e code complete from Psedo code.
Q: Chef loves lucky numbers. Everyone knows that lucky numbers are positive integers whose decimal…
A: Input/Output Parameter: The first line contains a single positive integer T, the number of test…
Q: When discussing buildings, what precisely do we mean when we talk about their "pattern?" How are…
A: Institution: In server-based and client-server systems, management is centralized, and all clients…
Q: Give some examples of the main pluses of the client/server architectural approach
A: For networks needing a high level of stability, the client/server paradigm is especially advised;…
Q: What distinguishes a data warehouse from a database, specifically?
A: Database: A database is a planned grouping of material that has been arranged and is often kept…
Q: Give some examples of the main pluses of the client/server architectural approach.
A: Client/Server Architectural Approach: Client-server architecture often consists of workstations,…
Q: Ram is a quick-acting, transient type of memory.
A: The operating system - (OS), application programs, and data that are now in use are stored in RAM -…
Q: With the help of quadratic probing solve the following and decide what index student ids should be…
A: Note: The programming language is not mentioned in the question so python programming language is…
Q: n and answer questions please dont JUST do code. and its not a wrighting asignment You will find it…
A: the program is an given below :
Q: Just what are the upsides of adopting design patterns in software development? What are three…
A: Definition: In software development, a design pattern is a general, reusable solution to a frequent…
Q: Why did the initial Linux developers choose for a kernel that was not preemptible? In a single…
A: Launch: One has a cooperative, non-preemptive DOS kernel. It was developed for devices without…
Q: If the procedure between in protocol 5 checked for the condition a Sb Sc instead of the condition a…
A:
Q: Answer the following questions about the MasPar MP-1: (a) Explain the X-Net mesh interconnect (the…
A: (a) x net mesh interconnect built into MP-1 X-Net mesh interconnect consists of number of related…
Q: How about listing three options for minimizing your time spent sitting in traffic? How do you tell…
A: The meaning of minimise: transient verb. Minimize expenditures and delays by reducing or keeping to…
Q: When snakes have a festival they like to have croissants. A snake festival is successful when the…
A: Step-1: Start Step-2: Declare variable croissant and is_holiday Step-3: Take input from user Step-4:…
Q: Compare the performance of write operations achieved by a RAID Level 5 organization with that…
A: Answer:-
Q: understand exactly what is meant by the word "consideration." What does this mean from a software…
A: SUMMARY Software requirements analysis (SRA)SRA is part of the software development process that…
Q: It is important to emphasize "divide and conquer," a fundamental tenet of software engineering…
A: A system-on-a-chip (SoC) is a microchip with all the necessary electronic circuits and parts for a…
Q: 4. Convert the following hexadecimal numbers to their binary equivalents: a. 1C b. 1F.C C. C67 d.…
A: Answer the above question are as follows
Q: When transitioning from on-premises servers to an IaaS-based architecture, what sorts of governance…
A: The infrastructure of the charity's information is managed by the organization's administration…
Q: What qualifications are necessary for an IT professional to work in data warehousing? 5. Explanation…
A: Introduction: Developing data management methods and procedures throughout a company or within the…
Q: Does the transition from on-premises servers to an architecture based on infrastructure as a service…
A: When migrating from onsite servers to cloud servers, are there any governance concerns? IaaS…
Q: Consider the following piece of pseudo- code for computing the average of a data set, where data is…
A: Given pseudocode is computing the average of a data set. Average of data set=Sum of numbers in the…
Q: Problem 1.8 The following code segment, consisting of six instructions, needs to be executed 64…
A: Given, The following instruction code segment contains the following number of instructions for each…
Q: For what reason is software engineering lacking in basic skills?
A: A collection of executable instructions is referred to as a programme: to finish a certain…
Q: Where should you look for governance problems when migrating your IT infrastructure to the cloud?
A: Introduction: Given that When transitioning from on-premise servers to an IaaS architecture, what…
Q: Here, you may choose from two different theories: the Path-Goal Theory and the Leader-Member…
A: Introduction: A leader is someone who doesn't display their dominance inside the business; instead,…
Q: How does the NTPS directory structure differ from the directory structure used in Unix operating…
A: Introduction The Windows NT operating system (OS) uses NTFS, sometimes referred to as the New…
Q: What factors should be taken into account, and how should they be handled, when creating models for…
A: Introduction: When developing models for software-intensive systems, what factors should be…
Q: What exactly does software engineering prototyping aim to achieve?
