Problem 2. Create a PDA that will accept the language { se {a,b}* | s= a^(ba)", n ≥0}. (15) e.g., {s, aba, aababa, aaabababa, ...} Enter the PDA in JFLAP and test it with at least 10 test cases. Include an image of the PDA and the test results. (Note: When creating a PDA in JFLAP, select "Single Character Input". When running tests, select "Accept by Final State".)
Problem 2. Create a PDA that will accept the language { se {a,b}* | s= a^(ba)", n ≥0}. (15) e.g., {s, aba, aababa, aaabababa, ...} Enter the PDA in JFLAP and test it with at least 10 test cases. Include an image of the PDA and the test results. (Note: When creating a PDA in JFLAP, select "Single Character Input". When running tests, select "Accept by Final State".)
Programming Logic & Design Comprehensive
9th Edition
ISBN:9781337669405
Author:FARRELL
Publisher:FARRELL
Chapter2: Elements Of High-quality Programs
Section: Chapter Questions
Problem 9RQ
Related questions
Question
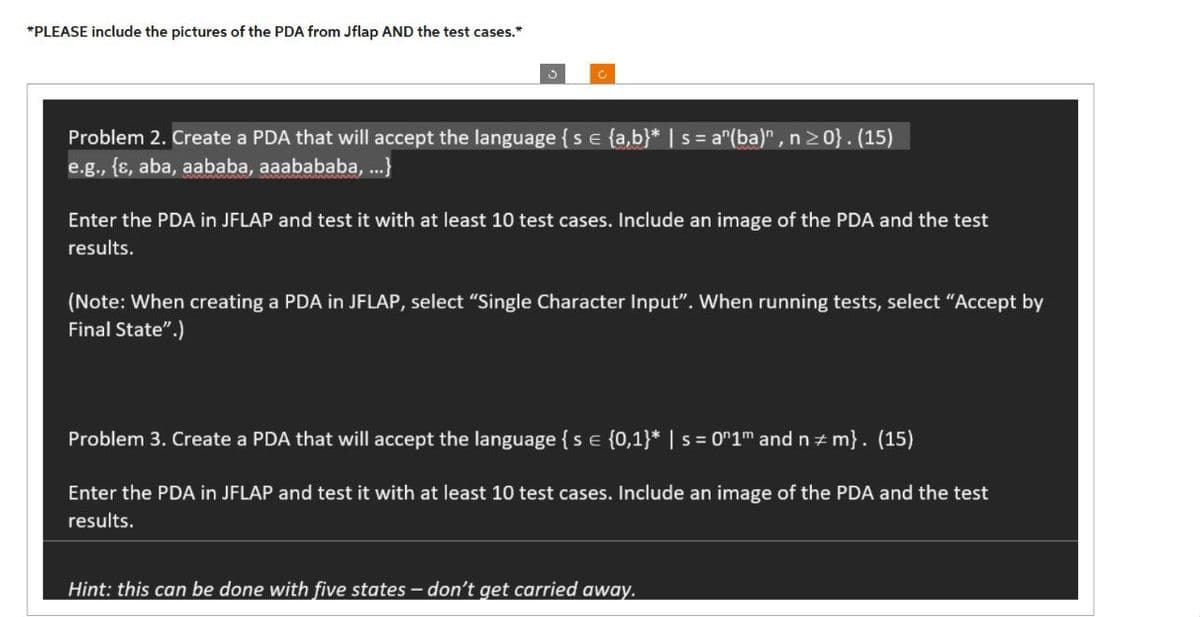
Transcribed Image Text:*PLEASE include the pictures of the PDA from Jflap AND the test cases.*
C
Problem 2. Create a PDA that will accept the language { s = {a,b}* | s = a^(ba)", n ≥0}. (15)
e.g., {s, aba, aababa, aaabababa, ...}
Enter the PDA in JFLAP and test it with at least 10 test cases. Include an image of the PDA and the test
results.
(Note: When creating a PDA in JFLAP, select "Single Character Input". When running tests, select "Accept by
Final State".)
Problem 3. Create a PDA that will accept the language { s = {0,1}* | s = 0″1m and n‡m}. (15)
Enter the PDA in JFLAP and test it with at least 10 test cases. Include an image of the PDA and the test
results.
Hint: this can be done with five states – don't get carried away.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage