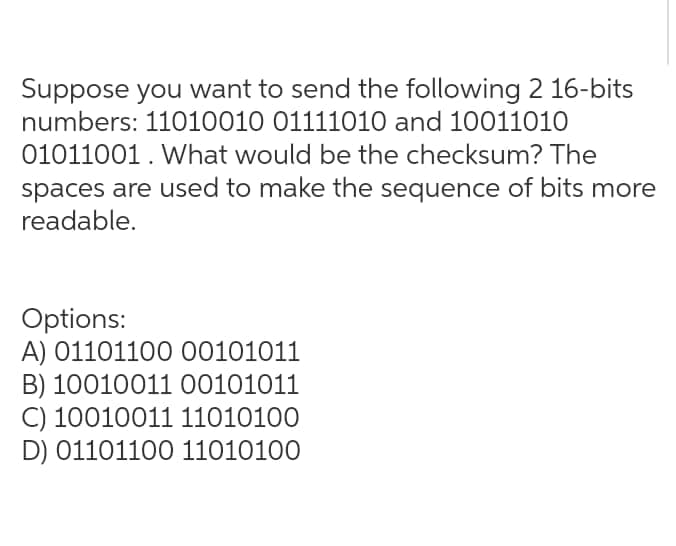
Suppose you want to send the following 2 16-bits numbers: 11010010 01111010 and 10011010 01011001. What would be the checksum? The spaces are used to make the sequence of bits more readable. Options: A) 01101100 00101011 B) 10010011 00101011 C) 10010011 11010100 D) 01101100 11010100
Q: What does MVC do in the way web applications are put together? In what ways is an MVC architecture…
A: Definition: Model-View-Controller (MVC) is an architectural pattern that divides an application into…
Q: Pervasive computing, often known as ubiquitous computing, varies significantly from conventional…
A: Ubiquitous Computing: The term "ubiquitous computing" does not refer to a particular technology, but…
Q: What steps may be taken to avoid man-in-the-middle (MITM) attacks? Answer the question step-by-step.
A: A man-in-the-middle attack is a type of eavesdropping attack: Every workplace application, including…
Q: Describe briefly how you propose to examine this DDoS assault using security engineering techniques
A: Answer :
Q: how flashbulb memories vary from other forms of memories in terms of their size and scope.
A: Flashbulb memories : Provide an example of each main kind of memory flashbulb memory and explain how…
Q: Start with an empty buffer pool of size 4 pages again. This time use this access pattern:…
A: Access Pattern given here is :S A G L I K L I M U T L U B A Y R A M L A RBuffer Size = 4 pages…
Q: In concurrent programming, what is the impact of the interaction of processes?
A: Concurrent Programming: The term "concurrent programming" refers to the practice of running many…
Q: What are some of the most common software-related problems that people encounter?
A: Software-Related Problems: Inaccurate data alterations, faults in out-of-date installed…
Q: 1. There can be any number of else..if statement in a if else..if block. 2. The if…else if statement…
A: Answer the following question. TRUE OR FALSE. 1. There can be any number of else..if statement in a…
Q: A system clocked at 1 GHz wants to read data from a hard disk. The hard disk needs some time to read…
A: After three polls To handle an interrupt and subsequently read data from the hard disk on a 1 GHz…
Q: world
A: Introduction of routing.
Q: Implementation with Results(Using Prolog) (Magic Square Problem)
A: The magic square is a square matrix, whose order is odd and where the sum of the elements for each…
Q: What are the most often used protocols for routing data? What factors are taken into account by…
A: Protocols for routing data: Exterior routing protocols are used to exchange routes across networks…
Q: Given the following characteristics for a magnetic tape using linear recording described in device…
A: Magnetic tape: It is a physical storage device used to store different kinds of data. It is…
Q: How fast can one complete the median? What is the recurrence relation that the algorithm follows?…
A: Solution: Recurrence relation: Let the problem be: finding the Kth largest element in an…
Q: What computer science ethical concerns should a researcher keep in mind while gathering data?
A: Data gathering: Research questions are answered, hypotheses tested, and results are evaluated via…
Q: Changing a database's setup necessitates the DEMS to update its catalog. Changing the catalog by…
A: The database information is stored in the System Catalog.
Q: Describe how a firewall resembles a data stream that has been divided into packets.
