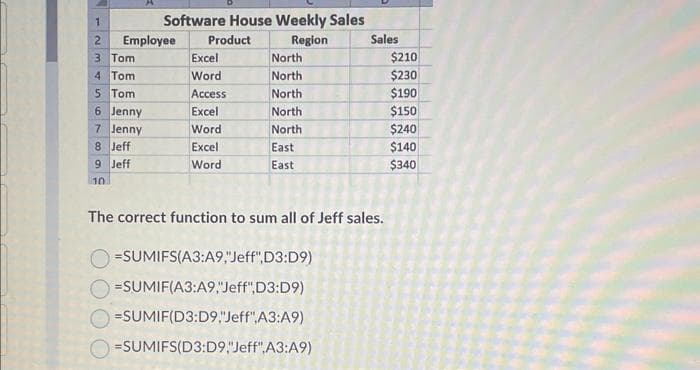
1 2 3 Tom 4 Tom Software House Weekly Sales Product Region Employee 5 Tom 6 Jenny 7 Jenny 8 Jeff 9 Jeff 10 Excel Word Access Excel Word Excel Word North North North North North East East Sales The correct function to sum all of Jeff sales. =SUMIFS(A3:A9,"Jeff",D3:D9) =SUMIF(A3:A9,"Jeff",D3:D9) =SUMIF(D3:D9,"Jeff",A3:A9) =SUMIFS(D3:D9,"Jeff",A3:A9) $210 $230 $190 $150 $240 $140 $340
Q: In most cases, character devices can transmit data far more quickly than block devices can. How…
A: Introduction: The system's standard system of system buffering is used by the block devices to…
Q: In light of the availability of on-chip L3 caches, please explain the pros and downsides of using…
A: Single threads execute one instruction sequence. The procedures are one-by-one. Multi-threaded…
Q: An arithmetic progression is a sequence of numbers such that the difference between the consecutive…
A: In this question, it is asked to provide a java code for the given problem statement. The problem…
Q: hat effect would runlevel 6 (or reboot.target) have if it were the syst
A: Lets see the solution.
Q: Which of the following is not a characteristic of IoT devices: remote controllability,…
A: IoTIoT is a network of interconnected computer devices that can conduct tasks and communicate with…
Q: The Priority. Queue ADT As an ADT, a priority queus P supports the following functions: • • • •…
A: Queue as ADT The queue abstract data type is defined by the following structure and operations.A…
Q: How many bytes of machine code and how many machine cycles do the following instructions take?…
A: In computer programming, machine code, also known as machine language, is the lowest-level…
Q: Immediate Activity Predecessor(s) A None B C DEFGH Calculate the expected time for completion an…
A: Time to completion: Time to completion (TTC) is a measurement of how long it will take to…
Q: comparison methods that can be useful when working with strings are StartsWith and EndsWith. These…
A: StartsWith and EndsWith are comparison methods that can be useful when working with strings. These…
Q: Mark all of the strings below it matches. Only consider full-string (not substring) matches.…
A: The above question is solved in step 2 :-
Q: If you publish an answer from another site, you will be downvoted. Answer in your own tongue, not a…
A: A synchronisation tool is semaphore. A semaphore component synchronizes or regulates access to…
Q: What is the output of the following code: .data A: .word 95 27 34 B: .word 391042 C: .word 642 315…
A: Here is the explanation regarding the given code.
Q: Determine which of the three IPv6 migration strategies is right for you.
A: IPv6: An organisation layer standard called Internet Protocol Version 6 facilitates information…
Q: Should a university course registration system be designed utilising the Waterfall or Agile…
A: Definition: The waterfall technique was developed as a standard paradigm for creating engineering…
Q: Describe three possible vulnerabilities in WiFi networks. Determine a possible attack method and a…
A: Introduction In simple terms, a Wi-Fi network seems to be a web connection that would be distributed…
Q: What is PGP, exactly? What are the five primary services provided by PGP?
A: What is PGP, given? What are the top five services that PGP offers? The answer is PGP, which stands…
Q: What is PGP, exactly? What are the five primary services provided by PGP?
