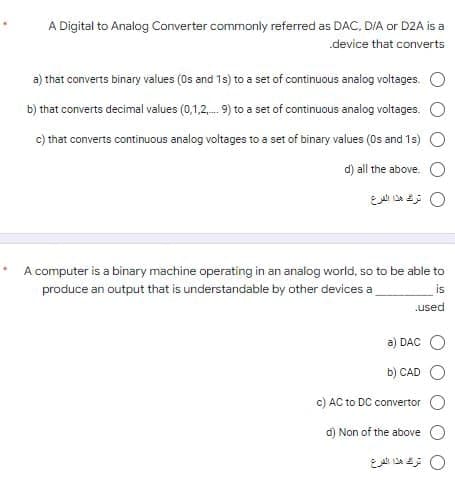
.device that conve ry values (0s and 1s) to a set of continuous analog voltages. nal values (0,1,2, 9) to a set of continuous analog voltages. tinuous analog voltages to a set of binary values (Os and 1s) d) all the above.
Q: how do I upload a file on bartleby.
A: You cannot upload the file in bartleby. We have only the option to upload image from the system. So…
Q: What does the term "waterfall" mean in the context of software development?
A: The waterfall model is a traditional model utilized in the framework improvement life cycle to make…
Q: What are the advantages and disadvantages of cloud data storage? Provide a list of firms that…
A: Answer:
Q: 1. Write a program using while loop statement to evaluate the equation y = xn when n is a…
A: Code: #include <stdio.h>#include<conio.h>int main(){int count, n;float x,y;printf("Enter…
Q: Task: Compute n! In this part of the assignment, you will write a recursive function that, when…
A: The function code for the calculation of factorial value is given in the next step.
Q: can this phong shading program be implemented in pure python? thanks in advance struct Lighting {…
A: It is defined as a powerful general-purpose programming language. It is used in web development,…
Q: When it comes to authenticating distant users, what sets them different from local users? Which one…
A: Start: Do remote users need to be authenticated? Which was more dangerous Validation: It identifies…
Q: Can you tell me about the storage structure that the Android operating system uses?
A: Introduction: We use a certain form of storage in Android to permanently store the data (not…
Q: What is the normal location of the devices that make up a LAN?
A: A local area network, more commonly referred to as a LAN, is a network that connects computers that…
Q: can I know the flowchart and pseudocode for this this coding...and can you add comment in the coding…
A: #include <iostream> using namespace std; //functions declaration void Square(float…
Q: Identify which documents should be sent to the developer at the end of a project.
A: Answer:
Q: struct grade { char id[10]; int mark; }; Using the student structure given above, create an array of…
A: The program is written in C Language. Check the program screenshot for the correct indentation.…
Q: write DQL statement to do the following (and a screenshot of the result): 2. Find products that have…
A: SELECT DISTINCT(P.ProductName) FROM OrderDetails O, Products P WHERE NOT (P.ProductID =…
Q: Create a c++ program that askt 4 numbers (a,b,c,d) and arrange it in ascending order using if-else
A: C++ Program: #include <iostream>using namespace std; int main(){ int a, b, c, d, tmp;…
Q: Root servers, DNS records, and iterated and non-iterated queries are all detailed in detail?
A: Introduction: The Domain Name System (DNS) is known as "the phonebook" on the Internet. Domain names…
Q: Public cloud vs private cloud: what's the difference? Do you have a preference for one over the…
A: Public cloud As a result of user rivalry in the public cloud, performance is diminished. In the…
Q: Prototypes and iterative waterfall models have many similarities (cse 320 software engineering)
A: The Waterfall Model is also known as the Classical or Traditional Model. Another name for the…
Q: Explain the relationship among physical address, segment address, and offset address. Discuss the…
A: The segment address is located within one of the segment registers, defines the beginning address of…
Q: How can you set up and manage both physical and virtual networking devices on a network at once?…
A: Virtual networking facilitates more centralization and simplification of network administration.
Q: brief report on the CT portion demonstration, please.
A: Given: a quick rundown of a CT component demonstration? Answer: A tiny beam of x-rays is focused on…
Q: it is conceivable to connect with a computer without an operating system, and if so, why.
A: Introduction: Here we are required to explain is it conceivable to connect with a computer without…
Q: Please elaborate on the many metrics that go into the software development process. Is there…
A: As a result: Could you provide us a more detailed overview of the metrics used in the software…
Q: The database design is likely to change frequently: 1. Database Extension 2. Database Intension 3.…
A: For the statement, "The database design is likely to change frequently" The given options are: 1.…
Q: List three ring topology benefits and drawbacks.
A: answer is
Q: It is necessary to provide specific information on the Universal Serial Bus (USB).
A: Universal Serial Bus (USB): USB is a standard interface that facilitates communication between…
Q: Please provide a comprehensive breakdown of the many forms that digital signatures may take.
