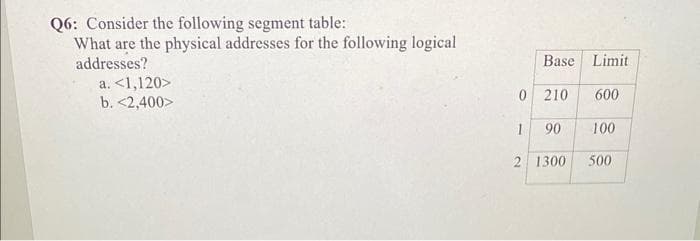
Q6: Consider the following segment table: What are the physical addresses for the following logical addresses? a. <1,120> b. <2,400> Base Limit 0 210 1 90 2 1300 600 100 500
Q: Note: ILLUSTRATE a. Illustrate vector addition using head-to-tail and parallelogram method. b.…
A: a).
Q: What considerations led to the decision to mandate that system developers use an object-oriented…
A: As we know, according to the requirement the software project can be small and complex and sometimes…
Q: Compare the performance of write operations achieved by a RAID Level 5 organization with that…
A: RAID Level 1 RAID 1 offers slower write speeds but could offer the same read performance as RAID 0…
Q: (a) The CPU computations and I/O operations cannot be overlapped in a multipro- grammed computer.…
A: The question is to find the given statements are true of false.
Q: I have a python task using pandas library, i have a dataframe df, list[], *** I want to count list…
A: You can use method mention below:
Q: How do cohesion and coupling affect software development
A: Introduction The complexity of the interface, which is where the passage or reference to the module…
Q: you have a particular design in mind that you'd want to talk about?
A: Introduction: A repeatable design pattern for software engineering response to a frequent problem in…
Q: what is the utilization of Pseudocode in programming.
A: Introduction: Pseudocode is organized English for portraying algorithms compactly. It is comprised…
Q: Exactly exactly do we mean when we state that requirements should be exhaustive and uniform?
A: During the requirement analysis phase of project development, a critical issue is raised. A useful…
Q: Why should I consider using an automated server software installation and configuration tool? In…
A: Given - What benefits can automated server provisioning and configuration offer? What negative…
Q: It is important to emphasize "divide and conquer," a fundamental tenet of software engineering…
A: Introduction: When people think about software engineering, they typically picture complex…
Q: Explain the function of scrambling in the context of digital-to-digital encoding techniques.
A: Answer : If we have a long binary data which includes large no of 1 and 0 so that make the data more…
Q: What perspectives should be taken into software-intensive systems?
A: Definition: In Our daily lives depend on complex software-intensive systems from banking to…
Q: Cryptocurrencies and the blockchain are currently very hip. Outline the impact of blockchain…
A: Introduction: A blockchain is a decentralized ledger that records all transactions within a group.…
Q: Answer the following questions about the MasPar MP-1: (a) Explain the X-Net mesh interconnect (the…
A: Here's the solution:
Q: What is the correct DOM method to update the src attribute value of the HTML img element. Please…
A: The textContent property alters or retrieves the text content for the specified node and all of its…
Q: Are there any potential pitfalls for an OS whose design allows for several threads to run…
A: Answer : OS has many pitfalls for using several threads design process which run simultaneously : As…
Q: Exactly exactly do we mean when we state that requirements should be exhaustive and uniform?
A: An elementary inquiry about the requirement analysis stage of project development has been posed to…
Q: How many distinct types of addressing exist in a computer network?
A: The issue is rooted in the fundamental OSI model layers. There are four potential forms of…
Q: Why have object-oriented techniques taken off with the systems developer community?
A: A computer programming paradigm known as object-oriented programming (OOP) arranges the architecture…
Q: When it comes to code, what role do Design Patterns play, and how exactly do they function? Explain…
A: The answer is given in the below step
Q: Architecture's advantages include... Compare a project with and without architecture. How will it…
A: Project-planning for softwareA software project is an extensive series of programming tasks.…
Q: Pick a domain where an expert system might serve as a helper, give at least five rules for the…
A: Solution: The main purpose of Expert System is to replicate knowledge and skills of human experts in…
Q: It's important to understand exactly what is meant by the word "consideration." What does this mean…
A: Here's the solution: Critical Concern Consideration is multifaceted.Consider past, current, and…
Q: It's important to think about what this phrase means. What do you think about this from the…
A: The same is true for software: it's simple to learn how to hack away at an issue, but creating a…
Q: It is important to emphasize "divide and conquer," a fundamental tenet of software engineering…
A: When considering software engineering, people often think about compound instructions, algorithms,…
Q: Explain the following terms associated with compound vector processing: (a) Compound vector…
A: The question is to explain the given terms related to vector processing.
Q: Define a situation where magnetic stripe cards are insufficient for authentication and smart cards…
A: A tiny microprocessor embedded in the smart card, which is comparable in size to a credit card or…
Q: Pick a domain where an expert system might serve as a helper, give at least five rules for the…
A: Areas where expert systems may assist:Medical diagnosis (using the patient's symptoms as the query,…
Q: Q1) write a program to find the summation of 10 elemnets array. if the sum even, creas the array…
A: Find Your Answer Below
Q: How about listing three options for minimizing your time spent sitting in traffic? How do you tell…
A: The meaning of minimise: transient verb. Minimize expenditures and delays by reducing or keeping to…
Q: Why should I consider using an automated server software installation and configuration tool? In…
A: Introduction: Given – What advantages might automated provisioning and setup of servers provide?…
Q: What is the type of the object of the evt function parameter in the following JavaScript code.…
A: Introduction: In this question, an event listener is given and we have to choose the correct…
Q: A company has two locations: a headquarters and a tactory about 25 km away. Inc factory has four…
A: It would be simple to multiplex the four terminals onto a single voice grade line. Since only one…
Q: Can anbody help me with this?
