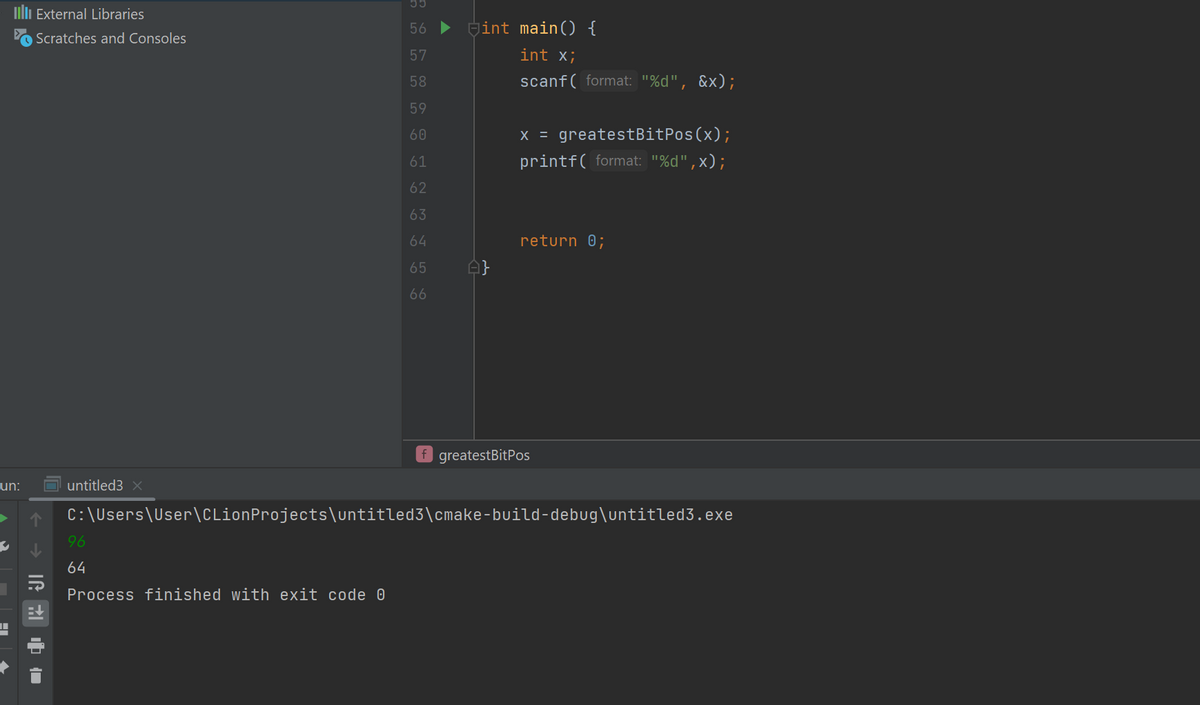
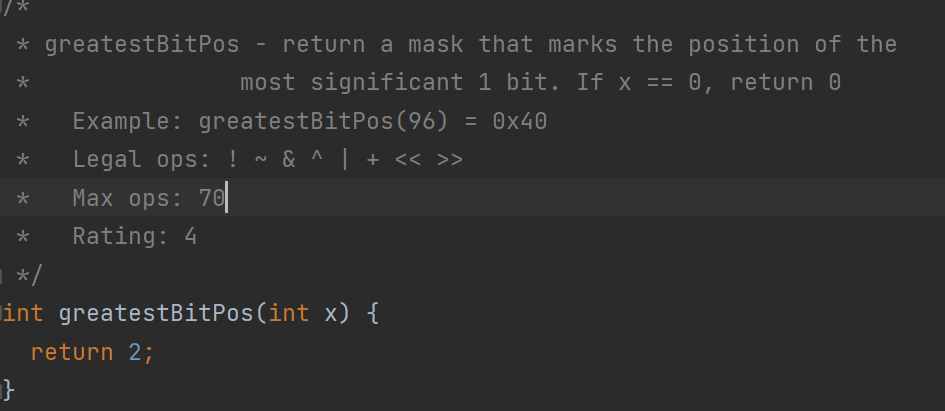
this my code to complete question in the picture but when I run it with 96 get 64 which is value of significant bit can you change it to get answer in example which should be greatestBitPos(96) = 0x40 can you provide it with example of output int greatestBitPos(int x) { int mask = x; mask |= mask >> 1; mask |= mask >> 2; mask |= mask >> 4; mask |= mask >> 8; mask |= mask >> 16; mask &= ~(mask >> 1); return mask;
Q: Assignment: Linked List of Students You have been tasked with implementing a program in Java that…
A: Java program: public class Student { private String name; private int grade; public…
Q: Provide some examples of actual cybercrime that people may be familiar with.