A: Introduction: Here we are required to explain how a firewall resembles a data stream that has been…
Q: Your firm has decided to shut a number of locations in order to save money and lessen the…
A: Given: Your firm plans to eliminate a few locations and give assistance for employees who want to…
Q: Assume that a computer system is having 4-page frames for holding process pages in the main memory.…
A: In FIFO algorithm, frame which has been occupied first will be first choosen for replacement. In…
Q: Are there any positive or negative effects of cloud computing on collaboration?
A: Essentially, the cloud computing movement refers to how any digital company's operations are…
Q: Consider the following table and tell which of the following syntax is correct for cell 1?
A: In the following table
Q: What exactly is congestion management in a computer network, and why is it necessary? Separate…
A: To comprehend congestion control, it is necessary to first comprehend what congestion is. Congestion…
Q: H.W. Design the interface circuit that make the interface between 8 switch and control 8 LED where…
A:
Q: The value of fxe dx by the using one-segment trapezoidal rule is most nearly 02 (A) 11.672 (B)…
A: solution in below step
Q: orrect the following code so that it correctly sets the value of each element of myList to the index…
A: ANSWER:-
Q: What are the procedures that must be taken to ensure that the data is accurate?
A: Data Accurate: One of the components of data quality is data accuracy. It refers to the accuracy of…
Q: The OSI layer, its functions, and the protocols that operate at each layer will be discussed in this…
A: In Computer networks OSI layer stands for Open System Inerconnection. It is a architecture…
Q: Is it better to use a static or dynamic route for a network? Is one better than the other?
A: Static routing is a form of routing that occurs when a router uses a manually-configured routing…
Q: A computer's output that is saved on optical media rather than paper or microfiche is known as what…
A: In this example, a computer output that is written directly to optical storage rather than paper or…
Q: The next sections go into great detail on network applications and application layer protocols.
A: Network applications include: As network functions become more virtualized and network control…
Q: In terms of data security, what are some risks? After that, we'll talk about how to avoid such…
A: A cyber or cybersecurity threat is an attempt to hurt, steal, or disrupt digital life. Cyber…
Q: Face-to-face communication varies from computer-mediated communication in many ways. Disseminate…
A: Using computers as a medium for communication is called computer-mediated communication (CMC).…
Q: Instruction: Create a java program that generates elements (randomly from 10 – 75) of a…
A: Logic :- (I) To generate random number in range:- arr[i][j]= Min + (int)(Math.random() * ((Max -…
Q: Task Assigned: Write a program to read input two strings sp_top, sp_bottom from the user and print…
A:
Q: It's important to know precisely what routing entails and how it works. Examine and contrast two…
A: Given: The next stage is to solve the problem of defining routing and routing techniques.
Q: Cloud computing's influence on cooperation is unclear, to say the least.
A: CLOUD COMPUTING REVOLUTION: The cloud computing revolution is essentially the transition of all…
Q: In what ways does static routing vary from that of dynamic routing? Which dynamic routing method is…
A: Static Routing Dynamic Routing…
Q: When an organisation is trying to keep its data safe, what is the goal? What are the benefits of…
A: Answer:
Q: What is congestion control in a computer network? The network may assist in congesting the system,…
A: Congestion Management: To understand congestion management, you must first understand what…
Q: Give a brief history of wireless LAN protocol development.
A: Evaluation of network protocols: - Since the introduction of IEEE 802.11, a slew of new IEEE…
Q: Create a class circle class with radius as data member. Create two constructors (no argument, and…
A: Class A class is user define interface which act as blueprint for creating objects and instances…
Q: Describe how TCP connects, how it controls its flow, and how it handles congestion
A: Lets see how TCP connects and establishes connection:---> Establishing a TCP Connection:--->…
Q: Explain how a semaphore is implemented in the ADA programming language. Is it possible for a job in…
A:
Q: 2. Using an iflelse construct, write a program that will calculate a person's pay based on the…
A: Find the required code in C++ given as below and output : As per company guidelines we are supposed…
Q: What may possibly cause a return to the currently executed instruction in the event of a fault?
A: The program which is to be executed is a set of instructions: Page fault is a phrase that refers to…
Q: To begin, let's take a closer look at routing. Identify the differences between two popular routing…
A: Explanation: What exactly is routing and how does it work? Routing is the ability to send IP…
Q: g) The smallest unit of binary data is the 1. bit. 2. byte. 3. word. h) Which of the following best…
A: Answer:
Q: Provide me with the MATLAB code to swap the first and last row of the matrix given below, mat = 1111…
A: Provide me with the MATLAB code to swap the first and last row of the matrix given below, mat = 1 1…
Q: So, what's the big deal with data encryption anyway?
