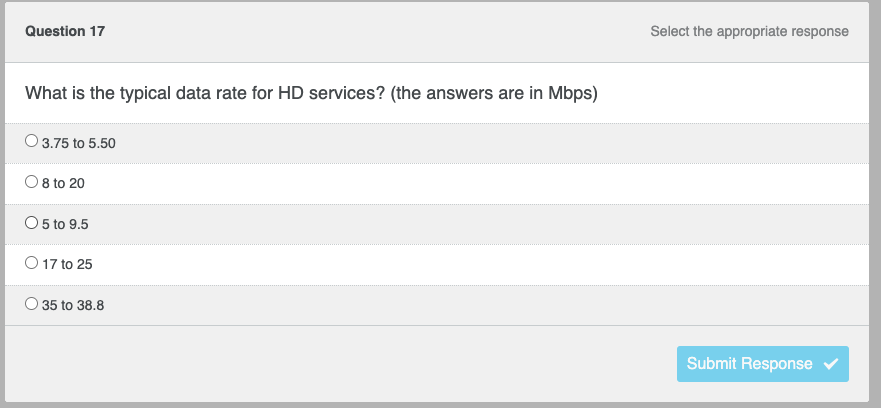
What is the typical data rate for HD services? (the answers are in Mbps)
Q: Why is it rewarding to work in Cybersecurity?
A: It is rewarding to work in Cybersecurity the reason is as follows.
Q: A) Add these two number AD45H and 98FCH. *
A: Below is the answer to above question. I hope this will be helpful for you..
Q: There are various selection structures that can be used in programming. What are the different…
A:
Q: Discussion on limitations and constraints on the use of springs ( Minimum 05), and corrective…
A: In the electrical designing and electrical industry, specialized springs, for example, Leaf springs…
Q: A multitude of ways are used to communicate input and output in computer systems, such as:
A: A multitude of ways are used to communicate input and output in computer systems, such as: Direct…
Q: Why is software quality crucial from a commercial standpoint?
A: Introduction: A perfect, top-notch software with problems can boost the company's trust and…
Q: Hey, so would i have to make three seperate java files labeled in order EncryptorOne EncryptorTwo…
A: Apart of this file you need one extra file for abstract class Encryptor also in a file. Files in…
Q: Explore the differences and similarities between Ubuntu and other Linux distributions. My point of…
A: An Linux is a one type of open source and unix operating system like operating systems and it also…
Q: An international round table conference will be held in india. Presidents from all over the world…
A: Since the programming language is not mentioned, I have done the code using Java.
Q: What security holes are used if someone does something on purpose to break a computer, and how will…
A: a vulnerability is a security weakness in a computer system that permits unauthorized or unwelcome…
Q: RAID-capable storage makes Oracle database backups obsolete in the modern world. Avoid writing with…
A: RAID(Robust Array of Inexpensive Disks), is a logical method for combining several discs into a…
Q: Utilizing cloud computing in financial systems raises security and other risks.
A: Risks of cloud computing in financial systems are: 1. restricted visibility into network operations…
Q: Comparison of online vs batch data input methods is necessary. Source data automation is shown.
A: Processing in batches is less expensive than accepting input online. The preparation of a batch of…
Q: Flynn's taxonomy should be increased by one level. At this level, what distinguishes computers?
A: INTRODUCTION: Flynn's scientific classification may be a classification of computer structures,…
Q: What advantages does RAID technology offer? What is the purpose of RAID's many tiers?
A: What is RAID technology? RAID stands for Redundant Array of Independent Disks and combines multiple…
Q: What is the difference between OCR and OMR (Optical mark recognition)?
A: The solution to the given question is: Basis for comparison OMR OCR Stands for Optical Mark…
Q: . Write a Java program to test if an array contains a specific value.
A: To write a Java program to test if an array contains a specific value.
Q: xplain why an inside attacker/hacker may be harmful to a firm in one paragraph. What may happen???…
A: A hacker is a person who use computer, networking, or other skills to solve a technological issue.…
Q: How were usability and user experience metrics utilised and distributed throughout the evaluation?
