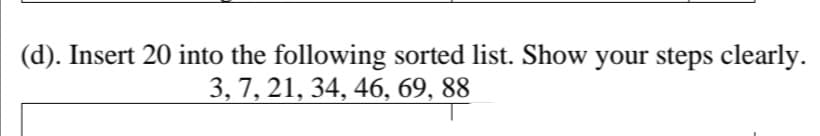
). Insert 20 into the following sorted list. Show your steps clearly. 3, 7, 21, 34, 46, 69, 88
Q: CODE USING C++ 2. A, e, i, o, u? by CodeChum Admin We've had enough about numbers, so why don’t we...
A: Code :- #include <iostream>using namespace std; int main(){ char character; char str[5]; ...
Q: 1).. ...reliable transport between sending and receiving process (TCP, UDP) 2) does not provide flow...
A: TCP (Transmission Control Protocol): It is used to decide how a particular PC ought to be connected ...
Q: 1-How can the CPU recognize the device requesting an interrupt ? 2-Since different devices are likel...
A: The CPU has numerous interrupt lines, and if you need more than that, there's a "interrupt controlle...
Q: How would you test the reliability of a network connection? 2. Why is it important to categorized N...
A: Given To know about the 1) Test the reliability of a network connection 2) Important to categoriz...
Q: Computer science Why is it that TCP can only be used on endpoint devices?
A: Introduction Why is it that TCP can only be used on endpoint devices?
Q: Computer Science I need to write an Assembler program in Matlab that translates programs written in...
A: I have answered this question in step 2.
Q: what are the Advantages of Present technology -UHDTV - HI-DEF Video Recorder -Compact Ultraportab...
A: The advantages of present technology of the following devices are
Q: III. The figure below shows synchronous TDM, the data rate for each input connection is 1 Mbps. If 1...
A:
Q: Using Java Eclipse IDE Create gui like this Frame Java Swing or jframe
A: Explanation: I have provided an explanation within the code in the comment. Code run successfully a...
Q: The specifications of a GPON network of 20 km single mode fibre (SMF) with three connectors and a 1:...
A: Below is the answer to above question. I hope this will meet your requirements....
Q: unsorted array = 18 21 13 5 14 8 21 19 5 14 Now use any Divide and Conquer algorithm to find the sm...
A: I give the code in Python along with output and code screenshot
Q: create a circle using javafx , count how many times the circle is being clicked and change its color...
A: Create a javafx code Create a circle Count how many times circle clicked. Change the color When clic...
Q: msh7.c can be terminated with exit , but msh8.c cannot. Is this true? Yes! No!
A: No
Q: Write, compile and test a program that displays the following patterns on the screen b) 1 12 a) *** ...
A: I have answered this question in step 2.
Q: 1. Describe how the arguments are used in the following code: def display_sta...
A: EXPLANATION: Given that their are two general method other than main methods, these methods are rec...
Q: the main objectives is to keep high operational database flexibility for their customers and supplie...
A: There are five factors that influence database performance: workload, throughput, resources, optimiz...
Q: Which one of the following is a proposition/statement? a. Six is an odd integer. b. Divide 12 by 2 t...
A: Given: Which one of the following is a proposition/statement? a. Six is an odd integer. ...
Q: The benefits of cloud computing are they the same as the benefits of traditional computing? What are...
A: Benefits of cloud computing over traditional computing: Cloud computing offers many benefits, It all...
Q: i. Find the output string for the input string babbab. ii. Determine whether the input string aabcab...
A: 1) string : babbab String b a b b a b State X X Z X X Z X Output 0 1 0 0 1 0
Q: Write a program that will take this dictionary: gradePoints = {"A":4,"B":3,"C":2,"D":1,"F":0} and ...
A: The average of the academic is determined by dividing the total amount of quality points earned for ...
Q: PLACE .FILL X45A7 LDI R3, PLACE The assembler puts the translated version of the LDI instruction abo...
A: Consider the instructions,PLACE .FILL x45A7LDI R3, PLACE• Here, the LDI instruction follows into the...
Q: Write an assembly program using MARIE's assembly Instruction set that prompts the user to enter a no...
A: CODE: JNS CheckInt /subroutine CheckInt LOAD X /Load the value of x after subroutine is ex...
Q: You are given a 2 by n grid, where the cell on row i column j contains a non-negative number ai,j . ...
A: ANSWER:-
Q: Which of the following is the most often utilised data link layer connection in wired networks? a. I...
A: Introduction Data Link Layer is used in transferring the data between various nodes in the network
Q: Explain the issue of zero-crossings in hybrid systems. Offer one example. Also explain why how the z...
A: Zero crossings in hybrid system is a function which passes through zero from a positive or negative ...
Q: 2. Write an application that reads the (x,y) coordinates for two points. This should prompt for and ...
A: Ans: Code: import java.util.Scanner;class Main{ public static void main(String arg[]) { ...
Q: Run zuul-with-enums-v2. How many rooms are there in the scenario? Draw a map of the existing rooms
A: "World of Zuul" is a very simple, text based adventure game. Users can walk aroundsome scenery.
Q: Let L be an integer list object. Write a function that reverses L without utilising any other data s...
A: Introduction Use a stack data structure such that the elements that are inserted first are removed ...
Q: What affects does delay skew have on the signal?
A: Intro What effects does delay skew have on the signal?
