n and answer questions please dont JUST do code. and its not a wrighting asignment You will find it useful to read through the whole question before starting t
n and answer questions please dont JUST do code. and its not a wrighting asignment You will find it useful to read through the whole question before starting t
Database System Concepts
7th Edition
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Chapter1: Introduction
Section: Chapter Questions
Problem 1PE
Related questions
Question
Please read information and answer questions please dont JUST do code. and its not a wrighting asignment
You will find it useful to read through the whole question before starting to answer it.
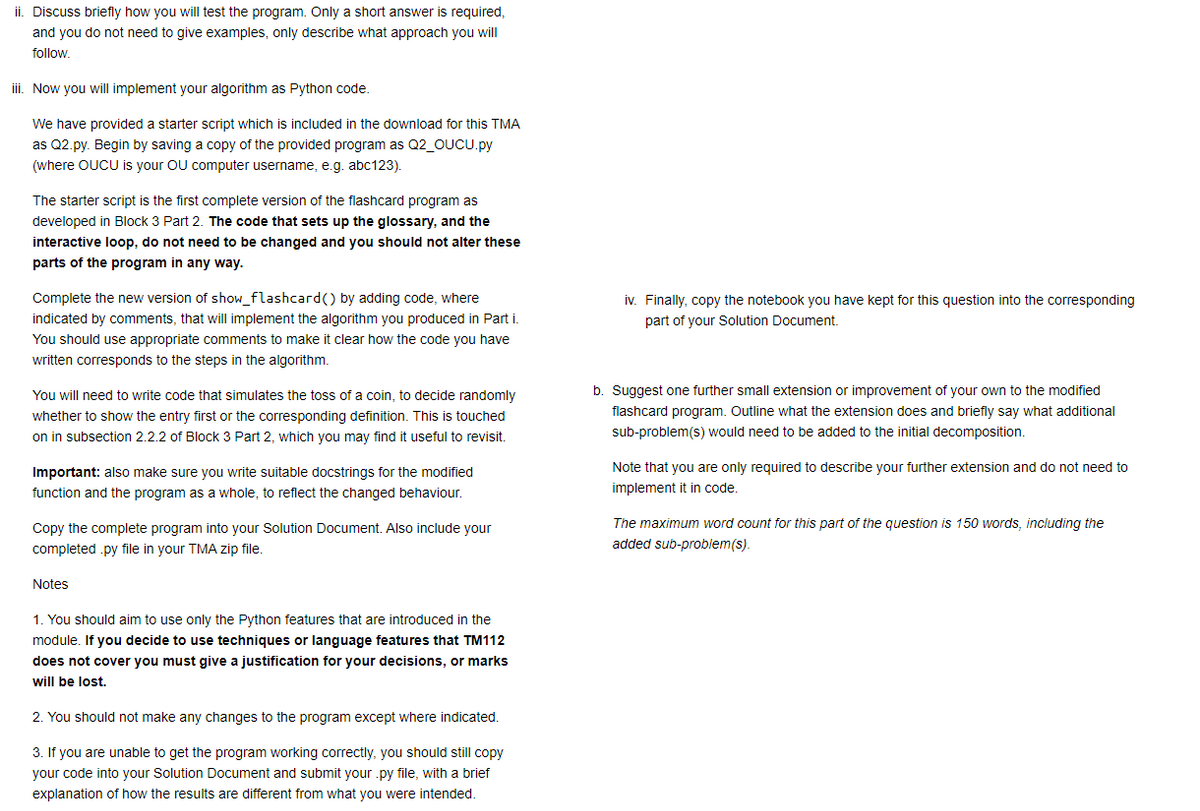
Transcribed Image Text:ii. Discuss briefly how you will test the program. Only a short answer is required,
and you do not need to give examples, only describe what approach you will
follow.
iii. Now you will implement your algorithm as Python code.
We have provided a starter script which is included in the download for this TMA
as Q2.py. Begin by saving a copy of the provided program as Q2_OUCU.py
(where OUCU is your OU computer username, e.g. abc123).
The starter script is the first complete version of the flashcard program as
developed in Block 3 Part 2. The code that sets up the glossary, and the
interactive loop, do not need to be changed and you should not alter these
parts of the program in any way.
Complete the new version of show_flashcard() by adding code, where
indicated by comments, that will implement the algorithm you produced in Parti
You should use appropriate comments to make it clear how the code you have
written corresponds to the steps in the algorithm.
You will need to write code that simulates the toss of a coin, to decide randomly
whether to show the entry first or the corresponding definition. This is touched
on in subsection 2.2.2 of Block 3 Part 2, which you may find it useful to revisit.
Important: also make sure you write suitable docstrings for the modified
function and the program as a whole, to reflect the changed behaviour.
Copy the complete program into your Solution Document. Also include your
completed .py file in your TMA zip file.
Notes
1. You should aim to use only the Python features that are introduced in the
module. If you decide to use techniques or language features that TM112
does not cover you must give a justification for your decisions, or marks
will be lost.
2. You should not make any changes to the program except where indicated.
3. If you are unable to get the program working correctly, you should still copy
your code into your Solution Document and submit your .py file, with a brief
explanation of how the results are different from what you were intended.
iv. Finally, copy the notebook you have kept for this question into the corresponding
part of your Solution Document.
b. Suggest one further small extension or improvement of your own to the modified
flashcard program. Outline what the extension does and briefly say what additional
sub-problem(s) would need to be added to the initial decomposition.
Note that you are only required to describe your further extension and do not need to
implement it in code.
The maximum word count for this part of the question is 150 words, including the
added sub-problem(s).
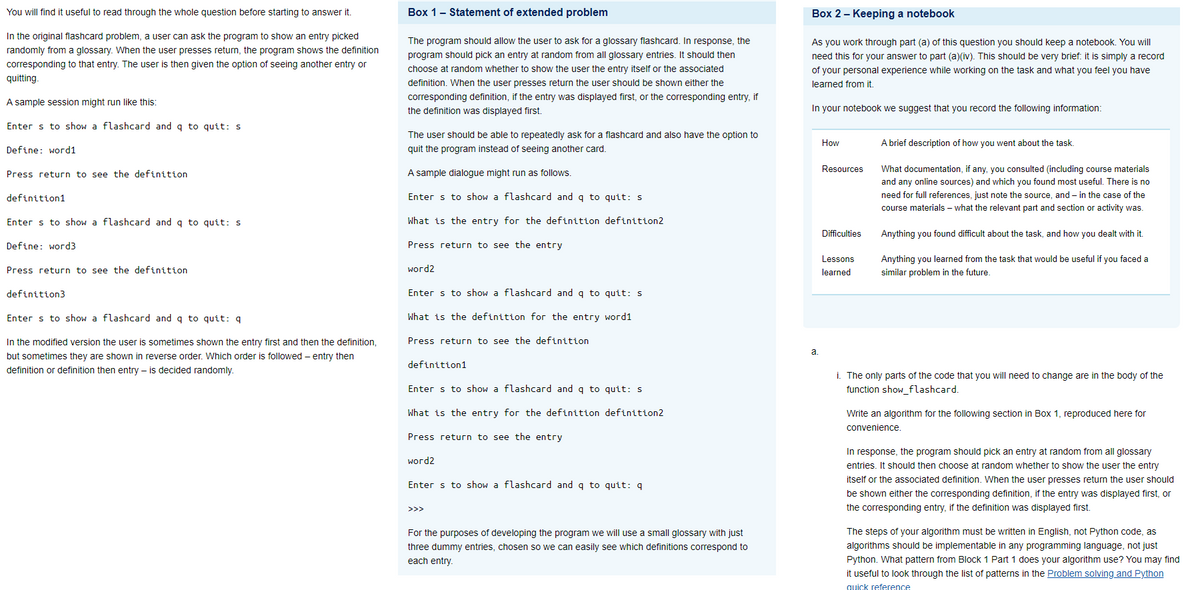
Transcribed Image Text:You will find it useful to read through the whole question before starting to answer it.