A: Data encryption: The process of converting plaintext data into ciphertext is known as data…
Step by step
Solved in 3 steps with 3 images

- Here is a permutation: location in new byte 1 2 3 4 5 6 7 8 location in source byte 1 3 5 4 2 8 6 7 The source is a byte (8 bits) and the result is a byte (8 bits). Bit numbering starts at one, on the left. If the source byte is 1011 1000 what is the new byte? (Write the answer as 8 characters 0 or 1 with a space in the middle.)You have two 32-bit numbers, N and M, as well as two bit positions, I and j. Create a method for inserting Minto N in such a way that M begins at bit j and ends at bit i. You can assume that bits j through I have enough space to accommodate all of M. That is, if M = 10011, you can presume at least 5 bits exist between j and i. You wouldn't have j = 3 and I = 2, for example, because M couldn't completely fit between bit 3 and bit 2.Input: N=10000000000, M=10011,i=2,j=6Output: N=10001001100Suppose you have a 4-letter alphabet {A, B, C, D} and you wish to devise a binary code (with nospaces) for this alphabet such that no two words would be encoded the same. For example, if A = 1and B = 11, then AA and B would be encoded the same. It takes one second to transmit eachcharacter of the binary code (so, 101 would take 3 seconds and 110101 would take 6 seconds).(a) If each letter occurs with the same frequency, determine the most efficient code for the alphabetand explain why it is the most efficient.(b) Now suppose letter A occurs about 40% of the time, B and C both occur about 25% of thetime each, and C occurs about 10% of the time. Determine the most efficient code and explainwhy it is the most efficient.
- Write a program that reads any file of text and prints the bit values corresponding to each bit in each character. Access the individual bit values using bit shifting and/or masking. For example: a b c 0 1 2 Output should look like: a => 00011101 (97) b => 00011102 (98) ... Please use the C program language with screenshots.“Hamming,” will read in an integer “k” and a bit string “s” from the command line, calculate the “Hamming Distances,” and prints all bit strings that have Hamming distance of “k” from “s.” Note: The Hamming Distance is equal to the number of bits in which the two strings differ. A sample run would be as follows. >java Hamming 2 00111111 1001 1010 0101 0110 0000Assume that D has the value 1010101010 and that the 5-bit generator G=10011 is used. What does R stand for? B. C. Does corruption exist? Publish your work. Repetition of parts a and b with the addition of the following: the numbers 1001010101, 0101101010, and 1010100000
- You receive the following data fragment: 0110 0111 1100 1111 0111 1101. You know that the protocol uses bit stuffing. Show the data after destuffingWrite a program to set in 8060 (bit 7) and clear (bit 0) of a byte wide number stored in address 0200-2460H, Save the modified bytes in address 0200-2700HUse DATA: 6FH, 3DH, 27H, 83H, DEH, 13H, 78H, 09H, F5H, 03H, 84H,7EH, 0BH, 87H, FEH, 11HYou are given two bit locations, I and j, together with the 32-bit values N and M. To insert Minto N, create a method that starts M at bit j and finishes it at bit i. It is safe to presume that all of M can fit in the bits j through i. Therefore, you may infer that there are at least 5 bits between j and I if M = 10011. M could not completely fit between bit 3 and bit 2, thus you would not, for instance, have j = 3 and I = 2.EXAMPLE Key in: NN 10000000000, M 10001001100 as output
- Write a program to transfer 8-bit numbers from 9080H to 9090H if D5 is 1 and D3 is 0. otherwise transfer data by changing bit D2 and D6 from 1 to 0 and 0 to 1. Assume there are ten numbers.How many 88-bit binary strings are there subject to each of the following restrictions? 1. The string starts with 001001. 2. The string starts with 001001 or 1010. 3. The string has exactly 4 zero’s. 4. The string has exactly 4 zeros’s and the first bit is 1.Compute CBC-MAC for a message of 16 bits, “ABCD” (in Hexa). Assume a block size of 8 bits with an IV=C9 (in hexa). For simplicity, assume the encryption to be a simple XOR of the key with the plaintext. Let the encryption key be D8 (in Hexa). (Hint: Divide the message into blocks of 8 bits each; XOR each block with the previous cipher output; then encrypt this with the key. For the first block, XOR it with IV.