A: What does PGP stand for? What are the five most essential services that PGP offers? PGP is short for…
Q: (15) 6. Minimal polynomial: a) Find the minimal polynomial of √3i over Q. b) Find the minimal…
A: Solution for the given question,
Q: Describe the inner workings of the CNSS security model. Just how big is it in three dimensions?
A: A three-dimensional model called the CNSS security model was created by John McCumbers in 1991.…
Q: Characterize the graphs G for which Y(G) +Y, (G)=p+1. 8
A: Introduction: The word "graph" does not apply to data charts like line graphs or bar graphs when…
Q: IP datagrams on a specific network can carry a maximum of only 440 bytes in the data portion. A node…
A: According to the information given:- We have to follow the instruction in order to get the number of…
Q: Can you explain the distinction between a class and an instance of a class?
A: In contrast, the instance of the class is a real thing that really uses the definitions of the class…
Q: What are the five most noteworthy computer graphics applications in today's corporate world?
A: GIVEN: What are the five most common ways that computer graphics are used? Here are five examples of…
Q: Compare the task of making a cake to the computation of three loop iterations on a parallel…
A: Introduction: Date level parallelism: It's a loop of a sort that will go through separate iterations…
Q: Mark all of the strings below it that it matches. Only consider full-string (not substring) matches.…
A: According to the information given:- We have to choose the correct option in order to satisfy the…
Q: Answer the following questions with a simple true or false and a short explanation of why you chose…
A: The data link layer protocol known as the SR protocol, or selective repetition protocol, transfers…
Q: Consider, as an example, a program that generates inventory reports for a company of reasonable…
A: Users of the Output: For the system generating inventory reports at a small store, the shop and…
Q: What is the MSC anchor's function in the GSM network?
A: Definition: A mobile switching station anchor role is another name for the anchor job in an MSC.…
Q: SAS transmits data to SCSI hard drives through parallel cables. How truthful or incorrect is this…
A: In order to determine if the statement "SAS sends data to SCSI discs through parallel connections"
Q: make notepad program in android studio kotlin
A: INTRODUCTION: You will discover how to make and use your first Android app in this codelab using the…
Q: A downgrade assault is defined as an attempt to lower something's value.
A: Downgrade assault is a type of computer attack which reduces it's security levels.
Q: What media features set an infrared network apart?
A: A wireless mobile technique called infrared (IR) is used for close-quarters device communication.…
Q: There are four general states of a process: (1) ready, (2) running, (3) waiting, and (4) terminated.…
A: Process : A running process is referred to as a program. It is the instance of a computer program…
Q: To what extent have vulnerabilities in the layer-2 protocol used by routers been discovered? When…
A: Introduction : Vulnerabilities are weaknesses in software, hardware, or firmware that can be…
Q: Write a Python program to create a joinplot and add regression and kernel density fits using "reg"…
A: jointplot The joint plot is the clearest approach to comprehend both the individual distribution of…
Q: Algorithm for Decision-making for a wumpus hunter using influence maps. Wumpus-Hunter-React(v) in:…
A: given data:
Q: Describe how the merging of the internet, mobile phones, and other media has paved the way for the…
A: Emerging Technologies: A disruptive technology is one that overthrows an existing technology and…
Q: Why do Chrome OS devices use less internal storage than competing desktop operating systems?
A: System Operating Procedures: The operating system (OS) is the software layer between the user and…
Q: 1. Write a MongoDB query to display the first 5 restaurants which are in the borough Bronx. 2. Write…
A: Suppose Structure of 'restaurants' collection: { "address": { "building": "1007", "coord": […
Q: What are some examples of Automata Theory in action?
A: The applications of automata theory must be determined here. Answer: There are several varieties of…
Q: Write a python program that reads the first n lines of a te Suppose you have a file with all these…
A: code;
Q: a. Hash the following reindeer names, in this order based on the first letter of their name into a…
A: To hash the reindeer names into a hash table of size 8, we can use a simple hash function that maps…
Q: One of the Big Ten Deliverables is often overlooked, misunderstood and even more often just plain…
A: The solution to the given question is: Answer C : Simple Operating Procedures (SOP) Simple Operating…
Q: To what end is encryption still considered the primary means of preventing information loss?
