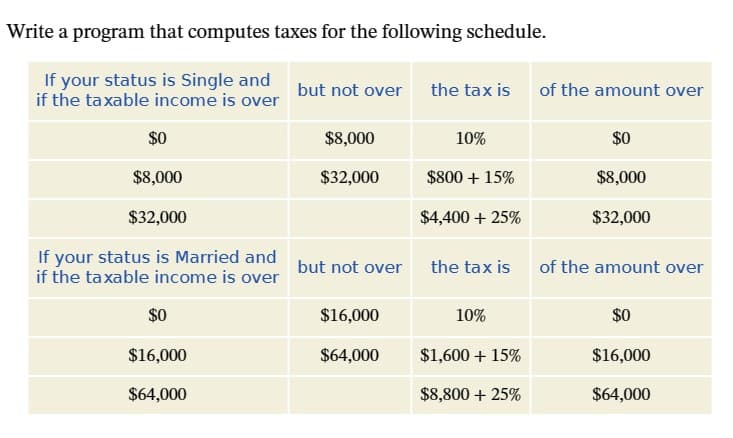
Write a program that computes taxes for the following schedule.
Q: This was mostly correct but there's an issue. The passwords underlined in red is supposed to be one…
A: The given code is reading file data space by space, not line by line. That's why we are getting Bad…
Q: html> Task 04
A: Let's create a .css file that will display the required elements in the given fashion.
Q: Please explain the concept of complexity in C++.
A: An algorithm's complexity is determined by how much time and/or space it takes to process an input…
Q: Neatly, design a DFA with the fewest possible number of states that accepts the language (ba +…
A: Here's a design for a DFA that recognizes the language L = {(ba + bab)*}: The start state is q0.…
Q: 8) Construct an equivalent DFA to the NFA below, using the method seeing in class. 90 a, λ 91 8 a b…
A: Given NFA: Set of states= {q0, q1, q2, q3} Initial state= q0 Final state= q1, q3 Set of input…
Q: If authentication was used, were we able to make any headway in accomplishing what we set out to do?…
A: Answer:
Q: When it comes to a supply chain, which is more important: cooperation or information sharing?
A: The management of products and services, beginning with the raw materials and continuing through the…
Q: Is there a method that can differentiate between the positives and negatives of the many…
A: An authentication system is a mechanism used to verify the identity of an individual or entity…
Q: 1010.10102 binary floating point to decimal floating point.
A: To convert the binary floating point number 1010.1010₂ to a decimal floating point, we can use the…
Q: The difference b
A: Introduction: In computing terms, there are two main components that make up a computer system:…
Q: Where does the information in these databases come from? Can you get a detailed inventory of what's…
A: Information collection is often referred to as needs gathering or data gathering. For each record in…
Q: Sort out the many approaches of classifying access control systems. Talk about the many options for…
A: Access control systems have the various types this are basically based on the things such as the way…
Q: Create a simple login form using Java Swing Create an RMI application with GUI that will allow…
A: Here's an example code for a simple login form using Java Swing and an RMI application that allows…
Q: ind a regular expression to describe each of the following languages, and draw the corresponding NFA…
A: a) The regular expression for this language is a(aa)*. The language consists of any odd-length…
Q: What did you expect to find out when you initially started searching the internet for solutions? Can…
A: INTRODUCTION: The Internet's revolutionary system architecture has changed the way people do…
Q: TODO: Polynomial Regression with Ordinary Least Squares (OLS) and Regularization *Please complete…
A: Please refer to the following steps for the complete solution to the problem above.
Q: If we were successful in obtaining authentication support, which of our goals would we have the most…
A: Create a list of the benefits and drawbacks of the various authentication processes. Advantages:
Q: B. Indicate which of the following are fundamental data types. c. long double g.double k. signed…
A: The fundamental data types in C/C++ are: char short int long float double long double unsigned char…
Q: Is there a way to compare and contrast the merits of different authentication methods, especially…
A: Modern security systems rely on authentication to make sure that only authorized users can access…
Q: The Set API has the following methods: void add(T) boolean contains(T) boolean…
A: The question is asking which data structure would provide the best worst-case performance for time…
Q: Use modular exponentiation to calculate 3^25(mod 7)
A: Hello student Greetings Hope you are doing great. Thank You!!!
Q: (Assembly windows code) Explain how you would use conditional statements (JZ,JE,...etc.) to solve…
A: Conditional statements in assembly language are used to change the flow of the program based on the…
Q: Is there a difference between digital signatures and other authentication processes?
A: Is there a difference between digital signatures and other authentication processes?
Q: Do hardware and software have distinct purposes?
A: Introduction This inquiry inquires as to the distinction between two key areas of computer science.…
Q: There must be a description of a fictitious scenario for the handling of logins. There are a few…
A: Many phishing attacks grab user credentials and log in as them. When a login seems suspicious, the…
Q: What happens if I leave off the extends Comparable phrase in an implementation like MaxPQ ?
