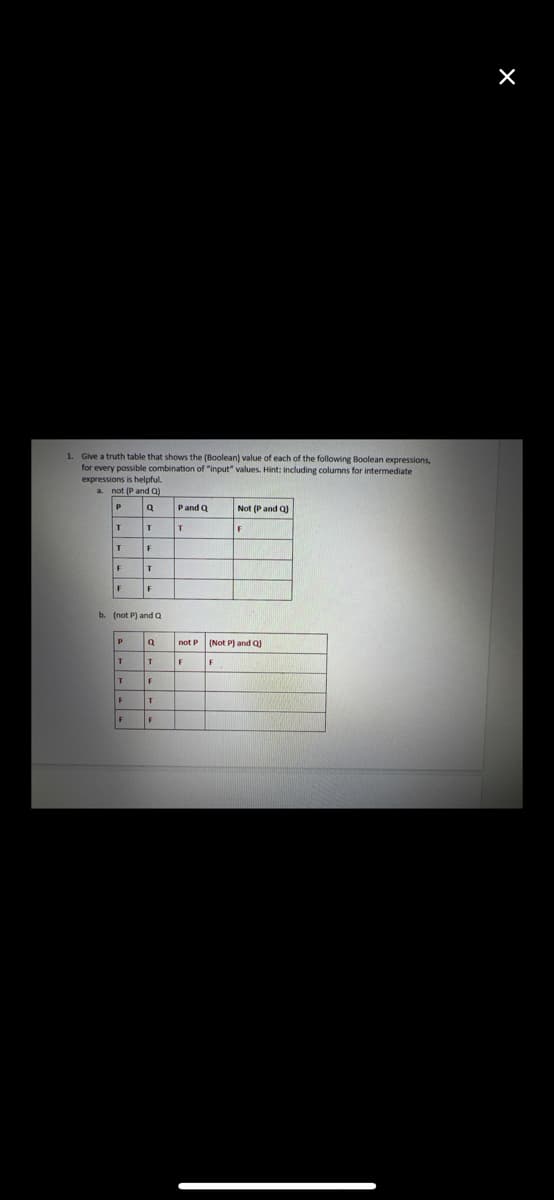
1. Give a truth table that shows the (Boolean) value of each of the following Boolean expressions, for every possible combination of "input" values. Hint: including columns for intermediate expressions is helpful a not (P and Q) Pand Q Not (P and Q) F F b. (not P) and Q P. (Not P) and Q not P T. F F.
Q: When surfing online, you get some strange data on an apparently secure website, and you realize you ...
A: Answer: The Certificate Authority is the organization that issues all the digital certificates for w...
Q: Take the two numbers from the user and try to multiply both of them using lambda function in python.
A: Write a Python program to input two numbers from the user and multiply both the numbers using the la...
Q: on, you may figure out how many computer instructions are required for each sou
A: Introduction: The algorithm determines the number of instructions executed from the source program a...
Q: When it comes to ensuring the resilience and availability of a LAN network, what are the most effect...
A: Introduction: LANs are computer networks that range in size from a few computers in a single workpla...
Q: After the SHR instruction is executed in the code sequence below, what is the final value for AL? MO...
A: Correct Option is B⇒ 0010_1011
Q: DISCUSS HOW TO BUILD SERVER-SIDE DATABASE-DRIVEN FUNCTIONALITY ENABLING DATA EXCHANGE BETWEEN CLIENT...
A: NOTE :- Below i explain the answer in my own words by which you understand it well. Internet brow...
Q: What protocol, besides SSL or TLS, is used to protect browser-to-webserver connections?
A: Introduction: It is safe to send and receive text through the Hypertext Transfer Protocol, which is ...
Q: What is the first general-purpose computer which consumes a huge room as its storage? a) EDVAC b) EN...
A: Your answer is given below with explanation.
Q: tialize:
A: public class Demo { public static void display(int n) { int count=0; while(n>0) { n=n/2; count...
Q: Explain what happens to your system when you change the default runlevel/target to runlevel 6 or reb...
A: Introduction: The /etc/inittab file sets the system's default run level. This is the runlevel that a...
Q: Provide two advantages and two disadvantages of the SEI's Capability Maturity framework's approach t...
A: Introduction: Capability Maturity brings together a strategy for reviewing common impediments to the...
Q: The question is, whether kind of program-level parallelism (data or control) is best suited to SIMD....
A: Introduction: When you decentralize a single program and run it on multiple processors, you implemen...
Q: stems, what exactly is
A: Virtual Memory It is a storage allocation system that allows secondary memory to be addressed as i...
Q: Computer science What is a hyper-threaded CPU, Why are hyper-threaded processors used?
