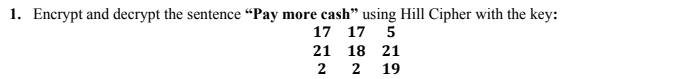
1. Encrypt and decrypt the sentence “Pay more cash" using Hill Cipher with the key: 17 17 5 21 18 21 2 2 19
Q: Determine the values of a, if any, for which all solutions of the differential equation y" – (2a – 1...
A: Given: Let us consider the given second-order homogenous equation yιι-2α-14yι+α2-14α+40y=0.
Q: 3. Write down the integral of a function f(r,0) in polar coordinates, over the integration domain de...
A: Given graph, We have to find integral of function in polar form of shaded region. We clearly see's...
Q: Howe2 A Cylinder of radiur (r) about 2 m and heis tht about 3 m Find the maximumerrurs in measuri
A: Introduction: The volume of the cylinder of radius r and height h is given by, V=πr2h To find an err...
Q: We have two complex numbers (C1 = 1+ j2) and (C2 = 4/-2.2°). Find %3D 1. Ст * С2 2. Ст — С2
A:
Q: Show wheatear the statements are True or False (provide explanation/justification). a. sup A E A' b....
A:
Q: Xn →1 and yet xn Yn . Find sequences (xn) and (ym) so that Yn does not converge to 0. . Let (xn) be ...
A:
Q: Determine the area of the region bounded by y=2x^2+10, y=4x+16, x=-2 and x=5. * 2/3 9. 46/9 O 1/3 O ...
A: Given curve is y=2x2+10, y=4x+16, x=-2 and x=5. We have to find the area of the region bounded by th...
Q: Suppose that a “word” is any string of five letters. Repeated letters are allowed. For our purposes,...
A: Disclaimer: Since you have posted a question with multiple sub-parts, we will solve first three sub-...
Q: Problem 1: A. In the piggy bank I have 90 coins. 20 quarters, some pennies, and 30 half dollars. How...
A: total coins =90 quarters=20; pennies=40; half dollar=30
Q: 16.9. Let y denote the boundary of the domain between the circle Iz| = 4 and the square whose sides ...
A:
Q: Let x be a solution of the differential equation d²x 뜨r + 8x = 0 df 8. such that x(0)=1/10, x'(0)=0....
A:
Q: - What does it mean to be a "function"? How can you determine function ality of a relation set or eq...
A:
Q: 2. v=i +k, u= 5i + 12j Find: u.v, |미, lu씨 b. the cosine of the angle between u and v. the scalar com...
A:
Q: Q1.Classifying the following differential equation: Linear or Governing Equations # В.С. # LC. Why? ...
A: “Since you have posted a question with multiple subparts, we will solve the first three sub-parts fo...
Q: Jerry will make deposit of 450 at the end of each quarter for 10 years. At the end of 15 years, Jerr...
A:
Q: dI(t) The voltage VL(t) across the inductor, where VL(t) = L · dt %3D The total voltage V(t) across ...
A:
Q: 2. Hノ=1geノ-1 アrンィ 8タ=ー =/ク(=2
A:
Q: A perpetuity has payments at the end of each four-year period. The first payment at the end of four ...
A: Present Value = P1×V4 + P2(V4)2 + P3×(V4)3 + ...Where P1 is the first payment, P2 is the second paym...
Q: Let x(t) be a Brownian motion with x(0). Mathematically prove or disprove that -4x(t)is a Brownian m...
A:
Q: Show that 97248 -1
A:
Q: i have 18 books what are two ways i can stack them in epaul groups
A: Permutations and combinations
Q: 6. Which of the following is NOT true? a. A point on the bisector of an angle is equidistant from th...
A: Let us solve the problems based on basic geometry using various properties of triangles in the next ...
Q: 9. What is the main purpose of Gage R &R? Write 2 or 3 lines.
A:
Q: (2)Solve the following initial valne Problemss- a) Xy'+Y=0(r2) = -2), b) e*y'=2(x+1)y° (ro) -V6) , c...
A:
Q: (D5+3D + 4D³ + 32 cos (2a) + 3e 12D²) y = 16 sin (2x)
A: The given differential equation is D5+3D4+...
Q: Suppose that an is a series so that its partial sums Sk = a1 +az + ...+ ak satisfies %3D n=1 1 1. k...
A: In kth partial sum, Sk of an infinite series converges to s, then series also converges to s. Also h...