A: Cybercrime is defined as a crime where a computer is the object of the crime or is used as a tool to…
Q: 2. The C language has two methods to create comments. Indicate each type and the give an example of…
A: The above question is solved in step 2 :-
Q: What is a great self-study roadmap for applied mathematics for a focus in computer science? What are…
A: To create a self-study roadmap for applied mathematics with a focus on computer science, you should…
Q: May I ask if you have any ideas for a decent illustration of the term "oops"?
A: There is an established syntax for developing programmes in the object-oriented programming…
Q: Definition of Parameterized Testing.
A: Testing 1) Testing is the process of evaluating a software application or system to identify any…
Q: Can you explain the parallels and contrasts between a time-sharing model and a distributed approach…
A: Introduction: Operating systems (OS) are an essential component of modern computing. There are…
Q: In a computer, what are the three most essential parts?
A: processor, often called the "brain" of a computer, is responsible for executing instructions and…
Q: Assess how you fit within the value chain. The value chain serves what purpose? So, how do you spend…
A: A number of processes are utilised in the value chain to convert input into output in a manner that…
Q: Consider the pattern of red and green packet arrivals to a router’s output port queue, shown below.…
A: Priority scheduling is a process scheduling algorithm that assigns a priority to each process and…
Q: Where can I find out more about SDLC? Just what are the names of the several stages?
A: The Software Development Life Cycle (SDLC) is a methodology for the development of software…
Q: Create a function that takes an amount of monetary change (e.g. 47 cents) and breaks down the most…
A: Input - Integer Output - String as per the condition logic - return { 'q': Math.floor(c /…
Q: When is an exception to a procedure necessary, and why?
A: The operating system schedules many tasks using process scheduling. The operating system chooses the…
Q: Specify all offests with hexadecimal values. Extra spaces or no spaces between arithmetic operators…
A: Please note that as per our guidelines, we are supposed to answer the first three in case of…
Q: Let R be an equivalence relation on A = {0,2,3,5} and R = {(5,5), (0, 2), (3, 3), (2, 0), (2, 2),…
A: To find the number of unique equivalence classes defined by R, we need to determine the number of…
Q: In the realm of computer programming, what does it mean when someone refers to something as a…
A: Introduction: In computer programming, the term "prototype" is commonly used to refer to a…
Q: What exactly is a biased exponent, and how may using one assist one in any way?
A: Unfair exponent Biased exponents are used to increase the exponent by a constant. The extra constant…
Q: Do you find it fascinating to see the evolution of emerging technologies?
A: Observing the development of emerging technologies can be exciting as it provides insight into the…
Q: When and where may malware be found? How are worms distinct from viruses? It is possible to get…
A: Malware, short for malicious software, can be found in various forms and locations. It is typically…
Q: How would one go about writing the SDLC module of a hospital in the context of midwife-led primary…
A: Conceptually speaking, the SDLC model is a form of a model. It develops a framework describing all…
Q: Create a simple matching algorithm for a round robin competition. in which the number of…
A: given data: in: round index r (0 ≤ r ≤ 2 · (n − 1)/2); number of players n (1 ≤ n)out: sequence R of…
Q: While making the transition from one system to another, what considerations should be made? Why…
A: System The term "system" is used here in a general sense and does not refer to any specific type of…
Q: network's routers
A: Given :- In the above given question, a statement is mention in the above given question Need to…
Q: Is CBIS suitable for each and every business out there? How exactly did the CBIS become made in the…
A: Online businesses use corporate computer-based information systems (CBIS) to acquire and sell goods.…
Q: What, if any, distinctions exist between a time-sharing system and a distributed operating system?
A: Time Sharing OS It enables the numerous users to share the computer at the same time. each action…
Q: Can you explain why and how firewalls work?
A: A firewall is an important network security system designed to protect devices and networks from…
Q: Explain how one can check a graph’s acyclicity by using breadth-first search.
A: Acyclicity of a graph can be checked by using breadth-first search. To do so, start at any vertex…
Q: How may formative scales be used to examine moderating influences across levels?
A: There are two different sorts of levels that make up the cross-level moderating effect. These are…
Q: Explain what dynamic scoping is, when it's utilized, and how it may be made to run faster.
