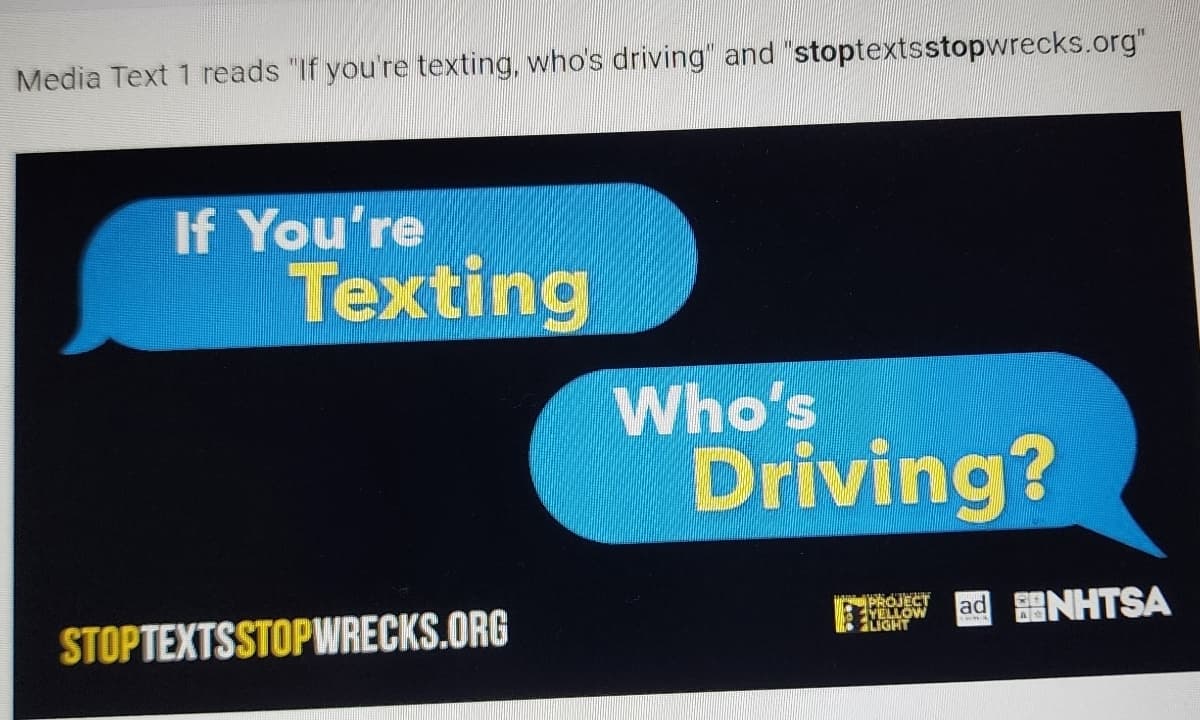
1-) What is the purpose of the media text? How do you know this? 2-) who is intended audience for the Media text? How do you know this? 3-) Identify and explain one persuasive technique ( graphic, visual, colors, symbol, typography, etc.)
Q: When it comes to software requirement engineering, why should COTS (Cost On The Shelf) selection be…
A: Below we provide an overview of why software requirement engineering uses COTS (Cost On The Shelf)…
Q: Is it possible to sum up software engineering in a few words? You say, "What's wrong with it?"
A: Software engineering refers to the practise of developing, operating, maintaining, and eventually…
Q: How many different methods are there to access a file? Can you tell me the pros and cons of using…
A: A file access definition can control access to data in specified tables and columns, or to tables…
Q: When we talk about "file handling," what do we mean, and why do we need file handling services in…
A: In programming, we might need to generate a certain type of input data multiple times. Only…
Q: Think of a situation that calls for the administration of logins, and then provide some informed…
A: Given: Scenario management is a practical method for organizing potential futures and developing…
Q: How does the authentication using multiple factors work? In order to stop someone from stealing your…
A: MFA is a security solution that requires several forms of authentication from various credential…
Q: What, if anything, do we expect authentication to do? Examine and contrast the merits and drawbacks…
A: Introduction Authentication: Identification of users who demand access to a connection, site,…
Q: What is the explanation of the issue, and what precisely is the function of the program that checks…
A: 1. Encryption is the study of secure communication techniques that allow only the sender and…
Q: Consider the many different options available in terms of graphic and picture altering software.
A: The above question is solved in step 2 :-
Q: Please, could you describe the idea of a challenge-and-response authentication system to me in your…
A: The answer to the question is given below:
Q: What type of relationship does the world of data communications have with the area of…
A: Let's examine the answer. the benefits of the database strategy that overcomes the restrictions of…
Q: What role does today's technology play, and how is it used, in ensuring that communication is…
A: Answer: We need to write the what are the role play today's technology to ensuring the communication…
Q: More information on the nature and operation of a memory hierarchy is provided below. For what…
A: It creates a hierarchical structure for computer storage that is based on how rapidly the computer…
Q: omes a virtual partner in the creative process. List and briefly explain the four interconnected…
A: Introduction: Hardware and software make up the computer technology that enables us to create…
Q: I need to know what the term "prototype" means in the context of computer programming.