A: Introduction :- In software's developments, the quality of programmes is a significant element's.…
Q: Write a python program that accepts a string as input and removes characters from the string which…
A:
Q: Please provide further information on the concerns that may arise from the usage of cloud computing.…
A: When people talk about "cloud computing," they refer to a network of servers connected over the…
Q: 2. convert the following negative numbers to binary numbers using the complement techniques. 2nd…
A: One's Complement 0011 0000 Number in 8-bit representation: Decimal-49 Binary1100 1111…
Q: 1. Convert from decimal number to binary number (-20.75)10- Your answer 2. Convert from Hexadecimal…
A: As I have read the guidelines I can provide answers to only 2 parts of the questions in case of…
Q: A conceptual framework for understanding cybercrime is being developed. It would be helpful if you…
A: Any criminal activity carried out via a computer, social media, or another form of technology is…
Q: Everything from DNS records to authoritative vs. root servers to iterated vs. non-iterated queries…
A: DNS records to authoritative vs. root servers to iterated vs. non-iterated queries is described in…
Q: AWS S3 guarantees how much durability and availability?
A: Amazon S3 is a thing storage organization that offers industry-driving adaptability, data…
Q: In your opinion, what are the most critical characteristics of high-quality software?
A: Introduction: The CISQ has determined five essential structural qualities that must be present for…
Q: When designing a software system, list and explain all of the tasks that must be completed.
A: The question is "when designing a software system, list and explain all of the tasks that must be…
Q: When it comes to computer architecture, what is the difference between Harvard and von Neumann?
A: The Answer start from step-2.
Q: How do you define a green computer
A: Green computing is described as the study and use of information technology with the intention of…
Q: Cloud computing has a lot of security flaws that must be taken into consideration.
A: Given: Cloud security should be discussed at every level of an organization, from the top down to…
Q: Hi really need help with this 8 assignment Oracle 12c: SQL Chapter 8 Question 3 and 5. 3. List the…
A: An query is a solicitation for information or data from a data set table or mix of tables. This…
Q: is properly to ensure autoencoder trained to compare two outputs and inputs. they must be similiar…
A: To check if an autoencoder has been appropriately trained, visualise the reconstructions and compare…
Q: How is the process of identity and authorization handled in cloud computing?
A: The Answer start from step-2.
Q: Determine whether the use of the cloud poses a security risk. What are the chances that they'll be…
A: Introduction: As a result of the proliferation of cloud computing, there has been a dramatic shift…
Q: The fetch-execute increment the cycle can be simply described by the following algorithm: the…
A: The fetch execute cycle was first proposed by John von Neumann. The cycle is the order of steps that…
Q: I'd want to know more about the Apps packages. Tell us everything about it in detail Identify at…
A: Start: A signed Android App Bundle that can be submitted to Google Play has been produced by Android…
Q: What issues with your company's information system should you be aware of, and what steps should you…
A: What issues with your company's information system should you be aware of, and what steps should you…
Q: write a Python program that should accept a word with maximum length of 25. A sentence is given,…
A: #reading sentence word by words=""#to store sentencewhile True:#runs until a word with upper case…
Q: C++ One way to create a pseudo-random three digit number (and we are including one- and two-digit…
A: Code: #include <iostream>#include <cstdlib>#include <ctime>using namespace std;…
Q: I wish to find out which of these methods was used to answer my question above. 1. training…
A: I wish to find out which of these methods was used to answer my question above. 1. training…
Q: Write the function calcWordFrequencies() in script.js that uses the JavaScript prompt() function to…
A: Coded using Javascript.
Q: What are the options for cloud backup? Where can I find a place to store my data for free on the…
A: Cloud backup is the process of creating a backup of specific data and putting it away in a cloud…
Q: In Microsoft office word program, how -can you insert a table?1 In Microsoft office word program,…
A: 1. In Microsoft office word program, the steps to insert a table are: Open Microsoft office word…
Q: Task 10: List all the tables contained within the system catalog, but only display the first 10…
A: If the database name is PetSuppliers Task 10: Query: SHOW FULL TABLES IN PetSuppliers WHERE…
Q: C++ Create a function set(v, i, j) that makes vector v contain the integers i through j. The…
A: Code: #include <iostream>#include <vector>using namespace std; void…
Q: and a value which you (function may be needs function that take an array want to find in the array.…
A: Please check the step 2, 3 & 4 for solution
Q: The execution of a machine code program on a von Neumann architecture computer occurs in a process…
A: The given question are fill in the blank questions.