A: Given: The charity management maintains the infrastructure of the charity information utilising the…
Q: Google has just established a presence in Pakistan with the opening of a local office there. You've…
A: We have asked for the characteristics that influence the microprocessor's speed.
Q: It's crucial to consider what this phrase signifies. What are your thoughts on this in terms of…
A: Introduction: So, what does Critical Concern mean in its most basic sense? Consideration may take…
Q: Print "Censored" if userInput contains the word "darn", else print userInput. End with newline. Ex:…
A: The above question is solved in step 2 :-
Q: Given a class C network IP address 197.20.11.0 and subnet mask is 255.255.255.240. 1. How many bits…
A: According to the information given:- We have to follow the instruction in order to find the How many…
Q: Architecture's advantages include... Compare a project with and without architecture. How will it…
A: Project-planning for software: A software project is an extensive series of programming tasks.…
Q: 2) An 8-way set associative cache memory can accommodate a total of 4K 64-bit blocks from main…
A:
Q: Explain the function of scrambling in the context of digital-to-digital encoding techniques.
A: Modern data communication techniques employ scrambling, a digital encoding technique that helps with…
Q: Give a brief explanation of dynamic memory allocation.
A: introduction: The process of managing system memory, while it is activin, is referred to as "dynamic…
Q: Which of the following Internet of Things components is accountable for translating an electrical…
A: Actuator, then, as an explanation:IoT systems use actuators to transform electrical signals into…
Q: USER INTERFERENCE QUESTION Imagine that you’ve been tasked with redesigning (you being a…
A: The Answer is in step-2.
Q: Define a situation where magnetic stripe cards are insufficient for authentication and smart cards…
A: To regulate access to a resource, ICC or IC cards are physical, electronic authorization devices.…
Q: How many distinct types of addressing exist in a computer network?
A: Computer networking is linking various computers so they can talk with one another and share…
Q: What distinguishes a data warehouse from a database, specifically?
A: Databases and data warehouses are both systems that store data.
Q: Complete the Kennel class by implementing the following methods: addDog(Dog dog) findYoungestDog()…
A: Add the dog at the end of the array in addDog method In findYoungestDog method, we need to iterate…
Q: It's important to understand exactly what is meant by the word "consideration." What does this mean…
A: Here's the solution: Critical Concern Consideration is multifaceted.Consider past, current, and…
Q: advantages and disadvantages of allocating single-user contiguous memory
A: Definition: Contiguous memory allocation for a single user: The user will have access to the CPU…
Q: copy else report.
A: First main class is defined that implements runnable which is actually interface that is used for…
Q: When moving from on-premise servers to an laaS-based design, what sorts of governance issues should…
A: Introduction: In this situation, cloud technology is not only useful but also a secure solution for…
Q: What are the things that make a good documentation?
A: In this question we have to discuss the best things that makes good documentations. Let's discuss
Q: I need help. For the attached image, derive the value of K that will result in a compression ratio…
A: CODE=
Q: List and briefly define important factors that can be used in evaluating or comparing the various…
A:
Make code complete from Psedo code.