A: The term "dynamic" refers to anything that is always changing. A paradigm that loads the programme…
Q: Determine whether or not a computer has any serious hardware issues, explain what could be causing…
A: Potential fault: Skipping work like upgrading the software or installing security software that…
Q: Please explain the differences between the ARM architecture and the core i3 architecture.
A: Core i3The Core i3 features built-in graphics. Core i3 is 64-bit architecture compatible. It offers…
Q: Let R be an equivalence relation on A = {0, 5, 7,9} and R = {(0, 9), (0, 5), (7, 7), (9,5), (5, 9),…
A: Since R is an equivalence relation, it partitions A into equivalence classes. An equivalence class…
Q: The file hierarchy consists of Blank 1, Blank 2, and Blank 3 (in alphabetic order).
A: This question is about the organization of files in a computer system. The term "file hierarchy"…
Q: Irrelevant are plans that haven't been tried and tested. List the many methods of testing that might…
A: Introduction: When it comes to plans and strategies, it's important to test them out to determine…
Q: Explanation of why different testing approaches are required at different phases of the software…
A: Introduction The software development life cycle (SDLC) is a set of techniques used by software…
Q: In our shuffling algorithm, let's say that you select a random integer between 0 and N-1 as opposed…
A: Suppose we have a deck of N cards labeled 1 through N. In each iteration of the shuffle algorithm,…
Q: In the following drawing, the RING mutual exclusion algorithm is running on a collection of…
A: The question describes a scenario where the RING mutual exclusion algorithm is running on a…
Q: Statements at the source level and I/O actions are both tracked by this variable.
A: Algorithm: An algorithm is a series of instructions that are well specified and are often used in…
Q: While working with a relational database, a select operation may be used to prune unnecessary…
A: The select operation is essentially an operation that searches the data contained inside the table…
Q: What's the deal with Deep Learning vs Traditional Machine Learning?
A: Deep learning: This subfield of machine learning operates on artificial Both neural networks and…
Q: What distinguishes hardware malfunctions from software ones?
A: Introduction: Hardware and software are two essential components of modern computer systems.…
Q: Create an algorithm to check whether the number entered is positive or negative using GoTo Statement…
A: Please find the answer below :
Q: Write a short C program that declares and initializes (to any value you like) a double, an int, and…
A: This code declares and initializes a double, an int, and a char variable, and then declares and…
Q: hing to the cloud solve all of a company's IT problems?
A: Cloud computing is a model for delivering on-demand computing resources over the internet, such as…
Q: The branch of mathematics known as ring topology may be thought of as a kind of geometry. Explain…
A: By interconnecting devices in a circle, a ring topology generates a circular data channel. Each…
Q: he purpose of this writing is
A: Wireless metropolitan area networks have been used even without the high cost of laying fiber or…
Q: A "standard" single-tape Turing machine M has a one-way infinite tape; the set of valid tape head…
A: Here the question is based on Turing Machine. Basically, a Turing Machine is a device that accepts…
Q: Where can I find out more about SDLC? Just what are the names of the several stages?
A: Systems development Life cycle is a defined technique for delivering a high-quality system that…
Q: What this phrase refers to is testing inside a "BLACK BOX." What are some of the many takes that may…
A: Black Box Testing is a method for evaluating the functionality of software applications without…
Q: Write a program that reads in lines from standard input with each line containing a name and two…
A: program given in next step:
int mask = x;
mask |= mask >> 1;
mask |= mask >> 2;
mask |= mask >> 4;
mask |= mask >> 8;
mask |= mask >> 16;
mask &= ~(mask >> 1);
return mask;
}
Step by step
Solved in 3 steps with 1 images

expected output is 0x40 not 64
example greatestBitPos(96) = 0x40