In the original flashcard problem, a user can ask the program to show an entry picked
randomly from a glossary. When the user presses return, the program shows the definition
corresponding to that entry. The user is then given the option of seeing another entry or
quitting.
A sample session might run like this:
Enter s to show a flashcard and q to quit: s
Define: word1
Press return to see the definition
definition1
Enter s to show a flashcard and q to quit: s
Define: word3
Press return to see the definition
definition3
Enter s to show a flashcard and q to quit: q
In the modified version the user is sometimes shown the entry first and then the definition,
but sometimes they are shown in reverse order. Which order is followed - entry then
definition or definition then entry is decided randomly.
Box 1 - Statement of extended problem
The program should allow the user to ask for a glossary flashcard. In response, the
program should pick an entry at random from all glossary entries. It should then
choose at random whether to show the user the entry itself or the associated
definition. When the user presses return the user should be shown either the
corresponding definition, if the entry was displayed first, or the corresponding entry, if
the definition was displayed first.
The user should be able to repeatedly ask for a flashcard and also have the option to
quit the program instead of seeing another card.
A sample dialogue might run as follows.
Enter s to show a flashcard and q to quit: s
What is the entry for the definition definition2
Press return to see the entry
word2
Enter s to show a flashcard and q to quit: s
What is the definition for the entry word1
Press return to see the definition
definition1
Enter s to show a flashcard and q to quit: s
What is the entry for the definition definition2
Press return to see the entry
word2
Enter s to show a flashcard and q to quit: q
>>>
For the purposes of developing the program we will use a small glossary with just
three dummy entries, chosen so we can easily see which definitions correspond to
each entry.
Box 2 - Keeping a notebook
As you work through part (a) of this question you should keep a notebook. You will
need this for your answer to part (a)(iv). This should be very brief: it is simply a record
of your personal experience while working on the task and what you feel you have
learned from it.
In your notebook we suggest that you record the following information:
a.
How
Resources
Difficulties
Lessons
learned
A brief description of how you went about the task.
What documentation, if any, you consulted (including course materials
and any online sources) and which you found most useful. There is no
need for full references, just note the source, and in the case of the
course materials - what the relevant part and section or activity was.
Anything you found difficult about the task, and how you dealt with it.
Anything you learned from the task that would be useful if you faced a
similar problem in the future.
i. The only parts of the code that you will need to change are in the body of the
function show_flashcard.
Write an algorithm for the following section in Box 1, reproduced here for
convenience.
In response, the program should pick an entry at random from all glossary
entries. It should then choose at random whether to show the user the entry
itself or the associated definition. When the user presses return the user should
be shown either the corresponding definition, if the entry was displayed first, or
the corresponding entry, if the definition was displayed first.
The steps of your algorithm must be written in English, not Python code, as
algorithms should be implementable in any programming language, not just
Python. What pattern from Block 1 Part 1 does your algorithm use? You may find
it useful to look through the list of patterns in the Problem solving and Python
quick reference
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Database System Concepts
Computer Science
ISBN:
9780078022159
Author:
Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:
McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:
9780134444321
Author:
Tony Gaddis
Publisher:
PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:
9780132737968
Author:
Thomas L. Floyd
Publisher:
PEARSON

Database System Concepts
Computer Science
ISBN:
9780078022159
Author:
Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:
McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:
9780134444321
Author:
Tony Gaddis
Publisher:
PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:
9780132737968
Author:
Thomas L. Floyd
Publisher:
PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:
9780133976892
Author:
Paul J. Deitel, Harvey Deitel
Publisher:
PEARSON

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781337627900
Author:
Carlos Coronel, Steven Morris
Publisher:
Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:
9780073373843
Author:
Frank D. Petruzella
Publisher:
McGraw-Hill Education