A: The process of encryption refers to the loop that The encoding of information is done with the…
Q: Do you think encryption mechanisms are a key to solving ransomware attacks?
A: Yes encryption mechanism will be a key to solve ransomware attacks.
Q: P is "Donna has a doll" Q is "Carol has a car" Write the simple English sentence for the following:…
A: Negation will change the sentence to a negative stance Question a Carol doesn't have a car and…
Q: Program - python Create an array of 10 integers and pre-populate it with 10 numbers. Then write a…
A: Below is an illustration of how to construct a 10-int integer array, pre-fill it with 10-numbers,…
Q: write a complete program in assembly (DO NOT use data segment in your code) c=0; b=7; do { C++; b--;…
A: SOLUTION- I have solved this problem in Assembly code with comments and screenshot for easy…
Q: As unique identifiers for each system, UIDs and GIDS can only be used once. How truthful or…
A: UIDs as well as GIDs The Unique Identifier, often known as the UID, is the group's one and…
Q: Shawn is approached by a medical staff team with a request to research and introduce a type of…
A: INTRODUCTION: IoT, or the Internet of Things, refers to the entire network of interconnected devices…
Step by step
Solved in 2 steps

- Hi, OCaml programming 1. Create a type slidingTile, consisting of a char matrix and two integers xand y. The integers x and y are the coordinates of an empty tile. 2. Create a function val slide : slidingTile -> int -> int -> slidingTile = <fun> that given a slidingTile and two integers, that represent a location in thematrix, it slides the tile from the specified location to the empty tile, thenreturns the altered slidingTile. If provided location is not adjacent to theempty tile, or out of bounds, then return the slidingTile unaltered. 3. Create a function val print_tile : slidingTile -> unit = <fun> that prints a slidingTile on screen with the corresponding characters fromthe matrix. However, print an empty space where the empty tile is instead.Plaese code in python Create another function count_glorious(low, high) that takes in two positive integers and returns a count of the number of “glorious” numbers between low and high, inclusive. If low is greater than high, return 0. Constraints: count_glorious must contain at least one call to the glorious function from part A. for glorious function refer to the link belowhttps://www.bartleby.com/questions-and-answers/computer-science-question/3b61b8cb-5bda-4d0d-9345-688dd5fb674eCreate the function that takes a list of dictionaries and returns the sum of people's budgets. Examplesget_budgets([ { "name": "John", "age": 21, "budget": 23000 }, { "name": "Steve", "age": 32, "budget": 40000 }, { "name": "Martin", "age": 16, "budget": 2700 }]) ➞ 65700 get_budgets([ { "name": "John", "age": 21, "budget": 29000 }, { "name": "Steve", "age": 32, "budget": 32000 }, { "name": "Martin", "age": 16, "budget": 1600 }]) ➞ 62600
- Describe the input, process and output of the following function. void reserveroom(vector<HotelRoom>& suite){ if (suite.size() < 3) {cout << "At least three rooms must be created...Cancelling request!";return;}bool found = false; //Flagint num, guest;cout << "\n\n\t\t\tRESERVE ROOM\t\t\t\n\n";cout << "Enter the Room Number you want to Reserve: ";cin >> num;for (unsigned int i = 0; i < suite.size(); i++) { //Iterate the roomsif (num == suite[i].GetNumber()) {cout << "\nRoom #" << suite[i].GetNumber()<< "\nCapacity: " << suite[i].GetCapacity()<< "\nDaily Rate: $" << suite[i].GetRate()<< "\nRoom Status: " << suite[i].GetStatus()<< " guest(s)"<< endl;cout << "\nEnter the number of guests to occupy the room: ";cin >> guest;suite[i].ChangeStatus(guest);found = true; //Lowers Flag cout << "________________________________________" << endl;<< "\nRoom #" <<…Why does your group think AnnounceDonation takes two arguments? For example, ("Bread", 5). Place a check (✓) beside your answer. AnnounceDonation accepts one input AnnouceDonation returns a value AnnounceDonation accepts two inputs AnnouceDonation does not return a value Does calling the AnnounceDonation function with different arguments produce the same result? Place a check (✓) beside your answer. Yes No Work as a group to compare the function call to the DonationTimeLeft function and the AnnounceDonation function. Why do you think AnnounceDonation is not assigned to a variable? Place a check (✓) beside your answer. AnnounceDonation accepts one input AnnouceDonation returns a value AnnounceDonation accepts two inputs AnnouceDonation does not return a valueCHALLENGE ACTIVITY 6.6.1: Function stubs: Statistics. Define stubs for the functions get_user_num() and compute_avg(). Each stub should print "FIXME: Finish function_name()" followed by a newline, and should return -1. Each stub must also contain the function's parameters.Sample output with two calls to get_user_num() and one call to compute_avg():FIXME: Finish get_user_num() FIXME: Finish get_user_num() FIXME: Finish compute_avg() Avg: -1 Use Python, please.