A: Introduction: In Java, it is possible to implement a priority queue using the MaxPQ class. This…
Q: You do realize that hardware and software are distinct categories, right?
A: Introduction: Hardware and software are two distinct categories in computing that work together to…
Q: How is the implementation of multifactor authentication carried out? To what end does this piece of…
A: Introduction: As a way to improve online security, multifactor authentication is gaining popularity.…
Q: Although some find cybercrime disgusting, others find it interesting
A: Cyber crime is the crimes that are carried out on the web which incorporates plotting an infection,…
Q: Can data breaches compromise cloud-based security measures? What precautions may be taken in case…
A: Given: Does a data leak have the potential to significantly affect cloud security? Can anything be…
Q: When did the prevalence and complexity of cybercrime increase to such a high level?
A: INTRODUCTION: Using a computer and a network to carry out illicit acts through digital means is the…
Q: In c++ Create a new project named lab7_2. You’re going to write a class of your choice! The class…
A: The C++ code is given below with output screenshot
Q: *10.1 (Anagrams) Write a function that checks whether two words are anagrams. Two words are anagrams…
A: C++ function that checks whether two words are anagrams: bool isAnagram(const string& s1, const…
Q: Which would NOT likely be an entity on an ERD model for an insurance company’s system that stores…
A: In an ERD model, an entity represents a type of object or concept that has a unique identity and…
Q: Could you provide your own explanation of what a challenge-and-response authentication system is and…
A: Challenge-reaction authentication is a set of computer security protocols where one party poses a…
Q: epsilon nfa not regular nfa
A: In this question, it is asked to convert the given regular expression to epsilon NFA Regular…
Q: When it comes down to it, what should we be hoping to accomplish with authentication? Analyzing the…
A: Introduction: The Goals of Authentication: 1. Authentication ensures that anybody trying to access a…
Q: When a data breach occurs on the cloud, is there any way to make it safer? Is there anything that…
A: Is it possible to strengthen cloud security after a data breach? What are some of the potential…
Q: You are familiar with the parent → child relationship in a binary tree. Write a function which…
A: Algorithm: Start Start by checking if the root is null. If it is, return false. Find the nodes…
Q: Which of the following string methods is a mutator? Choice 1 of 5:.replaceChoice 2 of…
A: The solution is given in the below step
Q: are the primary elements that computerized systems should have, and what are the anticipated…
A: What are the primary elements that computerized systems should have, and what are the anticipated…
Q: Provide me an example of a real SQL database, please
A: Structured Query Language Database language enables producing, altering, and accessing data from…
Q: Why is OSI an abbreviation for "Open System Interconnection"? Compare and contrast the OSI and…
A: a) The OSI model, also known as "Open System Interconnection," gets its name from the fact that it…
Q: Is there a way to compare and contrast the merits of different authentication methods, especially…
A: Distinguished: Differentiating oneself requires appreciating others. Outstanding people often…
Q: Is there a way to compare and contrast the merits of different methods, especially with regards to…
A: Distinguished: The ability to distinguish oneself implies a high regard for others. Exceptional…
Q: Consider a pure ALOHA network with an infinite number of nodes on a straight line path of length ‘n’…
A: We must first take into account the chance of successful transmission for a single node in order to…
Q: Every business should know how to store data in a safe place.
A: In today's digital age, data is one of the most valuable assets that any business can possess.…
Q: What is the purpose of a database audit log? Tell us how SQL Server uses Extended Events in 60…
A: An audit trail, also known as an audit log, is a series of chronological recordings that give…
Q: What are the goals that the authentication method is intended to achieve? Examine the advantages and…
A: Authentication methods are designed to achieve the goal of verifying the identity of an individual…
Q: Are the benefits of cloud computing the same as those of on-premises systems? What are the risks and…
A: Introduction: Rapid scaling, which was created expressly to optimise your workloads for the cloud,…
Trending now
This is a popular solution!