A: Introduction: Hyper-threading is a technique in which a CPU splits its physical cores into virtual c...
Q: From Oracle SQL Need the code. Task 3: In the NONCAT table, change the description of item ID DT12...
A: We want to change description of item ID DT12. New description is Dog Toy Gift Bonaza. He we used up...
Q: With regard to the performance of virtual machines, what is one of the most critical hardware resour...
A: For storage, it makes use of an variety of actual hardware resources such as RAM, CPU, and hard driv...
Q: Convert the decimal signed number -7 into 8-bit signed binary number. The signed binary number is 11...
A: Here in this question we have given a decimal number (-7) and we have asked to convert it into sign...
Q: Calculate the Average turn around time and Average Waiting time of SRTF and SJF Process Queue Burst ...
A: SRTF - It is a preemptive version of SJF. SRTF stands for Shortest Remaining Job First. In this algo...
Q: The several forms of data protection available in Microsoft Excel are outlined. Please provide concr...
A: The following are the many methods of data protection that MS-Excel offers: Explanation at the file,...
Q: Given Postfix Expression: . (а) А В + С * D - (b) А ВС * + D - Convert to INFIX!
A:
Q: iv) Input a string str from the user. Write a C++ program, to replace all the occurrences (if any) o...
A: Required:- iv) Input a string str from the user. Write a C++ program, to replace all the occurrences...
Q: Explain in details and give examples of instruction cycle focusing on Fetch, Decode and Execution cy...
A: Processors aren't unique from a positive point of view to a combustion engine, which always carry ou...
Q: Hello, I have to Design a class name Rectangle to represent a rectangle. The class contains: Two da...
A: We need to write a program for given scenarios with uml diagram. The code has been written in Python...
Q: Students in a software engineering programme are usually required to complete a major project at the...
A: Introduction: The advancement of software and the creation of intelligent, efficient information tec...
Q: You are given a binary array containing only 0's and 1's. You have to sort the array and you can swa...
A: Given a binary array containing only 0's and 1's. Write a C++ program to find the minimum number of ...
Q: What is the primary distinction between the development of generic software products and the develop...
A: Introduction: Firefox, Excel, Word, PowerPoint, Notes, Outlook, and other generic applications are o...
Q: What exactly is JAD? What is participatory design, and how does it work?
A: JAD stands Joint Application Development is a methodology that involves the client end user in the ...
Q: Write a recursive method toNumber that forms the integer sum of all digit characters in a string. Fo...
A: Recursion is a process in which a method calls itself continuously.
Q: 2. Write an 8085 program to add two 8-bit numbers Al and CO. Then store the final result into the Ac...
A: Given: Two 8-bit numbers A1 and C0 are given. Requirement: Write an 8085 program to add the given 8-...
Q: Write a complete C++ program that asks the user to input information for at least 10 students. Use s...
A: Answer the above questions are as follows:
Q: Make a distinction between spoofing and session hijacking. In the case that you're a web user, what ...
A: Solution: The session hijacking attacks are conducted when the users logged themselves into the syst...
Q: Feature-rich datasets are used in machine learning to train models (or attributes). We are aware, ho...
A: INTRODUCTION: DATA SET: A data set (or dataset) is a group of related pieces of information. When de...
Q: 3. Suppose we are given a directed acyclic graph G with a unique source s and a unique sink t. A ver...
A: 3) Given an undirected graph G and an edge uv in G. Design an algorithm that runs in 0(|E| + |V|) ti...
Q: When the CMP instruction sequence is executed, what is the final value for AL register ? MOV AL, 25h...
A: 1) The CMP instruction compares two operands. It is generally used in conditional execution. Its syn...
Q: What are the benefits of utilizing a compiled language as opposed to an interpreted language, and wh...
A: Introduction: Interpreted languages are programming languages that are usually interpreted, rather t...
Q: Consider the following directed search graph where S is the starting node and G1 and G2 are goal nod...
A:
Q: Convert the decimal signed number -7 into 8-bit signed binary number. The signed binary number is 11...
A: Answer:
Q: In embedded systems, what exactly is it about virtual memory that makes it so difficult to use?
A: Virtual memory is a common technique used in a computer's operating system (OS). Virtual memory uses...
Q: Explain built-in editor MATLAB with a interface
A: Create apps with graphical user interfaces in MATLAB Graphical user interfaces (GUIs), also known ...
Q: e of IAM and Give a real-time example
A: Lets see the solution.
Q: (C PROGRAMMING ONLY) Make a code with the string function of strchr (with user input)
A: Code: #include <stdio.h>#include <string.h>int main(){ char str[20]; gets(str); ...
Q: QUESTION SIX (6) Given the grammar G = ({S}, {a, b}, S, P) with production S- aSa, S- bSb, S-A i. Sh...
