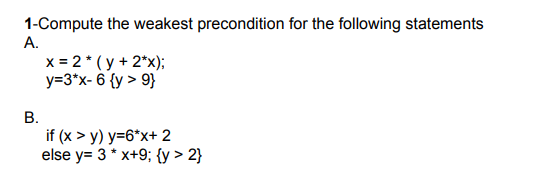
1-Compute the weakest precondition for the following statements A. x = 2* (y + 2*x); y=3*x-6 {y > 9} B. if (x >y) y=6*x+ 2 else y= 3*x+9; {y > 2}
Q: 2-Fully explain the following code and draw all possible outputs. Please input a number between 5…
A: Given code: <!DOCTYPE html> <html> <body> <p>Please input a…
Q: When the CMP instruction sequence is executed, what is the final value for AL register ? MOV AL, 25h…
A: Introduction: CMP instruction is used to compare the two operands. It does so by subtraction one…
Q: Network maintenance is an important task in organizations today who entirely rely on their network…
A: In the third party maintenance (TPM) industry. Network maintenance is essentially what you need to…
Q: What are the advantages and disadvantages of migrating to the cloud, and how do they stack up?
A: Migrating to the cloud refers to transferring data, applications, and other business elements into a…
Q: What exactly is the significance of Linux partitioning in relation to the operating system?
A: Creating and deleting partitions in Linux is a common practice because storage devices (such as hard…
Q: Is there a difference between how you study and how you study on the internet?
A: Here are some ways you can utilise the internet to help (and possibly speed up) your studies:…
Q: Linux is the only operating system that has all of the concurrent methods that are currently being…
A: In the field of software engineering, the word "concurrency" is used to refer to the strategies and…
Q: There are a lot of parallels can be seen between the iterative-and-incremental approach and the…
A: Iterative-and-Incremental: Iterative processes advance by continuous improvement, while incremental…
Q: Q4/Write c++ program by using stack to Push (insert) an element 'J' between two elements 'S' and 'R'…
A: Code (C++) #include <iostream>#include<bits/stdc++.h> using namespace std; int…
Q: For the following regular expression, find the equivalent NFA and then convert that NFA to a DFA:…
A: Given that
Q: Methods Java Write the appropriate method headings using the provided method name for the following…
A: “Since you have posted a question with multiple sub-parts, we will solve first three subparts for…
Q: When the CMP instruction sequence is executed, what is the final value for AL register? MOV AL, 25h…
A: CMP Instruction: An important instruction that is widely used in 8085 microprocessors is COMPARE…
Q: Research should be done to determine the usefulness of wireless network technologies in emerging…
A: Intro In some networks, physical cabling is not used. Wireless networks are gaining popularity…
Q: An information system is made up of a number of different pieces..
A: To collect, produce, and distribute pertinent data, people create and use information systems, which…
Q: architectural design in the software development process.
A: In this presentation, you'll learn about the significance of architectural design in the software…
Q: What kind of difficulties could be encountered by an operating system as a result of its having an…
A: A thread is a flow of execution through the process code, complete with its own programme counter…
Q: f a network upgrade is to take place, when and how long should it take?
A: Definition: Because of technology developments, the company might now work more quickly and…
Q: REMINDER: - Every recursive function must have one or more base cases, -The general (recursive) case…
A: ANSWER:-
Q: Should the operating system be more cautious in how it accesses the system when working with data…
A: Introduction Time-sharing: To properly use the structure, the OS may additionally include accounting…
Q: If you had to compile a list of all of the components that go into the creation of a typical…
A: The central component of the operating system that manages the operation of the software and the…
Q: Operating systems with the term "kernel mode" go hand in hand.
A: The answer of the question is given below
Q: Is there a list of the four most important traits for software developers? Take a look at the other…
A: To Do: to list the four most crucial qualities Answer: The four most crucial aspects of software…
Q: n data is stored in a cache in an entirely associative fashion, how does it
A: Introduction: A cache is a high-speed data storage layer used in computing that keeps a subset of…
Q: Testing is discussed on three different levels: the unit level, the integration level, and the…
A: Explanation Unit testing – what is it? --> Assume you are a software developer who is working on…
Q: A major part of the meaning of "kernel mode" may be attributed to operating systems.
A: Introduction The following section contains detailed information about kernel mode and the numerous…
Q: ElGamal Digital Signatures: How do you make and validate them?
A: The ElGamal signature system is a digital signature scheme based on the computational difficulties…
Q: If you're a systems analyst, what's the point of being bilingual? Which organizations could be…
A: Definition: Being bilingual provides you a significant advantage over the competitors in many…
Q: As a result of today's technology, this is now a reality. How did computers become so prevalent in…
A: The question has been answered in step2
Q: ays in which computer science project scheduling software packages may be helpful. As requested by…
A: Introduction: Project management certification helps set the framework for a successful project and…
Q: at exactly is the significance of Linux partitioning in relation to the operating sys
A: Introduction: Below describe is the significance of Linux partitioning in relation to the operating…
Q: The difference between the internet and the world wide web is a topic that will be covered in this…
A: Analysis of the issue: Using the following categories, distinguish between the Internet and the…
Q: What do you do when you see strangers on social media pleading for money or medical help?
A: The question has been answered in step2
Q: Think of a huge airline's database that uses snapshot isolation for data storage. Which case would…
A: Analyzers of systems The people in charge of creating and designing an information technology system…
Q: What is the main function of router?
A: Introduction: Routers are computer networking devices used to transport data packets from one…
Q: REMINDER: -Every recursive function must have one or more base cases, - The general (recursive) case…
A: The program is written in C .Please check the source code and output in the following steps.
Q: Methods Java Write the appropriate method headings using the provided method name for the following…
A: Step-1: StartStep-2: Call function printArea and pass 4.5 as an argumentStep-3: Call fucntion…
Q: Kernel functions are what Linux relies on to perform the majority of its tasks.
A: The answer is given in the below step
Q: 5. Consider a 5-drive, 300GB-per-drive RAID array. What is the available data storage capacity for…
A: we have given: N =5 (number of disk drives) B= 300GB (Block size) The capacity of the data storage…
Q: Construct a table that differentiates between the functional and non-functional needs of the…
A: Construct a table that differentiates between the functional and non-functional needs of the…
Q: Solving Differential Equation by Laplace Transform My Solutions > Solve the following initial value…
A: Using matlab, we need to solve the given initial value problems. Steps: 1. Define the necessary…
Q: Describe how a firewall resembles a data stream that has been divided into packets.
A: the answer of the question is given below
Q: Write a program that generates a random number in the range of 1 through 100, and asks the user to…
A: The answer for the above mentioned question is given in the following steps for your reference.
Q: the development of a list of the six components that make up an information system, is to give…
A: The information system which refers to the collection of various elements or of the various entities…
Q: Janet insists that the output for the following code should be y is 13. void tridec(int x) {x = 13;}…
A: Explanation: In order for the memory location to remain constant and any changes to the variable to…
Q: What precisely does a Demilitarized Zone, which is more often referred to as a DMZ, bring to the…
A: A Demilitarized Zone: A "demilitarize zone" is an agreed-upon territory between the parties to an…
Q: How about a single line to describe the kernel components that make up a typical operating system?
