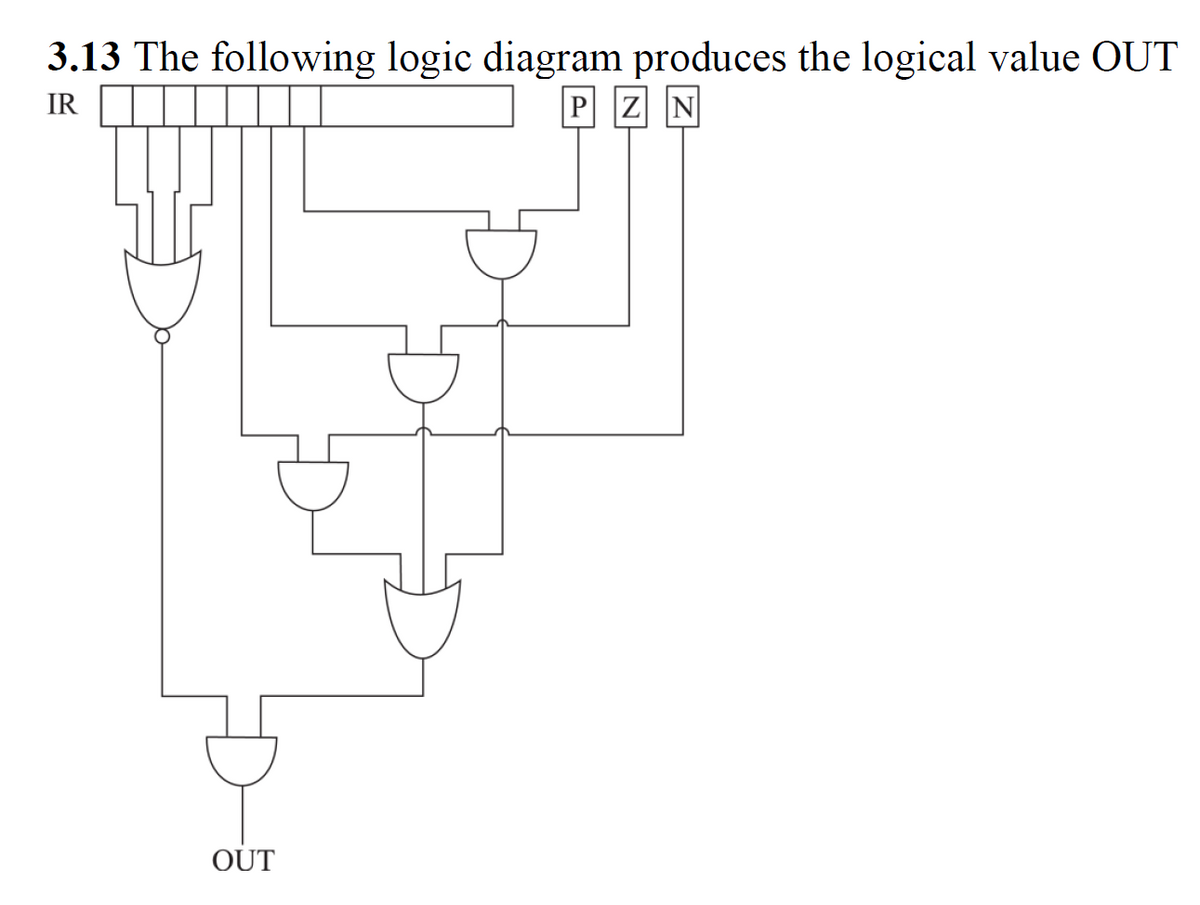
The following logic diagram produces the logical value OUT
Q: What are the many types of firewalls available and how are they used?
A: Introduction: This question will enlighten you on the various types of firewalls available,…
Q: What function does a firewall play in the design and deployment of a network?
A: Introduction: Firewalls are devices that regulate the flow of data between networks. Computers and…
Q: What instruction format is this? (one letter) Write out the full instruction in MIPS assembly…
A: What instruction format is this? (one letter) --> There are three instruction categories:…
Q: How are logical and linear addresses different, and how do they connect to one another?
A: Introduction Linear address: The linear address space means everything addresses that can be shaped…
Q: You may refer to them as application-layer messages. Is this a transport layer component? What is a…
A: Introduction: In the OSI model, the network layer is the layer that provides the host with the…
Q: What are the benefits of a file system-based website over an HTTP-based website?
A: HTTP website: The answer is that it is debatable. HTTP is fine if you're simply perusing the web,…
Q: We'll demonstrate how to construct a botnet and how to use it in a DDoS attack in this post.
A: Introduction: The following points may be used in the construction of a botnet:
Q: Computer science Explain the difference between connectionless and connection-oriented services.