- ; initialized data heresection .data msg db "Print String!", 0xamsglen equ $-msg ; string length in bytesSTDOUT equ 1 ; standard output deviceSYS_write equ 1 ; write messageSYS_exit equ 60 ; exit programEXIT_OK equ 0 ; return value ; code goes heresection .text ; The '_start' label identifies the program's entry point for the; linker for the 'nasm' assembler. If you use 'gcc', the entry point; is labeled 'main'global _start_start: ; send message string to standard output mov rsi, msg ; text address mov rdx, msgln ; string length (error here) mov rdi, STDOUT ; output device mov rax, SYS_write ; rax holds the function syscall ; system…Caesars Cypher in C programming language How do you program an encryption and decryption for a Caesars Cypher that covers all the possible ASCII characters? In this there should be a shift over K = 5 but the example below is K = 3. This should result in actual character and not the control ASCII represenations. For example: >>> $ encrypt(I have a key)N%mf{j%f%pj~>>> $ encrypt(see me at 3)xjj%rj%fy%8>>> $ decrpyt(|jfw%ns%gqzj)wear in blue Assume that the text parsing method has been succesful and it's the encryption/decryption of the char array that needs to be factored. Formula Encryption -> C = E(k, P) = (P + k) (mod 26) Decryption -> P = D(k, C) = (C - k) (mod 26) Where k = 5* Assignment: Word operations * * Description: * This assignment asks you to implement common word operations that are * not available in the Scala programming language. The intent is to practice * your skills at working with bits. * */ package wordOps /* * Task 1: Population count (number of 1-bits in a word) * * Complete the following function that takes as parameter * a 32-bit word, w, and returns __the number of 1-bits__ in w. * */ def popCount(w: Int): Int = ??? /* * Task 2: Reverse bit positions * * Complete the following function that takes as parameter * a 16-bit word, w, and returns a 16-bit word, r, such that * for every j=0,1,...,15, * the value of the bit at position j in r is equal to * the value of the bit at position 15-j in w. * */ def reverse(w: Short): Short = ??? /* * Task 3: Left rotation * * Complete the following function that takes two parameters * * 1) a 64-bit word, w, and *…
- Decrypt a message that was encrypted using the following logic: • First the words in the sentence are reversed. For example, "welcome to hackerrank" becomes "hackerrank to welcome" • For each word, adjacent repeated letters are compressed in the format <character><frequency>. For example, "mississippi" becomes "mis2is2ip2i" or "baaa" becomes "ba3". Note the format is not applied for characters with frequency 1. Also, the frequency will be no greater than 9 Return the decrypted string Exampl e..2.amplepython: def dna_slice(strand, first_nucleotides, last_nucleotides): """ Question 3 - Regex You are working with a long strand of DNA. Your task is to find and return the length of the first substrand that begins with the two-letter sequence specified in first_nucleotides and ends with the sequence specified in last_nucleotides. THIS MUST BE DONE IN ONE LINE. Args: strand (str) first_nucleotides (str) last_nucleotides (str) Returns: int strand_1 = 'TATGGGTCGAGCATGT' >>> dna_slice(strand_1, 'AT', 'CG') 8 >>> dna_slice(strand_1, 'GT', 'TG') 10 """ strand_1 = 'TATGGGTCGAGCATGT' pprint(dna_slice(strand_1, 'AT', 'CG')) pprint(dna_slice(strand_1, 'GT', 'TG'))given ASCIIOFSET .FILL x0030 NegASCIIOFSET .FILL xFFD0 ASCIINewline .FILL x000d ; Newline ascii code ASCIISpace .FILL x0020 ; Space ascii code ASCIIComma .FILL x002C ; Comma ascii code Use LC-3 I/O device to print number, commas, and spaces in printCommaSpace subroutine, also check code to see if it follows instructions and modify accordingly
- #include<stdio.h> #define FAIL_VAL -99999#define SUCCESS_VAL 99999#define MAX_USER 20#define MAX_LEN 200 char emailArr[MAX_USER][MAX_LEN];char passArr[MAX_USER][MAX_LEN]; char nameArr[MAX_USER][MAX_LEN];char addressArr[MAX_USER][MAX_LEN]; int user_count=0; int signupUser(char email[], char pass[]){ char Email_id[60]; int i;//p1=0,p2=0; printf("Enter your Email_id: "); scanf("%s", &Email_id); if(Email_id[i]=='@' && Email_id[i]=='.') { printf("Your Email_id is valid"); } else { printf("Email_id invalid.Please enter a valid id."); } } int loginUser(char email[], char pass[]){ //Write your code here} int buildUserProfile(char email[], char firstName[], char lastName[], char address[]){ //Write your code here} void searchByName(char name[]){ //Write your code here} void searchByAddress(char address[]){ //Write your code here} int main(){ while(1) {…#include<stdio.h> #define FAIL_VAL -99999#define SUCCESS_VAL 99999#define MAX_USER 20#define MAX_LEN 200 char emailArr[MAX_USER][MAX_LEN];char