A: A computer is the kernel: The kernel is a piece of computer software that controls every aspect of…
Q: The procedures of establishing information systems and assessing them are two separate but linked…
A: A formal, sociotechnical: Hierarchical structure called an information system (IS) is designed to…
Q: When making the switch to an ALL-IP network, what do you consider to be the most important…
A: We have provided a few considerations with regard to ALL-IP networks here. In addition, they…
Q: What kinds of challenges does it provide for an operating system to have an architecture that allows…
A: Operating System Architecture: All system resources are accessible to the kernel without…
Q: What does the word "memory void" refer to, and how is it defined? How is this even possible, and how…
A: Definition: A memory void is a mechanism for intentionally editing or cancelling unpleasant or…
Step by step
Solved in 3 steps

- Compute the weakest preconditions of the following statements for the given postconditions. Assume all variables are integers1)a = 2*b + 1;b = a*a + 1;{ a > 10 } 2)if (b > 0)a = 4*b - 10;elsea = b + 172;{ a > 0 }T/F 2. In Java, only if and if-else expressions are used in selection statements.Compute the weakest precondition for the sequence of statements: (Statement 1) b = 2b + 1; (Statement 2) b = b-3{b < 0}
- Explain these c++ statements void bar(int panam) {panam +=1;}(Numerical) a. Write a C++ program that accepts an integer argument and determines whether the passed integer is even or odd. (Hint: Use the % operator.) b. Enter, compile, and run the program written for Exercise 8a.Compute the weakest precondition for each of the following assignment statements and postconditions. x = 2 * y -5; y = x + 2; {y < 2}
- Write assignment statements for the following: Assign a value of 1 to between if n is in the range -k through +k, inclusive; otherwise assign a value of 0 Assign a value of 1 to uppercase if ch is an uppercase letter; otherwise, assign a value of 0. Assign a value of 1 to divisor if m is a divisor of n; otherwise, assign a value of 0.Can I please have the answer in C++ language 4.7: Time Machine Your time machine is capable of going forward in time up to 24 hours. The machine is configured to jump ahead in minutes. To enter the proper number of minutes into your machine, you would like a program that can take a start time (in hours, minutes, and a Boolean indicating AM or PM) and a future time (in hours, minutes, and a Boolean indicating AM or PM) and calculate the difference in minutes between the start and future time. A time is specified in your program with three variables: int hours, minutes; bool isAM; // You can also use a char, i.e. A or P for example, to represent 11:50 PM, you would store: hours = 11,minutes = 50, isAM = false or if using a char, hours = 11,minutes = 50, isAM = 'A' This means that you need six variables to store a start and future time. Write a program that allows the user to enter a start time and a future time. Include a function named computeDifference that takes the six variables as…Mark the following statements as true or false. i. An identifier can be any sequence of digits and letters. ii. In C++, there is no difference between a reserved word and a predefined identifier. iii. A C++ identifier can start with a digit. iv. The operands of the modulus operator must be integers. v. If a = 4; and b = 3; then after the statement a = b; the value of b is still 3. vi. The result of a logical expression cannot be assigned to an int variable. vii. Every if statement must have a corresponding else. viii. The expression in the if statement: if (score = 30) grade = 'A'; always evaluates to true. ix. The expression: (ch >= 'A' && ch = 'Z'. x. The expression !(x > 0) is true only if x is a negative number.
- State the order of evaluation of the operators in each of the following Java statements, and show the value of x after each statement is performed: a) int x =7+3 *6/2-1; b) int x =2% 2+2*2-2/2;(De Morgan’s Laws) In this chapter, we discussed the logical operators &&, ||, and !. DeMorgan’s Laws can sometimes make it more convenient for us to express a logical expression. Theselaws state that the expression !(condition1 && condition2) is logically equivalent to the expression(!condition1 || !condition2). Also, the expression !(condition1 || condition2) is logically equivalentto the expression (!condition1 && !condition2). Use De Morgan’s Laws to write equivalent expressions for each of the following, and then write a program to show that both the original expressionand the new expression in each case are equivalent.a) !(x < 5) && !(y >= 7)b) !(a == b) || !(g != 5)c) !((x <= 8) && (y > 4))d) !((i > 4) || (j <= 6))Solve the following questions: a)Solve the following postfix expressions i)2 3 + 1 - ii)3 4 - 10 + 7 2 3 * - 9 * /a) Convert the following infix to postfix expressions i)2 * 3 - 5 / 2 + 4 ii)1 * 2 * 3 * 4