Q: (7) Show that the given functionis an integrationy factory Solves a) Sinydx+ Cosydy =0(e), b)(a+i)Yd...
A:
Q: Question 4 The current I(t) in an LC series circuit is governed by the initial value problem below. ...
A:
Q: Determine the values of p. q, and r so that the function f(z) = pr + qa2 + rz will have an inflectio...
A: Given function is fx =px3 +qx2 +r x The function has an inflection point at (1, 2). The slope of the...
Q: Determine the! limit of the following sequence: (an} ={(1+ ) (-1)" cos n 2 %3D n2 i.e. cos n lim 1+ ...
A:
Q: On a hot Saturday morning while people are working inside, the air conditioner keeps the temperature...
A:
Q: Q.26 Let S, be the hemisphere x? + y? + z? = 1, z > 0 and S2 be the closed disc x? + y? <1 in the xy...
A:
Q: Suppose the productivity P of an individual worker (in number of items produced per hour) is a funct...
A:
Q: • A composite figure is a figure that can be into that are basic plane figure |, trapezoids, rectang...
A: (a) A composite figure is a figure that can be divided into regions that are basic plane figures.
Q: Determine the Equation from the information below: HA: none X-Int: (0, 0) VA: none Y-Int: (0, 0) Hol...
A: The graph of a straight line crosses the x axis at the x-intercept and the y axis at the y-intercept...
Q: b i Find the y-coordinates of the points of intersection of the parabola with equation...
A:
Q: Q– Fin the surface area of the portion of the paraboloid z= 6- 2x -y that is above the x-y plane (z-...
A: Solution :-
Q: 2- Solve the following system of equations using the Gauss and Gauss-Jordan elimination methods. 2x1...
A:
Q: 4. Prove that 17– 3v3~ 83 + 47V3 in Z+ ZV3. 5. Prove that 6 is not a prime in Z + ZV-6. 6. Prove tha...
A:
Q: For which odd primes p is 3 a square mod p?
A:
Q: Determine the Equation from the information below: X-Int: (5, 0) 3 HA: y = 4 VA: x =- 1 Y-Int: (0, =...
A:
Q: Let x be a solution of the differential equation d?x * + 8x = 0 df 8. such that x(0)=1/10, x'(0)=0. ...
A:
Q: how many factors does 16480464000 have
A:
Q: (8) Find the Integrating Factor of the equations and Solve it:- a)2 Coshx Cosydx=Sinhx SinyAY,b)(2co...
A: Since you have posted a question with multiple sub-parts, we will solve first three sub-parts for yo...
Q: and g. Be sure to put a scale on your graphs. 1) f) = -2". g(x) = 5- 2" 2) f(x) = 3", g(x) =-.3" +5 ...
A: "Since you have asked multiple questions, we will solve the first question for you. If you want any ...
Q: Hw.s Anofen cylinder Can hag an tnside radius 82cm and an inside heightof s cmuse the total derivati...
A: Volume of the cylinder with radius r and height h is given by V=πr2h For the volume of the metal use...
Q: Let u(x, y) be the solution of the partial differential equation (x+1)yu̟ -u, =0, x>0, y >0, y with ...
A:
Q: 3) Approximate the value of following integrals by using composite Trapezoidal rule, composite Simps...
A:
Q: Let V be the volume of the solid obtained by rotating about the y-axis the region bounded y = sqrt...
A:
Q: Use the method of cylindrical shells to find the volume generated by rotating the region bounded by ...
A: We will use Cylindrical / shell method to find volume of the solid generated
Trending now
This is a popular solution!
Step by step
Solved in 4 steps with 3 images

- Suppose that in an RSA Public Key Cryptosystem, the public key is e=13,m=77. Encrypt the message "go for it" using two-digit blocks and the 27-letter alphabet A from Example 2. What is the secret key d? Example 2 Translation Cipher Associate the n letters of the "alphabet" with the integers 0,1,2,3.....n1. Let A={ 0,1,2,3.....n-1 } and define the mapping f:AA by f(x)=x+kmodn where k is the key, the number of positions from the plaintext to the ciphertext. If our alphabet consists of a through z, in natural order, followed by a blank, then we have 27 "letters" that we associate with the integers 0,1,2,...,26 as follows: Alphabet:abcdef...vwxyzblankA:012345212223242526Suppose that in an RSA Public Key Cryptosystem. Encrypt the message "algebra" using the -letter alphabet from Example 4. Use two-digit blocks. Use three-digit blocks. What is the secret key?a. Excluding the identity cipher, how many different translation ciphers are there using an alphabet of n "letters"? b. Excluding the identity cipher, how many different affine ciphers are there using an alphabet of n "letters," where n is a prime?
