The radioisotope ¹4C (half life = 5730 years) is used for carbon dating. What is the first order rate constant for ¹4C?
Q: Do you believe that there are risks involved with the use of cloud computing in financial systems,…
A: Yes, there are certainly risks involved with the use of cloud computing in financial systems,…
Q: Why is it required to use a modem to connect a phone line to a communication adapter?
A: Introduction: There are just two components to a modem: an amplifier, a demodulatorIt converts…
Q: contrasting two transmission methods (twistted piars, coxial cable, microwave, satalitte, fibre…
A: Transmission Media: The repeater is the series circuit connecting the transmitter and the receiver…
Q: Why does it seem like my disk is thrashing? What actions may you take to mitigate the consequences…
A: When a hard drive is busy moving data back and forth between memory and the disc in rapid…
Q: round on the evolution of co
A: Introduction: The foremost people employed the first counting system. They counted with sticks,…
Q: What would occur if there were no programs that could be relocated? This could make memory paging…
A: In this question we have to understand what would occur if there were no programs that could be…
Q: Which of the following does Ubuntu utilize to get an IP address? In order to understand what you are…
A: Ubuntu Server IP Address Utilizing netplan is necessary in order to configure an IP address on an…
Q: f this Term.h I need .cpp file of this header file please help me Please make sure they compiles…
A: #include <iostream>#include <string>#include "Date.h" using namespace std; class Term…
Q: Further details on the criteria used to rate the product's quality as well procedure would be of…
A: A software metric is a characteristic of a program that can be measured or counted.Program metrics…
Q: Maintain a clear distinction between research methods and research methodology, and be sure to…
A: Research methods refer to the specific techniques or procedures used to collect and analyze data in…
Q: Installing Windows 8 on a gaming PC that does not have dedicated video hardware and does have a free…
A: 32-bit PCI video cards. Most PCI slots on motherboards are 32-bit, 5-volt. Most 5 volt PCI video…
Q: What is the multifactor identification procedure? What security precautions does it take to guard…
A: Multi factor identification procedure also known as multi-factor Authentication (MFA), is an…
Q: Some experts in the field of information technology believe that businesses should employ ex-hackers…
A: The answer is given below step.
Q: Determine the kind of wire you have and how it varies from other types of wires.
A: Twisted-pair cable, coaxial cable, fiber-optic cable, and wireless communication are discussed and…
Q: If all the capacities in the given network are integers, prove that the algorithm always returns a…
A: 1. Programming is the process of creating a set of instructions that tells a computer how to perform…
Q: Let's start by looking into routing in more detail. The aim of this exercise is to help you tell the…
A: How does routing function, and what is it? The ability to send Internet Protocol (IP) packets from…
Q: Discrete event simulation is necessary due to four considerations
A: Introduction: Simulation modelling securely resolves issues in the real world. It provides an…
Q: Consider the significance of wireless network technology in today's developing countries. Wireless…
A: 1. A computer network refers to interconnected computing devices that can exchange data and share…
Q: ou manager has asked you to write a report to a customer who will be using digital circuits that…
A: JK Flipflop is a sequential circuit in which the current output is depends on the previous output…
Q: Which has larger memory addresses, virtual or physical? Why?
A: A computer is a digital electronic machine that can be programmed to automatically perform a series…
Q: C++ Need help with the functions While testing I am not getting the count for the vowles and…
A: Please refer to the following steps for the complete solution to the problem above.
Q: How do you think technology and social media affect your social skills and the skills of your peers?…
A: It is widely accepted that technology and social media can have both positive and negative impacts…
Q: Write the state of the elements of the vector below after each of the first 3 passes of the…
A: 1) Selection sort is a simple and efficient sorting algorithm that works by repeatedly selecting the…
Q: How it functions makes a distinction between local and remote user authentication. Which of the…
A: Authentication of remote users: It is a process through which a distant server confirms a user's…
Q: In what four different ways is discrete event simulation capable of being depicted as critical?
A: Each associated event in the process occurs at a certain moment. The event's occurrence is what…
Q: When referring to subprograms, variables, and other objects in code, which is better to use: fully…
A: Introduction: It is necessary for him to initiate communication with another officer in the sales…
Q: You manager has asked you to write a report to a customer who will be using digital circuits that…
A: Introduction: Sequential logic devices are digital circuits that use a clock signal to store the…
Q: In your opinion, which facet of the software engineering profession is the most important, and why?
