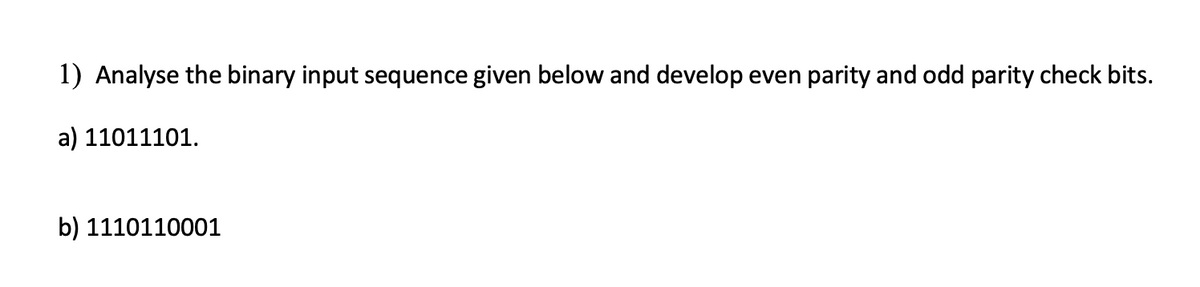
1) Analyse the binary input sequence given below and develop even parity and odd parity check bits. a) 11011101. b) 1110110001
Q: Write a program named CountConsonants that accepts a phrase " Given below " from the user and counts…
A: Note:- As the language of the program is not specified, the below program is in Python language.…
Q: What are the advantages of retaining browsing history, and how long can it be kept?
A: Introduction: The following are some of the advantages of maintaining your browsing history:
Q: Provide screen shot of every step other wise I will give down vote Create a AWS lambda function in…
A: The above question is solved in step 2 :-
Q: Write a program to find the factor of any binary numbers
A: n = abs(int(input("Enter Integer: "))) n0 = n Factors = [] factor = 1 while n>0: bit =…
Q: This structure is the best model for describing the chapters and sections and subsections of a…
A: A Queue is a direct construction which follows a specific request where the tasks are performed. The…
Q: DQ1: You want to use Google dorks to footprint the site but only want results that show file…
A: filetype Description: File type . You can use the filetype: operator in Google Search to limit…
Q: What exactly is cloud-based data storage, as well as some of its primary benefits and drawbacks?
A: Cloud Computing: Cloud computing is the on-demand distribution and pay-as-you-go pricing of IT…
Q: Write a sub called GetName that asks the user to type a first name and last name in an input box,…
A: According to the Bartleby guideline, we are supposed to answer only one question at a time. Kindly…
Q: Provide screen shot of every step other wise I will give down vote Create one s3 bucket in AWS…
A: The above question is solved in step 2 and step 3 :-
Q: This is a third time to uploading question every time expert giving wrong answer. R Code 1.…
A: We need to build decision tree model in r. We need to plot the confusion matrics and print the…
Q: Let Ro be a finite chain ring. For any finite left Ro-module M, the cyclic submodules of M form a…
A: GIVEN DATA :- finite chain ring is -R0 finf out- for any finite left R0-module M,the cyclic…
Q: The One-Time Pad is a symmetric cipher that offers perfect secrecy. If used correctly, there are no…
A: One-Time Pad is also known as unbreakable cipher. The key that is used to encrypt the message is…
Q: In one of convolutional layers a ConvNet, the input has the size of 68x62x32, and you convolve it…
A: ANSWER:
Q: (FYI: Pseudocode is required (Not any programming language) Design a pseudocode program that loads…
A: ANSWER:-
Q: ame, address, city, zip, phone number, email, hourly rate, start date, end date, and number of hours…
A: I have used multi-level inheritence logic to make your program, Kindly check the attached code and…
Q: Q2: Write a program to calculate the average of student who has registered n number of courses.
A: CODE:
Q: You are free to use or not use Mathematica to do the following problem. (a) Let o(x, y, z) = ry + z.…
A:
Q: Create a class Time which contains: ● Hours Minutes Seconds Write a C++ program using operator…
A: #include<bits/stdc++.h> using namespace std; class Time{ int Hours,Minutes,Seconds;…
Q: The counting concept underpins the operation of a digital computer. why?
A: Introduction: A concise explanation of the logic that underpins the operation of a digital computer…
Q: Using C++ and Visual Studios Using your own creativity, make a set of class templates that have…
A: For this class template, put everything in one place--do not declare the member functions and have…
Q: Write down the values of Carry, Overflow, Zero, Sign, Auxiliary Carry, Parity flag after each…
A: Auxiliary carry flag : The Auxiliary Carry Flag (AF) is one of the 8086 microprocessor's six status…
Q: 1. When dose buffer overflows occur Buffer overflows occurs when we do not properly account for the…
A: Buffer overflows occurs when we do not properly account for the size of the data input into an…
Q: Why do you think that the method area of a JVM is shared by all threads running in the virtual…
A: Java Virtual Machine(JVM) => JVM drives the Java Code. => It converts Java bytecode into…
Q: You have a sorted linked list. Fill in the missing code in the following function. void Sorted…
A:
Q: Following is a problem statement. Which of the below provides is the correct variables used for the…
A:
Q: Convert 101 decimal to binary: Convert 1100110 binary to decimal: Convert 85 decimal to binary:…
A:
Q: What are the advantages of multi quadrant drive
A: Hello student
Q: Ques.9 explain Prism's minimum spanning tree and also write its pseudocode to implement it.
