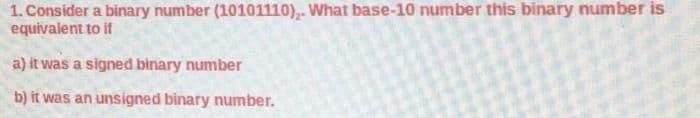
1. Consider a binary number (10101110),. What base-10 number this binary number is equivalent to if a) it was a signed binary number b) it was an unsigned binary number.
Q: Could you tell me the names of the three primary frequency bands used in wireless communication syst...
A: Wireless communication systems make extensive use of three primary frequency bands, the names of whi...
Q: Consider an implementation of QuickSort that, given an array A[0..n - 1] of n elements, always choos...
A: Algorithm: quickSort(array, leftmostIndex, rightmostIndex) if (leftmostIndex < rightmostIndex) ...
Q: What does it imply to claim that two items have a "is a" relationship?
A: Is-a (is a or is a) is a syntactic relationship between abstractions (for example types, classes) in...
Q: C++ Please explain the code below. It doesn't have to be long, as long as you explain what the impo...
A: Please refer below for your reference: I have added comments in every line so you can understand: La...
Q: In C program Given two arrays: the first one having all the scores and the second being the test num...
A: Here, I have to write a C program to the above question.
Q: Given: The root of Tree T1 is Node M D G K H N Tree T1 1. Determine: Breadth-First Traversal of Tree...
A: Given: The root of the tree t1 is Node M. We have to determine Breadth first search and pre-orde...
Q: Problem #3 - Search a string. Write a program which counts the number of a particular character foun...
A: I give the code in C along with output and code screenshot
Q: ####### in python ########## Calculate the approximate solution of th system of equations. xy = (z^2...
A: Python Code We can get the L¹ norm using the linear algebra module of the Numpy package which offers...
Q: Given: Language L2 = {w | w has as many 0's as 1's} Determine: Reversal of L2 = L2^R
A: Given :
Q: How do you keep track of elements in a partially filled array
A: Partially Filled Array An array that is partially filled has indexes that aren't being used to stor...
Q: Bookm. Suppose the HTML file for your web page project includes a div element with the id value "cup...
A: what should be placed in the blank to complete the function
Q: draw and explain generic block diagram of an IoT device. explain in what circumstances you will pref...
A: IoT devices are the nonstandard computing devices that connect wirelessly to a network and have the ...
Q: What are some of the similarities between string and lists?
A: Lists can be changed, but Strings cannot. Second, list members can be of many types, whereas a Strin...
Q: What is multifactor authentication, and how does it work? What role does it play in password securit...
A: What is multifactor authentication, and how does it work? What role does it play in password securit...
Q: e know the order of growth is O(n). List the steps leading to your calculation in case your answer i...
A: the answer is an given below :
Q: In what circumstances would you prefer to utilize an abstract class over a base class?
A: Abstract class is a type of class that is declared with the "abstract" keyword. It can have both abs...
Q: What does a Details view entail?
A: EXPLANATION AND ANSWER: DETAILS VIEW: If a programmer wants to display the columns of a single row o...
Q: 1.2. Fully discuss how interrupts improve the efficiency of the processor; make use of a diagram to ...
A: As per the company guidelines we are provide first three question answers only.so please repost rema...
Q: What are the most important computer science concepts to understand?
A: Introduction: The study of computers and computing, as well as its theoretical and practical applica...
Q: What does a Details view entail?
A: Details view shows the clear view of the particular area with having greater clarity. Lets understan...
Q: To inspect the File System (e.g. NTFS) of a partition/volume, we can use the following utility tool(...
A: We need to discuss DISKPART, FSUTIL and WMIC commands.
Q: Salespeople are identified by their id, name and deptID; and might take trips. EaC rip has a from-ci...
A: Here below we make simple ER diagram with cardinality, attributes, entities and relationship: =====...
Q: e problem areas based on the elevations in various regions and the expected rise of the nearby river...
A: Explanation: ask the user for river rise check the list for elements less than rise and change thos...
Q: What component does an application use instead of dealing directly with the database?
A: Introduction: What component does an application use instead of dealing directly with the database?
Q: f 64KB is hav $ 24 bits. Th to the cache s. е са
A:
Q: e Your Task: Write a program that creates a file - Your program should request the user to enter...
A: the code is an given below : Program - import java.io.FileWriter; import java.util.Scanner; public ...
Q: Write the program in python Using a list of integers (which you may code directly into your program...
A: Here I have created the function to get the pairs. Inside the function, I have used a loop to extrac...
Q: To format a number stored in the variable x using the local standards for displaying numeric values ...
A: to format a number stored in the variable x using the local variable for displaying numeric value
Q: of the following is false in reference to python ? Dictionary is an unordered collection of key-valu...
A: Solution:
Q: est non negative r
A: given - Is pivot raw the highest non negative ratio
Q: UML Activity Diagram for plotting the unemployment rate include swimlanes.
A: Here is the uml diagram for plotting the unemployemeny rate include swimlanes
Q: Assume that all the course syllabus in your working directory are named by a major çode of three alp...
A: Given :- Assume that all the course syllabus in your working directory are named by a majorcode of t...
Q: What is Session State in HTTP?
A: Given :- What is Session State in HTTP?
Q: necessary to describe VRAM.
A: We are going to understand VRAM in computers. VRAMs stand for Video Random Access Memory. Let's unde...
Q: What happens if the priority levels of numerous processes are the same in CPU scheduling?
A: Introduction: The scheduler permits each process to execute for its own time as long as they are rea...
Q: The Perrin numbers, P(n), are defined by the recurrence relation Р(п) — Р(п — 2) + P(п — 3) - with i...
A: Actually, python is a easiest programming language. It is a dynamically typed programming language. ...
Q: Discuss various security vulnerabilities linked to memory management.
A: Various security vulnerability linked to memory managment
Q: If you mistakenly delete a file and want to recover it, you must do the actions outlined below.
A: We are going to understand if one has deleted a file in their system then how can one recover it.
Q: Write down the four circumstances in which CPU scheduling choices are made.
A: CPU scheduling permits one operation to use the CPU while the other's processing is delayed (in a wa...
Q: Draw a flowchart or write pseudocode to represent the logic of a program that allows the user to ent...
A: Flowchart:
Q: Learn everything there is to know about social networking. What exactly is autonomous computing, and...
A: Introduction: Social networking sites such as Facebook, Twitter, and LinkedIn are examples of intern...
Q: Create a function to calculate a shopper’s total spending, excluding shipping and tax amount, with B...
A: Introduction Create a function to calculate a shopper’s total spending, excluding shipping and tax ...
Q: NOTE: USING C++ ONLY Implement all the functions from the Question 2 and make a login and sign up m...
A: Implementation of functions to login and registration of a user that stores in a file is given below...
Q: n of jQuery is to “drive broad adoption and ongoing development of key JavaScript solutions and rela...
A: Explanation: The purpose of jQuery is to make utilizing JavaScript on your website easier, as well ...
Q: What is the significance of architecture? Consider a project and map it both withou and with archite...
A: Introduction: As we all know, software architecture is the mapping of strategic needs to architectur...
Q: 4. Design an algorithm for computing Vn] for any positive integer n. Besides assignment and comparis...
A: Task :- write an algorithm to find the square root of the given number n.
Q: Many system architects base their IT system designs on an n-tier architecture, wheren is a number wi...
A: let just first know What is Architecture? A specification for how a set of software and hardware tec...
Q: What are the consequences of loading extra characteristics (that may or may not be required for anal...
A: Introduction: PySpark overview PySpark is one of the interfaces for Apache Spark in Python. It acti...
Q: Explain what the stack pointer register is and what it does in a few words.
A: Given: Explain what the stack pointer register is and what it does in a few words
Q: Suppose we have a virtual address of 26 bits in a byte addressable machine. Page size is 8K bytes. A...
A: Suppose we have a virtual address of 26 bits in a byte addressable machine. Page size is 8K bytes. A...
Step by step
Solved in 3 steps with 2 images

- A(n) __________ is an integer stored in double the normal number of bit positions.E. What is the hexadecimal representation of each of the following binary numbers?I) 0011 0101 1101 1010II) 1100 1110 1010 0011III) 1111 1110 1101 10111) Using IEEE 754 representation for single precision floating point, give the 32-bit binary encoding for the numbers below.Show the sign, exponent, and mantissa (significand).a. -2.40625b. 11.2265625 2) Given the following binary number: 1101.0111, what will be its decimal numberequivalent?
- 1)Using IEEE 754 representation for single precision floating point, give the 32-bit binary encoding for the numbers below.Show the sign, exponent, and mantissa (significand).a. -2.40625b. 11.2265625 2) Given the following binary number: 1101.0111, what will be its decimal numberequivalent?6. Convert the following numbers from unsigned binary notation to decimal notation, and from 6-bit 2's complement notation to decimal notation: i) 110011, ii) 001101, iii) 101101 7. Show how each of the following floating point values would be stored using IEEE-754 single precision (be sure to indicate the sign bit, the exponent, and the significand fields): a. 12.5 b. −1.5 c. 0.75 d. 26.625 8. The following is a representation of a decimal floating value using IEEE-754 single precision. Find out the value in decimal. 0 10000011 10101000000...0Convert the following decimal number into equivalent binary number and hence write the binary number in 64- bit long real format (53.36755) i need the answer by same way example through picture please.!
- A. How many bits are needed to represent 214(octal) in binary?B. Show the 2’s complement binary (10 bits) representation of (-246)(10)C. Convert the following 2’s complement binary number to decimalrepresentation:10010010D. What is the minimum number of binary bits needed to represent each of the following unsigned decimal integers?I) 65II) 409III) 16385A binary code uses ten bits to represent each of the ten decimal digits. Each digit is assigned a codeof nine 0’s and a 1. The code for digit 6, for example, is 0001000000. Determine the binary code forthe remaining decimal digits.
- State the minimum number of binary bits needed to represent 42319 unsigned decimal integers ?Suppose you are given 6-bit signed fixed-point number in binary where there are 3 bits before and 3 bits after binary point. Calculate its range and precision. Also, convert 110.011 in 4-bit unsigned binary fixed-point number to decimalB. What is the decimal representation of each of the following unsigned binary integers? 11111000 11001010 11110000

