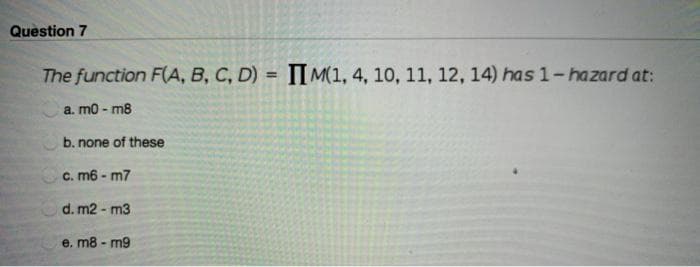
Question 7 The function F(A, B, C, D) = IIM(1, 4, 10, 11, 12, 14) has 1-hazard at: a. m0-m8 b. none of these c. m6 - m7 d. m2 - m3 e. m8-m9
Q: In terms of strategy, does legacy system development have a future? When should the entire system be…
A: Intro An estate plan is a procedure that is planned, carried out, and used in a totally distinct…
Q: What are some examples of actions that could be utilized in software development to anticipate…
A: Here are some examples of actions used during software development to anticipate change and make…
Q: It is important to emphasize "divide and conquer," a fundamental tenet of software engineering…
A: When considering software engineering, people often think about compound instructions, algorithms,…
Q: 5- The assignment model is a special case of the transportation model in which the number of origin…
A: The assignment model is a special case of the transportation model in which the number of origin…
Q: 172.16.0.0 (class B IP address) into four subnets
A: The answer is
Q: Consider a two-link network where Host A is connected to the router by a 1 Mbps link with 10 ms…
A: Transmission Delay: The amount of time needed to send each bit of the packet onto the outgoing link…
Q: When transitioning from on-premises servers to an IaaS-based architecture, what sorts of governance…
A: Over the past three years, the Cloud Security Alliance has attracted around 120 corporate members…
Q: Redefining the withdraw method in the Checking Account class is an example Of ---- Give explanation…
A: Introduction In this question, we are asked to fill the gap of this “Redefining the withdrawal…
Q: D-AMPS has appreciably worse speech quality than GSM. Is this due to the requirement that D-AMPS be…
A: The question has been answered in step2
Q: When it comes to software development, what role do design patterns play? Do you have a particular…
A: Introduction: A reusable response to a typical problem in software design is a software engineering…
Q: Why is a computer's read-only memory (ROM) preprogrammed before it is ever built?
A: Given that, how does the production-time-programmed ROM memory function? "Read-only memory" refers…
Q: Discuss the strengths and weaknesses of implementing an access matrix using access lists that are…
A: Answer: We need to write the strength an weakness of implementation the access the matrix using…
Q: Demonstrate by example (write down a few dozen arbitrary bit patterns; assume one start bit and a…
A:
Q: Just what are the upsides of adopting design patterns in software development? What are three…
A: Definition: In software development, a design pattern is a general, reusable solution to a frequent…
Q: algorithm for finding all occurrences of a sequence in another sequence using the suffix array of…
A: Algorithm which refers to the algorithm that contains the set of the rules or the instruction that…
Q: Where does Model-View-Controller fit into the bigger picture of what makes up modern online…
A: MVC is an architectural paradigm that divides an application into three fundamental logical…
Q: D-AMPS has appreciably worse speech quality than GSM. Is this due to the requirement that D-AMPS be…
A: The question has been answered in step2
Q: Describe the steps involved in putting a finite-state machine under control.
A: Introduction: A finite automaton (FSA, plural: automata), finite an automaton, or simply a state…
Q: give an instance of how virtual servers are used in a learning environment
A: in the following section we will be discussing about an instance of how virtual servers are used…
Q: Create an IP address plan as efficiently as possible for the network shown below. The address space…
A: Given IP address is 192.168.10.0/25 Network A requires 50 addresses and network B requires…
Q: Exactly exactly do we mean when we state that requirements should be exhaustive and uniform?
A: During the requirement analysis phase of project development, a critical issue is raised. A useful…
Q: Suppose that a sender and receiver use asynchronous transmission and agree not to use any stop…
A: Synchronous transmission Synchronous transmission modes are utilized when a lot of information…
Q: Suppose that a selective-reject ARQ is used where W = 4. Show, by example, that a 3-bit sequence…
A: Answer:
Q: When it comes to code, what role do Design Patterns play, and how exactly do they function? Explain…
A: Introduction: A comprehensive, repeatable solution to a typical software design issue is a software…
Q: I'm interested in the definition of the phrase "essential consideration." What do you think of this…
A: In many cases, the important: Area is the part of the code that grants you access to the collective…
Q: If you can, give an instance of how virtual servers are used in a learning environment.
A: Electronic server: In contrast to a dedicated servers, a virtual server collaborates with other…
Q: What was the primary inspiration for the creation of computer languages?
A: Programming Language Evolution The essential building block of the modern IT world is, in fact, a…
Q: When and why were computer programming languages developed?
A: Computer language programming: Programming language or any of the different languages used to…
Q: Consider a two-link network where Host A is connected to the router by a 1 Mbps link with 10 ms…
A: The answer is given in the below step
Q: What does the acronym NFA (Nondeterministic Finite Automata) mean?
A: Introduction: A non-deterministic algorithm is the execution of concurrent algorithms with race…
Q: What do low-level programming languages serve? What distinguishes them from one another?
A: Introduction: Programming languages written at the most basic levelLow-level languages are ones that…
Q: What prerequisites must one meet in order to pursue computer science?
A: Computer science is the discipline that investigates computers, algorithms, computational systems,…
Q: Give a thorough description of the main contrasts between procedural and object-oriented programming…
A: Answer:
Q: Although they are not interchangeable, RAM and Register are both types of memory.
