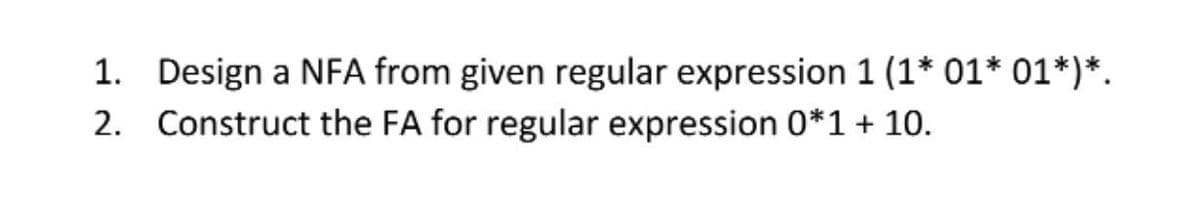
1. Design a NFA from given regular expression 1 (1* 01* 01*)*. 2. Construct the FA for regular expression 0*1 + 10.
Q: Exactly how many different kinds of programming paradigms do you think there are? Then, why are…
A: The term programming paradigm alludes to a way of programming. It doesn't allude to a particular…
Q: Q3. A link has a signal-to-noise ratio of 2000 and a bandwidth of 12000 KHz. What is the maximum…
A: AS, we know in case of noiseless channel SNR ratio is 0. and Therefore bandwidth of channel is same…
Q: What does the Organization's history imply? As it relates to the request for new web servers?
A: Introduction: Web server: a brief overview of its origins and purposeAn internet server, also known…
Q: Both the sequential search algorithm and the binary search algorithm have distinct benefits, but…
A: Introduction: Searching in a particular order. There is no need for a sorted list. It can be used in…
Q: The image below is the assignment, and above that is the code written to solve it... Please explain…
A: C# is the programming languages that are developed with the .NET framework library. It is developed…
Q: A security incident response plan's objectives should include preventing theft and security…
A: Introduction Assume the following scenario: What are the tactics and aims for an information…
Q: How does cryptography work with a secret key? Please include a concise explanation, such as how the…
A: Introduction: Secret key encryption employs a single key that both parties must know (normally Alice…
Q: which is transmitted over the channel. Let T(w) denote t word. (a) What is the probability that T(w)…
A: The answer is
Q: Please assist us in locating our check. The query CPU on the database server is rather expensive in…
A: SSMS CPU usage: After you have established a connection to your SQL Server or Azure SQL instance, go…
Q: Which protocol utilizes SSL or TLS to encrypt data sent between a browser and a web server?
A: According to the information given:- We have to find out the protocol utilizes SSL or TLS to encrypt…
Q: An explanation of the challenge–response authentication mechanism is needed. What makes it more…
A: NOTE :- Below i explain the answer in my own words by which you understand it well. Challenge…
Q: When someone claims that data granularity has been specified, what precisely does it mean?
A: Granularity of the data: What exactly does "Data Granularity" mean? A data structure's amount of…
Q: Methodologies and SDLC are obviously distinct. You may explain the software development life cycle…
A: Introduction: SDL (Software Development Lifecycle) manages projects effectively.
Q: Could you kindly describe how a relational database management system works?
A: Intro Could you kindly describe how a relational database management system works
Q: Which data structure is most likely to be included in an implementation of a recursive algorithm…
A: First lets understand what is recursive Algorithm: it is a process which calls itself by reducing…
Q: It's important to know how programming languages have evolved, in your perspective.
A: Introduction: Programmer-specific languages may give several extremely significant advantages, such…
Q: Q.1: Write a program to set 100 in the upper triangular of a given matrix a(4,4). For example array…
A: #include <iostream>using namespace std; int main() { // your code goes here int a[4][4];…
Q: What are the primary distinctions between a two-tier and three-tier application architecture? Which…
A: Intro Three tire database architecture runs faster than two tier database architecture and three…
Q: Scalability in the cloud: could you please explain and clarify it for me? What aspects of cloud…
A: Inspection: Could you please clarify what cloud scalability is and what it means? What criteria…
Q: Is there an organization, management, and technology element of an information system?
A: Introduction: Information system An information system is a cohesive set of components that gather,…
Q: There are various obstacles to overcome before mobile technology becomes a reality. How much money…
A: Web-based services: A web service (WS) is either a service provided by one electronic device to…
Q: Is the internet useful if you have a physical or mental disability? How do you think technology will…
A: Answer to the given question: The internet has assisted individuals with making their lives simpler…
Q: The OSI security architecture contains a wide array of advanced precautions to ensure the…
A: Intro The route used by all packets between their source and destination is the same. It is not…
Q: 15) Write instructions that first clear bits 0 and 1 in AL. Then, if the destination operand is…
A: We need to write an assembly code for the given scenario.
Q: what is Procedure footer ?
A: Introduction: Footer of the procedure:
Q: Explain, contrast, and compare any two of the following security architectural models:
A: Models and architectures for security (Description) -> A security system's security architecture…
Q: GSM time slot is 577 s (microseconds) in duration and includes far more than a snapshot of each ind…
A: The answer is
Q: The distinction between a low-level programming language and a high-level programming language…
A: Language at the Lowest Level: A low-level programming language is one that provides almost little…
Q: Why is the User Datagram Protocol (UDP) not a good choice for the Email application? Describe in…
A: UDP is a protocol for the transport of data that does not need a connection. Because UDP does not…
Q: Could you please discuss the advantages and disadvantages of utilizing MySQL
A: MySQL is a Relational Database Management System (RDBMS) that employs the Structured Query Language…
Q: You are going to create a website for your new business, explain all steps to develop an E-commerce…
A: The above question is solved in step 2 :-
Q: LWC Assignment: Create a LWC component to display the output: Data Binding Example Hello, Jhon Ron!…
A: According to the information given:- We have to define LWC component to display output.
Q: Explain why internet apps must be safe. Why is having a secure application important? SQL injection…
A: Intro Web application security uses several strategies and processes to safeguard browsers and…
Q: Justify why authentication is an issue in today's cyber society
A: According to the information given:- We have to justify authentication is an issue in today's cyber…
Q: c. subnet mask d. 1st, 2nd, xth subnet addresses (where x is the requested number of subnets) e.…
A: The answer is
Q: 10) Functions in high-level languages often declare local variables just below the return address on…
A: According to the information given:- We have to write a function in high level language on the basis…
Q: Share information about the ARP protocol with a coworker. Include information about the layer it…
A: Inspection: Tell a coworker about the ARP protocol. Mention the layer it works at, as well as the…
Q: What distinguishes Powler, Pacu, and ScoutSuite in the realm of cloud security? Using cloud security…
A: Intro All data communications must be highly encrypted in order to reduce danger. Authentication is…
Q: Provide a description of the CNSS security model.
A: The Answer is
Q: ion systems in te
A: Information system, an integrated set of components for collecting, storing, and processing data and…
Q: 14) Write instructions that jump to label L2 when the signed integer in AX is greater than the…
A: Given that: Write the instruction for jump to label l2 when ax > cx Instruction: cmp ax,cx jg L2…
Q: write a c++ code to inserting 25 elements. into stack using linked list data structer and display…
A: #include <iostream>using namespace std;//node class for linked listclass node{ public:…
Q: Is there a standard format that a business case for moving to the cloud should follow?
A: Encryption: Compare the following cloud differentiators with your buying infrastructure while…
Q: java
A: Introduction Java is a kind of programming language that is being used for object oriented…
Q: You should apply three different classification algorithms to one arff dataset and compare the…
A: You can also use the Apriori technique on a different dataset. Explain all of the rules and provide…
Q: Is the security architecture of Open Systems Interconnection (OSI) equipped with cutting-edge…
A: Non-repudiation: When neither the sender nor the recipient of a communication may refute the…
Q: What exactly is the benefit of executing the server application before the client application? When…
A: The answer is given below.
Q: There is a routing table in the figure on a router. If packets with the following destination IP…
A: The routing table given is:- Address Next hop 198.52.60.0/23 Ethernet 0 198.52.62.0/23…
Q: Determine the most crucial components of an information technology system. To have a…
A: Introduction: The fundamental elements of an information system
Q: Which of the following are noun phrases? indicate all that apply "the woman" "the crispy apple"…
A: A noun phrases is a group of two or more word that is headed by a noun that include modifiers Even…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 2 images

- Draw a parse tree for expressions, (i) A:=B+C+ A(b) Find a regular expression that matches the FA above. (e) If the FA is a DFA, draw an equivalent NFA. If it is an NFA, draw an equivalent DFA.67. In BASIC language statement "300 LET A = 2(X+3)", syntax error is a. subtraction sign missing b. asterisk sign missing c. GO function is missing d. NET function is missing
- Question 1 A) Build an expression tree for the following expressions: (x+y) * (a-b) Explore the expression tree using: i. Prefix - ii. Infix - iii. Postfix - B) Build an expression tree for the following expressions: X*(Y/Z) Explore the expression tree using: i. Prefix - ii. Infix - iii. Postfix -a) Construct the FA from the given Regular Expression a(a + b)*b + b(a + b)*a(a+b)* (aa) (a+b)*Pls answer the 3 subparts c d and e
- Linear Algebra using MATLAB. Solve the following problem using MATLAB. Write the syntax and the MATLAB out put on the space provided.Peter withdrew 10000 pesos from his bank account today. He uses 5000 to fix his car. Then, he divide the money into 5 equal parts and gave away 4 parts and kept 1 part for himself. He took his wife to the restaurant and spent 600 pesos on meals. The remaining cash was divided among his 5 children for their allowance. Write a numerical expression in MATLAB syntax to represent this situation and then find how much money Peter has now?Design DFA for the following Language. Where Σ= {0,1){w l w starts with a 01 and ends with a 01)Evaluate following prefix expressions /-AB*+DEF *^+A/BD-EFG /*-AB/DE**FGH



