Python programming Provide 3 examples of python programming using try-except statement and/or traceback
Python programming Provide 3 examples of python programming using try-except statement and/or traceback
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter10: Pointers
Section10.1: Addresses And Pointers
Problem 5E
Related questions
Question
100%
Python
Provide 3 examples of python programming using try-except statement and/or traceback
Thank you!
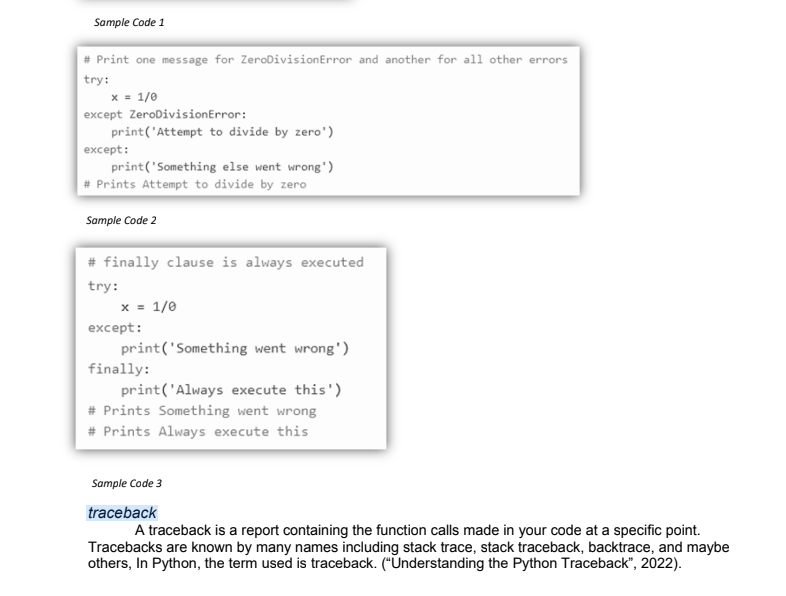
Transcribed Image Text:Sample Code 1
# Print one message for ZeroDivision Error and another for all other errors
try:
x = 1/0
except ZeroDivisionError:
except:
print('Attempt to divide by zero')
print('Something else went wrong')
# Prints Attempt to divide by zero
Sample Code 2
# finally clause is always executed
try:
x = 1/0
except:
print('Something went wrong')
finally:
print('Always execute this')
# Prints Something went wrong
# Prints Always execute this
Sample Code 3
traceback
A traceback is a report containing the function calls made in your code at a specific point.
Tracebacks are known by many names including stack trace, stack traceback, backtrace, and maybe
others, In Python, the term used is traceback. ("Understanding the Python Traceback", 2022).
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 5 steps with 8 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,
