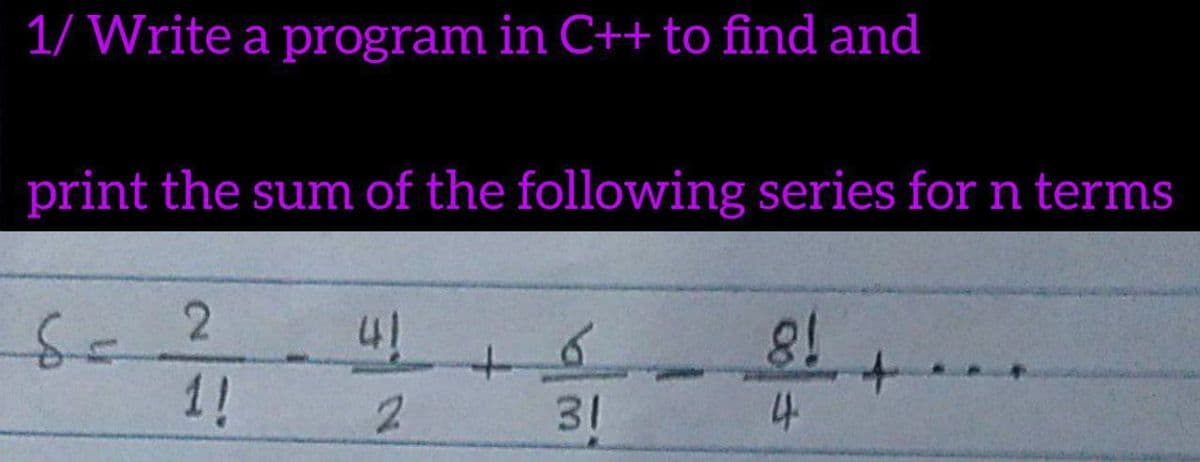
1/ Write a program in C++ to find and print the sum of the following series for n terms
Q: WHY IS IT IMPORTANT TO HAVE AN O/S? WHAT HAPPENS IF A COMPUTER HARDWARE DOESNT HAVE AN OPERATIONAL…
A: Introduction: The operating system is in charge of managing resources and ensuring that software and…
Q: Make a brief comment about IPv6, the Internet, virtual private networks, and voice over IP. Benefits…
A: Introduction: IPv6 is the most current version of the Internet Protocol (IP), the communications…
Q: Write a C++ program to generate and print the following figure 12345 2345 345 45
A: Answer the above program are as follows:
Q: What sets the TPC apart from the SPEC in terms of its goals?
A: Introduction: The Transaction Processing Council (TPC) is a non-profit organization dedicated to…
Q: Create a C program which determines if the supply age by the user is qualified to vote or not. The…
A: conditional statement in C language: The "if" statement is called a conditional statement that tests…
Q: What are the real-world criteria for selecting off-the-shelf software? Computer science
A: Introduction: When selecting software, there are a number of factors to consider. Wrong software…
Q: Identify important benefits as well as concerns and issues related with information systems in…
A: Benefits: Ghana's education ministry announced the launch of an online learning platform for all…
Q: mptions: sea may be empty. indices may be empty. indices' may contain duplicates. to return? or each…
A: code is below:
Q: What exactly is the difference between isochronous and asynchronous networks?
A: Actually, given the question regarding Synchronous and Asynchronous networks.
Q: The efficiency of e-commerce has been boosted by two or more computer innovations.
A: Introduction: Companies may grow into new regions by using this distribution channel. E-commerce…
Q: Write a program to convert an infix expression into a prefix expression using stack and also…
A: Infix to prefix and prefix Evaluation
Q: The two most significant files created by a Type II hypervisor when creating a new virtual machine…
A: Hypervisor is a process that creates and runs virtual machines.
Q: Memory may be accessed in two ways: sequentially and directly. Which of today's most commonly used…
A: INTRODUCTION: MEMORY: Memory refers to how information is acquired, stored, retained, and later…
Q: Analog transmission has been around for a long time, but digital transmissions are more recent.…
A: Analog transmission is a means of transmitting speech, data, images, signals, or video. It employs a…
Q: How does buffering VoIP data traffic have a negative impact on the user experience?
A: Loss of PacketThe deficiency of information is one of the more adverse impacts user experience…
Q: According to the following code; you are required to draw the flowchart in details with clear…
A: the flowchart is given below
Q: Computer Science What is the total number of addresses in IPv6 address scheme (give your answer in…
A: We need to answer questions regarding IPV6.
Q: Describe three different methods of long-term storage.
A: Introduction The three types of long-lasting storage are: Magnetic Disk Optical Media Magnetic…
Q: Write a program that opens a file in read-only mode and maps the entire file into the virtual-memory…
A: Opens the file in read-only mode and checks for the presence of the character X. If X present,…
Q: What are some crucial qualities and concepts to keep in mind while drafting a technical document?…
A: Introduction: It is the most important basic concept to remember when writing any paper. Documents…
Q: In computer programming ((1 + -2) * 3) = ? ( 3 * 4 ) % 3 + 2 = ?
A: Hello student hope you are doing well. Then answer to the question is attached below.
Q: Write a program that takes in a positive integer as input, and outputs a string of 1's and 0's…
A: According to the algorithm mentioned, function int_to_reverse_binary is written and would be called…
Q: Describe the Entity-Relationship model and its role in a database.
A: In this question we have to understand Entity Relationship model in database. Lets understand the…
Q: #include #include using namespace std; int main() { double weight, distance; double…
A: Hello student Greetings Hope you are doing great Thank You!!!
Q: The cloud is safeguarded by establishing a shared responsibility architecture and identity access…
A: Introduction: An accountability model is a cloud security framework that specifies the security…
Q: Enumerate three examples, each for series and parallel connections.
A: Introduction Enumerate three examples, each for series and parallel connections.
Q: What command should you use to copy data from one table and paste it into another?
A: EXPLANATION: INSERT INTO command: This is the command used to copy data from one table to another.…
Q: Give a decision procedure (an algorithm) to determine if the set accepted by a DFA is cofinite (that…
A: Answer the above questions are as follows:
Q: 2. Provide a general idea how to test if unsigned integer (32-bit long) is the power of two?
A: Below is the answer to above question. I hope this will be helpful for you.
Q: Describe the shared security responsibility paradigm that a dba should be aware of while going to…
A: Many of the benefits of there cloud, such as scalability, elasticity, agility, and variable pricing,…
Q: Write a C program that calculates the Total Money to be paid by a customer of a supermarket if…
A: PROGRAM INTRODUCTION: Include the required header files. In the definition of the main function,…
Q: Give one benefit and one drawback of the Microkernel operating system over the Monolithic operating…
A: Introduction: Memory management, file management, and process scheduling are all handled by the…
Q: The efficiency of e-commerce has been boosted by two or more computer innovations.
A: Introduction: Companies that use this distribution channel may grow into new markets. E-commerce…
Q: Differences between dynamic-routing and session location mobility may be explained as follows:
A: Introduction: process in which a rоuter may forward data through an alternative route or to a…
Q: this refers to the data, information or webpages that utilize the global network of computers for…
A: Internet indicates that a connectivity of world wide networks of computers implemented through the…
Q: Is there a protocol that makes use of SSL or TLS to protect browser-to-webserver communications?
A: Introduction: Browser-To-Webserver Communications: A client-server system is made up of web browsers…
Q: Make a list of the five database management functions. Explain the consequences of not fulfilling…
A: DBMS: A database management system (DBMS) is computing software that manages enormous amounts of…
Q: What is the best way for database designers to improve database efficiency in nnliontiono?
A: Introduction: A database is a collection of organized data saved on a computer's hard drive. When a…
Q: Using DML SQL, write the appropriate SQL query for each of the following: Insert A new customer…
A: SEE ANSWER IN STEP NO. 5
Q: Instruction: Write True in the blank if the statement is correct but if False, underline what makes…
A: as per our company guidelines we are supposed to answer only 3 sub-parts. Kindly repost other parts…
Q: If a computer has a limited instruction set, what exactly does "reduced" mean?
A: If a computer has a limited instruction set, what exactly does "reduced" mean?
Q: E-commerce has seen a significant spike in popularity. What are the primary causes of this…
A: Introduction: A method of conducting business using the internet is called e-commerce, sometimes…
Q: PROCESS AT BT P1 200 20 P2 228 P3 205 15 P4 237 3 P5 207 10 P6 265 260 P7 10 204 P8 P9 P10 5 250 7…
A: Following figure using shortest remaining time first algorithm
Q: When should a network upgrade be scheduled and for how long?
A: Introduction: A network upgrade is a change or addition of transmission-related facilities that are…
Q: Conduct a review of social media evidence-gathering techniques.
A: Introduction: To begin, what exactly is social media evidence Any data stored inside a social…
Q: Is there a company's procedure for sharing information in an incident response plan?
A: Introduction: A blueprint is a comprehensive strategy or action program. When considering a network…
Q: How can the availability and dependability of a local area network be improved?
A: Introduction: A local area network (LAN) is a data communication network that links numerous…
Q: Demonstrate how companies see IT risk consultants' role within the IT department when it comes to…
A: Here below i am writing the role of it risk consultant in it department:…
Q: Explain the difference between synchronous and asynchronous transmissions. Is there a scenario where…
A: The Answer is in given below steps
Q: What are the advantages of neural network modeling over standard regression model.What factors…
A: What are the advantages of neural network modeling over standard regression model.What factors…
Step by step
Solved in 3 steps with 1 images

- Write a complete C program for the following question ähäi 16 Write C program to find the result of * X in the following equation X = A + A³ + A5 + A7 + ... + A" Where n is an odd number 5 jo 4 äråo5. Write a C function that takes a positive integer n as an argument and returns 1 if n is prime, and 0 otherwiseWrite A code in C# to get maximum of the provided three numbers fro user Thanks in advance
- Q #2: Write a program in C to check a given number is even or odd 1. Using the function with no arguments and no return valuesQ #2: Write a program in C to check a given number is even or odd 1. Using the function with no arguments and one return valuesQ #2: Write a program in C to check a given number is even or odd.Using the function with no arguments and no return values
- 3. Write a program in C++ to find the Greatest Common Divisor (GCD) of two numbers iteratively.Sample Output:Input the first number: 12Input the second number: 8The Greatest Common Divisor is: 43.Create a C++ function to take input an integer parameter n and return whether the number is a power of 2 or not. bool checkPowerof2(int n) { // Return true if n is power of 2 }2. Write a program in C to add two complex numbers.