A: Prototyping is a useful tool in software development as it allows developers to test and refine…
Q: If your network is very straightforward, what commands have you used and what troubleshooting?…
A: In this question we have to understand if network is very straightforward, what commands should be…
Q: Describe how a challenge-response system works in the context of a secure login process. Do you…
A: Using a challenge/response system, users are given a confidential password that is also saved in a…
Q: How many processes are involved in making a website? Explain each procedure and its significance in…
A: There are several processes involved in making a website, including: Planning and research: This…
Q: In Linux, what purpose does the system's partitioning serve?
A: System partitioning Disk partitioning or System Partitioning is the process of dividing up a hard…
Q: How would you succinctly explain what software engineering is for? Just what are you trying to find?
A: Software engineering is a systematic approach to designing, implementing, operating, and retiring…
Q: What impact does hierarchy have on the size of an organization as well as the administrative…
A: Answer:
Q: In this day and age, what part do restrictions on access play in the bigger picture of everything…
A: Here is your solution step by step -
Q: Volatility to the requirements caused by the change in the scope, however this is not always true.…
A: Introduction Software development is troubled by requirements volatility, which could also lead to…
Q: Are you able to demonstrate the benefits of using the Work Breakdown Structure (WBS) concept by…
A: "A work breakdown structure lists all of the activities required to accomplish a project, divides…
Q: what what is meant by the term "multifactor authentication" in this context. In what ways does it…
A: Multifactor authentication (MFA) is a security measure that requires users to provide more than one…
Q: What are the many different kinds of metrics for the dependability of software that are available?
A: Introduction The dependability of the software product is estimated utilizing reliability measures.…
Q: As firms expand and post increasing information about their business activities on their websites,…
A: Given: We have to discuss web mining and its types. What are the Web's significant challenges for…
Q: Explain the main strategies used to compress digital videos.
A: Redundancy in video data can be decreased and eliminated through the use of video compression…
Q: Authentication using challenge-response mechanisms needs further description. What exactly makes it…
A: The two basic components of challenge-response authentication in its most fundamental form are a…
Q: The concept of a finite state machine is essential, but what exactly does that term mean?
A: Finite state machine definition A specific kind of automata known as a finite state machine, which…
Q: How does the software as a service (SaaS) paradigm work? Could you please give me a brief…
A: Introduction to Software-as-a-Service: SaaS is a paradigm for delivering software that enables…
Q: Within a switched and routed network, how does the department ensure user access?
A: There are numerous approaches to assure user access in a switched and routed network: ACLs: These…
Q: Please offer an explanation of the mechanism used by the system that allows you to circumvent all of…
A: See the solution. database benefits over classic file management systems: Data reduction. The…
Q: What are some of the objectives that the LOCAL directive is working toward in order to achieve its…
A: Assembler directives are textual instructions that tell the assembler how to carry out a specific…
Q: The administration of logins in a made-up situation may be broken down into its component parts…
A: The approach of managing several futures and crafting scenarios that are precisely fitted to a…
Q: Reflection of constructing exam.
A: Designing tests is an important part of assessing students understanding of course content and their…
Q: There are several different approaches that may be used when managing logins. Put everything you've…
A: The complete explanation may be found in the subsequent stages. Explanation: => Provide a…
Q: When you speak about the goals of the authentication process, what precisely is the ultimate result…
A: Definition: Authentication is used when servers need to know who is accessing their information or…
Q: Is there anything that we are able to do with authentication's assistance? As you can see, selecting…
A: Is there anything that we are able to do with authentication's assistance As you can see, selecting…
Q: In HTML5, what precisely does the canvas element do?
A: Introduction The Hypertext Markup Language, all the more frequently known as HTML, is the markup…
Q: In the context of the design and development of software, how does the concept of coupling compare…
A: In the context of the design and development of software, how does the concept of coupling compare…
Q: In HTML5, what precisely does the canvas element do
A: INTRODUCTION: HTML: The Hypertext Markup Language, more often known as HTML, is the markup language…
Q: Question 9 nag Consider the following computational problem: Given two length-n arrays R and C,…
A: Greedy approach:- The greedy approach is an algorithmic approach that attempts to solve a problem by…
Q: Draw the corresponding Gantt diagrams for this scheduling algorithms; - First Come First Served.
A: Given table contains 5 processes from P1 to P5. Each process contains it's arrival time and Burst…
Q: Speculate about a situation in which login credentials need to be managed and then describe the…
A: Provide an example of a fictional circumstance involving login management. Identify many distinct…
Q: Authorization lists have to be encrypted and guarded from prying eyes since it is so simple to…
A: Authentication is the process of confirming the credentials of a person or device requesting access…
Q: Did using authentication help us get closer to our objectives? In this part, we'll examine the…
A: Introduction The method involved with learning whether a person or thing is who or what it professes…
Q: Concoct a made-up story to show how the sign-in procedure works, and use it as an example. It's…
A: Scenario management is an efficient way to handle several futures and create customised scenarios.…
Q: What takes place if it is not possible to construct a resource that is part of a stack?