A: The answer of the question is given below:
Q: Although they are not interchangeable, RAM and Register are both types of memory.
A: Register: 1) Registers are the memory that is readily accessible to the CPU. These are tiny memory…
Q: How fast can a cable user receive data if the network is otherwise idle?
A: The answer of the question is given below:
Q: What was the primary inspiration for the creation of computer languages?
A: Answer:
Q: Discuss the reasons why the operating system might require accurate information on how blocks are…
A:
Q: How fast can a cable user receive data if the network is otherwise idle?
A: Given: An Ethernet cable is a kind of connection used to link computers in order to facilitate…
Q: Compare the throughput achieved by a RAID Level 5 organization with that achieved by a RAID Level 1…
A: Answer - RAID 1 stands for Redundant Array of Independent Disk Level 1. RAID 5 stands for Redundant…
Q: What is meant by "Critical Consideration"? Is this also true for the development of software?
A: Consideration may appear in a multitude of forms. Past, present, and future factors may all be taken…
Q: What are the best solutions for developing legacy systems? When would it be more prudent to replace…
A: The Answer start from step-2.
Q: Discuss the relative advantages and disadvantages of sector sparing and sector slipping.
A: Due to the additional time: Needed to perform the track transition and rotation, sector sparing…
Q: Discuss the strengths and weaknesses of implementing an access matrix using capabilities that are…
A: The strengths and weaknesses of implementing an access matrix using capabilities that are associated…
Q: Why have object-oriented techniques taken off with the systems developer community?
A: The following reasons have made it necessary for system engineers to employ an object-oriented…
Q: How fast can a cable user receive data if the network is otherwise idle?
A: Given: An Ethernet cable is a kind of connection used to link computers in order to facilitate…
Q: Exactly exactly do we mean when we state that requirements should be exhaustive and uniform?
A: Introduction: Completeness refers to instances when a specification involves all that is known to be…
Q: Are there any steps other than prototyping and incremental delivery that can be used during the…
A: The programme will always need to be updated: More and more people are using cutting-edge gadgets…
Q: computers have very amazing power. Is there any proof that computers have been widely used in…
A: SummaryThere are many ways to measure computer performance – and each one produces slightly…
Q: Redefining the withdraw method in the Checking Account class is an example Of Give explanation of…
A: Answer- Method overriding
Step by step
Solved in 2 steps with 1 images

- Simplify the following Boolean functions using four-variable K-maps: C: F(w,x,y,z)=sum (1,3,4,5,6,7,9,11,13,15)1. Determine the determinant and Solve for Value of w, x, y, z Given: w – 12x +13y – 7z = 232w + 15x + 16y + 12z = 19 4w – 10x + y + 17z = 24 3w + 2x – 3y + 2z = 14*THIS IS MATLABGiven four 2D points a0, a1, b0, and b1, design a robust procedure to determine whether the line segments a0a1 and b0b1 intersect.
- draw the kmap and find the POS and SOP of the following minterms: F(V,W,X,Y,Z) = Σm(0,2,4,6,7,8,10,11,12,13,14,16,18,19,29,30)Using Kmaps, determine all the minimal sums and minimal products for the following functions: F(w,x,y,z) = ∑m(6,7,9,10,13) + dc(1,4,5,11,15) F(w,x,y,z) = ∑m(1,2,3,4,6,9,12,14)+dc(5,7,15) F(w,x,y,z) = ∏M(0,2,3,5,6,9,10,11,13) F(w,x,y,z) = wx + y’z + wx’y’ + w’xyz F(w,x,y,z) = (w+x’)(w+y+z)(w’+x’+z’)(w+y’+z)(3a) Compute the stability function S of the Rosenbrock method (108), that is, compute the (rational) function S(z), such that y1 = S(z)y0, z ∶= hλ, when we apply the method to perform one step of size h, starting from y0, of the linear scalar model ODE y˙ = λy, λ ∈ C
- Please explain, as simplistically (but thoroughly) as possible, how to develop a k-map from a truth table to be used to simplify an equation.Examples: xz + (xy + ~z) ~xyz + yz + x~yneed proper solution with complate explainationSimplify the following Boolean functions, using K-maps: F (A, B, C, D)=?(1,3,6,9,11,12,14)
- In each case below, show using the pumping lemma that the givenlanguage is not a CFL.e. L = {x ∈ {a, b, c}∗ | na(x) = max {nb(x), nc(x)}}Here is the Berkeley Madonna code: {Top model} {Reservoirs} d/dt (Q) = + Stimulus - Imemb INIT Q = -65/cap {Flows} Stimulus = Intensity*SquarePulse(3,.5) {at t=3 of 0.5 duration} Imemb = IL+IK+INa {Functions} Intensity = 100 {microamps} cap = 1 E = Q/cap {Submodel "INa_"} {Functions} ENa = 50 INa = gNa*(E-ENa) GNaMax = 120 gNa = GNaMax*m*m*m*h {Submodel "m_gates"} {Reservoirs} d/dt (m) = + m_prod - m_decay INIT m = am/(am+bm) {Flows} m_prod = am*(1-m) m_decay = bm*m {Functions} am = 0.1*(E+40)/(1-exp(-(E+40)/10)) bm = 4*exp(-(E+65)/18) {Submodel "h_gates"} {Reservoirs} d/dt (h) = + h_prod - h_decay INIT h = ah/(ah+bh) {Flows} h_prod = ah*(1-h) h_decay = bh*h {Functions} ah = 0.07*exp(-(E+65)/20) bh =…Simplify the following Boolean functions, using Karnaugh maps: a. ?(?, ?, ?,?) = ∑(1,5,9,12,13,15)