Q: NW Q3) IP addressing operates at the network layer (Layer 3) of OSI, IP addresses must be able to id...
A: We have to find here:- a) Sub-net maskb) sub-net idc) range of ip address for given few hosts.
Q: You are hired to develop an automatic patient monitoring system for a home-bound patient. The system...
A: As the answer is below ? 1)Patient: The target actor responsible for designing the system. All inter...
Q: (b). Determine the asymptotic growth rate of the following expressions and justify your answers: (i)...
A: Find the answer with reason given as below :
Q: (C PROGRAMMING ONLY) 1. Leap Year Detector by CodeChum Admin Let’s try to find out whether a year ...
A: I have provided C CODE along with CODE SCREENSHOT and 2 OUTPUT SCREENSHOTS-------------
Q: 2. Explain any two structures of Operating Systems Services.
A:
Q: Complete the Python program to create a Horse table, insert one row, and display the row. The main p...
A: Here is the solution with an output:-
Q: How can we improve the dependability and accessibility of a local area network?
A: Introduction: According to the question, a local area network (LAN) is a computer network made up of...
Q: Write a C++ program that contain a menu rto call user defined functions on a onc dimendional array :...
A: C++ program have the feature which enables the programmers to define the function which is their own...
Q: Lab 13 Adding a JTextBox and a JTextArea Add a JTextField and a JTextArea to the frame. Initialize ...
A: Given The answer is given below
Q: ployee struct as a single struct. You wi employees out to a file. The SAVE com Y argument and return...
A: The file code is given as,
Q: Write a C++ program that contain a menu rto call user defined functions on a onc dimendional array :...
A: Given, 1- fill the array with integers >20 2- print the content of the array 3- find all perfect ...
Q: What is the significance of access restrictions in today's world? Please include at least two instan...
A: Introduction: Access control is a security method that limits who or what can see or utilize resourc...
Q: Write the Java statement for the following. Declare an array of String named jleague with values “C...
A: Declare an array of String named jleague with values “Clark, Bruce and John” ____________________...
Q: d. Distinguish between the following pairs of Big O notations and give practical examples to illustr...
A: Time complexities are measured using the Big O notation.
Q: The following pseudocode should set the values of a 10-element array to the values 1 through 10 then...
A: The question is to correct the pseudocode.
Q: iv. Class has the greatest number of hosts per given network address b)B a) A c)C d)D UDP needs the ...
A: iv) Number of hosts in class A = 2 24 Number of hosts in class B = 2 16 Number of hosts in class C =...
Q: 1-How can the CPU recognize the device requesting an interrupt ?
A: Note: This is a multiple-question-based problem. As per company guidelines, the first question is so...
Q: Javaprogram - Using a nested loop, create a program that produces the following output: ...
A: class Test { public static void main(String[] args) { int i,j=3,k; for(i=1;i<=3...
Q: a. Write a python program that writes data to a file. The data consists of a series of records, each...
A: the answer for above question is :
Q: 5. Why are information policy, data administration, and data quality assurance essential for managin...
A: let us see the answer:- "Since you have asked multiple questions I am solving the first one for you ...
Q: What sorts of analyses can the NLOGIT software package perform?
A: Introduction Following are types of analysis that can be performed on NLOGIT: Data Analysis Model ...
Step by step
Solved in 2 steps with 1 images

- USE THE LIST = {1, 2, 3, 4, 5, 6, 7, 8, 9, 10} not 10 9 8 7 6 5 4 3 2 1The following numbers are inserted into an empty LLRBT in the given order: 11, 2, 14, 25, 15, 13, 16. Please draw the resulting LLRBT.2. List all the steps used to search for 7 in the list 1, 3, 4, 5, 6, 8, 9, 11 using a) a linear search b) a binary search
- 5(b) Give the two arrays that will be merged by the final step of mergesort on [8, 2, 1, 4, 5, 3, 7, 9].Apply Quicksort algorithm to arrange the following numbers in ascending order. Highlight the partitioning position on each stage. 12, 50, 13, 6, 78, 45, 42, 90, 15, 34C# The following code is for the Divide portion of the MergeSort algorithm. There is one mistake in the code. State where the error is, why it is a mistake and how to fix it.
- (python) 14. Based on the following Sorted List, show the steps of a Binary Search if the search key was -5: Enter the index value for the left, right and comparison. Enter one of the following for the Result answers: Left, Right, Found, Not Found. If there is no value needed in a location, put N/A [ -34, -23, -11, -5, 1, 3, 7, 11, 14, 19, 20, 25, 33, 42 ]7. Do the insertion sort for the data below: 55, 79, 23, 40, 90, 15this is not the proper answer, the list is list = {1, 2, 3, 4, 5, 10, 9, 8, 7, 6} not list {10, 9, 8, 7, 6, 5, 4, 3, 2, 1}
- Q1: Fill the following tables using recursive linear search algorithm. Search 10 from the list 9 , 16 , 7 , 12 , 10 , 32 using Recursive Linear search Algorithm Search(0,6, 10) a1≠10 and 1≠6 Search 8 from the list 9 , 16 , 7 , 12 , 10 , 32 using Recursive Linear search Algorithm Search(0,6, 8) a1≠8 and 1≠6int [] list = {43,81,7,46,50,14,26} and the length = 7(c++)Apply bubble sort on the following data 11,44,55,-6,66,88,22,55,66,10

