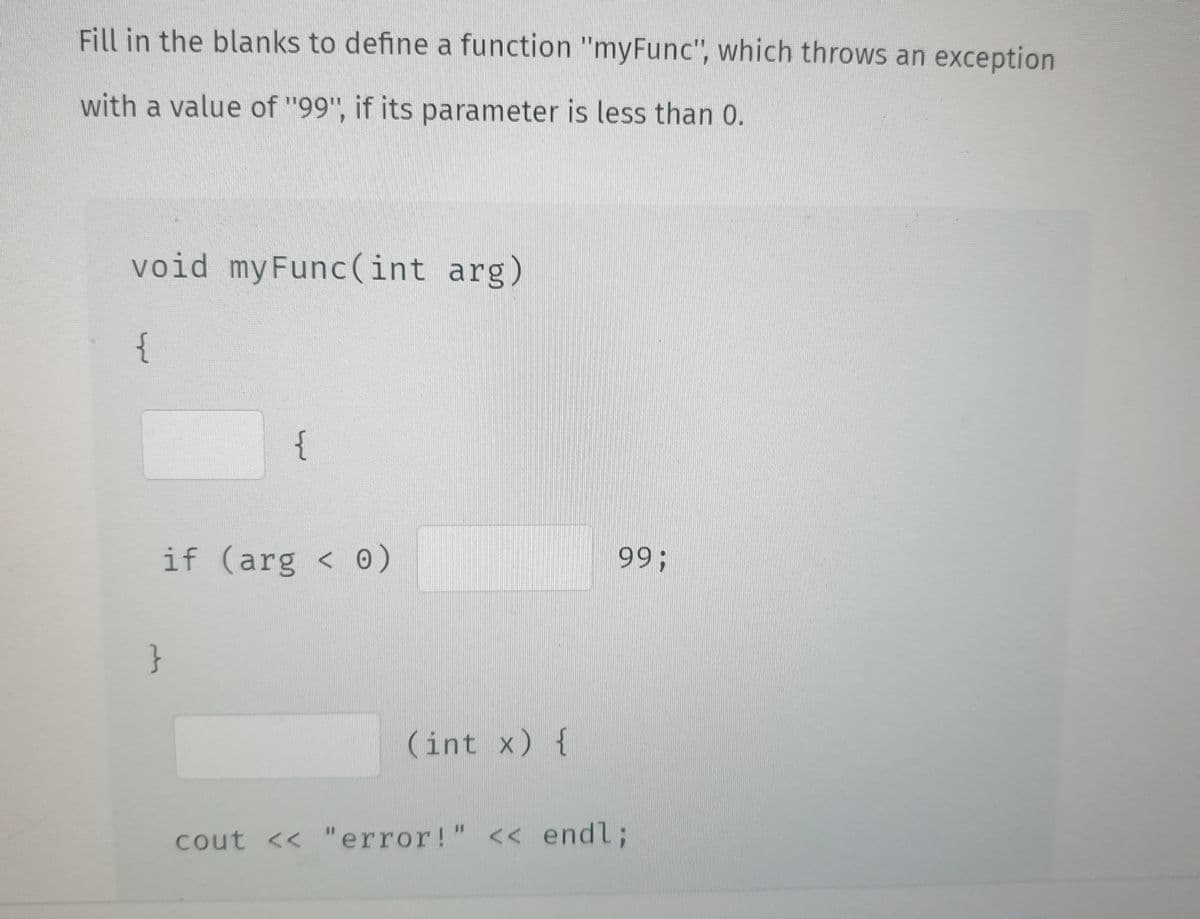
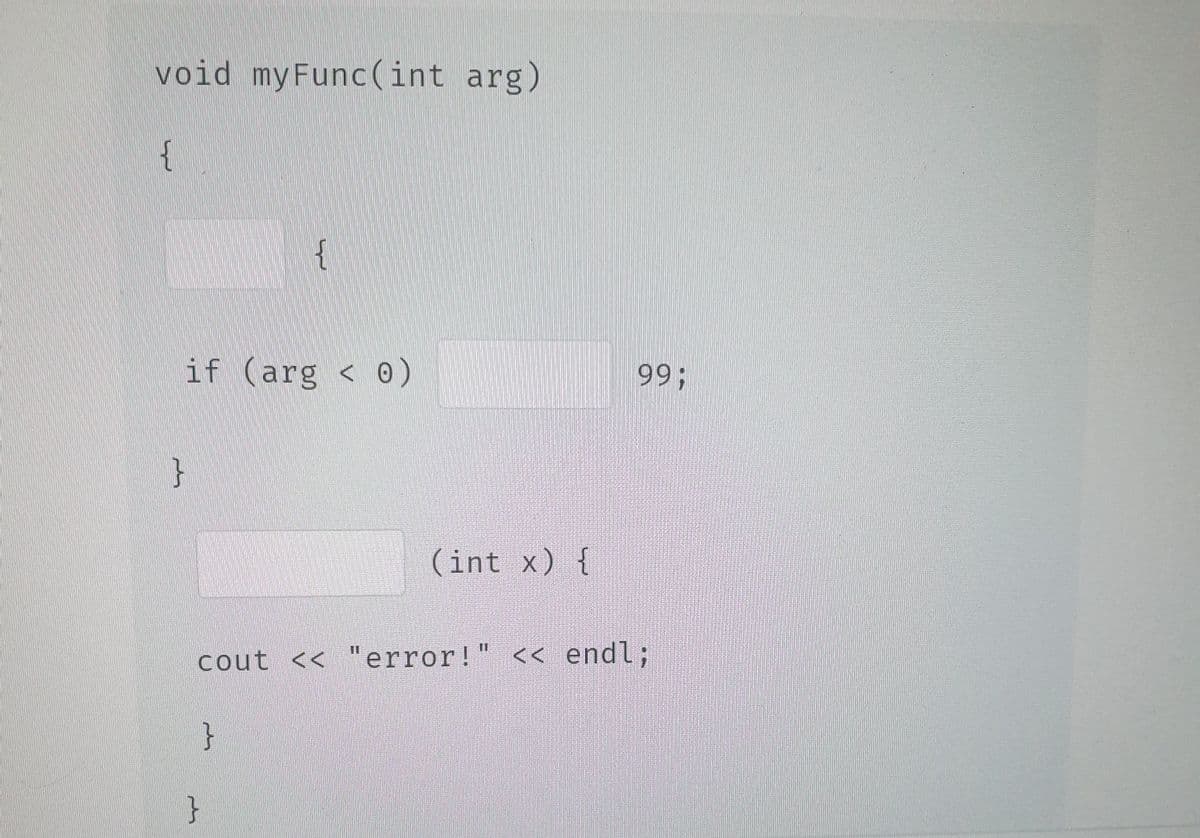
Fill in the blanks to define a function "myFunc", which throws an exception with a value of "99", if its parameter is less than 0.
Q: How is a pairing heap represented? a) binary tree b) fibonacci tree c) heap ordered tree d) treap
A: A binary search tree is a main binary tree, whose internal nodes each stores a key and each has two…
Q: cuss in detail ten AI technologies used for educational system tran
A: Introduction: Below the discuss in detail ten AI technologies used for educational system…
Q: What basic traits and qualities make up a descriptive model?
A: Introduction A descriptive model is an interaction that portrays genuine occasions and the…
Q: Explain the differences between supervised and unsupervised learning using an example.
A: Introduction: Machine learning, a subfield of artificial intelligence and computer science, aims to…
Q: Define technological shifts
A: answer is
Q: Convert the following grammar to its CNF form: S→ ASA | aB | CaB
A:
Q: Test Test:: } newObj.mem mem = + newObj; return newObj; Test (Test obj) { obj.mem; operator+ class…
A: Polymorphism is an OOP concept by which we can perform a single action in different ways i.e. using…
Q: The roots of the elements of the subtrees are smaller than the root of the heap. a) True b) False
A: Correct Answer: False
Q: Briefly explain the 4IR categories namely physical, digital and biological
A: Answer:
Q: Q. When automatic failover occurs, Amazon RDS will emit a DB Instance event to inform you that…