passArr[MAX_USER][MAX_LEN]; char nameArr[MAX_USER][MAX_LEN];char addressArr[MAX_USER][MAX_LEN]; int user_count=0; int signupUser(char email[], char pass[]){char Email_id[60];int i;//p1=0,p2=0;printf("Enter your Email_id: ");scanf("%s", &Email_id); if(Email_id[i]=='@' && Email_id[i]=='.'){printf("Your Email_id is valid");}else{printf("Email_id invalid.Please enter a valid id.");} } int loginUser(char email[], char pass[]){//Write your code here} int buildUserProfile(char email[], char firstName[], char lastName[], char address[]){//Write your code here} void searchByName(char name[]){//Write your code here} void searchByAddress(char address[]){//Write your code here} int main(){while(1){printf("*******************************************************************\n");printf("1. signup User. 2. login User. 3. build User Profile.…#include<stdio.h> #define FAIL_VAL -99999#define SUCCESS_VAL 99999#define MAX_USER 20#define MAX_LEN 200 char emailArr[MAX_USER][MAX_LEN];char passArr[MAX_USER][MAX_LEN]; char nameArr[MAX_USER][MAX_LEN];char addressArr[MAX_USER][MAX_LEN]; int user_count=0; int signupUser(char email[], char pass[]){char Email_id[60];int i;//p1=0,p2=0;printf("Enter your Email_id: ");scanf("%s", &Email_id); if(Email_id[i]=='@' && Email_id[i]=='.'){printf("Your Email_id is valid");}else{printf("Email_id invalid.Please enter a valid id.");} } int loginUser(char email[], char pass[]){//Write your code here} int buildUserProfile(char email[], char firstName[], char lastName[], char address[]){//Write your code here} void searchByName(char name[]){//Write your code here} void searchByAddress(char address[]){//Write your code here} int main(){while(1){printf("*******************************************************************\n");printf("1. signup User. 2. login User. 3. build User Profile.…
- #include<stdio.h> #define FAIL_VAL -99999#define SUCCESS_VAL 99999#define MAX_USER 20#define MAX_LEN 200 char emailArr[MAX_USER][MAX_LEN];char passArr[MAX_USER][MAX_LEN]; char nameArr[MAX_USER][MAX_LEN];char addressArr[MAX_USER][MAX_LEN]; int user_count=0; int signupUser(char email[], char pass[]){ char Email_id[60]; int i;//p1=0,p2=0; printf("Enter your Email_id: "); scanf("%s", &Email_id); if(Email_id[i]=='@' && Email_id[i]=='.') { printf("Your Email_id is valid"); } else { printf("Email_id invalid.Please enter a valid id."); } } int loginUser(char email[], char pass[]){ //Write your code here} int buildUserProfile(char email[], char firstName[], char lastName[], char address[]){ //Write your code here} void searchByName(char name[]){ //Write your code here} void searchByAddress(char address[]){ //Write your code here} int main(){ while(1) {…Program Specifications: Your task is to write a program that can decrypt a message that has been encoded using a Caesarcipher. Stated another way, you need to find the “shift” for the cipher. Once you have the shift,you know the mapping so you can decrypt the message. the encryption code. use python. def encrypt(text, r): #abcdefghijklmnopqrstuvwxyzresult = ''for i in range(len(text)): # Hello Khoorchar = text[i]if char.isupper():result = result + chr((ord(char) + r - 65 ) % 26 + 65)else:result = result + chr((ord(char) + r - 97) % 26 + 97)return result while True:msg = input("\n\tEnter a String / message e.g. Today is Thursday ")rotation = int(input("\n\tEnter number of rotation e.g. 3 "))print("\n\tOriginal Message is==> ",msg," with rotation ",rotation, " The CypherText ", encrypt(msg,rotation)) No hand written and fast answer with explanationCiphers use many bitwise operations for cryptography. Write an ARM assembly program to use ciphers. See the steps below to implement the cipher. In this program you will implement a Symmetric Encryption. a) Assign a variable name “Choice” with value 0 or 1 to show the choice for encryption or decryption. 0 for encrypt and 1 for decrypt. . b) If we assign 0 to the variable choice the program will do encryption and if its 1 the program will do decryption. c) For encryption design a key value, for that assign your last nonzero number of your number in a variable called “Key” Example: if your number is 5012345 Assign 5 to the variable Key and use it as the Key for encryption. d) For choice 0 store the Cipher in a variable called “C”, for choice 1 store the Plain text in a variable called “P” (use symmetric Key cryptography and implement that for encryption and decryption). e) Test the encrypt program using the first letter of your name in capital case and to test decryption use the…