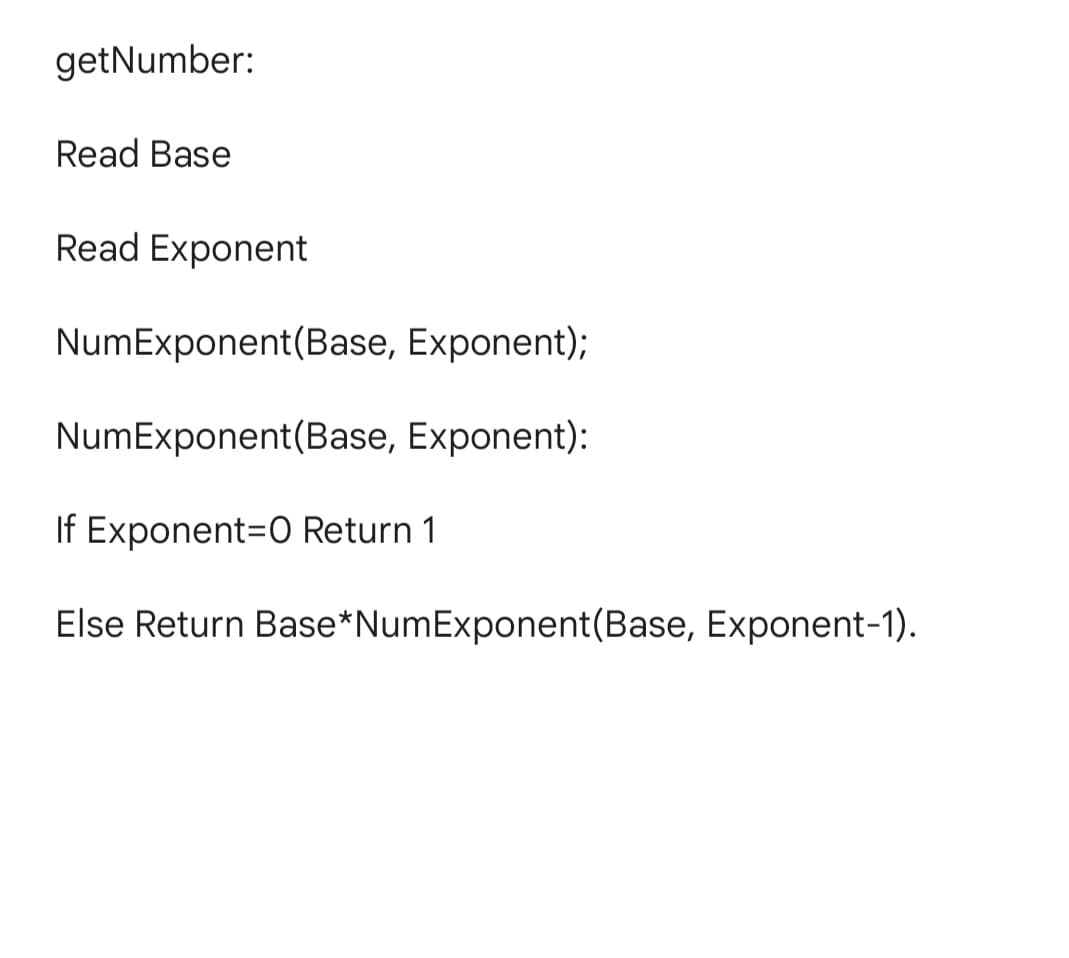
Step by step
Solved in 2 steps with 1 images

- please code in pythonis_phone_num: This Boolean function takes a string and returns True if it is in the formatddd-ddd-dddd, where d is a digit, False otherwise. Example calls:is_phone_num('123-456-7890') --> Trueis_phone_num('123-4556-7890') --> Falseis_phone_num('(123)456-7890') --> Falsewaht is value versionFor each expression in the left-hand column, indicate its value in the right-hand column. Be sure to list a constant of appropriate type (e.g., 7.0 rather than 7 for a double, Strings in "quotes"). Expression Value (int) 9.0/2 23 % 5 - (16 % 10) 1.5 * 2 - 6 / 4 “1”+1 (2+3)+”Hello”+4+2*3 23456/100%10 “a”+4-2
- #include <stdio.h>#include <stdlib.h> //declaring variables globally to calculate coinsint cent50 = 0;int cent20 = 0;int cent10 = 0;int cent05 = 0; //calculate change//pass change variable by addressvoid calculateChange(int* change) {//calculate change only if change is positiveif(*change > 0) {if(*change >= 50) {*change -= 50;cent50++;}else if(*change >= 20) {*change -= 20;cent20++;}else if(*change >= 10) {*change -= 10;cent10++;}else if(*change >= 05) {*change -= 05;cent05++;}//call calculateChange recursively calculateChange(change);}} // function to display the cents valuesvoid printChange() { if(cent50)printf("\n50 Cents : %d coins", cent50);if(cent20)printf("\n20 Cents : %d coins", cent20);if(cent10)printf("\n10 Cents : %d coins", cent10);if(cent05)printf("\n05 Cents : %d coins", cent05);//reset all cent variables with 0cent50 = 0;cent20 = 0;cent10 = 0;cent05 = 0; } //take change input from user//change variable passed addressvoid TakeChange(int*…2.15 LAB: Musical note frequencies On a piano, a key has a frequency, say f0. Each higher key (black or white) has a frequency of f0 * rn, where n is the distance (number of keys) from that key, and r is 2(1/12). Given an initial key frequency, output that frequency and the next 4 higher key frequencies. Output each floating-point value with two digits after the decimal point, which can be achieved as follows:print(f'{your_value1:.2f} {your_value2:.2f} {your_value3:.2f} {your_value4:.2f} {your_value5:.2f}')______ does not end a request. response.write() response.end() response.render()