A: Yes, Amazon RDS will notify you that an automatic failover took place by sending a DB Instance…
Q: When automatic failover occurs, Amazon RDS will emit a DB Instance event to inform you that…
A: Amazon Relation Database System(RDS) The Amazon Relational Database Service (Amazon RDS) is a Web…
Q: Explain the different factors affecting the processing speed of CPU.
A: In Step 2, I have provided answer with brief explanation-----------------
Q: How well do you comprehend the TCSEC orange book?
A: Introduction: computer protection Fundamentally, computer security is the protection of computer…
Q: Which tree provides a linear time solution for substring operation?
A: Which tree provides a linear time solution for substring operation?a) Rope Treeb) Suffix Treec)…
Q: Consider the dataset in terms of attribute-value pairs where F is the value, and A,B, C are…
A: We can think about the entropy of a dataset in terms of the probability distribution of observations…
Q: Remove Duplicates This function will receive a list of elements with duplicate elements, this…
A: Duplicate element Duplicates include integer, string, or list item that occurs multiple times.…
Q: How is artificial intelligence explained in caret?
A: Introduction: Caret includes predict to help you predict the dependent variable for the testing set…
Q: GSM time slot is 577 s (microseconds) in duration and includes far more than a snapshot of each…
A: The answer is
Q: What are the disadvantages of normal binary tree traversals?
