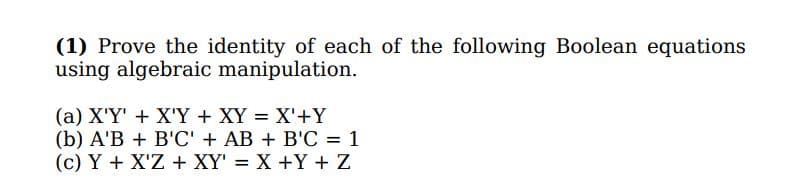
(1) Prove the identity of each of the following Boolean equations using algebraic manipulation. (a) X'Y' + X'Y + XY = X'+Y (b) A'B + B'C' + AB + B'C = 1 (c) Y + X'Z + XY' = X +Y + Z
Q: The three primary activities of a program are __________, __________, and __________.
A: Introduction: System software refers to the programmes that control and manage the basic functions o...
Q: Exercise 5.27 Find the Green functions on the following regions in R a) the semi-ball B(0, R) n {(z,...
A:
Q: Write an ARM assembly program to convert temperatures from Celsius to Fahrenheit or from Fahrenheit...
A:
Q: Assembly language ARM-Cortex I am using a Tiva Board With Port F open with PF1 output, and PF0,PF4 ...
A:
Q: 14) Suppose FSA M1 and M2 are defined as follows: M1(Q, S, qo, A, 8) = ({I, II, III }, {a, b}, I, {I...
A: According to the information given:- we have to follow the instruction and perform the task.
Q: Perform Quick sorting algorithm using the given array elements: 1, 3, 9, 8, 2, 7, 5 where the pi...
A: # Quick sort in Python # function to fin # Quick sort in Python # function to find the partition p...
Q: Overflows in Java's buffers are regarded to be "safe." As a result, does this mean it's better suita...
A: Introduction: Security is a critical component of all development projects in any business. The Jav...
Q: Given the underlying array [845747269, -1503365430, 21201], what is the value of the Oth nybble in D...
A: Solution:
Q: ᴜꜱɪɴɢ ᴍᴀᴛʟᴀʙ ᴄʀᴇᴀᴛᴇ ᴀ ᴠᴀʀɪᴀʙʟᴇ ꜰᴛᴇᴍᴘ ᴛᴏ ꜱᴛᴏʀᴇ ᴀ ᴛᴇᴍᴘᴇʀᴀᴛᴜʀᴇ ɪɴ ᴅᴇɢʀᴇᴇꜱ ꜰᴀʜʀᴇɴʜᴇɪᴛ (°ꜰ). ᴄᴏɴᴠᴇʀᴛ ᴛʜɪꜱ...
A: Find the required code given as below and output:
Q: wer the following: Let R be a subset of pixels in an image. We call R a region of the image if R is ...
A: Neighbors of a Pixel . N4 (p) : 4-neighbors of p.• Any pixel p(x, y) has two vertical and two flat n...
Q: In what way does the choice of a data typefor a field help to control the integrity ofthat field?
A: Lets see the solution.
Q: Assembly Language in the KEIL software,
A:
Q: Write a Python program to list all the files which is present under "/" directory.
A: I have provided DIRECTORY SCREENSHOT , PYTHON CODE and CODE SCREENSHOT WITH OUTPUT ---...
Q: To facilitate access to external file systems, the Virtual File System layer was utilised. It did, h...
A: The primary goal of the virtual file system layer is to allow client programs to access various type...
Q: Determine whether there is a feasible schedule for the following set of periodic processes. If yes, ...
A: Given Determine whether there is a feasible schedule for the following set of periodic processes. If...
Q: please use java to answer the following question Develop a GUI application to manage product file...
A: JavaFX GUI A JavaFX GUI-based product management application. Have a pane label, three input element...
Q: 2. Consider the following grammar, and try to parse the string ))). conversion and steps in LL(1) pa...
A: Given 2. Consider the following grammar, and try to parse the string ) ) ) ) ) ) ) using all the con...
Q: Differentiate the different I/O mapping method. Do not just define each method. Give examples on how...
A: INTRODUCTION: The monitor, mouse, keyboard, computer data storage, hard disc drive (HDD), graphic ca...
Q: Discuss the benefits and drawbacks of often updating software.
A: In the world of computing, software is the application software that runs on computers and performs ...
Q: Who was the world's first female computer programmer and how did she do it?
A: Computer is discovered in the early 1830s by Charles Babbage, then later most of the generation came...
Q: Explain the difference between an object file and an executable file.
A: Lets see the solution.
Q: What problems can arise during view integration or merging relations?
A: Lets see the solution.
Q: Is there a date on when the ENIAC was created?
A: With ENIAC's completion in February 1946 and a cost to the government of $400,000, the war that it w...
Q: Write a program to evaluate the arithmetic statement A*[B+C*(D+E)]/ F*(G+H) (a) Using 3 address inst...
A: Lets see the program in the next steps
Q: Hi Experts! Would you please try to solve this as soon as possible with 100 % Accuracy? If possible,...
A: A bootstrap is the program that initializes the operating system (OS) during startup. The term boo...
Q: What changes would you need to make to ensure that the application works on mobile phone browsers?
A: Lets see the solution.
Q: Write a Java program using OOP concept that perform the union and symmetric difference between two s...
A: Algorithm: Start Create a class named setClass with data(which is set which stores character value)...
Q: his Batch file has 4 commands to execute what are they
A: The four commands are given below.
Q: In the code cell below, create and populate an instance of a weighted graph to represent the followi...
A: Import the networks module in your code. Select the file. Create the graph with certain parameters...
Q: Describe the whole process of designing address subblocks and back it up with an example of separati...
A: The given IP address is 10.10.10.0 /27 Here /27 means # of network ID bits is 27. Therefore number o...
Q: Needing help with networking question: Which of the following commands can you use to diagnose DNS p...
A: DNS stands for domain name system which is conversion of numeric ip address into string address.
Q: Q14: Write C++ program to find e from the following series: e =1+x+ (x / 2!) + / 3!) + ... (x / al) ...
A: Lets see the program in the next steps
Q: 0-9 vercase alphabetic characters vercase alphabetic characters and digits 0-9
A: 2. Ans: In Modulud Arithmetic Z26, we have 26 characters, The all characters are assigned a un...
Q: What processes may be utilised to develop a knowledge of how computers were bought, used, and invent...
A: Computers: A computer is a machine that can react to commands and conduct logical and mathematical p...
Q: In what way did the computer get made?
A: Introduction: Computers store and process data using a binary system of ones and zeros. Computers a...
Q: Was the contemporary computer developed at some point in the future?
A: Introduction: First Modern Computer: Charles Babbage was an English mathematician and inventor and t...
Q: source programs and the screenshots of your MARS execution windows. 2. Create the data declaration ...
A: 1) program : .dataName: .asciiz "James"Age: .byte 24Numbers: .word 11, 33, 20Letter1: .asciiz "M" ...
Q: 1.A type of peripheral device that is used in sensors and actuators. (Complete Name/Statement) 2. I...
A: Answer: Answer-1: Sensors and actuator both are peripheral device which is used to connect with robo...
Q: Q4. Why does kernel need data structure? If O means busy and 1 means free, what does 1001101 bitstre...
A: Kernel needs data structure to store about the current state of the system. That means if any new da...
Q: Write a test program that invokes these functions to display the following tables: Celsius Fahrenhei...
A: #include<iostream> using namespace std; double celsiusToFahrenheit(double celsius){ //con...
Q: In C language program that uses an ARRAY for (C)ourtside (M)id and (U)pper; Please try to use an arr...
A: //code in C #include<stdio.h>#include<conio.h>#include<ctype.h>#include<stdlib...
Q: Are read, write, and execute permissions sufficient for controlling access to web applications? Why ...
A: I have answered this question in step 2.
Q: Suppose a survey study is conducted asking subjects to taste 6 different ice-cream flavors (chocolat...
A: quantity. For example, ice cream flavoursoWith nominal data, all we can do is record the frequency o...
Q: Find the C program language Starting My Business by CodeChum Admin I want to be an entrepreneur!...
A: The if statement evaluates the test expression inside the parenthesis (). If the test expression is ...
Q: Set up a scenario in which the CIA's three pillars of integrity are all present.
A: Introduction: Integrity is the most crucial quality in the CIA trifecta. Its purpose is to protect t...
Q: In the below cell, we have imported all the functions you will need to complete this assignment; not...
A: ANSWER:-
Q: Hardware and software are two different things. What is the difference between the two?
A: Difference between hardware and software is mentioned below,
Q: Complete the below function in Python language def checkPassword(pass): #pass must have length betwe...
A: Required:- Complete the below function in Python language def checkPassword(pass): #pass must have a...
Q: 1. Create a console program that will perform the following: Ask the user to enter the pieces of app...
A: Start input number of apple input total price output original price and output converted price stop
Q: 3. Is Recursive Descent Parser (RDP) more powerful than LL(1) parser ( or LL(1) is a subset of RDP)?...
A: answer is
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

- Computer science need correct Answer Simplify the following algebra expressions, (i) x'+y'+ xyz' (ii) A + A'B + A'B'C + A'B'C'DComputer Science: Use appended Table to show that the following Boolean identities are satisfied. Boolean variable and/or Boolean expressions postfixed with ’ symbol are considered negated. For instance, X’ is equivalent to NOT X.a. X + ( X’ Y + X Y )’ = X + Y’b. (( X Y ) Z ) + ( Y Z ) = Y Zc. X’ Y = X’ Y + X’ Y Zd. (X + Y) = XYZ’ + XY’Z’ + X’YZ’Simplify the following Boolean expressions to a minimum number of literals indicating theorems used for each step . 1. ABC + A 'B + ABC' 2. x'yz + xz 3. (x + y)'(x' + y') 4. xy + x(wz + wz') 5. (BC' + A' D)(AB' + CD ')
- 2. Simplify the following Boolean expressions, using three variable K-maps: (a) F(x,y,z) = xy+x′y′z′+x′yz′ (b) F(x,y,z) = x′y′+yz+x′yz′ (c) F(x,y,z) = x′y+yz′+y′z′Simplify the following functional expressions using Boolean algebra and its identities. List the identity used at each step. a) F(x,y,z) = y(x' + (x + y)')b) F(x,y,z) = x'yz + xzc) F(x,y,z) = (x' + y + z')' + xy'z' + yz + xyzValidate/ prove that the following Boolean Laws/Theorems are the equal/same using the Truth Table: 2. X.Y + X'.Z + Y.Z = X.Y + X'.Z
- Simplify the following equation using Boolean Identities: ~x~yz + ~xy~z + x~y~z + x~yz + xy~z + xyz Construct truth tables for the following: xyz+ x~(yz) + ~(xyz) (x + y)(x + z)(~x + z) Use the truth tables from the previous question to create equations in SOP and POS format. Develop truth tables for the following equations: a) (A+B)(B+C)b) ~A(B + C)c) (A+B)^(CD)Given the Boolean function F below, reduce it to a simplest form using identity laws. Provide step-by-step activities along with the identity used at each step. F(X,Y,Z)= X’Y’Z + X’YZ + XY’Z + XYZQuestion 6 Computer Science Simplify the following Boolean Algebra expression using Boolean Identities (where ' means "not") (A+B+C+D')(E+A)(E'+B+C+D')
- Question 4the complement of the following logical expression xy'+ywUsing the laws of boolean algebra simplify these expressions and LIST the laws used to justify each step. . Each final result should be expressed as a sum of products of literals, where each product uses the smallest number of literals. a. ABC + ABC’ + A’C + A’B’C + AB’C b. A'B' + A'BC' + (A + C')' c. A' + A'B'CD' + A'B'C'D' + AB'C' + AB'CD' + ABD + BC'DShow that the argument is valid, indicating the rule of inference or logical equivalence applicable to each step. ∃x ( C(x) ∧ ( ¬ S(x) → ( V(x) ∨ W(x) ) ) )∀x ( V(x) → ¬ C(x) )¬ ∃x ( W(x) ∧ C(x) ) _________________________∴ ∃x ( S(x) ∧ ¬ W(x) )