A: The solution to the given question is:
Q: a) Categorize FOUR (4) main layers of automata theory, and explain each layer briefly. b) List ONE (...
A: Introduction: Automata is a machine that can accept the strings of a language L over an input alpha...
Q: Is cloud computing capable of addressing all of a company's worries about its information technology...
A: Answer :
Q: Define the concept of a unified memory architecture.
A: The goal of unified memory is to reduce data redundancy by copying data between separate areas of me...
Q: An HTTP GET command retrieves data from a website via its URL True False
A: We are given a statement about HTTP GET command , lets see if it is true or not.
Q: 1. What is Failover-Clustering and why do you think it is so widely used?
A: Failover clustering is Microsoft's implementation of the high availability cluster method for provid...
Q: What is the main idea of pseudoreplication in a mensurative experiment? GIve an example and explain.
A: Pseudo replication occurs when the observations are not statistically independent and this pseudo re...
Q: Write a class called MonetaryCoin that is derived from the Coin class presented in Chapter 5. Store ...
A: Coin class we could define the following data: face, an integer that represents the current face HE...
Q: Do you believe that wireless applications are the ones that stand to benefit the most from error cor...
A: Error correction It is best utilised with wireless apps or networks and is a terrific challenge. The...
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- Build truth tables or abbreviated truth tables (on your own scratch paper) to determine whether the following arguments are valid or invalid. (A v B) --> (C • D), (X v ~Y) --> (~C • ~W), (X v Z) --> (A • E), ∴∴~X Group of answer choices A. Valid B. InvalidConstruct a truth table for the statements belowa. (p ∧ q) ∧ (~r ∨ q).b. ~[~p ∧ (q ∧ r)]c. [p ∧ (q ∨ ~p)] → ~p then find the truth value of the statement givena. p is a false statement, q is a true statement and r is a true statement.b. p is a false statement, q is a false statement and r is a false statement.c. p is a false statement, q is a false statement and r is a true statement.Simplify the following expression using Boolean algebra rules and create a truth table for the simplified expression: Are the two expressions equivalent?Explain.
- Show using a truth table if the following statements are equivalent. d. p → (q ∨ r) and (p → q) ∨ (p → r)e. [p ↔ (q ∨ r)] ∨ q and (p → q) ∨ (p ↔ r)Are the statements P → (Q ∨ R) and (P → Q)⋁(P → R) logically equivalent? Create a truth table.Create truth tables for the following expressions:a. S = NOT((A OR B) AND (NOT(A) OR NOT(B)))b. S = (A AND B) OR NOT(A OR B)c. S = (A) OR (B AND C) OR (NOT(B OR C) AND (A OR C))d. S = ((A AND B) OR (C AND D)) AND NOT((C AND NOT(A)) OR (B AND D))
- Construct a truth table and use it to determine which of the following statements is equivalent to the statement ∼p∧∼q.i need answer of all. if any answer will be skipped, your answer will be rejected. only complete answer will be accepted. b) Make a truth table for the statement ¬P ∧ (Q → P). What can youconclude about P and Q if you know the statement is true? a) Make a truth table for the statement (P ∨ Q) → (P ∧ Q). c) Make a truth table for the statement ¬P → (Q ∧ R).The following argument is quantificationally valid. Explain why. (∀x)(Sx ⊃(Gx ∨Bx))(∃x)(Sx & ~ Bx) (∃x)Gx Can you explain in words not symbols?
- Using the test technique(for example, replace E with symbol a... ), prove or disprove the following identities concerning regular expressions.1. (E + F)∗ = (E∗ + F∗)∗2. (EE)∗ = E∗ + E^2Construct a truth table that displays all possible values for the following expression: ~p ^ ( ~p V q ) -> ( p V q ) **Provide a list for the order of the operators that should be evaluatedCorrect answer will be upvoted else downvoted. Computer science. decimal portrayal of x without driving zeroes comprises of a digits; the decimal portrayal of y without driving zeroes comprises of b digits; the decimal portrayal of gcd(x,y) without driving zeroes comprises of c digits. gcd(x,y) indicates the best normal divisor (GCD) of integers x and y. Output x and y. In case there are various replies, output any of them. Input The primary line contains a solitary integer t (1≤t≤285) — the number of testcases. Every one of the following t lines contains three integers a, b and c (1≤a,b≤9, 1≤c≤min(a,b)) — the necessary lengths of the numbers. It very well may be shown that the appropriate response exists for all testcases under the given limitations. Extra requirement on the input: all testcases are unique. Output For each testcase print two positive integers — x and y (x>0, y>0) to such an extent that the decimal portrayal of x without…