A: Introduction: Here we are required to explain and provide a comprehensive breakdown of the many…
Q: What are the differences between public and private cloud computing? What do you think is the best…
A: As per the question statement, We need to list difference between public and private cloud…
Q: For procedures that aren't addressed by a systems analysis, consider using Structured English
A: A human (or individual) will study a system to carry out a process known as systems analysis. This…
Q: Which of these two scheduling approaches—preemptive or non-preemptive—requires more time and…
A: Non-preemptive scheduling allots the CPU to the process until it stops or moves to the waiting…
Q: e) Assume a database named "Hospital" exists on the MYSQL server. The database contains a table…
A: HTML: HTML stands for HyperText Markup Language. It is used for creating web pages. It is very…
Q: Why should Artificial Intelligence be classified as both a science and an art form?
A: The study of intelligent behavior, learning, and adaptability in machines is the focus of the field…
Q: 1. Create a class named Cat. Declare two (2) empty instance variables: catType (String) and…
A: In this question we have to create a java class and create some constructor methods which will set…
Q: Why do we utilise MATLAB to solve difficulties in Computational Geometry?
A: Introduction: In business and academia, MATLAB is used by millions of engineers and scientists for…
Q: Write a c++ program that display the basic student information (age, class, name, avg) use simple…
A: The C++ program along with the snapshot of code and output is given below:
Q: In a recovery file, what are the necessary requirements for the entries of transaction status and…
A: Database systems: Database systems, like any other computer system, might fail, but the data they…
Q: There are many different types of software processes, but they all must have the same core tasks.…
A: Authentic programming procedures are staggered arrangements of specialist, communitarian, and…
Q: 1. In the code editor, you are provided with a main() function that asks the user for 2 integers.…
A: The given main function is: int main(){ int a, b; printf("Enter Integer 1: ");…
Q: a ) How to add 40 on this linear hashing ? b) How to delete 10 on this linear hashing ? please…
A: Linear hashing is a form of dynamic hashing scheme. In linear hashing there is no need of the…
Q: Use a variety of examples to explain real-time operating systems. Explain how it differs from a…
A: Real-time operating system: It is often used in environments where a significant number of events…
Q: 2- Numerate (e) the Op-Amp Configurations and explain one of them.
A: Introduction: Here we are required to explain what is Op-Amp configuration and explain one of them.
Q: While Linux and UNIX are command-line operating systems, they also include graphical user…
A: We shall examine Linux and UNIX operating systems in the provided situation. DESCRIPTION - Although…
Q: Write a program using interrupts to get data serially and send it to P2 while Timer 0 is turning the…
A: below is the code:
Q: What exactly is a digital certificate, and how is it used? Exactly what does it mean when you talk…
A: Start: What is a digital certificate and what does it mean? What is a certificate authority's…
Q: Formal Languages and Automata Theory Explain this in detail. “A language is decidable iff it is…
A:
Q: Are digital certificates and certificate authorities part of the pki?
A: yes, the digital certificates and certificate authorities are the part of PKI. Explanation:- PKI or…
Q: Explain in great detail the many forms that digital signatures might take.
A: Given: We have to discuss in detail the many forms that digital signatures might take.
Q: When retrieving emails, what protocol is used?
A: As per our guidelines we are supposed to answer only one question. Kindly repost other questions as…
Q: Cluster Analysis is one of the tasks of Data Mining. Explain what Cluster Analysis is, what it is…
A: Clustering is the process of dividing a collection of abstract objects into classes. Cluster…
Q: Solve the following problem using MATLAB. Write the syntax and the MATLAB out put on the space…
A: We have to find how manyboxes of mangoes were there? Given that number of mangoes in each crate =42…
Step by step
Solved in 2 steps

- (Practice) Although the total number of bytes varies from computer to computer, memory sizes of millions and billions of bytes are common. In computer language, the letter M representsthe number 1,048,576, which is 2 raised to the 20th power, and G represents 1,073,741,824, which is 2 raised to the 30th power. Therefore, a memory size of 4 MB is really 4 times 1,048,576 (4,194,304 bytes), and a memory size of 2 GB is really 2 times 1,073,741,824 (2,147,483,648 bytes). Using this information, calculate the actual number of bytes in the following: a. A memory containing 512 MB b. A memory consisting of 512 MB words, where each word consists of 2 bytes c. A memory consisting of 512 MB words, where each word consists of 4 bytes d. A thumb drive that specifies 2 GB e. A disk that specifies 4 GB f. A disk that specifies 8 GBBit Manipulation We reviewed bitwise logical operations in C (&=AND, |=OR, ^=XOR): A = 0011 1100 B = 0000 1101 --------------------- A&B = 0000 1100 A|B = 0011 1101 A^B = 0011 0001 For the following three questions, assume: A = 1010 1010 1010 B = 0000 1111 0000 And compute the results of these bitwise operations: (A & B)& B 1 Answer: (A | B)| B 2 Answer: (A ^ B)^ B 3 Answer: We also discussed the C shift operations (shift left=<< and shift right=>>). For the following two questions, assume: C = 0001 1001 1010 And compute the results of these shift operations: 4. C >> 3 4 Answer: 5. C << 2 5 Answer:The Population Studies Institute monitors the population of the United States. In 