A: Introduction With CloudFormation, user maintain connected resources as nothing more than a single…
Q: Describe a finite-state machine.
A: A finite-state machine is a mathematical model of computation. It is an abstract machine that can be…
Step by step
Solved in 2 steps

- PLEASE I NEED URGENTLY THANK YOU For this task just think of this code as your code and prove what changes you would make with before and after photos Task Program Amendments Following your testing make any amendments necessary to ensure that the program runs to specification. Submit your program code with comments showing clearly where amendments have been made. Here examples (attached image section) I WANT AT LEAST 3 CHANGES / SCREENSHOTS Same like examples and write small writing about what you did. my code Pastebin link because of word limit https://pastebin.com/K9xpCevhHi there, can you please create a PHP file based on the instructions in the image please?. You don't have to finish 100% of it, just around 70% is fine and try your best if you can do more :) I really appreciate it and will definitely give a thumbs up! Thank you so much and have a great day!!Create a project named ClassicBookSelector that contains a Form with a ListBox that lists at least five classic books that you think all educated people should have read. When the user places the mouse over the ListBox, display a Label that contains a general statement about the benefits of reading. The Label disappears when the users mouse leaves the ListBOX area. When the user clicks a book title in the ListBOX, display another Label that contains a brief synopsis of the specific book. Also, change the BackColor of the Form to a different color for each book.
- What is the output of the following program? DO NOT COPY FROM OTHER WEBSITES Upvote guarenteed for a correct and detailed answer. Thank you!!!Instructions 1. Study the syntaxes in this image file: sample.PNG 2. Go to this online IDE. 3. Create a Python script that will compare two (2) numbers entered by the user. Refer to the attached image and to the following algorithm. There is no need to create a class similar to how Java works. 3.1. User enters the first number. 3.2. User enters the second number. 3.3. If the first number is less than, greater than, or equal the second number, a message is displayed. 4. Upload the .py file and a screenshot of your output.Help me out guys Posting this same question 2nd time. Please attach write code with screenshot Otherwise downvoted directly. Do fast. Don't make sense Don't give me wrong answer
- Note: If the code for three files would be too big and cannot be placed fully here, send the zip folder with three files (mentioned below) to amir.luganda@bk.ru, please. It is very urgent and important, so, please, send the files to the email, please. Design a JavaFX Calculator App using Java programming language that implements the basic arithmetic operations of the calculator. Your design should reflect (but it's not mandatory) the basic layout of the calculator depicted below. You can have your own original design. JavaFX recommended components to be used: GridPane Buttons or TilesPane TextFields Submission files: Calculator.java CalculatorController.java Calculator.fxml What should be included Symmetry of design Color balance Readability of text is easy and clear Filenames must follow the naming convention of JavaFX MVC design pattern All Buttons react to buttonPressed event properly Arithmetic operations (addition, subtraction, multiplication, division) are working Button "C"…UCAS-W3SCCHOOL-SMALL PARAGRAPH ----not table ---- (IMPORTANT DONT COPY PASTE WRITE YOUR OWN WORD, FIRST PERSON WRITING!) NO HANDWRITING NO COPY PASTE THANK YOU!What can I do if each line gape is very close, also box is very close (box means where you fill up). Also buttons gaps are close(For example- under the page you have three buttons- next, beack, edit). So how can I write each word has enough space and enough size. using react, please write a code. See sample example
- Need Simple C++ OOP project it can be game I.E Car or Snake or Lodo, managment or your choice related but project should be long i.e 350-400 lines and simple (it only look long nothing else required) Please any unique which is not available in youtube or google No pointers use, no struct, no vectors, no graphics Thanks I have seen your projects like managments, games its great please make a project for me that make my teacher happy thanks :)Question is attached in screenshot appreciate the help thanks! fwefw eeproperties so that the given output is produced. Do not change any given code. s1 = ShoppingCart() p1 = Product("Razer BlackShark","Headset",99.99,5) p2 = Product.createProduct("Razer Huntsman","Keyboard",249.99,12) print("1.====================================") s1.addGadget(p1,p2) print("2.====================================") s1.setCartName("Amazon") s1.addGadget(p1,p2) s1.addGadget(Product("HyperX Fury","Mousepad",26.99,21)) print("3.====================================") print("Total Products created:",Product.totalProducts) print("4.====================================") s1.printCartDetails() print("5.====================================") s1.removeFromCart("Logitech G ProX Superlight") print("6.====================================") s1.removeFromCart("Razer Huntsman") print("7.====================================") s1.printCartDetails() Output: 1.==================================== Please set the cart name first. 2.====================================…



