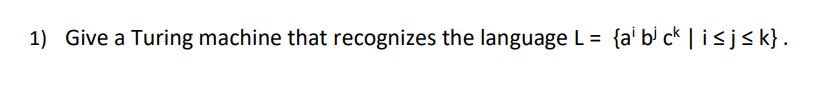
1) Give a Turing machine that recognizes the language L = {ai b³ ck | i≤j≤ k} .
Q: To provide just one example, if you plan on starting a media firm and need individuals with certain…
A: Given: Data that is presently in use is duplicated on a backup storage device. A backup storage…
Q: Why isn't a hash structure the best option for a search key used in range queries?
A: For the reason that: Hash structure is discussed; why isn't it the best choice for a search key that…
Q: What are the two sorts of services provided by the Internet to its users? What are some of the…
A: The Internet provides two types of services to its applications: The Internet offers its…
Q: Code in python Brute Force Attack You will take an encrypted msg and the code will search for the…
A: # The encrypted message and the character set to use for the keysencrypted_msg =…
Q: How large could the new state set be? How small could it be? (Machine M4) i) Justify your answer.
A: Since you have posted multiple questions, we will provide the solution only to one question as per…
Q: What are the two major visual distinctions between the constructor and the class's methods
A: Constructors; Constructors are answerable for instating objects, despite the fact that they produce…
Q: When it comes to solving data storage issues, it's important to weigh the benefits and drawbacks of…
A: Introduction While concluding which data storage arrangement is best for a business, it is…
Q: Q2: Generate 1000 random processing times from a normal distribution with mean = 6 min and stdv 1.2…
A: Python is general purpose because it is used to create different variety of programs and it is not…
Q: Identify the several parts that make up a computer. Discuss how many there are and the number…
A: In this question we need to explain different parts of a computer which make up a computer. We also…
Q: operation of Linux in Business
A: To be a successful Linux administrator, you need to be familiar with the concepts of adjusting…
Q: Provide some background on how reliability and availability are related in the context of a data…
A: Data Communication Networks: In a network, a computer is considered reliable if it consistently…
Q: In modern businesses, what role does IT play in facilitating communication?
A: In this question we need to explain the role of Information Technology (IT) in facilitating…
Q: Palindrome program in C Get the number from user. Hold the number in temporary variable.…
A: Palindrome program in C
Q: What exactly is a memory leak in C++? Why is it important to address it?
A: Given: Could you please explain what a memory leak is in C++? Why should anything be done about it?…
Q: Database management systems may be useful even for single-user programs with little data needs. Are…
A: Given: "It is usually wise to utilise a database management system, even for small applications with…
Q: Brief introduction to the pros and cons of having global connection in a cloud computing setting.
A: Cloud computing is a technology that enables businesses to provide consumers with compute services…
Q: What are some examples of Automata Theory in action?
A: We need to give examples of Automata Theory in action.
Q: They have revolutionized the way their business clients obtain software and resources by providing…
A: Cloud computing infrastructure which refers to the one it is the collection of hardware and software…
Q: Write a single SQL statement to list albums with three columns: the title of the album, the total…
A: Creating Table Album: First create the Album Table using below query, CREATE TABLE…
Q: When it comes to solving data storage issues, it's important to weigh the benefits and drawbacks of…
A: When it comes to solving data storage issues, it's important to weigh the benefits and drawbacks of…
Q: Question 4 There are some errors exist in the following HTML files, read it carefully and fix the…
A:
Q: Is your computer's or mobile device's operating system easily accessible? Why is this advantageous
A: An operating system is in charge of managing software, processes, memory, and hardware. It enables a…
Q: There are many distinct methods in which information may be generated and processed by a computer…
A: Data processing It is a method for compiling unreliable data and turning an interpretation into…
Q: Question 7 Based on the function below, assume that the passed input parameter for x=4; What will be…
A: Question 7) C Program: #include <stdio.h> int fun1(int); int func1(int x) { int b;…
Q: Is Microsoft Excel used for data collection and tabulation in at least three main places at your…
A: MS Excel is mainly used for reporting, data analysis, and storage. Because of their excellent visual…
Q: Thoughts about the upsides and downs of becoming global in the cloud computing setting.
A: Introduction: With the use of this technology, businesses may provide their clients compute services…
Q: How does cloud scalability operate, and what is it exactly? What characteristics of cloud computing…
A: Cloud scalability In cloud computing, Cloud scalability refers to the ability to increase or…
Q: Short notes regarding phishing and spyware are required. Please be certain that you do it properly.…
A: The first step is to explain phishing and spyware. Phishing is a sort of social engineering often…
Q: Provide some background on the connection between network reliability and availability. Explaining…
A: The length of time the infrastructure is operational without interruption is tracked by network…
Q: What kinds of network topologies are allowed, and which ones do you recommend using?
A: Introduction: The configuration of a network, which comprises nodes and connecting lines through…
Q: What is the distinction between computer architecture and computer organisation, and how can the two…
A: Answer: The needs and design implementation for the various components of a computer are…
Q: The advantages of cloud computing are many, but what are some of the more notable ones? Is cloud…
A: According to the policy we can only give the answer of first three questions, repost your remaining…
Q: ng Windows, what's the difference between the modes nd the ones that don't?
A: Introduction: The majority of us are familiar with the power-off state at this point. All open…
Q: The main goal of computer networking is to connect computers and other devices so they may…
A: Network:- Network is defined as a collection of computer systems that are connected to each other…
Q: true or false please quickly thanks ! (a) Every computer that we use is connected to the Internet…
A: False. Most computers are not connected to the Internet backbone directly. They are connected to the…
Q: How do you add a hyperlink to an email message in Windows?
A: Body of an Email: Body. The actual text of the email is contained within the body. In most cases,…
Q: (15) 6. Minimal polynomial: a) Find the minimal polynomial of √3i over Q. b) Find the minimal…
A: Solution for the given question,
Q: Provide some background on how reliability and availability are related in the context of a data…
A: In the context of computer networking, "reliability" refers to the degree to which a computer…
Q: n a few phrases, describe four distinct kinds of public key distribution scheme
A: Introduction A public secret's an oversized numerical worth that's wont to inscribe knowledge. The…
Q: Suppose nodes A and B are on the same 10 Mbps broadcast channel, and the propagation delay between…
A: Please refer to the following step for the complete solution to the problem above.
Q: What are some technical benefits a business may get from selling its products on Amazon rather than…
A: Selling the goods via Amazon rather than your own e-commerce website has the following technical…
Q: Using examples from computer science, compare and contrast the concept of abstraction. To emphasise…
A: Our mission: The answer is on the significance of abstraction in software engineering and what the…
Q: What exactly is System Call and what does it imply? How does the operating system handle this?
A: Required: a) What does System Call mean? How does the operating system handle it? System calls…
Q: Evaluate the postfix expressions by using the algorithm in the book. You MUST show the steps to get…
A: First Let's see the rule to follow that will be used to evaluate the postfix expression. Algorithm…
Q: There is one rule that must be followed when passing a property to a method as a parameter. What…
A: Answer:
Q: In computer engineering, what is the distinction between synchronous and nonsynchronous buses?
A: S.NO Topic Synchronous Bus Asynchronous bus 1. Clock Rate A synchronous bus works at a fixed…
Q: Can you explain the main difference between logic programming and procedural programming?
A: In this lesson, we'll break down the key differences between logic programming and its procedural…
Q: Carefully designed algorithms should not have any hidden meanings.
A: Algorithm: The algorithm is a sequential procedure. A well-designed algorithm should be devoid of…
Q: Check out how low-income areas use wireless networks. WiFi is preferred over LANs and physical…
A: Introduction: Wi-Fi is a wireless technology that connects computers, tablets, smartphones, and…
Q: Define the function: int power (int base, int exp); It accepts the arguments for base and exponent…
A: Here I have defined the recursive function named power(), which will return the power of the given…
Step by step
Solved in 2 steps with 1 images

- 10 Consider a Turing machine that cannot write blanks; that is, for all λ(qi, a) = (qj, b, L or R), b must be in Γ- {□}. Show how such a machine can simulate a standard Turing machine.. Define a Turing Machine that accepts the following language:L = {w ∈ {!, }∗| w = vw'v where v, w' ∈ {!, }∗, |w'| = 2, and |v| = 3}Determine a Turing machine for the language L = {ww_ | w is a string of 0s and 1s} where w_ is the reversed string of w. If w = 011, then w_ = 110. The Turing machine must therefore check whether the input string x belongs to the language L. Draw a Finite state machine
- Determine a Turing machine for the language L = {ww | w is a string of 0s and 1s} where w is the reversed string of w. If w = 011, then w = 110. The Turing machine must therefore check whether the input string x belongs to the language LSuppose we make the restriction that a Turing machine must always write a symbol different from the one it reads, that is, if δ(qi; a) = (qj ; b; L or R), then a and b must be different. Does this limitation reduce the power of the automaton? Explain.Construct a Turing machine that semi-decides the language ac*bc*a. Does the same machine also decide this language? Explain why.
- Please draw out a DETERMINISTIC Turing MachineConstruct a Turing Machine M, which accepts the language L = {w|wea²b²m,n=m21) over the alphabet (a, b).Fact: ATM {{M, w) | Turing machine M accepts w} is undecidable. So is HALT {(M, w) | Turing machine M halts on w}. = Prove that the following language is undecidable. Here M is a Turing machine. L= {(M) | M halts on at least one input and infinite loops on at least one other input} .
- Construct a Turing Machine that accepts the language L defined as follows: L = { w: num, (w) #num,(w) }.Let T be the Turing machine defined by the following 5-tuples:(s0, 0, s1, 0, L)(s0, 1, s1, 0, L)(s1, 0, s2, 1, R)(s1, 1, s1, 1, R)(s0, B, s1, 1, R)(s1, B, s2, 0, R)(s2, 0, s3, 1, R)(s3, 1, s3, 1, R)(s3, 0, s4, 0, R)For the following tape, determine the intermediate tapes, states, and head positions; and final tape, state, and head position when T halts. Assume T begins in the initial position.states0 | B | B | 1 | 0 | 0 | B | B | B |Consider L={(TM) | TM stands for the Turing machine, which halts on all input, and L(TM)= L' for some undecidable language L'}. The encoding of a Turing machine as a string over the alphabet 0-1 is (TM), and L is? decidable and recursively enumerable decidable and recursive decidable and non-recursive undecidable and recursively enumerable