A: In this question we have to understand the Prism's minimum spanning tree and also will discuss the…
Q: What is the size of my ROM if I want a maximum output of 6 bits? Is 16 x 6 or 16 x 8 is enough? or…
A: A ROM is referred to as 2n×m ROM size and is defined as having 2n words and m output bits per word.…
Q: Use the Internet to identify and compare three different mobile device management (MDM) tools.…
A: The information provided was mined from: Mobile Device Management Software Compare product features…
Q: What is a MAC address, and how does it differ from an IP address?
A: Introduction: IP addresses and MAC addresses both give unique IDs for internet computers. MAC…
Q: Dont copy & paste form other side Proof of optimality the Huffman tree can now be proved by…
A: Lemma: For any Huffman tree constructed by function buildHuff that contains at least two letters,…
Q: If the IP fragment offset is equal to 40, and sequence number of start byte of payload is 500 then…
A:
Q: What are the many inputs and outputs of the software system design process that must be discusse
A: Introduction: A software system is a collection of intercommunicating software-based components that…
Q: Write a program that will do the following: 1. Create a dictionary with names as keys and grade as…
A:
Q: This is a third time to uploading question every time expert giving wrong answer. R Code 1. Take…
A: We need to build decision tree model in r. We need to plot the confusion matrics and print the…
Q: What models of business processes are used for web applications? What would happen to a web…
A: Solution: There are two key considerations while choosing the development process model. 1) The size…
Q: Let P and V are two atomic operations P represents wait and V represents signal operation. Counting…
A: I will explain it in details,
Q: computer science - How to conduct a training requirements analysis for a new e-learning system…
A: Introduction: An e-learning system is a system that provides learning skills to those who use it.
Q: Write a program in the language of two people in a 1:3 ratio, if the heir is male, the share is…
A: Introduction Input : Heir type Amount Output : Share of parents and heir
Q: You have been hired as an assistant to the head network administrator in an ISP (Internet service…
A: According to the information given:- We have to define the protocol to use in this scenario to…
Q: Develop an activity diagram of the following scenario The 2021 IEEE 23rd International Multitopic…
A: It is one of the UML diagrams under behavioral category. It is used to explain the control flow from…
Q: In java, create a program that gathers user input and prints a paystub. This assignment requires one…
A: Start. Get the details. Perform the operation to find the paystub. Print the result. Exit.
Q: describes the input system used by a IX-generated lexical analyzer (though not by LEX itself). This…
A: describes the input system used by a UX-generated lexical analyzer (though not by LEX itself). This…
Q: We use lots of codes in our personal and business lives. How many can you name?
A: The question has been answered in step2
Q: After MHAV1, what was the platform capable of processing both HSD as well as MPEG-based video?…
A: correct answer is option B.
Q: Write an HTML form that includes the labels, inputs, and similar default settings as seen in the…
A: HTML - <div class="wrapper"><div class="title"> </div><div…
Q: Create a class Time which contains: Hours ● Minutes Seconds ● Write a C++ program using operator…
A: The code is given in the following steps for your reference.
Q: What process model would you propose for incremental software development when you have a team of…
A: Introduction: The following are the attributes of the program that will be created: A fixed 9-person…
Q: 21. Create a program in C++ to find the product of the ASCII values of all digits in the string…
A: CODE:
Step by step
Solved in 2 steps

- Calculate -4 * 5 using Booth's Algorithm, where Q = -4 and M = 5. What is the 8 bit pattern at the end of the 3rd cycle? a. 1101 1001 b. 1011 0011 c. 0000 0011 d. 0010 100135) Assuming seven-bit two’s complement binary representation, write the bit patterns for the following decimal numbers in hexadecimal: a) -73b) -1c) 94Exercise on Hamming Code An 8-bit data word stored in memory is 00111100, while word fetched from the memory is 00101100.1) How many check bits should be combined in word stored and word fetched?2) Find check bits in word stored.3) Find check bits in word fetched.4) Find which bit position contains error.
- Assume you have 4 bits of storage available to store signed binary integers, If possible using the two complement representation of integers, perform binary addition on the following. Is it possible to store the result? Show your work and explain. (-4) + (-5) (-7) + (+3)Calculate (3.41796875 *10-3 * 6.34765625 *10-3) by hand, assuming each of the values arestored in the 16-bit half precision format described in in the textbook. Assume 1 guard, 1 roundbit, and 1 sticky bit, and round to the nearest even. Show all the steps, and write your answer inthe 16-bit floating point format.Assume you have 4 bits of storage available to store signed binary integers, If possible using the two complement representation of integers, perform binary addition on the following... Can you store the result? Show your work and explain! (-4) + (-5) (-7) + (+3)
- Q.1) Add the following 6-bit two’s complement numbers. State the result in hexadecimal and indicate whether overflow occurred. (a) 0x3A + 0x2F (b) 0x15 + 0x2B (c) 0x19 + 0xAUsing binary numbers of 8 bits each, convert to binary and solve the following arithmetic operations using two’s complement representation: (13)10 - (25)10 -(13)10 - (18)10Assuming we are using the Hamming algorithm presented in your text and even parity to design an error-correcting code, find the code word to represent the 8-bit information word 11011011. PLEASE SHOW WORKING, UNDERSTANDABLE THANK YOU
- Add 16 and 16 using two's complement representation with 6 bits. Is there an overflow? a. 100000, no overflow b. 100000, overflow c. 010000, overflow d. 010000, no overflowExample: 1.7 .given the two binary numbers x=1010100 and y=1000011, perform the subtraction(a) x-y; And (b)y-x, by using 2's complement.Character P is encoded as 1010000 in a computer. Usually, a parity bit will be sent together with a character. What is the odd parity bit for character P?