- Suppose that in an RSA Public Key Cryptosystem. Encrypt the message "pascal" using the -letter alphabet from Example 4. Use two-digit blocks. Use three-digit blocks. What is the secret key?Suppose that the check digit is computed as described in Example . Prove that transposition errors of adjacent digits will not be detected unless one of the digits is the check digit. Example Using Check Digits Many companies use check digits for security purposes or for error detection. For example, an the digit may be appended to a -bit identification number to obtain the -digit invoice number of the form where the th bit, , is the check digit, computed as . If congruence modulo is used, then the check digit for an identification number . Thus the complete correct invoice number would appear as . If the invoice number were used instead and checked, an error would be detected, since .Rework Example 5 by breaking the message into two-digit blocks instead of three-digit blocks. What is the enciphered message using the two-digit blocks? Example 5: RSA Public Key Cryptosystem We first choose two primes (which are to be kept secret): p=17, and q=43. Then we compute m (which is to be made public): m=pq=1743=731. Next we choose e (to be made public), where e must be relatively prime to (p1)(q1)=1642=672. Suppose we take e=205. The Euclidean Algorithm can be used to verify that (205,672)=1. Then d is determined by the equation 1=205dmod672 Using the Euclidean Algorithm, we find d=613 (which is kept secret). The mapping f:AA, where A=0,1,2,...,730, defined by f(x)=x205mod731 is used to encrypt a message. Then the inverse mapping g:AA, defined by g(x)=x613mod731 can be used to recover the original message. Using the 27-letter alphabet as in Examples 2 and 3, the plaintext message no problem is translated into the message as follows: plaintext:noproblemmessage:13142615171401110412 The message becomes 13142615171401110412. This message must be broken into blocks mi, each of which is contained in A. If we choose three-digit blocks, each block mim=731. mi:13142615171401110412f(mi)=mi205mod731=ci:082715376459551593320 The enciphered message becomes 082715376459551593320 where we choose to report each ci with three digits by appending any leading zeros as necessary. To decipher the message, one must know the secret key d=613 and apply the inverse mapping g to each enciphered message block ci=f(mi): ci:082715376459551593320g(ci)=ci613mod731:13142615171401110412 Finally, by re-breaking the message back into two-digit blocks, one can translate it back into plaintext. Three-digitblockmessage:13142615171401110412Two-digitblockmessage:13142615171401110412Plaintext:noproblem The RSA Public Key Cipher is an example of an exponentiation cipher.
- Suppose the alphabet consists of a through z, in natural order, followed by a blank and then the digits 0 through 9, in natural order. Associate these "letters" with the numbers 0,1,2,...,36, respectively, thus forming a 37-letter alphabet, D. Use the affine cipher to decipher the message X01916R916546M9CN1L6B1LL6X0RZ6UII if you know that the plaintext message begins with "t" followed by "h". Write out the affine mapping f and its inverse.Suppose that in a long ciphertext message the letter occurred most frequently, followed in frequency by. Using the fact that in the -letter alphabet, described in Example, "blank" occurs most frequently, followed in frequency by, read the portion of the message enciphered using an affine mapping on. Write out the affine mapping and its inverse. Example 2 Translation Cipher Associate the letters of the "alphabet" with the integers. Let and define the mapping by where is the key, the number of positions from the plaintext to the ciphertext. If our alphabet consists of through, in natural order, followed by a blank, then we have "letters" that we associate with the integers as follows:Decrypt the message "XMJQYJWNSUQFHJ" which was encrypted with a Caesar cipher with a shift of 5 (A to F). Give your response in all caps with no spaces.
- What is the secret message produced from the message “MEET YOU IN THE PARK” using the Caesar cipher?Decrypt the message EABW EFRO ATMR ASIN, which is the ciphertext produced by encrypting a plaintext message using the transposition cipher with blocks of four letters and the permutation ? of {1, 2, 3, 4} defined by ?(1) = 3, ?(2) = 1, ?(3) = 4, and ?(4) = 2.Suppose that when a string of English text is encrypted using a shift cipher f (p) = (p + k) mod 26, the resulting ciphertext is DY CVOOZ ZOBMRKXMO DY NBOKW. What was the original plaintext string?