A: Correct answer is a
Q: What is the basic operation performed in a pairing heap? a) merge b) deletion c) insertion d)…
A: Multiplication (repeated addition) and division are two different ways that the fundamental…
Q: Draw the waveform for the data 100100110 using the following encoding schemes: (i) Unipolar NRZ (ii)…
A:
Q: Consider the game having the following normal form. Which of the following strategies of the row…
A: According to the information given:- We have to choose the correct option to satisfy the statement.
Q: Show the output that would be generated by each of the following program fragments: for w in "Now is…
A: for w in "Now is the winter of our discontent ... ".split () split() method in Python split a string…
Q: What will be the position of 5, when a max heap is constructed on the input elements 5, 70, 45, 7,…
A: Answer is option b) 5 will be at last level in max heap child node should be less than the…
Q: Given a chess board, your job is to write a program that takes two squares x and y as input and then…
A: Program: #include <bits/stdc++.h> using namespace std; int dx[8]={-2, -2, -1, -1, 1, 1, 2,…
Q: Write a program using stack and queue with linked implementation. Sample output: Press q to generate…
A: please check the step 2 & 3 for solution
Q: List the essential features of an Embedded Computer Solution.
A: Intro An embedded computer is characterized as a regulator customized and constrained by an ongoing…
Q: e
A: you forgot to provide the table names. that really does not matter here. let us call the first table…
Q: real-time cl ach host nee 00 unique ic ne that each IPv4 addres nique ID fo
A:
Q: IN JAVA Write a method (also known as functions in C++) named isPerfect that takes in one parameter…
A: A perfect number is a number whose sum of factors (excluding the number itself) is equal to the…
Q: The steps for finding post-order traversal are traverse the right subtree, traverse the left subtree…
A: However, there are numerous ways to navigate around the data in a hierarchical data structure like a…
Q: 4. Convert the NFA in Figure 1 into an equivalent DFA using the standard procedure. for such a…
A: Below is the answer to above question...
Q: write alogrithms for the following blocks of code... 1st block: void HRM::UpdatePerson(){ int…
A: Define one structure to hold the details of an employee. This structure can hold the first name,…
Q: If there are c children of the root, how many calls to the merge procedure is required to reassemble…
A: Let us see the answer below,
Q: Who among the following provided the first online contribution of Suffix Tree? a) Weiner b) Samuel…
A: Explanation- A suffix tree is otherwise called a PAT tree or a place tree in software engineering.…
Q: What kinds of tools and technologies may be utilised to help in software testing? Give detailed…
A: Introduction: The following tools and technologies can be used to help in software testing. Tool for…
Q: Explain the following terms: Cursor, Embedded SQL, JDBC, SQLJ, stored procedure.
A: The question has been answered in step2
Q: 5.18 LAB - Word frequencies Write a program that reads a list of words. Then, the program outputs…
A: Answer: Algorithms Step1: we have make function name as freq to pass the argument as string Step2:…
Q: Which statement is correct of suffix tree with a string of length n?
A: Which statement is correct of suffix tree with a string of length n?a) The tree has n leaves.b)…
Q: Question What factors are behind the changes in the OWASP Top 10 web application security list?
A: What Is OWASP? The Open Web Application Security Project (OWASP) is a 501(c)(3) nonprofit…
Q: Who among the following algorithm is used in external memory and compression of the suffix tree? a)…
A: The answer is Farach’s algorithm . Below is the explanation :
Q: Lottery number generator: Write a program that generates a seven-digit lottery number. The program…
A: Step-1: StartStep-2: Declare a empty listStep-3: Start a loop from i=0 to 6 Step-3.1: Declare a…
Q: Can leaf node be called child node in a ternary tree? a) True b) False
A: Can leaf node be called child node in a ternary tree? Answer is true.
Q: List and discuss ten AI technologies used for educational system transformation.
A: Introduction: Artificial intelligence is broadly used to give customized suggestions to individuals,…
Q: Anna and Belle have a lot of common friends but the two of them are not on speaking terms. Both want…
A: from the given question, Anna and Belle have a lot of common friends. both are inviting friends on…
Q: What new developments in computers and software engineering have taken place outside of the United…
A: Introduction: By employing engineering principles, software engineering describes the process of…
Q: What use does the Toolbox serve in the Visual Studio setting?
A: Toolbox: When the cursor is moved over the Toolbox icon on the left side of the Visual Studio IDE,…
Q: Given a chess board, your job is to write a program that takes two squares x and y as input and then…
A: C++ Program #include <bits/stdc++.h> using namespace std; int dx[8]={-2, -2, -1, -1, 1, 1, 2,…
Q: Programming Task 1: Happy Number A happy number is a number defined by the following process:…
A: - We have to code for the happy number in java.
Q: How many spanning trees does the following graph have?