A: Introduction: The question concerns severe challenges in the subject of software engineering, and…
Q: There are two major advantages of electronic mail over conventional mail for modern communication.…
A: Email isn't just for text messages. Any type of multimedia can be sent within mail, also helps in…
Q: .Write the definition of classes and interfaces in the diagram below using following details: a)…
A: The JAVA codes for all the classes and interfaces ae given in the below step
Q: In your own words, what precisely is the problem with NRZ? The more pressing question is, how can it…
A: According to the information given:- We have to define problem with NRZ and the more pressing…
Q: Think about wireless networks in underdeveloped countries. Wireless has taken the place of LANs and…
A: Introduction: Mobile users can get real-time data from a wireless network while moving around your…
Q: Given the following statements: s1 = 'Computational Thinking' s2= "Python Rocks!" Show the result of…
A: Note: The answer of the first three subparts are given in this solution. Kindly repoost the…
Q: Define the sets A, B, C, D, and E as follows: • A = {x € R: x 2} • C = {x € R: |x| <2} E • D = {x €…
A: Given, A=x∈R:x<-2 A is the set of all real numbers x such that x is less than -2. In interval…
Q: The importance of linguistic skills for a systems analyst and why they must be met. Which groups may…
A: Technical knowledge must be translated by a systems analyst: into English that non-technical people…
Q: Does associative memory vary from regular memory? Which choice is more expensive, and why is it more…
A: Associative memory and regular memory are two different types of computer memory that serve…
Q: To what do we refer when we say "operating system?" To what do the operating system's two main…
A: An operating system (OS) is a collection of software that manages and controls the hardware and…
Q: Identify the three instances of discrete event simulation from the list below.
A: The answer is given below step.
Q: Just presume that there isn't any relocatable software code. How may the memory paging procedure be…
A: Introduction: Software that can have its execution address changed is referred to as relocatable…
Q: Give an example of how the CPU of a computer could affect the performance as a whole.
A: Introduction: The CPU is constantly obeying computer programme instructions that tell it which data…
Q: Prove the following asymptotic bounds. 1 + 2 + ··· +n ∈ Ω(n2
A: The formula for the sum of the first n positive integers is n(n+1)/2. We can use this formula to…
Q: What checks can you do to ensure that each network device has a different MAC address? How about…
A: Each device on a different local network should have the same Media Access Control (MAC) address. If…
Q: Think about the impact that wireless networks may have in nations that are still developing. Why are…
A: Today we have wifi capability in almost every smartphone. So wireless networking is becoming more…
Q: For instance, if you are starting a media firm and want to hire graphic designers and media…
A: Employee recruitment is an essential part of any business, and it is especially important when…
Q: What would you do if two devices on your local area network had the same media access control (MAC)…
A: MAC stands for Media Access Control, which is a unique identifier assigned to a network interface…
Q: EXPERIMENT: Watching the Image Loader using e global flags to enable a debugging feature Write all…
A: The experiment is about modifying the source code for Image Loader software to enable a debugging…
Q: In your opinion, what is the most important function of an OS?
A: An operating system is the most important software that runs on a computer. It manages the…
Q: ow it functions makes a distinction between local and remote user authentication. Which of the…
A: It is difficult to determine which method presents the most security risk without additional…
Q: What precisely are these things called triggers? Which function are they meant to serve? How can the…
A: Triggers are SQL procedures that execute automatically when certain commands, including INSERT,…
