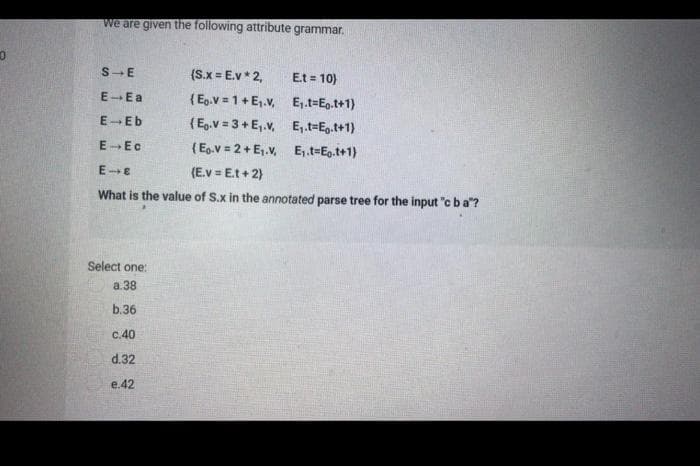
0 we are given the following attribute grammar. S E (S.x = E.v* 2, Et = 10) E-Ea (Eg.v=1+E₁.v, E₁.t=Eo.t+1) E-Eb (Eg.v=3+E₁.v, E₁.t-Et+1) E-Ec (Eo.v=2+ E₁.v. E₁.t=Eo.t+1) E-E (E.v=Et + 2) What is the value of S.x in the annotated parse tree for the input "cba"? Select one: a.38 b.36 c.40 d.32 e.42
Q: Why is the Internet Held Up as a Paradigm for ICT? Provide evidence to support your assertions.
A: telecommunications and information technology (ICT) Modern correspondence, coordinated media…
Q: Define each layer of the OSI model and explain its function.
A: Define each layer of the OSI model and explain its function.
Q: It is necessary to define the concept of application virtualization.
A: Introduction: Application virtualization: Provide multiple/many runtime environments for…
Q: In-depth discussion of architectural design's significance in software development.
A: The architectural design is necessary for the program to represent the software design. "The process…
Q: For what reasons is the Internet considered a model of ICT? Both the explanation and the…
A: For what reasons is the Internet considered a model of ICT? Both the explanation and the…
Q: Why is the Internet Held Up as a Paradigm for ICT? Provide evidence to support your assertions.
A: Answer : Internet held up as a paradigm for ICT this is because , internet contains a lot of data…
Q: When should distributed database systems employ data replication to address data fragmentation if it…
A: In computing, replication is the process of exchanging data among redundant resources, such as…
Q: How do cohesion and coupling relate to creating well-designed software?
A: Answer: We need to write the how cohesion and coupling related for creating well designed software…
Q: Exactly what tasks do operating systems primarily serve to perform?
A: An operating system handles input/output to and from attached hardware devices, such as hard disks,…
Q: Can technology be utilized in some manner to enhance learning? My outlook on many different issues…
A: Can technology be utilized in some manner to enhance learning? My outlook on many different issues…
Q: When people refer to "operating systems," what do they really mean?
A: OS is also known as operating system.
Q: In what other ways has the use of ICT benefited us, and what ways has it hindered us?
A: ADVANTAGES OF ICT USE IN BUSINESSES Businesses can store, process, analyse, and exchange enormous…
Q: What benefits and drawbacks come with software of "good enough" quality?
A: Please find the answer below :
Q: Seek for actual implementations of design patterns and defend their quality.
A: INTRODUCTION In this question, we are asked to Seek actual implementations of design patterns and…
Q: With this talk, you'll delve into the topic of architectural design and analyze why it's important…
A: Given: Architectural design is crucial to software development. In software development,…
Q: In what other ways has the use of ICT benefited us, and what ways has it hindered us?
A: In what other ways has the use of ICT benefited us? if I talk about the ICT then it will benefit…
Q: To what extent do virtual private networks (VPNs) improve on the safety of public Internet…
A: Virtual private networks: Network-based VPNs link untrusted networks securely. All of a company's…
Q: Consider a file system on a disk that has both logical and physical block sizes of 512 bytes. Assume…
A:
Q: Provide a comprehensive breakdown of the kernel of an operating system, outlining its many…
A: Constituents of the Core The kernel of an operating system is identical to the system's central…
Q: The difference between deterministic and non-deterministic computers according to their purpose and…
A: INTRODUCTION: When it comes to a determining whether or not machines are deterministic, it is…
Q: What motivates developers to create a microkernel for an OS? Is this method dissimilar to the…
A: Given: What principle underlies the development of the microkernel in an operating system? What…
Q: When it comes to a local area network, what precautions should be taken to ensure its availability…
A: LAN is also known local area network.
Q: How have the advantages and disadvantages of ICT been felt by the general public?
A: Advantages of ICT: Communication:With the help of ICT, it became faster and more efficient to…
Q: When two or more individuals collaborate, what does it mean? Make a list of all the different…
A: Answer: we need to write about the individuals collaborate and what does it mean and also make it…
Q: The value of architectural design in creating high-quality software is discussed in this lecture.
A: Identification of essential system components and their communications. The architectural design…
Q: Summarize the key characteristics between circuit- and packet-switching networks.
A: Introduction 1) The two separate switching techniques used to link the many communicating devices in…
Q: You've discovered that an unauthorized user or users accessed sensitive customer data from your…
A: Security lapses happen when unauthorized access is granted to a computer's data, applications,…
Q: This article will provide an in-depth overview of Windows Service Control Manager.
A: Introduction: SCM: The Windows NT family of operating systems has a special system feature called…
Q: Give a little history of how wireless LAN standards came to be.
A: A wireless LAN is a wireless computer network that links two or more devices using wireless…
Q: There are various difficulties in creating an information system architecture to serve this new…
A: Definition: An information system architecture provides a formal definition of business or…
Q: In-depth discussion of architectural design's significance in software development.
A: Architectural design's significance in software development: In the context of software development,…
Q: reless networks for developing countries. Why are some businesses eschewing LANs and wired…
A: the solution is an given below :
Q: Give some concrete examples of the differences between the operationalization of objective and…
A: Examining two things side by side: In order to hold a particular values while a programmer is being…
Q: Recursion In python
A: I have provided PYTHON CODE along with CODE SCREENSHOT and OUTPUT SCREENSHOT…
Q: Think about the benefits and drawbacks of introducing wireless technology. To ensure smooth…
A: Advantages of wireless networking Increased efficiency Improved data communications lead to faster…
Q: The security of a virtual private network (VPN) surpasses that of public Wi-Fi (VPN). When using a…
A: According to the information given:- We have to define the security of a virtual private network…
Q: Provide a comprehensive breakdown of the kernel of an operating system, outlining its many…
A: Given: We have to discuss Provide a comprehensive breakdown of the kernel of an operating system,…
Q: encryption could be a problem for application-le andling encrypted payloads via an application-
A: End-to-end encryption (E2EE) is a system of correspondence where just the conveying users can peruse…
Q: Malicious traffic might be redirected from one VLAN to another, resulting in an intrusion into the…
A: VLAN :- VLAN is a custom network which is created from one or more local area networks. It enables a…
Q: How you use virtual machines for an OS vs how you use them for a program is quite different. Extend…
A: Virtual machines abstract our personal computer's hardware, including the CPU, disc drives, RAM, and…
Q: Discuss how data mining may be used to achieve various goals.
A: INTRODUCTION: Information mining could be a handle utilized by companies to turn crude information…
Q: The purpose of this article is to provide an overview of Windows Service Control Manager and its…
A: Introduction: The Windows NT series of operating systems has a special system feature called Service…
Q: 7 3 8 9 4 10 0 11 5 2 6
A: Sorry to say but the output for the given binary tree is not 3,4, 5, 2 Below I show you the code and…
Q: What distinguishes Ubuntu from other server operating systems, and what features does it share with…
A: We need to distinguish Ubuntu server from other server operating systems.
Q: In linear programming problems, the object function is more important than the constraints; why is…
A: The most optimal solution to a problem whose constraints have been specified can be determined with…
Q: JAVA Write a java program using streams to get the longest string from the list by using lambda…
A: Lambda expression is a short block of code which takes in parameter and return a value. A stream is…
Q: Unfortunately, we cannot examine the inner workings of operating systems and how they accomplish…
A: The answer of the question is given below
Q: The two primary roles of an OS should be briefly explained
A: in the following section we will be discussing about the primary functionalities of operating…
Q: A computer's operating system is primarily responsible for the following:
A: Computer's operating: We will discuss operating system duties in detail and how these duties are…
Q: It makes sense to discuss non-systems analytical approaches using structured language.
A: Given: Structured analysis uses data flow and entity connection models, process requirements, and…
7...
Step by step
Solved in 2 steps with 2 images

- True or false: In RapidMiner, the label (dependent variable) can be coded either alphabetically (e.g., true/false) or numerically (e.g., 0/1). True or false: The Logistic Regression operator in RapidMiner offers only one algorithm for model creation."Equatable and Comparable" in the Swift Programming: The Big Nerd Ranch Guide (2nd Ed.) e-book: Point’s current conformance to Comparable yields some confusing results. let c = Point(x: 3, y: 4) let d = Point(x: 2, y: 5) let cGreaterThanD = (c > d) // false let cLessThanD = (c < d) // false let cEqualToD = (c == d) // false As the above example demonstrates, the trouble arises in comparing two points when one point’s x and y properties are not both larger than the other point’s. In actuality, it is not reasonable to compare two points in this manner. Fix this problem by changing Point’s conformance to Comparable. Calculate each point’s Euclidean distance from the origin instead of comparing x and y values. This implementation should return true for a < b when a is closer to the origin than b. Use the formula shown in below Figure 25.1 to calculate a point’s Euclidean distance. Figure 25.1 Euclidean distance Euclidean distanceA Student can be either a graduate student or an undergraduate student. A graduate student can be either a Masters or a PhD student. An undergraduate student can be an honour student. A department has both undergrad and graduate students. A department offers courses and each course is taught by a professor. Professors, Graduate students, and Honours students do research. Every person has a name. A student has ID. A department has location and a course has ID. Write java code for the above scenario. Each attribute should have a public getter and a public setter. You should use inheritance whenever possible. You have to override the toString operation in each class that defines an attribute. The overriden toString should print out the value of the attributes in the class. The research operation takes research subject as an input string and simply prints out the research subject. The Student class should have an arraylist of courses that the student takes, and an operation to add a…
- ______ is a special operator used to check whether an attribute value matches a given string pattern. Between Null Like In1. You can manage risk in your orders by adding the TakeProfit/StopLoss attributes using fxcmpy. Group of answer choices True False 2. The following code retrieves and prints the candles data using the fxcmpy package. from fxcmpy import fxcmpy_candles_data_reader as cdr print(cdr.get_available_symbols()) Group of answer choices True False 3. Optimizers are a set of procedures defined in SciPy that either find the minimum value of a function or the root of an equation. Group of answer choices True FalseAlias is also known as a data type. True False We can use Hierarchy to combine two values of a dimension into a single category. True False ........... Which of the following can include multiple version of the same worksheet? * 0/2 Dashboard and stories Stories but not dashboards Dashboards but not stories Neither dashboards nor stories ......... A color gradient is used for which of the following * 0/2 Discrete measure Continuous measure Both continuous and discrete N/A
- DISCRETE STRUCTURE Alia went to a fast-food restaurant. She has been offered to buy a meal-deal with discounted price. The meal-deal set can only have one main menu and one side or one beverage. Main menu Pizza – Blazing Seafood • Pizza – Chicken Supreme . Pizza- Beef Pеррегoni Burger – Single cheese Burger – Double cheese Side Crispy Fries • Potato Wedges • Cheesy Pop • Chicken Fries • Sweet Potato Fries Beverage . Соса-Cola • 7 UP • Lemonade • Peach Tea • Lemon Tea i. How many ways a meal-deal can be formed if Alia prefer a set that contain burger? ii. How many ways a meal-deal can be formed if Alia does not like Coca-Cola?Some rows of the STUGRADE table of a school are shown below: STU_CODE CLS_CODE GRADE YEAR 291 111 3.1 2010 938 101B 2.3 2011 931 M101 3.3 2040 291 M101 3.4 2018 190 111 2.0 2021 931 321 3.9 2003 Suppose that STU_CODE is the student code (foreign key) and CLS_CODE is the class code (foreign key). Which of the following computes the average for each year of the student with code 931? a. SELECT AVG(GRADE) FROM STUGRADE WHERE STU_CODE = 931 GROUP BY YEAR b. SELECT AVG(GRADE) FROM STUGRADE WHERE STU_CODE = 931. c. SELECT AVG(GRADE) FROM STUGRADE GROUP BY STU_CODE = 931 d. SELECT AVG(GRADE) FROM STUGRADE WHERE STU_CODE = 931 GROUP BY AVG(GRADE)Imagine that a piece of a primary key is also a potential secondary key. Can you tell me what your reaction would be?
- Which of the following classifiers is least likely to underfit or overfit the data? Group of answer choices a) Linear b) KNN c) NN Answer with proper explanation else skipThe values of the set membership is represented by ___________ Select one: a. Both Degree of truth and Probabilities b. Degree of truth c. Discrete Set d. ProbabilitiesQuestion 5 Full explain this question and text typing work only thanks write in tuple calculus Hotel(hotelNo,hotelName,city) Room(roomNo,hotelNo,type,price) Booking(hotelNo,guestNo,dateFrom,dateTo,roomNo) Guest(guestNo,guestName,guestAddress) list the names and cities all of guests