A:
Fill in the blanks. Question and blanks are in the picture
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

- Fix an error and show it please? And here are the information about the homework and for the error too. def kwargs_to_args_decorator(*args, **kwargs): This question is meant to test your knowledge of creating a decorator that accepts an arbitrary number of positional and keyword arguments, to decorate a function that accepts an arbitrary number of positional and keyword arguments, and alters the arguments before passing them to the decorated function. When the decorated function is invoked, this decorator should modify the arguments the decorated function receives. This decorator should filter out all positional arguments passed to the decorated function, which are found in the positional arguments passed to the decorator when the decorator was initialized. It should also filter out all keyword arguments with keys that are found in the keyword arguments given to the decorator when the decorator was initialized. After performing the modifications to the arguments, the decorator should…In c++ implement function getPercentage that takes two inputs: grade and total Grade and outputsthe gradepercentage as follows: percentage = (grade/total grade)*100 . (Assume a student can notget a grade above 100%)Define your own exception classes:1. DivideByZeroException as a derived class of Standard Library class runtime_error,that is used to detect division by zero run time error.2. NegativeNumberException as a derived class of Standard Library class logic_error,that is used to detect if the user entered a negative number as a grade.3. InvalidGradeException as a derived class of Standard Library class logic_ error, thatis used to detect if a user entered an invalid input (grade greater than total grade).Use the above exception classes after implementing them to apply exception handling foryour getPercentage function.QUESTION 15 Python supports the creation of anonymous functions at runtime, using a construct called __________ A. def B. pi C. anonymous D. lambda
- void getChar(char& c, istream& infile, int& i){ infile.get(c); if (c == '\n') i++;} COULD YOU REWRITTE THE FUNCTION ABOVE. AND BY REWRITE. I MEAN CHANGE THE FUNCTION NAME, PARAMETERS, AND ITS IMPLEMENTATION. HOWEVER, THE FUNCTION MUST STILL ACHEIVE THE SAME GOAL.C++ Write the definition of the function int computerProd() with parameters that receives as arguments two integer values values, computes their product and returns it to the calling function.C++ Write the defenition of the function int computerProd() with parameters that receives ss arguments two integer values values compute their product and returns it to the calling function.
- Q2 Write the pseudo-code of Q1 using C++ language supposing that you have the following variables and functions already defined: A1: the distance from target A2: the angle to target MOVEFORWARD: to move forward TURN(VAL): to turn right or left. If the parameter is positive it turns to the right, else to the left.Use Clojure to complete these questions: Please note that this is the beginning of the course so please use simple methods possible, thanks a. The built-in function type is useful for checking what kind of object an expression evaluates to. Write a function both-same-type? that takes two arguments, and returns true when they both have the same type, and false otherwise. b. Write a function list-longer-than? which takes two arguments: an integer n, and a list lst and returns true if lst has more than n elements, and false otherwise. For example, (list-longer-than? 3 '(1 2 3)) should return false, and (list-longer-than? 2 '(1 2 3)) should return true. c. See attached picture.Please code in python You are tasked with helping write part of an exciting new word-guessing game, “Durdle”. The game is one in which a player attempts to guess a five-letter word in successive guesses. In this problem and the next one, we will build an implementation of this word-guessing game. First, to support this game, we will write a function named durdle_match(guess, target) that takes in two strings - a player’s guess, and the target word that the player is attempting to guess. Each of the given words is five letters long. This function should return a five-letter string consisting of the letters B, G, and Y that has a meaning associated with the guess as follows: B: This letter in the guess does not appear in the target string Y: This letter in the guess appears in the target string in another location G: This letter in the guess appears in the same location in the target string Hints: You may assume that both of the input strings are 5 letters and all lowercase.
- a. Extend the definition of the class newString as follows:i. Overload the operators + and += to perform the string concatenation operations.ii. Add the function length to return the length of the string.b. Write the definition of the function to implement the operations defined in part a.c. Write a test program to test various operations on the newString objects.Q. Please solve this C++ program and show all the steps. (kindly do not use any advanced coding or coding info from any other program. Don't copy from other sources too) a) Add a new function convMonth to the class Date that returns the month in letters (e.g., January, February, etc.). b)Add a function that prints the date using the following format: Month dd, yyyy . Example, January 21, 2023 c) Test the new functions of the class Date by creating dynamically (i.e., using pointers) two objects of the class Date and invoking the new member functions on both objects. Deliverables: date.h, date.cpp, testdate.cpp. (any description or thought process of this coding problem will be really useful, particularly in part c) please let me know if there's any way I could contact you for further assistance,( please!) Thank you !1) Write a complete program that will have a main function and a function called twice. a. Write a function named twice whose only parameter is an integer pointer.b. This function doubles the value stored at the location pointed by the pointerparameter.c. In the main method, declare an integer variable num and initialize it to 5. Call thefunction twice from main such that the function twice will double the value of num.d. In the main method and after calling the function, print the variable num.