Q: Which of the three below employs "definite event simulation?"
A: Discrete event simulation (DES) is a technique used to represent real-world systems that may be…
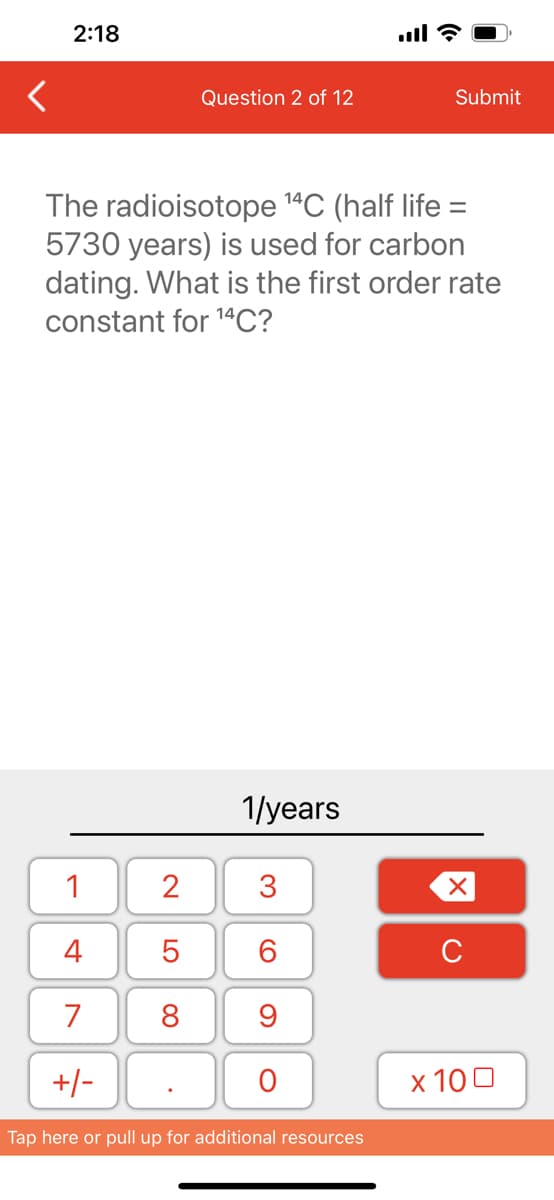
The half-life of a radioactive isotope is directly related to its first-order rate constant, k. The half-life, t1/2, is given by the equation:
t1/2 = (ln 2) / k
Step by step
Solved in 2 steps

- Applying the banker’s algorithm, which of the following would be a possible order of completion for the following state? Available = (4, 4, 1, 1) Allocation Max ABCD ABCD T0 1202 4316 T1 0112 2424 T2 1240 3651 T3 1201 2623 T4 1001 3112f(n) = n3 - (n2 log2 n) + 2n f(n) ∈ O(n3) by giving the constants (c, n0) and arguing that your constants hold as n goes to infinity by either "chaining up", "chaining down", carefully treating the inequality as an equality and doing some algebra, or even weak induction. Also, what is the minimum value for c (in the definition of O() ) forj this problem and is it an exclusive or inclusive minimum/bound.7) Find the esuts nsteps 8 << 98812 0 13 g ) By sing FORloopsand F crestamattx D, O=| 3 1 3 3 8 =1 PO ... A
- A zero memory source has a source alphabet S = {s1, s2, s3}, with P = {1/4, 1/8, 5/8}. Find the entropy of the source H (S). Find the entropy of the second H (S2) extension and verify; then Find H(S4) and H(S11)?Correct answer will upvoted else downvoted. segment of place where there is length n there are k climate control systems: the I-th climate control system is set in cell artificial intelligence (1≤ai≤n). At least two climate control systems can't be put in a similar cell (for example all man-made intelligence are particular). Each climate control system is characterized by one boundary: temperature. The I-th climate control system is set to the temperature ti. Illustration of portion of length n=6, where k=2, a=[2,5] and t=[14,16]. For every cell I (1≤i≤n) discover it's temperature, that can be determined by the equation min1≤j≤k(tj+|aj−i|), where |aj−i| means outright worth of the distinction aj−i. As such, the temperature in cell I is equivalent to the base among the temperatures of forced air systems, expanded by the separation from it to the cell I. How about we take a gander at a model. Consider that n=6,k=2, the main forced air system is put in cell a1=2 and…Q1 The periodic function sin(2x) has multiple roots between x values of -5π and 5π. If xL = -15 and xU = 15, which of the following statements is true using a bracketed method? Select one: a. All roots will be returned b. The middle root will be returned c. The chosen bracket is invalid for bracketed methods d. A single root will be returned e. The algorithm will be stuck in an infinite loop Q2 Consider x and y to represent data points (xi,yi), where i = 1, 2, 3, … n. What is the length of pafter running the following command? p = polyval(x,y) Select one: a. n b. n - 1 c. n + 1 d. Empty variable e. 1 Q3 Consider a system of linear equations in the form of AX = B, where X is the unknown vector. Which of the following can be used to solve for X? Select one: a. X = A\B b. X = B./A c. X = inv(B)*A d. X = inv(A)./B e. X = B\A
- Alice and Bob want to use Diffie-Hellman Key Establishment to share a key and they have agreed to use the prime number p=97 as their modulus. They have to choose their g from the following list of numbers, none which are unfortunately primitive roots: 6, 9, 18Sort these numbers in the order of suitability, putting the most suitable on the left. Select one: a. 18, 6, 9 b. 9, 18, 6 c. 18, 9, 6 d. 6, 18, 9 e. 9, 6, 18Please help me make a Truth Table on this F = A'B'C' + A'BC + AB'C + ABC' + ABC please make like this in my example attached photo.For each part, describe whether the following information is easier to remember or difficult to remember, give a proper justification? Similarly, for each part show whether this information is in correct format and also give proper justification that how the following information can increase short term memory? ANY OUC HUNKT HESEL ETTE RSIN TOWO RDSO NLY C Issabrinagoingtogetanewiosphone 1962001199503221879219402010











