1. How many entities are there within the entire database? 2. How many attributes are there for each entity? 3. Give at least four (4) constraint within each of the entities.
1. How many entities are there within the entire database? 2. How many attributes are there for each entity? 3. Give at least four (4) constraint within each of the entities.
Chapter3: Data Representation
Section: Chapter Questions
Problem 1PE
Related questions
Question
Transcribed Image Text:10:50
49
..
Case Study 1 (CC-105).p. O
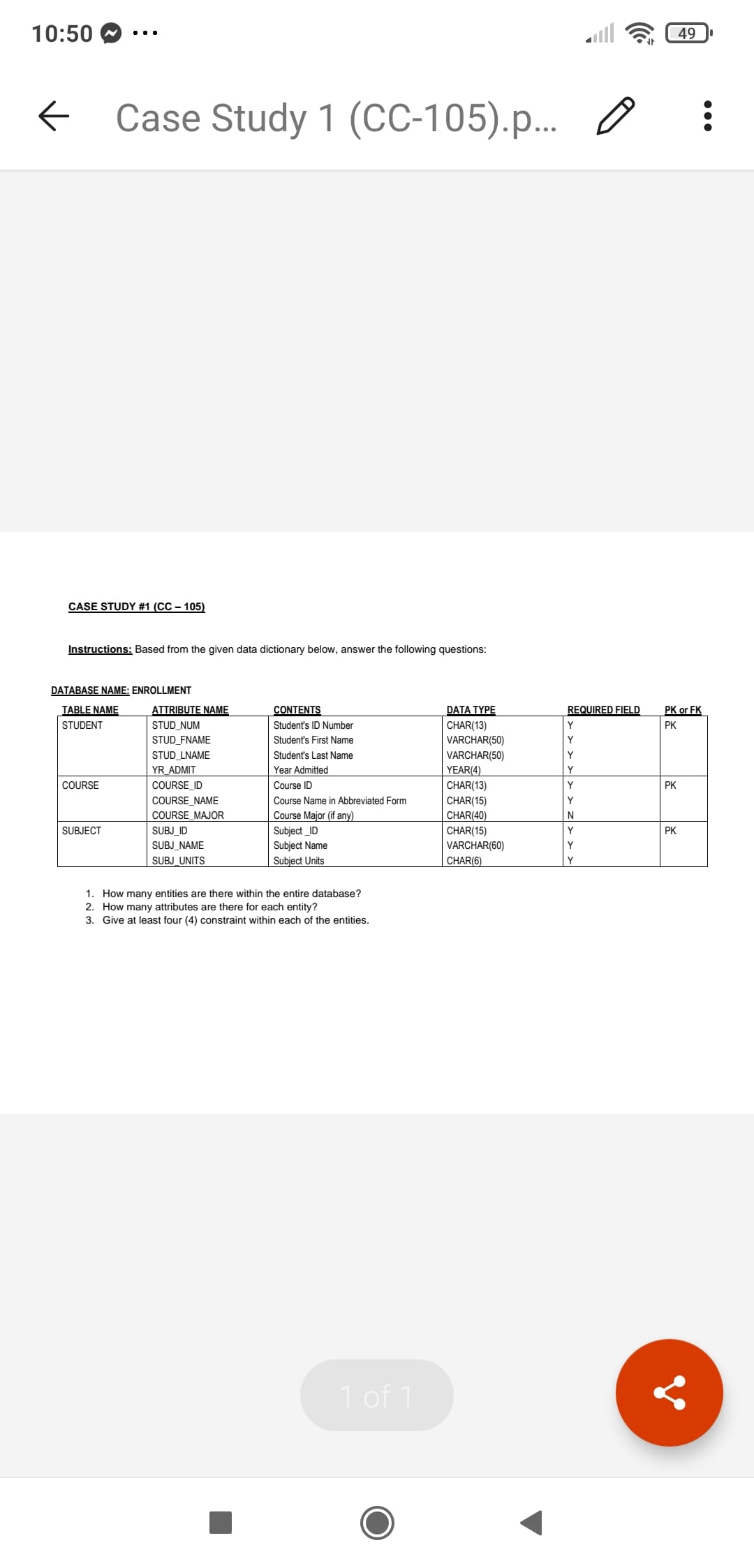
CASE STUDY #1 (CC – 105)
Instructions: Based from the given data dictionary below, answer the following questions:
DATABASE NAME: ENROLLMENT
TABLE NAME
ATTRIBUTE NAME
CONTENTS
DATA TYPE
REQUIRED FIELD
PK or FK
STUDENT
STUD_NUM
Student's ID Number
CHAR(13)
VARCHAR(50)
Y
PK
STUD_FNAME
Student's First Name
Y
STUD_LNAME
Student's Last Name
VARCHAR(50)
YEAR(4)
Y
YR ADMIT
Year Admitted
Y
COURSE
COURSE ID
Course ID
CHAR(13)
CHAR(15)
CHAR(40)
CHAR(15)
VARCHAR(60)
CHAR(6)
Y
PK
COURSE_NAME
Course Name in Abbreviated Form
Y
Course Major (if any)
Subject _ID
Subject Name
Subject Units
COURSE MAJOR
N
SUBJECT
SUBJ_ID
Y
PK
SUBJ NAME
Y
SUBJ_UNITS
Y
1. How many entities are there within the entire database?
2. How many attributes are there for each entity?
3. Give at least four (4) constraint within each of the entities.
1 of 1
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning