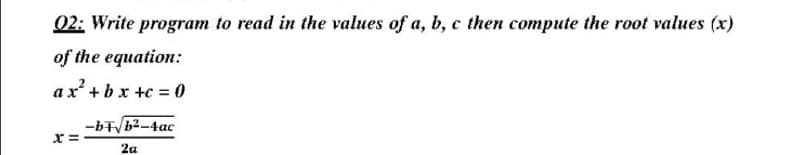
02: Write program to read in the values of a, b, c then compute the root values (x) of the equation: ax²+bx+c = 0 -bT√b²-4ac X= 2a
Q: What are the most important tasks that an operating system performs?
A: Answer
Q: What is the significance and function of the central processing unit (CPU)? Explain your point of…
A: The CPU is the brain of a computer containing all the circuitry needed to process input store data,…
Q: Where does cloud computing fit into the overall structure and operations of an organisation in the…
A: Explanation: You may create content for your audience while also assisting them in finding it via…
Q: What role does data modeling play in the analysis process, and how valuable is it? How can we figure…
A: Indeed, the following highlights the significance and use of data modeling throughout the analysis…
Q: When a child process utilizes unnamed pipes to read the parent's message buffer, what happens…
A: The answer is
Q: What distinguishes the software development process from software modeling? Describe how one aids…
A: Given: Software Development Process: A software development process is a method of breaking down…
Q: A global firm expands throughout Pakistan. What form of network would you choose if you were…
A: INTRODUCTION: Here we need to tell What form of the network would you choose if you were employed to…
Q: Include some of the choices to be taken, the proper business model, payment alternatives, and the…
A:
Q: The functionality of Network APIs should be described in brief terms
A: The Network API gives capacities to arrange calls by means of HTTP or HTTPS. The Network API…
Q: JAVA Using interfaces we can specify similar behaviors for possibly disparate classes.…
A: Below is the code:
Q: What is data encapsulation, and why would you use it?
A: Given: Encapsulation is the collection of data into a single entity. It's a technique that connects…
Q: Explain the benefits and drawbacks of adopting software packages instead than custom-made apps.
A: While the phrases packaged software and bespoke software are pretty similar, they are not…
Q: Draw a Component Diagram for the Restaurant Online Order management system.
A: Introduction: UML Component diagrams are used in modelling the physical aspects of object-oriented…
Q: What does a firewall defend from? There are rules to packet filtering.
A: 1. What is the main purpose of a firewall? The most important purpose of a firewall is to help…
Q: When it comes to memory, what exactly is dynamic memory?
A:
Q: Explain the characteristics of Ubuntu OS in terms of server operating systems.
A:
Q: 1 + 3 + 5 + ....... + (2n-1) = n^2 P(k+1) Prove the induction
A: Induction Proof: It is used to prove the particular sequence is true. There are three steps in this…
Q: To improve network quality, talk about metrics in your own terms.
A: 1. latency In an organization,latency alludes to the proportion of time it takes for information to…
Q: RPC semantics are susceptible to a variety of errors. What are the two types of failures and how do…
A: Failures should be taken into consideration when RPC calls are made. Failures can be due to client…
Q: What role does data modeling play in the analysis process, and how valuable is it? How can we figure…
A: The act of generating a simplified representation of a software system as well as the data pieces it…
Q: To determine whether an implementation affects the efficiency of your system, how do you conduct an…
A: Each mobile app requires CPU, RAM, hard disc, virtual memory, network bandwidth, and other…
Q: a) You are a new project manager at an IT firm. Your task is to develop an application that is…
A: a) Facts: We need to design an application for an information system organization in which other…
Q: What are some other types of firewalls than router-based?
A: foundation: While routers blindly transfer communication between two networks, firewalls monitor the…
Q: Is it because TCP is more secure than UDP?
A: TCP and UDP: TCP provides trustworthy data transit from one host to another; HTTP, FTP, SMTP, and…
Q: When compared to a primitive data type (such int, double, or boolean), how is a String different?
A: primitive data type: Because only classes may have methods, string is non-primitive. Primitive…
Q: // Program describes two files // tells you which one is newer and which one is larger import…
A: Solution :: Code: import java.nio.file.*; import java.nio.file.attribute.*; import…
Q: How can a system be successful technically yet fail organizationally?
A: Several factors contribute to specific software products and efforts with significant technological…
Q: Confidentiality, Integrity and Availability are core attributes in security. Identify 3 threats to a…
A: Introduction: Confidentiality, Integrity and Availability are core attributes in security. Identify…
Q: Who is in charge of adding new items to the forwarding list? Additions to the forwarding table may…
A: Introduction: A router refers to a networking tool that determines an appropriate and available…
Q: Explain FIVE (5) evaluation of cloud service agreements in step 6; Develop Governance Policies and…
A: Cloud computing allows businesses to respond to changing business demands faster and more agilely…
Q: draw the timing diagram of the following instructions MOV E,A
A: MOV instruction: It is used to copy data from source to destination. The first operand is…
Q: In what ways is DHCP beneficial? An IP address, on the other hand, may be referred to as a "MAC…
A: DHCP stands for Dynamic Host Configuration Protocol, It is a network management protocol used to…
Q: To improve network quality, talk about metrics in your own terms.
A: Network Quality: When analyzing or improving network performance, there are numerous parameters to…
Q: Discuss rule based knowledge based system with example.
A: A knowledge based system is a form of artificial intelligence. It aims to capture the knowledge of…
Q: Do you know how to tell the difference between network diagrams AOA and AON? Explain.
A: Answer
Q: ollow the comments to finish the following EMACS code: #…
A: It is defined as a text editor designed for POSIX operating systems and available on Linux, BSD,…
Q: MY NOTES Examine the following while loops and determine the value of ires at the end of each of the…
A: -> We can mod (or remainder) using % For eg. 4 mod 3 = 1 Is same as 4 % 3 =1 -> We can…
Q: Please solve the problem in R-STUDIO, IN R LANGUAGE. THANK YOU Q. Write a function which will take…
A: Write a function which will take 1 argument, the number of days. a. Your first task is to take the…
Q: Daffodil Institute is granted the block 172.20.110.0/16. The administrator wants to create 16
A: The answer is
Q: What exactly do you mean when you say "MS Word"?
A: Microsoft word is a word processor software ,it was developed by Microsoft in 1983. It is the most…
Q: Is there a way to use Amazon Web Services to connect business applications?
A: AWS can be used to store critical data. It offers multiple types of storage to choose from, allowing…
Q: Using Ubuntu/Linux, create an interface type Menu using AWK combined with Zenity for these specific…
A: while [ 'Exit' !=opt ] ; do clear; op=$(zenity --list --text="\t\t\t\t\tElectronic…
Q: What is an operating system, and how does it aid in the coordination of computer system activities?
A: Introduction: What is an operating system, and how does it aid in the coordination of computer…
Q: Learn all you can about cloud computing and social networking blogs.
A: Start: Peer-to-peer cloud computing is a subset of social cloud computing that allows peers to…
Q: What can Amazon Web Services do with data?
A: Presentation: Amazon Web Services (AWS) is a safe cloud computing platform that helps businesses…
Q: Discuss how the information system is influenced by the organization.
A: When it comes to supporting management operations, the primary job of an information system is to…
Q: When it comes to configuration management, what is it and how does it differ from other methods?
A: Commencement: Configuration management is a systems engineering method that assures a product's…
Q: Comparison between TCP and UDP In your capacity as a software architect, provide examples of two…
A: Usually TCP is a connection-oriented protocol, whereas UDP is a connectionless protocol.TCP is…
Q: Explain the characteristics of FreeBSD in terms of server operating systems.
A: Ans: the characteristics of FreeBSD in terms of server operating systems is: 1) It is containing…
Q: How does beginning with a bundled data model on paper compare to starting from scratch in computer…
A: Required: What is the difference between beginning a data modelling project using a packaged data…
Step by step
Solved in 3 steps with 1 images

- c# Write program that asks to enter an x numbers and sum the even numbers and odd numbers separately then print the sum?A- write a program that multiply a number in Ax by 19B- write a program that divides the number in BL by the number in CL then multiplies the result by 2Write oop program to read 10 numbers and find the summation of first five numbers , and multiplication of second five numbers
- Find an incorrect line in the following code segment: void swap(int *x, int *y) { int t = *x; *x = *y; *y = t;}....int a = 2, b = 3;swap(*a, *b);Task#3: Write a program that asks the user to enter an integer and then display the hexadecimal representation of that integer.MIPSUsing C++ Write a program that prints a multiplication table for numbers up to 12
- Q2/Write program in C++ that 10 computes the following: y=1+1/x + 2/x^2 + 3/x^3 +...........+ n/x^nWrite a program using function to check if the number is even or odd?Write a program to return the product of digits of given number.Write a program to find the sum of given 2 numbers.Write a program to find the max of two given numbers.Write C++ program to generate 10 random numbers in range 1 to 100 and print them in single line separated by ,