- given input word, return the list of abbreviations.ex)word => ['word', 'wor1', 'wo1d', 'wo2', 'w1rd', 'w1r1', 'w2d', 'w3', '1ord', '1or1', '1o1d', '1o2', '2rd', '2r1', '3d', '4']""" def generate_abbreviations(word): def backtrack(result, word, pos, count, cur): if pos == len(word): if count > 0: cur += str(count) result.append(cur) return if count > 0: # add the current word backtrack(result, word, pos+1, 0, cur+str(count)+word[pos]) else: backtrack(result, word, pos+1, 0, cur+word[pos]) # skip the current word backtrack(result, word, pos+1, count+1, cur).most_frequent_word() takes a string as the input parameter and returns two values; the word that appears most frequently in that string and the total number of times that word appears in that string. In case of a tie, return the first word that appears in the string. Hint: you can use the unique_words function that you wrote in (4). Sample outputs:>>> data = “chapter one hottest day summer so far drawing close drowsy silence lay over large square houses privet drive cars usually gleaming stood dusty drives lawns once emerald green lay parched yellowing”>>> word = most_frequent_word(data)>>> print(word)('lay', 2)>>> data_2 = "a cat in a hat and a big black bear on a big black rug">>> word = most_frequent_word(data_2)>>> print(word)('a', 4)Fix the following code:Dim dblRegularPay As DoubleDim dblOvertimePay As DoubleintRegularPay = 783.87intOvertimePay = 105.92lbl.TotalPay = (dblRegularPay + dblOvertimePay).ToString ('C')
- #include <iostream> using namespace std; int main() { string c_name ; string car_n; int n, member_n , total ,d; char choice; cout<< "Muscat Auto Workshop"<<endl<<endl; cout<< "Enter customer name : ";cin>>c_name; cout<<" Enter car plate number : ";cin>>car_n; cout<<" choice the required service "<<endl; cout<<" 1-Basic Tuning : 50 OMR "<<endl; cout<<" 2-Software Re-installation : 60 OMR "<<endl; cout<<" 3-Parts Replacement : 100 OMR"<<endl; cout<<" 4-Body Paint : 120 OMR"<<endl; cin>>n; if(n==1) { cout<<" charges before discout = 50 OMR "<<endl; } else if ( n==2) { cout <<" charges before discount = 60 OMR "<<endl; }else if (n==3) { cout<<" charges before discount = 100 OMR "<<endl; }else if (n==4 ) { cout<<" charges before discount = 120 OMR"<<endl; } cout<<" Do you…To remove the value of a variable but keeping the variable in PowerShell, we can use this cmdlet: Group of answer choices Delete-Value Clear-Variable Clear-Value Remove-Variableprogramming: C# (Csharp) Help me please kindly apply the C# METHOD on my program Here is my code: using System; //HEADERclass program { static void Main() { int n; Console.WriteLine("Enter 5-digit number: "); // PROMPT USER n = Convert.ToInt32(Console.ReadLine()); // SCAN Console.Write(n / 10000 % 10 + "*"); Console.Write(n / 1000 % 10 + "*"); //ASTERISK PROCESS PART Console.Write(n / 100 % 10 + "*"); Console.Write(n / 10 % 10 + "*"); Console.Write(n % 10 ); // RESULT }}