Step by step
Solved in 4 steps with 4 images

- Write a program named GuessingGame that generates a random number between 1 and 10. (In other words, in the example above, min is 1 and max is 11.) Ask a user to guess the random number, then display the random number and a message indicating whether the users guess was too high, too low, or correct.Write a program that calculates the electricity bill. The rates of electricity per unit are as follows:If the units consumed are <=300, then the cost is Rs. 12 per unit.If the units consumed are >300 and <=500, then the cost is Rs. 17 per unit. If the units consumed exceed 500 then the cost per unit is Rs. 22A line rent of Rs. 1500 is also added to the total bill and surcharges of 5% extra if the bill exceeds Rs. 15000. Calculate the total bill with all the conditions given above.Write a program that computes the theoretical flame temperature when a mixture of methane, propane, n-butane, and n-pentane (0% to 100& methane in 5% increments; 0 to 100 mol% propane in 5% increments; 0% to 100% mole n-butane in 5% increments) at 25°C is burned with excess air (0% to 100% excess in 5% increments) preheated to preheated to (50°C to 200°C in 10°C increments)
- Write a program that can be used to calculate the federal tax. The tax is calculated as follows: For single people, the standard exemption is $4,000; for married people, the standard exemption is $7,000. A person can also put up to 6% of his or her gross income in a pension plan. The tax rates are as follows: If the taxable income is: Between $0 and $15,000, the tax rate is 15%. Between $15,001 and $40,000, the tax is $2,250 plus 25% of the taxable income over $15,000. Over $40,000, the tax is $8,460 plus 35% of the taxable income over $40,000. Prompt the user to enter the following information: Marital status If the marital status is “married,” ask for the number of children under the age of 14 Gross salary (If the marital status is “married” and both spouses have income, enter the combined salary.) Percentage of gross income contributed to a pension fund Your program must consist of at least the following functions: Function getData: This function asks the user to enter the…Write a program that can be used to calculate the federal tax. The tax is calculated as follows: For single people, the standard exemption is $4,000; for married people, the standard exemption is $7,000. A person can also put up to 6% of his or her gross income in a pension plan. The tax rates are as follows: If the taxable income is: Between $0 and $15,000, the tax rate is 15%. Between $15,001 and $40,000, the tax is $2,250 plus 25% of the taxable income over $15,000. Over $40,000, the tax is $8,460 plus 35% of the taxable income over $40,000. Prompt the user to enter the following information: Marital status If the marital status is “married,” ask for the number of children under the age of 14 Gross salary (If the marital status is “married” and both spouses have income, enter the combined salary.) Percentage of gross income contributed to a pension fundWrite a program that can be used to calculate the federal tax. The tax is calculated as follows: For single people, the standard exemption is $4,000; for married people, the standard exemption is $7,000. A person can also put up to 6% of his or her gross income in a pension plan. The tax rates are as follows: If the taxable income is: Between $0 and $15,000, the tax rate is 15%. Between $15,001 and $40,000, the tax is $2,250 plus 25% of the taxable income over $15,000. Over $40,000, the tax is $8,460 plus 35% of the taxable income over $40,000. Prompt the user to enter the following information: Marital status If the marital status is “married,” ask for the number of children under the age of 14 Gross salary (If the marital status is “married” and both spouses have income, enter the combined salary.) Percentage of gross income contributed to a pension fund Your program must consist of at least the following functions: Function getData: This function asks the user to…
- Write a program that computes the fuel efficiency for a multi-leg journey. The program will first prompt for the starting odometer reading and then get information about a series of legs. For each leg, the user enters the current odometer reading and the amount of gas used (separated by a space). The user signals the end of the trip with a blank line. The program should print the miles per gallon achieved on each leg and the total MPG for the trip.Write a program that computes the cost of postage on a first-class letter according to the followingrate scale: 105 cents for the first gram or fraction of a gram, 35 cents for each additional half gram,plus a $ 15 service charge if the customer desires special delivery. Note: any partial gram increasewill add 35 cent. For example 1.1 g and 1.5 g will cost 105 +35 = 140 cents $ 1.40Write a program that will compute the sales tax on a $352 purchase. Assume the state sales tax is 4.5 percent and the county sales tax is 2.5 percent. code n cs++ please
- Write a program that calculates the change due a customer by denomination; that is, how many pennies, nickels, dimes, etc. are needed in change. The input is to be the purchase price and the size of the bill tendered by the customer ($100, $50, $20, $10, $5, $1)Write a program that asks the user to enter a number of seconds.Solving the Time Calculator ProblemThere are 86400 seconds in a day. If the number of secondsentered by the user is greater than or equal to 86400, thethe program should display the number of days in that manyseconds.There are 3600 seconds in an hour. If the number of secondsentered by the user is less than 86400 but is greater than orequal to 3600, the program should display the number of hoursin that many seconds.There are 60 seconds in a minute. If the number of secondsentered by the user is less than 3600 but is greater than or equalto 60, the program should display the number of minutes in thatmany secondsA company wants a program that will calculate the weekly paycheck for an employee based on how many hours they worked. For this company, an employee earns $20 an hour for the first 40 hours that they work. The employee earns overtime, $30 an hour, for each hour they work above 40 hours. Example: If an employee works 60 hours in a week, they would earn $20/hr for the first 40 hours. Then they would earn $30/hr for the 20 hours they worked overtime. Therefore, they earned: ($20/hr * 40hrs) + ($30/hr * 20 hrs) = $800 + $600 = $1400 total.