2008, this institute wrote a program to create files of the numbers representing populations of the various states, as well as the total population of the United States. This program, which runs on a Motorola processor, projects the population based on various rules, such as the average numbers of births and deaths per year. The institute runs the program and then ships the output files to state agencies so the data values can be used as input into various applications. However, one Pennsylvania agency, running all Intel machines, encountered difficulties, as indicated by the following problem. When the 32-bit unsigned integer 1D2F37E8 (representing the overall U.S. population prediction for 2013) is used as input, and the agency’s program simply outputs this input value, the U.S. population forecast for 2014 is far too large. Can you help this Pennsylvania agency by explaining what might be going wrong?…
- Building RESTful Web Services for Fibonacci Sequence Operations Using Spring Preface The Fibonacci sequence is a series of numbers where each number is the sum of the two preceding numbers. The sequence starts with 0 and 1, and each subsequent number is the sum of the two previous numbers. The sequence continues infinitely and goes as follows: 0, 1, 1, 2, 3, 5, 8, 13, 21, 34, 55, 89, 144, 233, 377, and so on. The sequence is named after Leonardo Fibonacci, an Italian mathematician who introduced the sequence to the Western world in his book Liber Abaci, which was published in 1202. The Fibonacci sequence has many interesting mathematical properties and has been observed in various natural phenomena, such as the branching of trees and the spirals in shells. Question In this assignment, you will be building a set of RESTful web services using Spring that will allow clients to perform several operations related to the Fibonacci sequence. The web services will be able to generate the…In the Hamming coding system (7.3), its representation is expressed as 3 control (test) bits and 7 total bits (data+control bits).In the literature, control bits are represented as (cl, c2, c3, or (pl, p2, p3, .) The bit string sent by encoding with Hamming coding (15,4) is on the receiving side, It is retrieved as 001100101100 (pl.p2.dll). According to this bit sequence;Which option is given according to the control bits (p1.p2.p3.p4) sequence of the received bit sequence?A 0110B 1100C 1001D 0011E 0010Ships of the navy of communicate at sea via code signals transmitted by flags, as follows: each ship has six flags (the same set of six flags is on every ship); a code is formed by choosing three flags and arranging them, from top to bottom, on the mainmast. How many different codes are possible? Example: "don't pull that big plug in the bottom of the boat" differs from "if you sail too close to the edge, you'll fall off"
- Correct answer will be upvoted else downvoted. Computer science. Mike found two double integers an and b of length n (the two of them are composed exclusively by digits 0 and 1) that can have driving zeroes. All together not to fail to remember them, he needed to build integer d in the accompanying manner: he makes an integer c because of bitwise adding of an and b without moving convey, so c might have at least one 2-s. For instance, the aftereffect of bitwise adding of 0110 and 1101 is 1211 or the amount of 011000 and 011000 is 022000; after that Mike replaces equivalent continuous digits in c by one digit, accordingly getting d. In the cases above after this activity, 1211 becomes 121 and 022000 becomes 020 (thus, d will not have equivalent continuous digits). Sadly, Mike lost integer a preceding he could compute d himself. Presently, to perk him up, you need to track down any paired integer an of length n to such an extent that d will be greatest conceivable as integer.…Consider an encoding scheme where integer numbers from 1 to 26 are encoded as character 'A' ro 'Z'. for example , integer 1 encodes character 'A' integer 2 encodes character 'B' and so on last till integer number 26 which encodes character 'Z'. Using this encoding scheme, design a system to count all possible decodings for a given digit sequence. For example, for digit sequence "1524" there are three possible decodings. 1, 5, 2, 4 - AEBD 1, 5, 24 - AEX 15, 24 - OXAssume that CS=3500, DS=4500, SS=5500, SI=2200, DI=4200, BX=7300, BP=8000, AX=3420 (all values are in hex). Calculate the physical address of the memory and show the contents in each of the following: a) MOV [BP]+10,AX b) MOV [SI],AX c) MOV [BX][DI]+20,AX
- A communication satellite orbits the earth at distance of 30000 miles with each mile having a propagation speed of 5 x 10^(-6) seconds. The data rate of the satellite link is 1 Mb/s. Suppose a data frame is 1250 bytes and that ACKs have negligible processing and transmission times. With the Stop-and-Wait protocol, what is the maximum utilization possible.Discuss ways in which the utilization can be improved. Remember that the satellite is far away and therefore outline the disadvantages to any scheme you propose that may improve the utilization.Which of the following best describes Von Neumann's architectural style?a) A fixed-point binary number system has 5 whole bits and 3 fractional bits. What is the range of numbers in binary that can be represented in this format? What is the decimal value of the largest number that can be represented? b) A fixed-point binary number system has 4 whole bits and 12 fractional bits. Show the (4-hexit) hexadecimal representation of the following decimal numbers 0.375, - 1.33, and 1/40 in this finite format. Do not show recurring sequences. c) Assume a 16-bit floating point format designed as follows: 4-bit signed exponent and 12-bit fraction. Normalization is strictly enforced. What is the hexadecimal representation of the 16-bit floating point format for 1/40?