A: Introduction: Because of corporate policy, we can only respond to one question at a time, so please…
Q: Which storage medium is the most suitable for users' data backups? Your solution should be…
A: It refers to the digital recording of files and documents and their subsequent storage in a storage…
Q: What causes the time interval between bytes in asynchronous transmission to vary?
A: Answer is given below -
Q: What is the proper term for a single person who is in charge of organizing a distributed denial of…
A: Intro If a single individual is in charge of organizing a distributed denial-of-service assault,…
Q: Where can I learn more about the protocols supported by SSL? How are SSL and SSH different from one…
A: Introduction: SSL (Transport Layer Security) support for HTTPS. TLS is a network protocol that uses…
Q: How does assembly language interact with machine language?
A: The solution to the given question is: Assembly language is low-level computer programming: Assembly…
Q: What precisely is an Internet protocol (IP) address? What is the purpose of mnemonic addresses? Is…
A: To discuss about IP addresses and mnemonic addresses. To determine the number of unique domains that…
Q: Consider two-dimensional vector data in which no data components overlap. Is it feasible to convert…
A: Introduction: Yes, it is possible to convert this sort of vector data into raster data in certain…
Q: tecture fro
A: The significant distinction between the two architectures is that in a Von Neumann architecture all…
Q: So, what exactly is a DNS forwarder?
A: Intro In Domain Name System (DNS), a DNS relay is a DNS server used to transfer DNS queries for…
Q: Explain how a file management system can give many users access to files for the purpose of changing…
A: GIVEN: Explain how a file management system can give many users access to files for the purpose of…
Q: What is the primary difference between mainframe and laptop operating systems? What do they have in…
A: Introduction: In order to differentiate between the operating systems of mainframe computers and…
Q: How Does Networked Communication Benefit You?
A: Intro Essentially, it lets linked devices interact with one other, independent of any variations in…
Q: Is maintaining net neutrality necessary? Appropriately justify your response.?
A: Introduction Net Neutrality is a theory that argues that Online service providers should give and…
Q: Data cells will represent the degrees of activities for the decisions being made when developing a…
A: There is one statement given as follows: When formulating a linear programming problem on a…
Q: Solve the problem in C++ (Geometry: find the bounding rectangle) A bounding rectangle is the…
A: The complete is given below in C++ Programming Language:
Q: How am I to determine what a MAC file is?
A: Macintosh File System: Apple Computer established the Macintosh File System (MFS) as a volume format…
Q: What five (5) traits would you use to characterize a system?
A: Characterize a system: The way a system reacts to incoming signals defines it. A system contains…
Q: What use does a firewall serve in network design?
A: Firewalls regulate the flow of information between networks: Computers and servers dedicated to this…
Q: Projectile Motion Write a program to provide information on the height of a ball thrown straight up…
A: Python Code:- ##This is getInput() function, def getInput(): ##First ask user to enter the…
Q: t–server a
A: The application logic may be covered in the server data set, on the client (inside the UI), or both…
Q: What are the distinctions between the network edge, core, access, and physical media, and how are…
A: Network edge and core: Endpoints are referred to as the network edge. It's the initial link…
Q: s and phys
A: An data-flow diagram is an approach to addressing a progression of information through an…
Q: How is a hash value safeguarded for message authentication? Can a MAC algorithm be exploited without…
A: Another kind of security is message authentication. The message authentication data security feature…
Q: Write the statement in words if: p: Firemen work hard. q: Firemen wear red suspenders. 1) ~q 2) p…
A: Tilde sign is used for negation which represents negation of a sentence. ∧ logic combines two or…
Q: ween mainframe operating systems and laptop operating systems? What are some of these two people's…
A: Among the qualifications between PCs and mainframes computers is a mainframes computer working…
Q: How many Matlab seat licenses are required for there to be a ~1% steady state probability
A: The answer is
Q: How is an arithmetic shift distinguished from a logical shift? Explanation with examples
A: Please find the answer below :
Q: oes the time gap
A: Below why does the time gap between bytes fluctuate
Q: There are two VPN protocols listed. Describe the tunneling method used to create Virtual Private…
A: A VPN protocol is a collection of instructions or rules that govern data transfer between your…
Q: In a nutshell, define technology diffusion in computer science.
A: To be determine: Define technology diffusion in short.