Q: propagation delay and the router is connected to Host B by a 15 Mbps link with a 25 ms propagat Host…
A: The answer is
Q: All the following are advantages of Mesh except: O a. The topology is robust. O b. Each connection…
A:
Step by step
Solved in 2 steps

- a. Discuss the advantages and disadvantages of each of the following transmission media, in terms of cost, political impact, ease of installation and adaptability in providing a range of services to clients. i. Coaxial ii. Twisted pair iii. Optical fiber ii. What problem with data transmission in broadband coaxial cable networks is addressed using frequency splitting b. Define the role of a firewall and draw a diagram that shows where a firewall should be positioned with relation to protecting a local network i. How can a firewall prevent external attacks on the network and control traffic flow through the firewall c. Discuss the hierarchy and addressing issues surrounding the construction of large networks i. Comment on the current status of IPv6 in this context Identify the major emerging problems for IPv4 and discuss how they are addressed in IPv6 ii. Explain using an example, how bit stuffing is used to preserve frame boundaries when transmitting binary data at the…Assume you urgently need to transfer 40 Gigabytes of data from Los Angeles to New York City. For data transfer, you have a 500 kilobit dedicated connection. Would you prefer to transfer the data over this connection, or will you take it yourself to New York? Describe your answer.COMPUTER NETWORKS, PLEASE ANSWER IT IF YOU ARE EXPERT ON THIS TOPIC. 100 stations use a wireless communications channel bandwidth of 1 MHz, in band 400MHz-401MHz. * Assuming all 100 stations use FDM (Frequency Division Multiplexing), what is the usual bandwidth allocation for each station? * Assuming all 100 stations use CDMA (Code Division Multiple Access), what is the usual bandwidth allocation for each station?
- Discuss the concept of bandwidth in the context of transmission media. How does the choice of transmission media impact available bandwidth and data transfer rates?Discuss the importance of bandwidth in data transmission. How does the choice of transmission medium affect the available bandwidth?18.a. What's the transceiver optical budget in a 100Base-FX Ethernet network?A. –20 dBmB. 11 dBC. –31 dBmD. 17 dB 18.b. How far can cable links span in the ring portion of an FDDI network?A. 300 kmB. 20 kmC. 200 kmD. 100 km
- Suppose you would like to urgently deliver 50 terabytes data fromBoston to Los Angeles. You have available a 100 Mbps dedicated link for datatransfer. Would you prefer to transmit the data via this link or instead use FedExover-night delivery? Explain1- Difference between CSMA/CD and CSMA/CA. 2- Differentiate CDMA, TDMA and FDMA? 3 - In what ways IPv6 better than IPv4?The throughput of the link between the core switch and an employee laptop with 268,535,446 bits of data transmitted through a link in 1,810.80 seconds was calculated by an Omantel network engineer. Using the example above, respond to the following questions: Describe the principle of effective bandwidth.
- What is the significance of the "cable pinout" in computer connections? Provide examples of how different pinouts can affect data transfer.I need a comparative table of 100BaseT, 1000BaseT, 1000BaseL.X, 1000BaseS.X, 100GBaseT, 10GBaseLR, discussing topology, cable, transfer speed, access method and a possible commercial use of eachSubject: Data Communication Networks Thanks in advance for your quick response! Question 4: An image is 800 × 600 pixels with 2 bytes/pixel. Assume the image is How long does it take to transmit it over a 56-kbps modem channel? If the bandwidth of a spectrum band ranges from 106to 109Hz, what is the corresponding wavelength range? 3. A client-server system uses a satellite network, with the satellite at a height of 35,000 km. What is the best-case delay in response to a request?