A: Code:- A=[1 2 2;3 4 5;6 7 8];[u ,s ,v] = svd(A);k = 1;A1 = u(:,1:k)*s(1:k,1:k)*v(:,1:k)'; %'//…
Q: Give some examples of the main pluses of the client/server architectural approach.
A: Client/Server Architectural Approach: Client-server architecture often consists of workstations,…
Q: It's important to think about what this phrase means. What do you think about this from the…
A: Given: So, what is Critical Concern Consideration may manifest itself in a variety of ways. Factors…
Q: Where does Model-View-Controller fit into the bigger picture of what makes up modern online…
A: Answer : Car driving mechanism is responsible or working on Model view controller. That basically…
Q: So, what is SETI, and how does it benefit from the idea of distributed computing?
A: Institution: SETI, or the Search for Extraterrestrial Intelligence, is a scientific term. SETI is…
Q: It's important to think about what this phrase means. What do you think about this from the…
A: The same is true for software: it's simple to learn by hacking away at a problem, but turning it…
Q: What kinds of governance issues arise when migrating from in-house servers to an IaaS-based…
A: Introduction: IaaS is a cloud service where a cloud service provider (CSP) leases out highly…
Q: In what ways do fat-client and thin-client architectures vary from one another?
A:
Q: Cryptocurrencies and the blockchain are currently very hip. Outline the impact of blockchain…
A: A blockchain is a distributed ledger of all group transactions. Members can confirm transactions…
Q: Which considerations, and how they should be made, are most important when modeling…
A: Software-intensive systems: A software-intensive system is one that relies heavily on software.…
Q: Doesn't this part need a brief overview of the two features generally agreed upon as the most…
A: Introduction: running system: A piece of software is called an operating system. controls and runs…
Q: Where should you look for governance problems when migrating your IT infrastructure to the cloud?
A: Due to that What are some of the governance issues to be on the lookout for a while switching from…
Q: Can you describe the operating system and provide an example of how it works?
A: An operating system’s (OS) is pieces of softwares that connects a user's computer’s to it’s…
Q: When it comes to software development, what role do design patterns play? Do you have a particular…
A: In software engineering, a design pattern is a general solution to a problem in software design that…
Q: How many distinct types of addressing exist in a computer network?
A: Computer networking is linking various computers so they can talk with one another and share…
Q: The interns who appear to be violating numerous security rules are approached by the CISO and…
A: Definition: Security is one of the most crucial components for many organisations. Every…
Step by step
Solved in 2 steps

- Consider the following segment table:Segment Base Length Base Limit0 1200 5001 2200 10242 6400 2563 8000 700What are the physical addresses for the following logical addresses?a. 2, 250b. 3, 690c. 0, 515Consider the following segment table: Segment Segment (Base) Length (Limit) 0 319 560 1 3200 14 2 89 95 3 1330 600 What are the physical addresses for the following logical addresses? Segment Offset a 0 430 b 1 10 c 2 500 d 3 400Check the following schedules, whether they are conflict serializable? S1: R1(X); W1(X); R2(X); R1(Y); W1(Y); R2(Y) S2: R1(X); W1(X); R2(X); R2(Y); R1(Y); W1(Y)
- Q) An ISP is granted a block of addresses starting with 150.80.0.0/16. The ISP wants to distribute these blocks to 2600 customers as follows; a) The first group has 200 medium-size businesses; each needs 128 addresses.b) The second group has 400 small businesses; each needs 16 addresses.c) The third group has 2000 households; each needs 4 addresses. Design the sub-blocks and give the slash notation for each sub-block. Find out how many addresses are still available after these allocations.Briefly explain extended destination indexIn the RENTALS table shown in fig 2, 40 customers have created 50 rental contracts over time. A RENTALS record is 122 bytes and the block size for your OS is set to 1024 bytes with each block having a 1 byte pointer to the next written block as well as a 1 byte pointer to the next physically consecutive block. Calculate the blocking factor for unspanned blocking of RENTALS records. a)4 b)400 c)320 d)8
- Consider the following segment table: What are the physical address for the following logical address? a) 0,826 b) 1,269 c) 2,8 d) 3,700 e) 4,138 Segment Base (Starting Address) Length (bytes) 0 103 529 1 20 264 2 909 9 3 1974 980 4 7929 176Consider the following segment table (all expressed and addressed in bytes) Segment Base Length 0 500 1000 1 4500 1500 2 7000 3000 3 11000 2400 4 15000 875 What are the physical addresses for the following logical addresses? a. 0,430 b. 1,1520 c. 2,500 d. 3,400 e. 4,1120Determine the first 4 subnets and usable address range of the following and submit your table on Canvas. 192.168.200.0/24 for 58 addresses 172.16.10.0/24 for 28 addresses 10.10.10.0/24 for 100 addresses 209.165.200.0/24 for 10 addresses
- An ISP is granted a block of addresses starting with 129.80.0.0/16. The ISP wants to distribute these blocks to 2600 groups as follows: i. The first group has 200 medium sized businesses; each needs 14 hosts. ii. The second group has 400 small businesses; each needs 6 hosts. iii. The third group has 2000 point-to-point links; each needs 2 hosts. iv. Design the sub-blocks and give the slash notation for each sub-blockAn ISP is granted a block of addresses starting with 10.100.10.0/16.The ISP needs to distribute these addresses to three groups ofcustomers as follows:. The first group has 64 customers; each needs 128 addresses.. The second group has 128 customers; each needs 128 addresses.. The third group has 128 customers; each needs 32 addresses.. Design the sub blocks and find out how many addresses are still available after these allocation.How are logical and linear addresses related to one another, and what are their differences?