- For this c++ hw 1) Make a function that reads in 2 integers from the user. (call it Get2Ints) 2) Make a function that swaps 2 integers (call it swap) 3) Make a function swapAndMult that takes two ints as parameters, and one more int parameter which will be a multiplier swapAndMult should take the two parameters and multiply them by the multiplier. The parameters should return from the function with new values. swapAndMult should NOT print out the values. 4) Make a function that prints 2 integers. Call it Print2Ints Main function should: a) declare two integers and a multiplier b) read 2 integers from the user (use your function) c) print the values of the integers (use the function) d) swap the integers e) print the values of the integers f) read an additional integer (the multplier) from the user g) print the multiplier from the user (sometimes called 'echoing the input') h) call swapAndMult i) print the values of the integersJupyter Notebook Fixed Income - Certicificate of Deposit (CD) - Compound Interest Schedule An interest-at-maturity CD earns interest at a compounding frequency, and pays principal plus all earned interest at maturity. Write a function, called CompoundInterestSchedule, that creates and returns a pandas DataFrame, where each row has: time (in years, an integer starting at 1), starting balance, interest earned, and ending balance, for an investment earning compoundedinterest. Use a for(or while) loop to create this table. The equation for theith year's ending balance is given by: Ei =Bi (1+r/f)f where: Ei is year i's ending balance Bi is year i's beginning balance (note: B1 is the amount of the initial investment (principal) r is the annual rate of interest (in decimal, e.g., 5% is .05) f is the number of times the interest rate compounds (times per year) The interest earned for a given year is Ei - Bi Note the term of the investment (in years) is not in the above equation; it is used…Define a getter function named totalRevenue() that subtracts budget from boxOffice and returns the result. // Code will be tested with a different movielet movie = { title: "Forrest Gump", director: "Robert Zemeckis", composer: "Alan Silvestri", budget: 55000000, boxOffice: 677900000, awards: [], /* Your solution goes here */ };
- CHALLENGE ACTIVITY 6.6.1: Function stubs: Statistics. Define stubs for the functions get_user_num() and compute_avg(). Each stub should print "FIXME: Finish function_name()" followed by a newline, and should return -1. Each stub must also contain the function's parameters.Sample output with two calls to get_user_num() and one call to compute_avg(): FIXME: Finish get_user_num() FIXME: Finish get_user_num() FIXME: Finish compute_avg() Avg: -1 Use Python please.4. Write a function named “removeNegativePrice” that accepts the vector of pointers to PurchaseOrder objects. It will go through that list and remove all PurchaseOrder objects with the negative cost per item. It will also return how many PurchaseOrderobjects that it has removed from the list. Please show how this function is being called and can delete PurchaseOrder objects with negative cost from the list. C++Computer Science Write in Javascript please and use high order functions liek map or filter or reduce let obj = [ { mode: "hot" }, { temp: "low" }, { mode: "cold } ] I want to create a function that get object by key such as: myFunc("mode"); returns { mode: "hot" } next call of myFunc("mode") returns { mode: "cold



