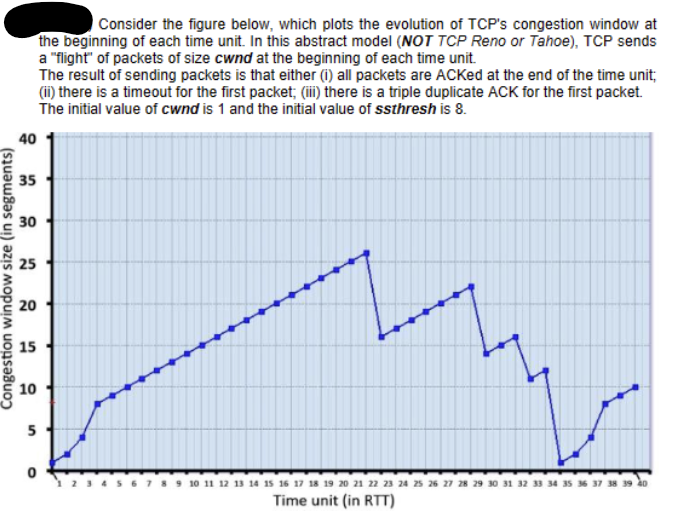
40 40 Consider the figure below, which plots the evolution of TCP's congestion window at the beginning of each time unit. In this abstract model (NOT TCP Reno or Tahoe), TCP sends a "flight" of packets of size cwnd at the beginning of each time unit. The result of sending packets is that either (i) all packets are ACKed at the end of the time unit; (ii) there is a timeout for the first packet; (iii) there is a triple duplicate ACK for the first packet. The initial value of cwnd is 1 and the initial value of ssthresh is 8. 35 30 25 25 Congestion window size (in segments) 20 15 15 10 10 5 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 Time unit (in RTT)
40 40 Consider the figure below, which plots the evolution of TCP's congestion window at the beginning of each time unit. In this abstract model (NOT TCP Reno or Tahoe), TCP sends a "flight" of packets of size cwnd at the beginning of each time unit. The result of sending packets is that either (i) all packets are ACKed at the end of the time unit; (ii) there is a timeout for the first packet; (iii) there is a triple duplicate ACK for the first packet. The initial value of cwnd is 1 and the initial value of ssthresh is 8. 35 30 25 25 Congestion window size (in segments) 20 15 15 10 10 5 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 Time unit (in RTT)
Principles of Information Security (MindTap Course List)
6th Edition
ISBN:9781337102063
Author:Michael E. Whitman, Herbert J. Mattord
Publisher:Michael E. Whitman, Herbert J. Mattord
Chapter6: Security Technology: Access Controls, Firewalls, And Vpns
Section: Chapter Questions
Problem 2RQ
Related questions
Question
Given evolution of TCP's congestion window, provide following: a. List the times, at which TCP is in slow start, congestion avoidance and fast recovery states. b. List the times, at which the first packet in the sent flight of packets is lost and indicate whether the packet loss is detected via timeout, or by triple duplicate ACKs. c. List the times at which the value of ssthresh changes and provide the new value of ssthresh.
Transcribed Image Text:40
40
Consider the figure below, which plots the evolution of TCP's congestion window at
the beginning of each time unit. In this abstract model (NOT TCP Reno or Tahoe), TCP sends
a "flight" of packets of size cwnd at the beginning of each time unit.
The result of sending packets is that either (i) all packets are ACKed at the end of the time unit;
(ii) there is a timeout for the first packet; (iii) there is a triple duplicate ACK for the first packet.
The initial value of cwnd is 1 and the initial value of ssthresh is 8.
35
30
25
25
Congestion window size (in segments)
20
15
15
10
10
5
10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36
Time unit (in RTT)
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 2 images

Recommended textbooks for you

Principles of Information Security (MindTap Cours…
Computer Science
ISBN:
9781337102063
Author:
Michael E. Whitman, Herbert J. Mattord
Publisher:
Cengage Learning

Principles of Information Security (MindTap Cours…
Computer Science
ISBN:
9781337102063
Author:
Michael E. Whitman, Herbert J. Mattord
Publisher:
Cengage Learning