Q: 2. With all the proper steps, show that the following grammar is CLR(1) but not LALK(1). What are…
A: Given, S→ Ac / bAa / Ba / bBcA→dB→d
Q: Peering is a typical practice between two ISPs at the same hierarchy level. How does an IXP generate…
A: Intro Internet Service Provider (ISP): An internet service provider is a technique that includes…
Q: Is it possible for the server to determine if the user is attempting to surf the web or send a…
A: Please find the answer below :
Q: How are sequential and combinatorial logic distinct
A: Please find the answer below :
Q: 2. During the summer months, a rental agency keeps track of the number of speedboats rented each day…
A: I am giving handwritten explanation. See below steps.
Q: Hexadecimal's function is unknown. The hexadecimal system is quite versatile.
A: Hexadecimal point: The base-16 number system is referred to as hexadecimal numerals. The hexadecimal…
Q: What use does assembly language serve?
A: Assembly language is an intermediary language. It use numbers, symbols, and abbreviations instead of…
Q: How quickly can data move over an Ethernet local area network?
A: Introduction: Ethernet is a networking technology that is widely used in wired Local Area Networks…
Q: Write aprogram to calculate the average value of three numbers,then if average value more than 100…
A: Given: Write a program to calculate the average value of three numbers, then if average value more…
Q: More than 90% of the microprocessors/micro- controllers manufactured is used in
A: The answer is
Q: 4. Determine whether each distribution is a probability distribution
A: Rule for checking weather a given distribution is probability distribution or NOT. 1) Each…
Q: What is a computer system? Explain its components.
A: Introduction What is a computer system? Explain its components.
Trending now
This is a popular solution!
Step by step
Solved in 4 steps with 3 images

- Implement the following Boolean expressions as they are stated: (a) X = ABC + AB + AC (b) X = AB(C + DE)2) Simplify the following Boolean expressions, using three-variable K-maps:F(x,y,z) = x′y′ + yz + x′yz′ PS:Please type instead of paper writingState (in words) the negation of the following statements.1. (∃x ∈ Z)P(x) ∧ (∀y ∈ R)(¬Q(y)).
- Consider the following precondition and assignment statement: {x>=4} < x = x - 4; >. Show whether the above statement interferes with the triple: {x >= 0} < x = x + 5; > {x >= 5}.C++ : solve the following question in the picture.Write the robot program using the VAL+ for the following automation case. First draw the problem; then handwrite the VAL+ code. The robot picks up FIVE blocks of size 100x100x100 mm that are stacked at a fixed position and place them at the corners and center of a square table of size 500 x 500 mm. Select the original position on the table on your own.
- f : {1, 2, 3} ® {a, b, c, d} f(1) = c f(2) = b f(3) = a g : {a, b, c, d} ® {x, y, z} g(a) = y g(b) = x g(c) = x g(d) = z Find the composition gofDetermine the truth value of each of the following statements. We assume that the domain for all variables consists of all integers. 1. n m (n2< m)2. n m (n < m2)3. n m (n + m = 0)4. n m (nm = m)5. n m (n2+ m2= 5)6. n m (n2+ m2= 6)7. n m (n + m = 4 n – m =1)8. n m (n + m = 4 n – m =2)9. n m p (p = (m + n)/2)2. Simplify the following Boolean expressions, using three variable K-maps: (a) F(x,y,z) = xy+x′y′z′+x′yz′ (b) F(x,y,z) = x′y′+yz+x′yz′ (c) F(x,y,z) = x′y+yz′+y′z′
- Write an outline and logic for the following code: EMPTY = '-' BLACK = ‘X’ WHITE = ‘O’ BOARD_SIZE = 8 DIRECTIONS = [(0, 1), (0, -1), (1, 0), (-1, 0), (1, 1), (-1, -1), (1, -1), (-1, 1)] def initialize_board(): board = [[EMPTY for _ in range(BOARD_SIZE)] for _ in range(BOARD_SIZE)] board[3][3] = WHITE board[3][4] = BLACK board[4][3] = BLACK board[4][4] = WHITE return board def print_board(board): print(" 1 2 3 4 5 6 7 8") for i in range(BOARD_SIZE): print(f"{i + 1} ", end="") for j in range(BOARD_SIZE): print(f" {board[i][j]}", end="") print() def is_valid_move(board, row, col, player): if board[row][col] != EMPTY: return False for direction in DIRECTIONS: dr, dc = direction r, c = row + dr, col + dc while 0 <= r < BOARD_SIZE and 0 <= c < BOARD_SIZE: if board[r][c] == EMPTY: break if board[r][c] == player:…Given a, b, c, show the following assertion: if a | b and a | c then a | b + c and a| b –cComputer Science Given the following declaration and assignment: declare X X=midtermexam(mcq:[d b c a b] q1:[a [b [c]]] q2:q3(q4 q5 [a b [e c]])) How much is X.q1.2.1.2? What are the expressions related to X that will display e, q3, and 3? Programm in OZ

